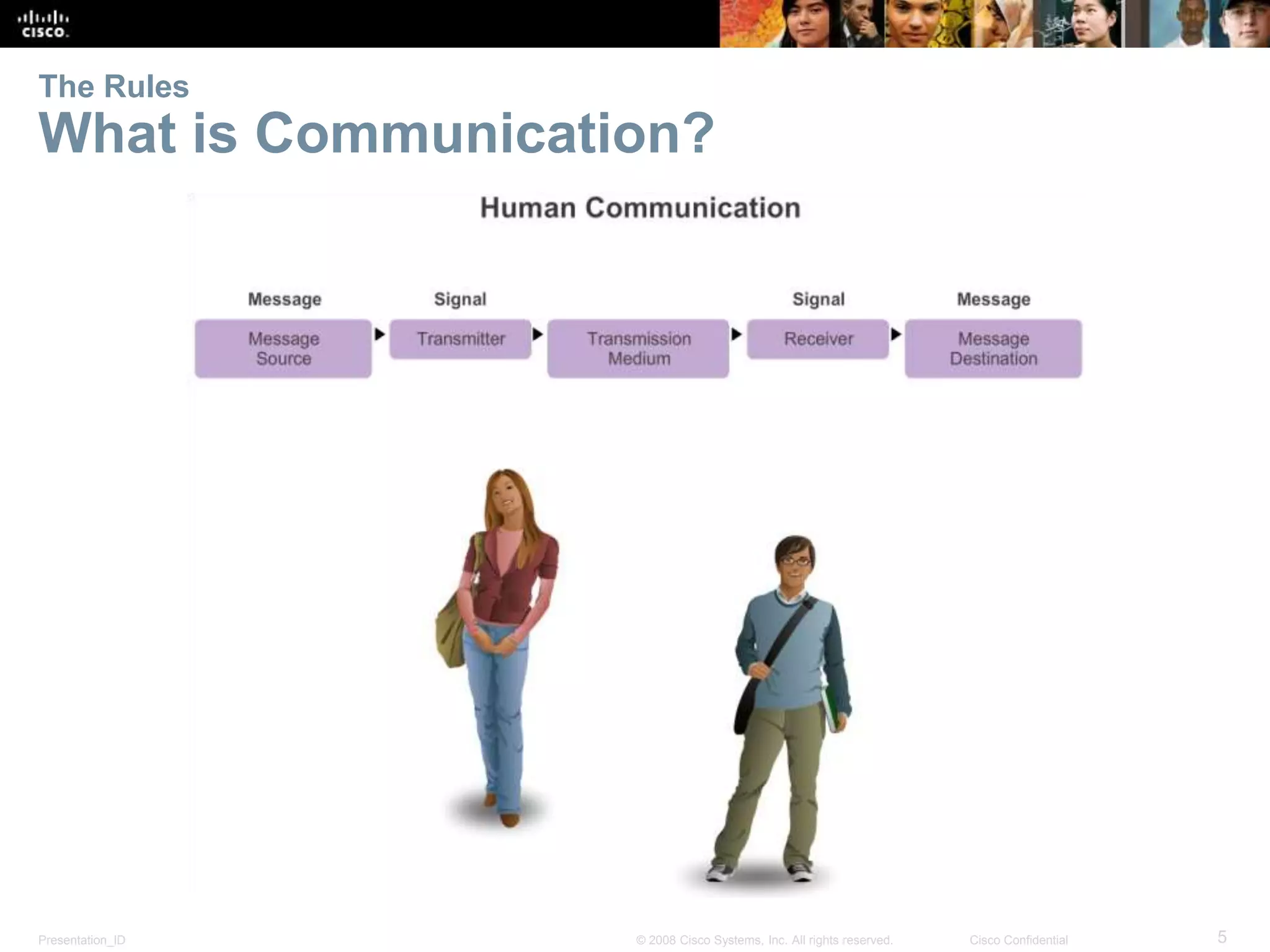
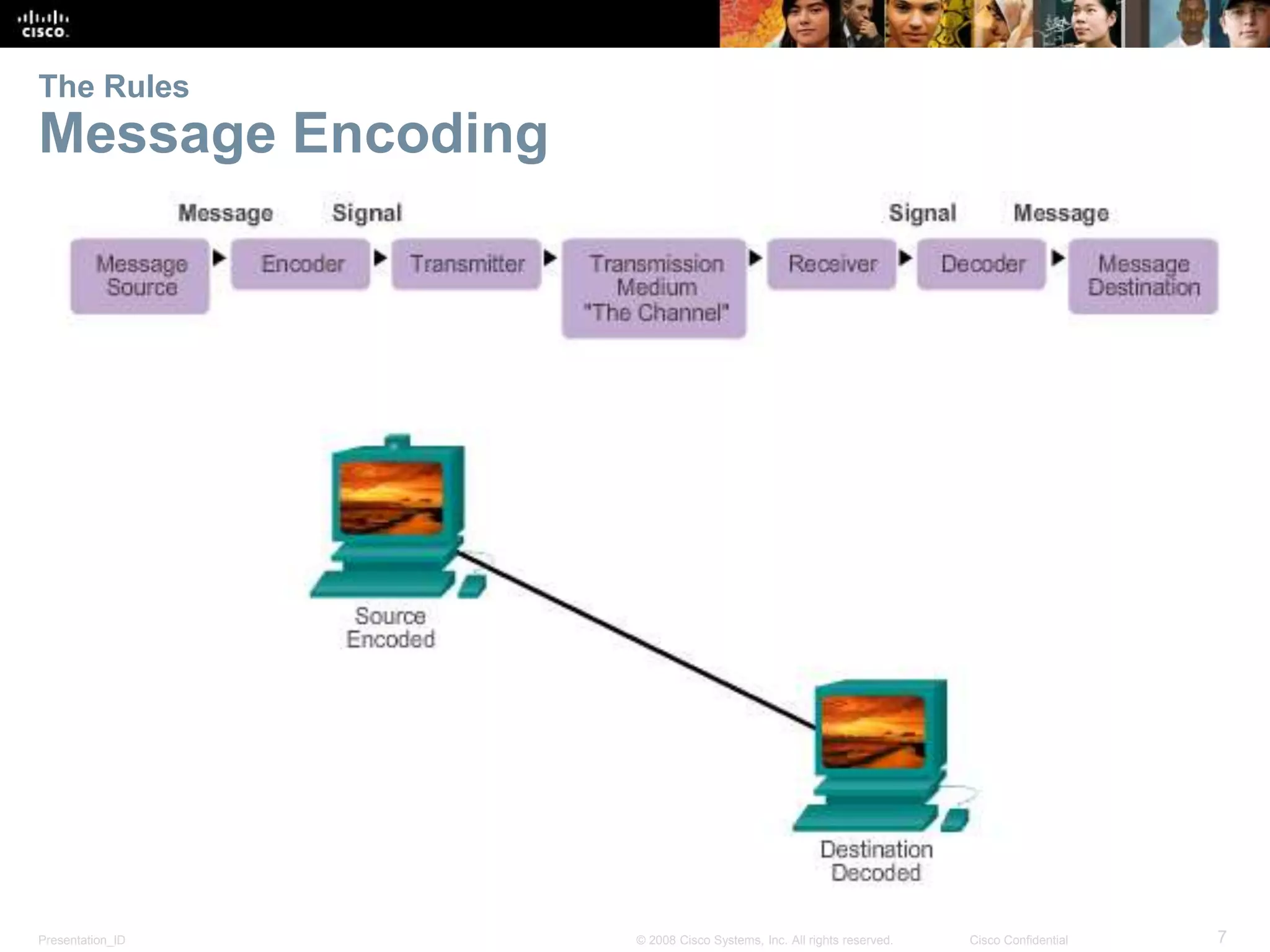
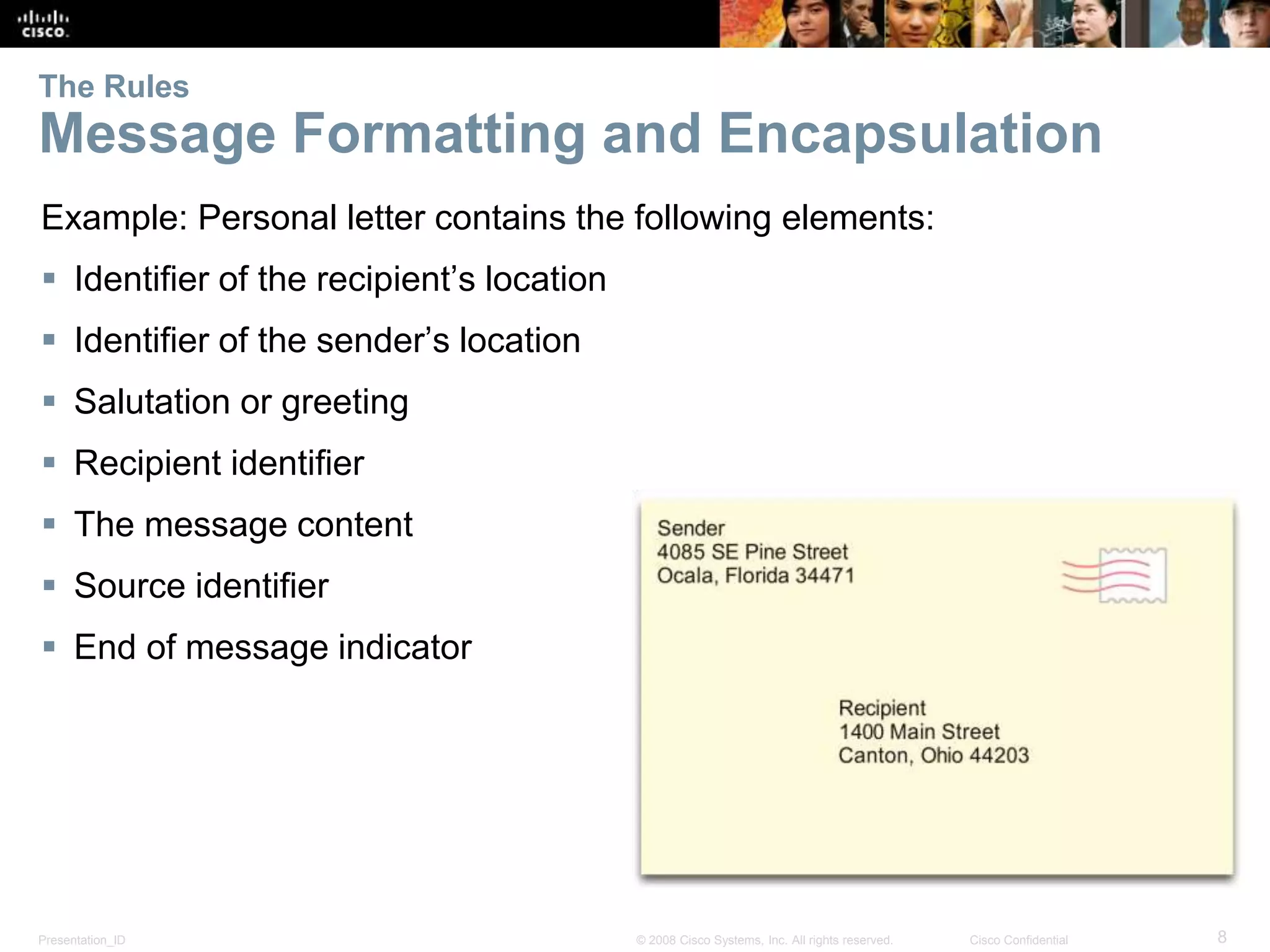
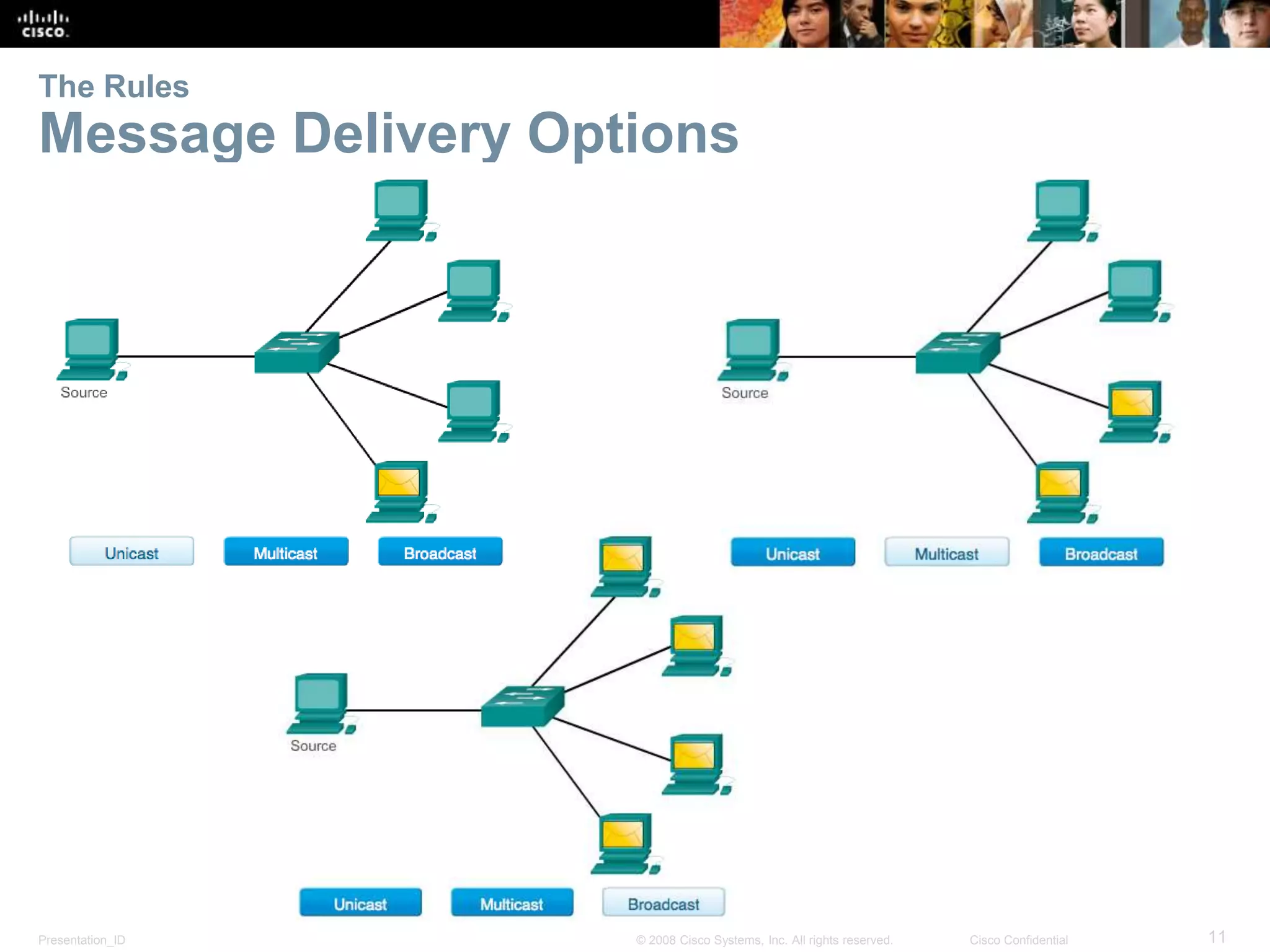
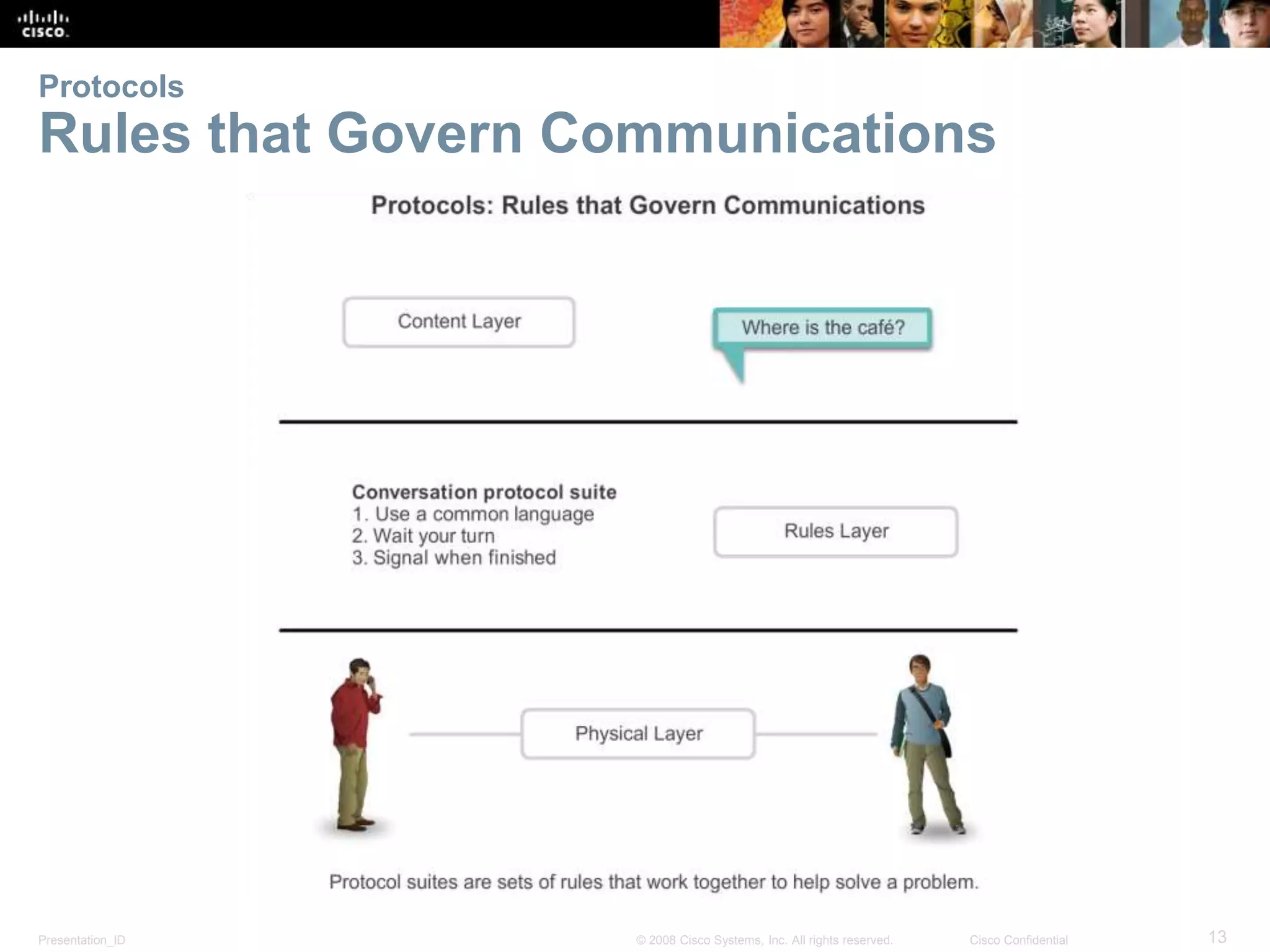
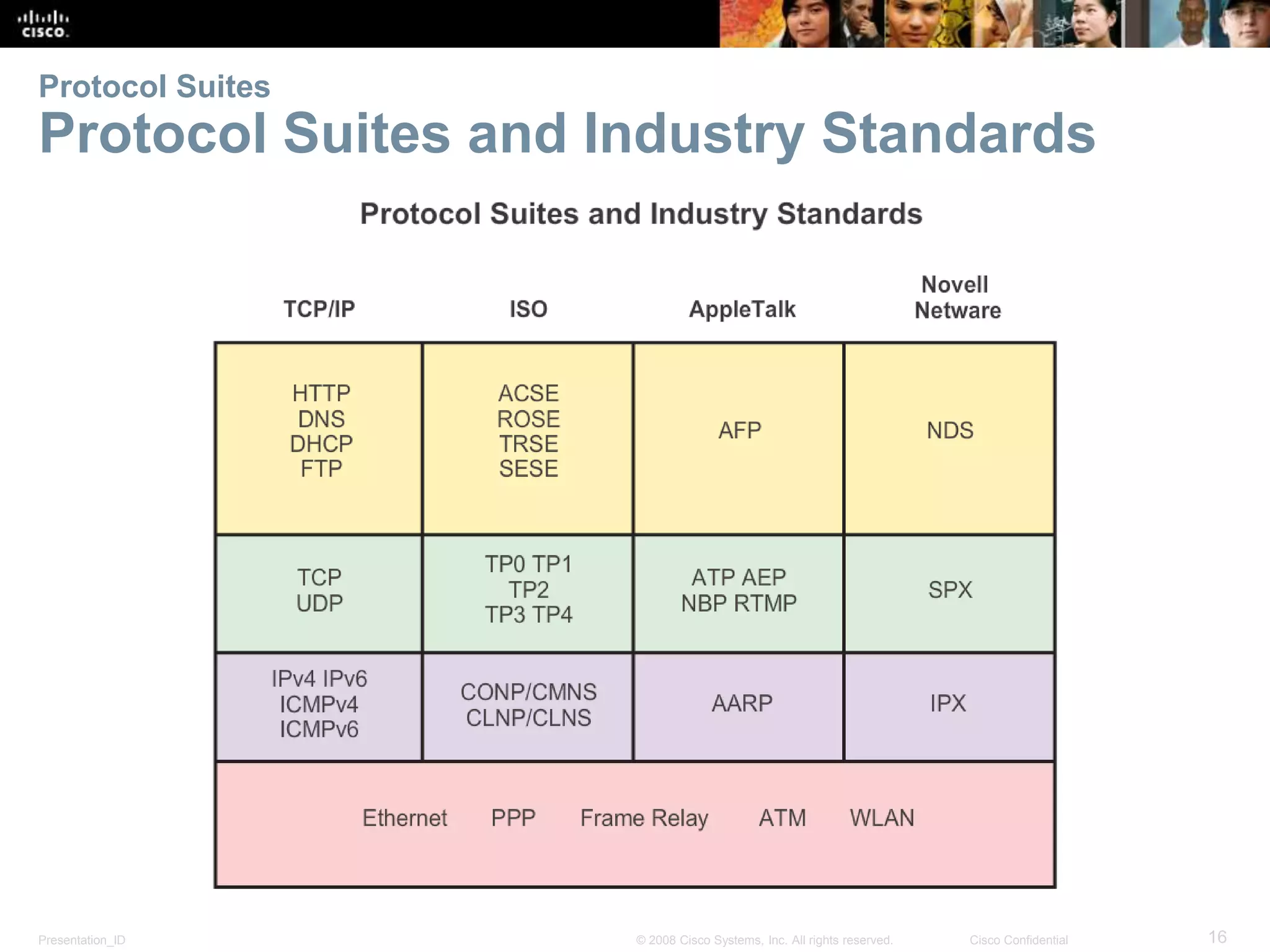
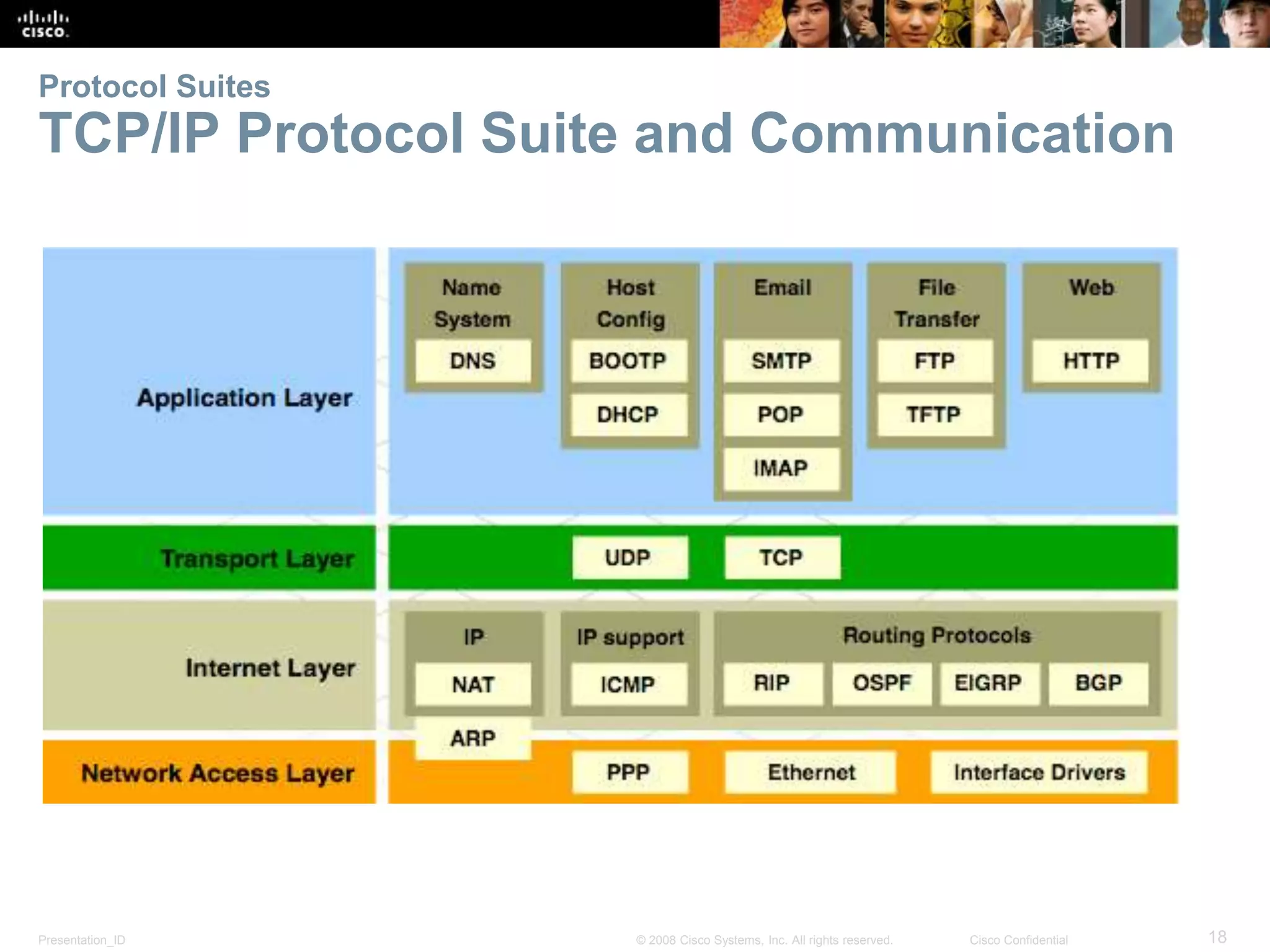
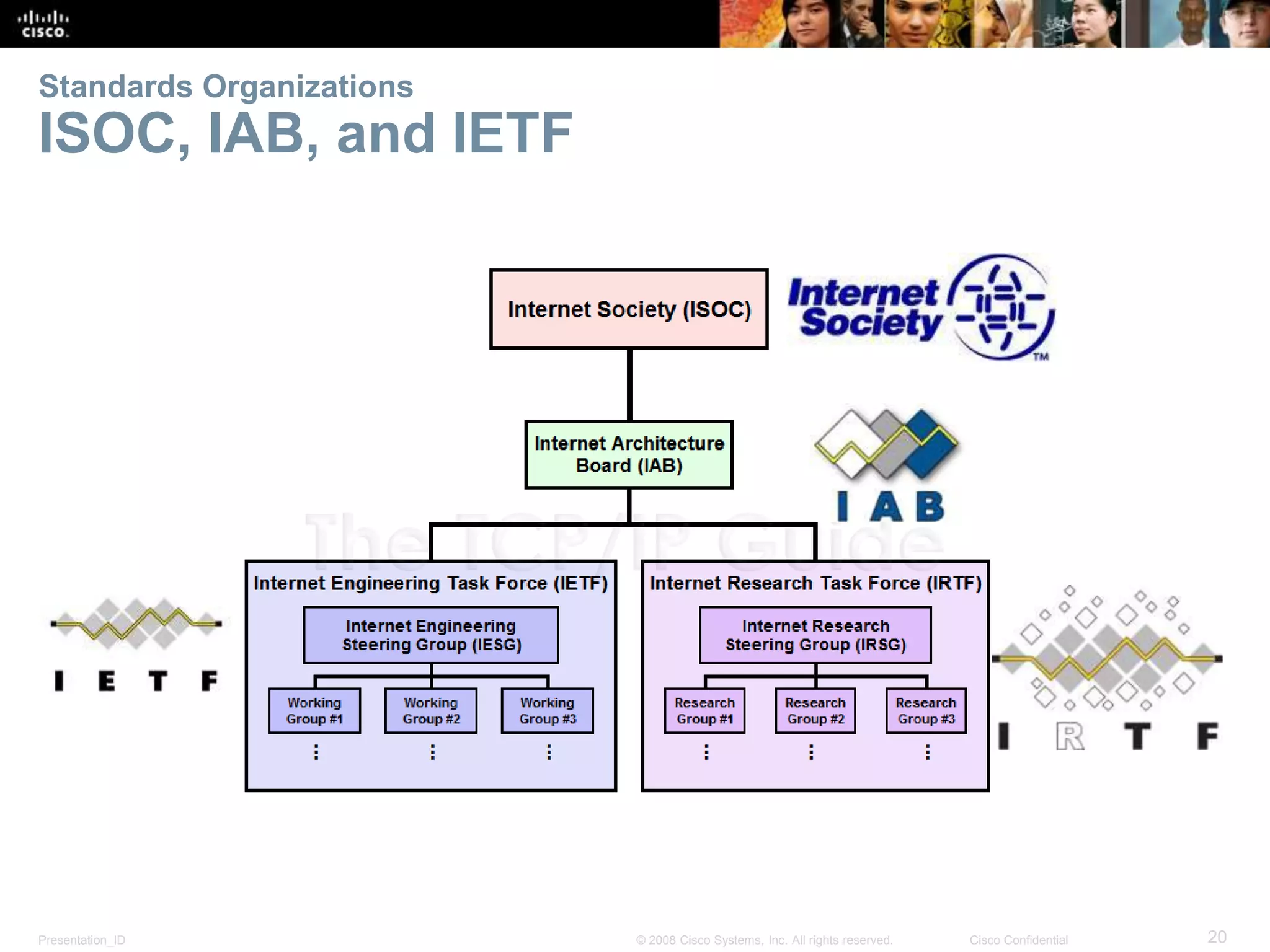
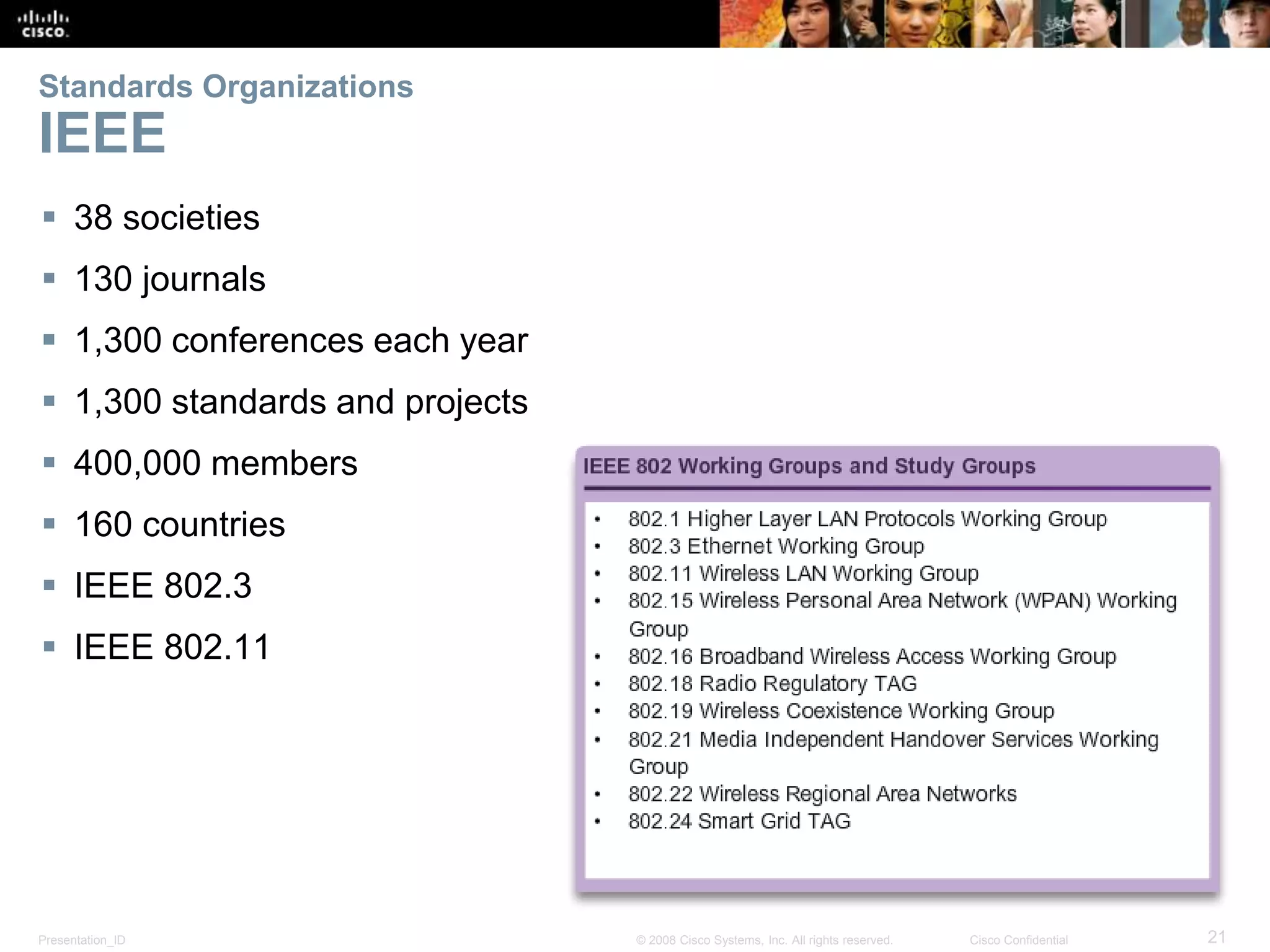
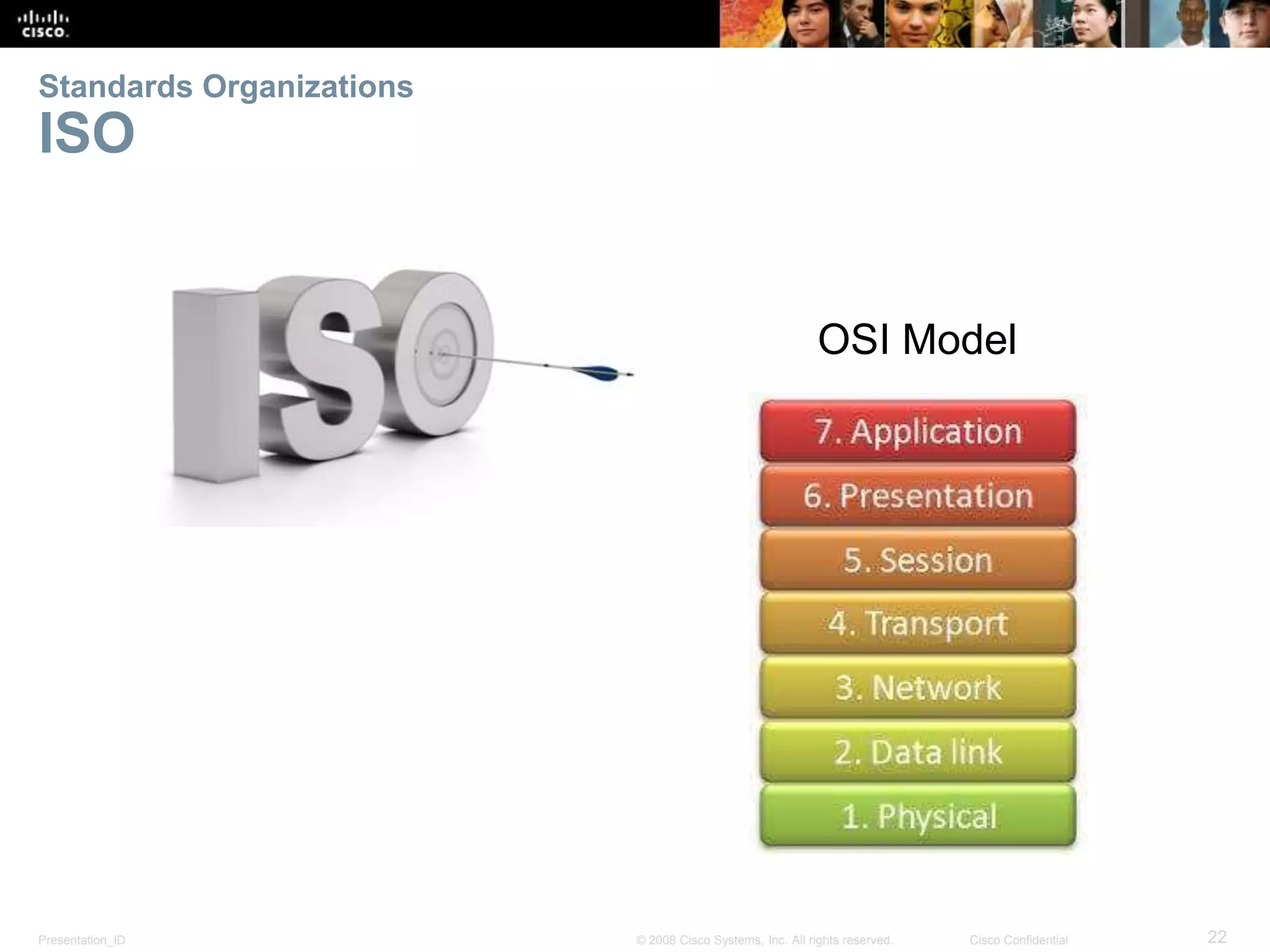
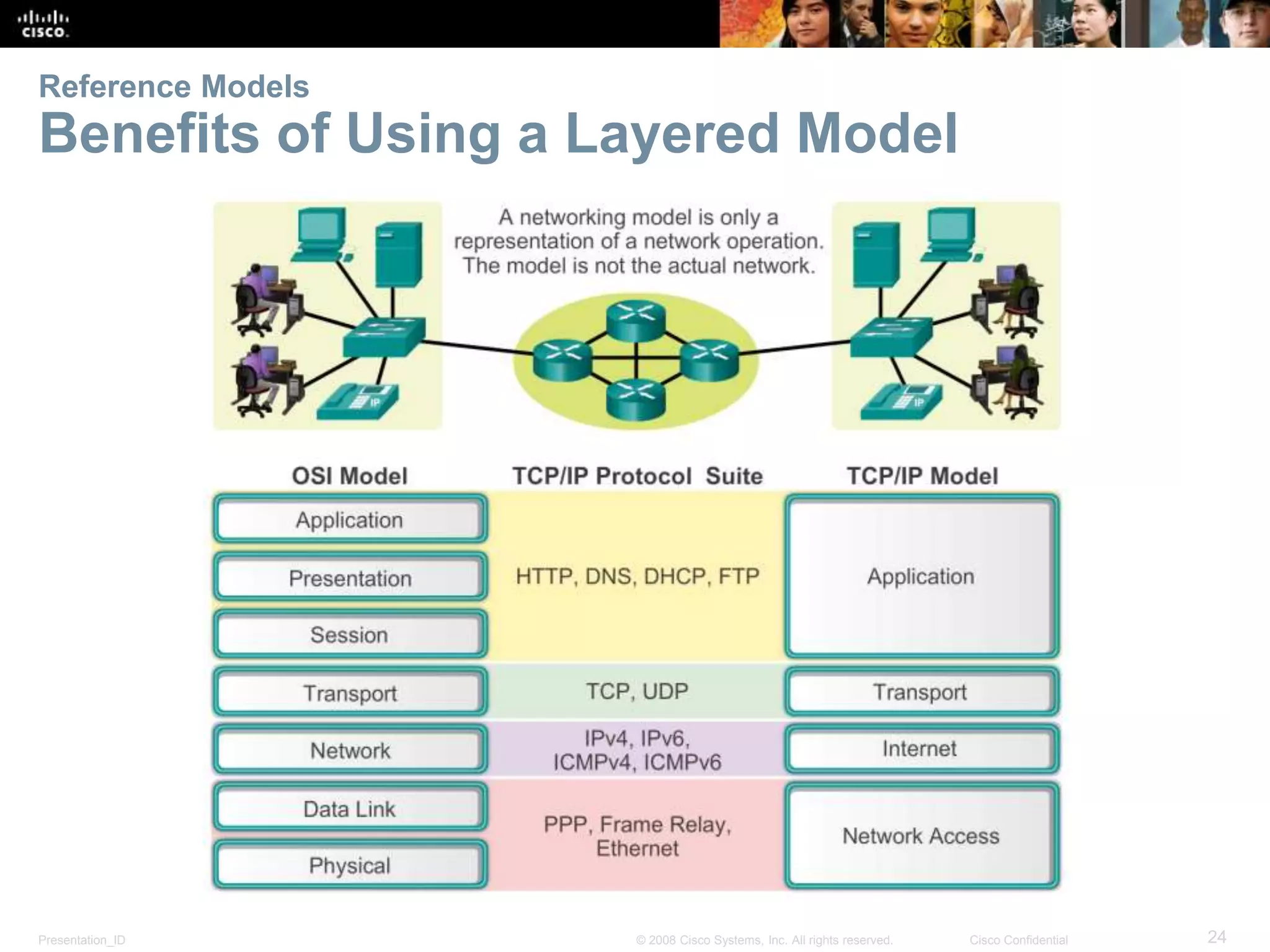
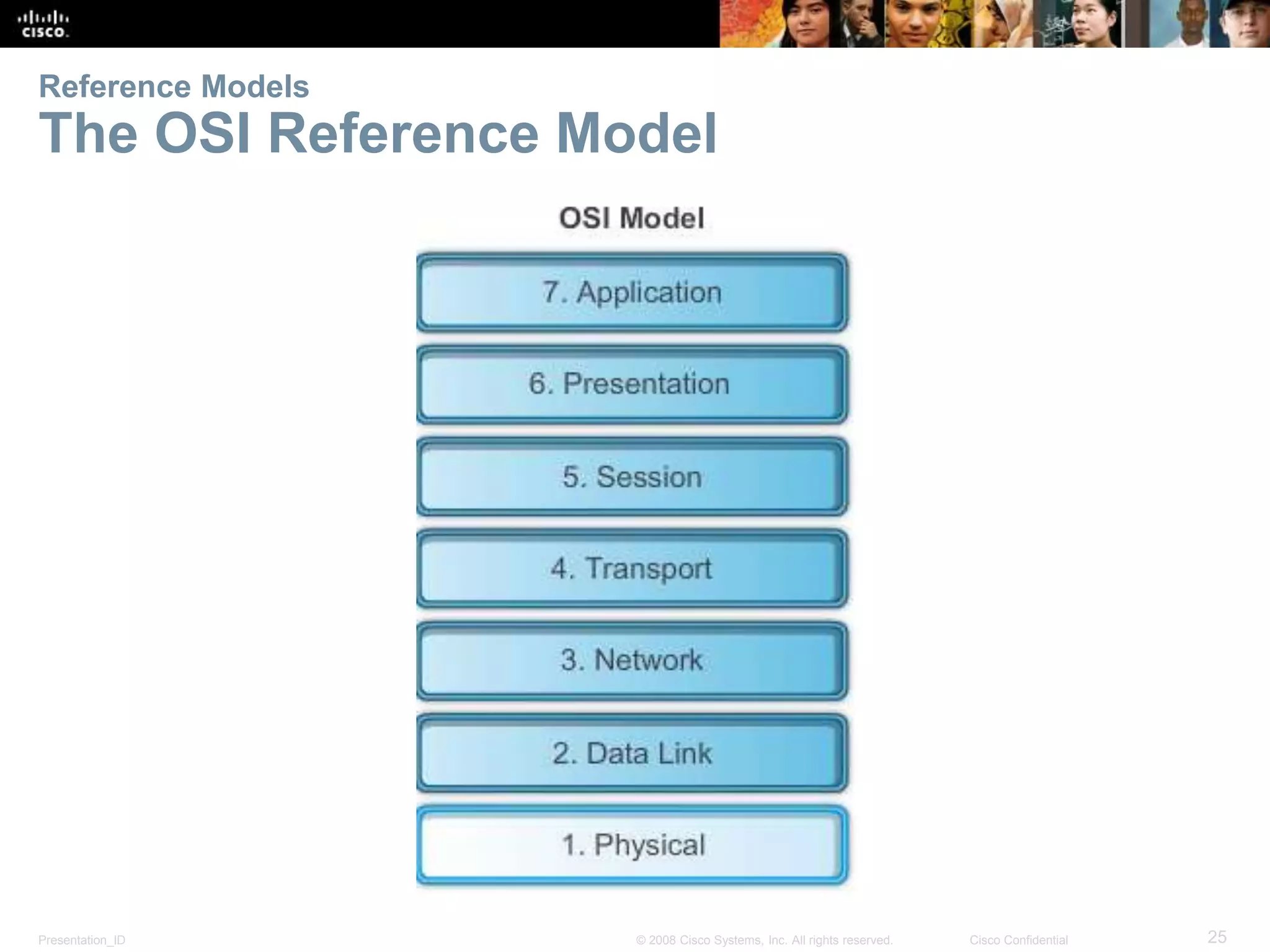
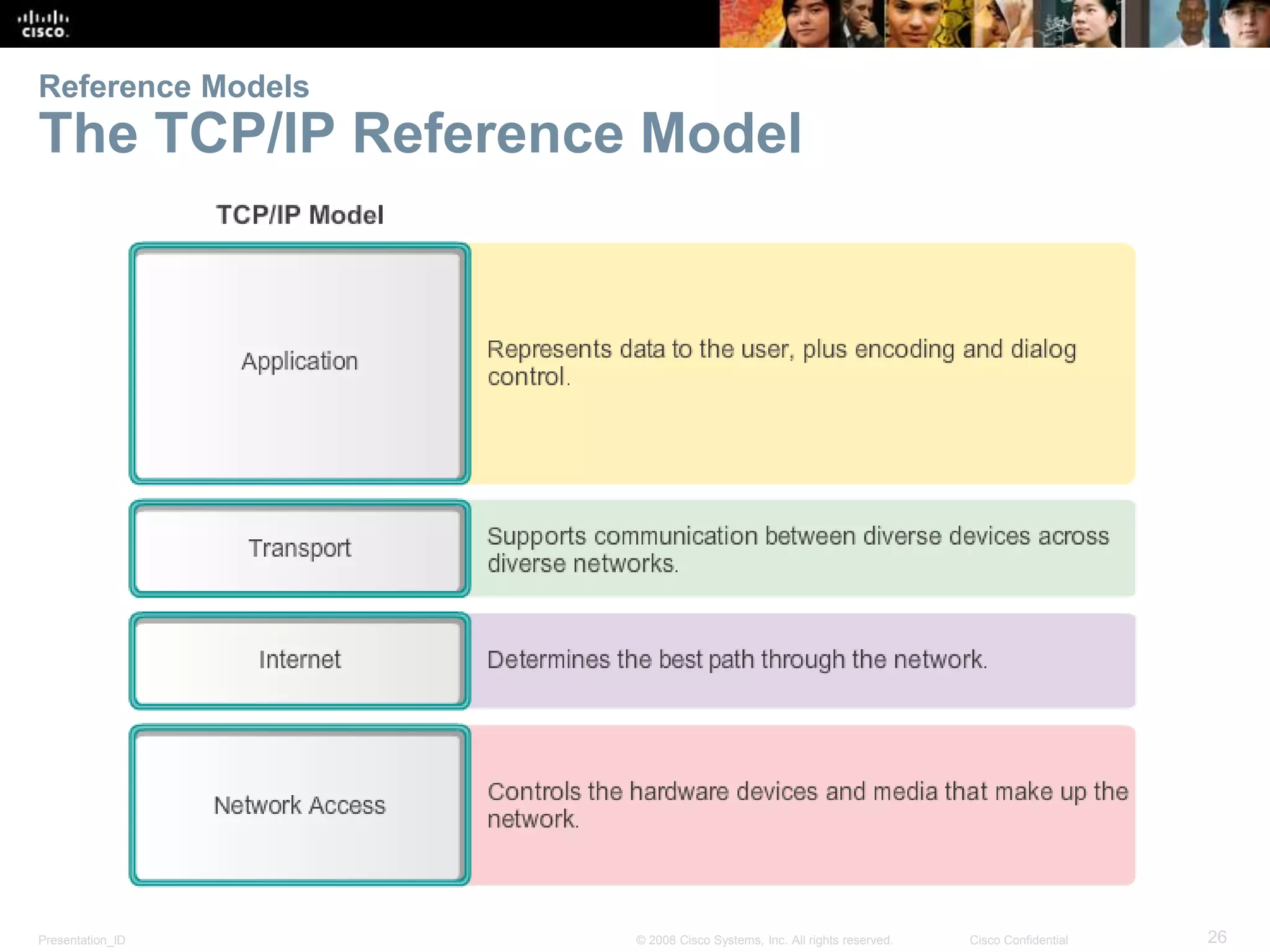
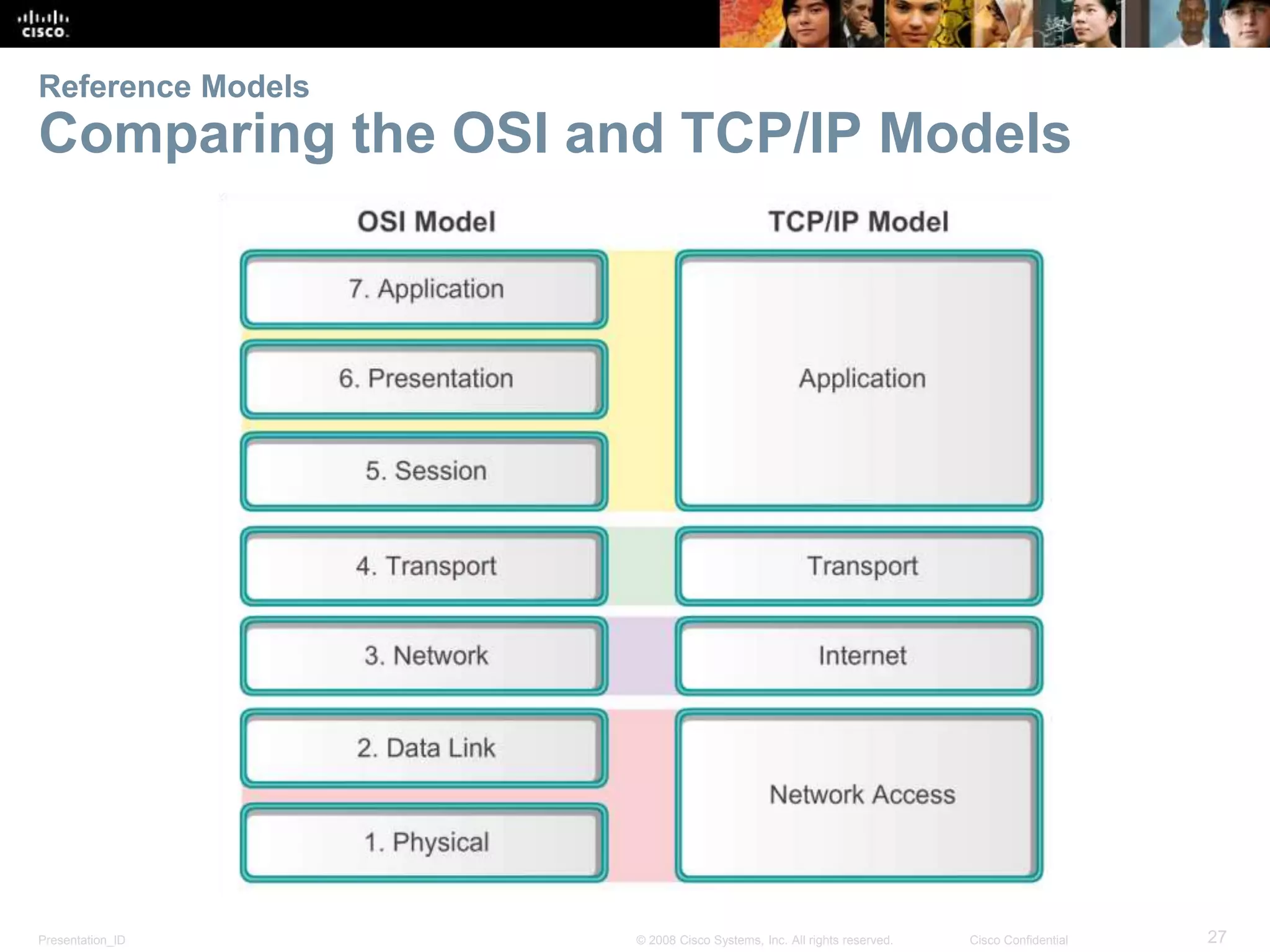
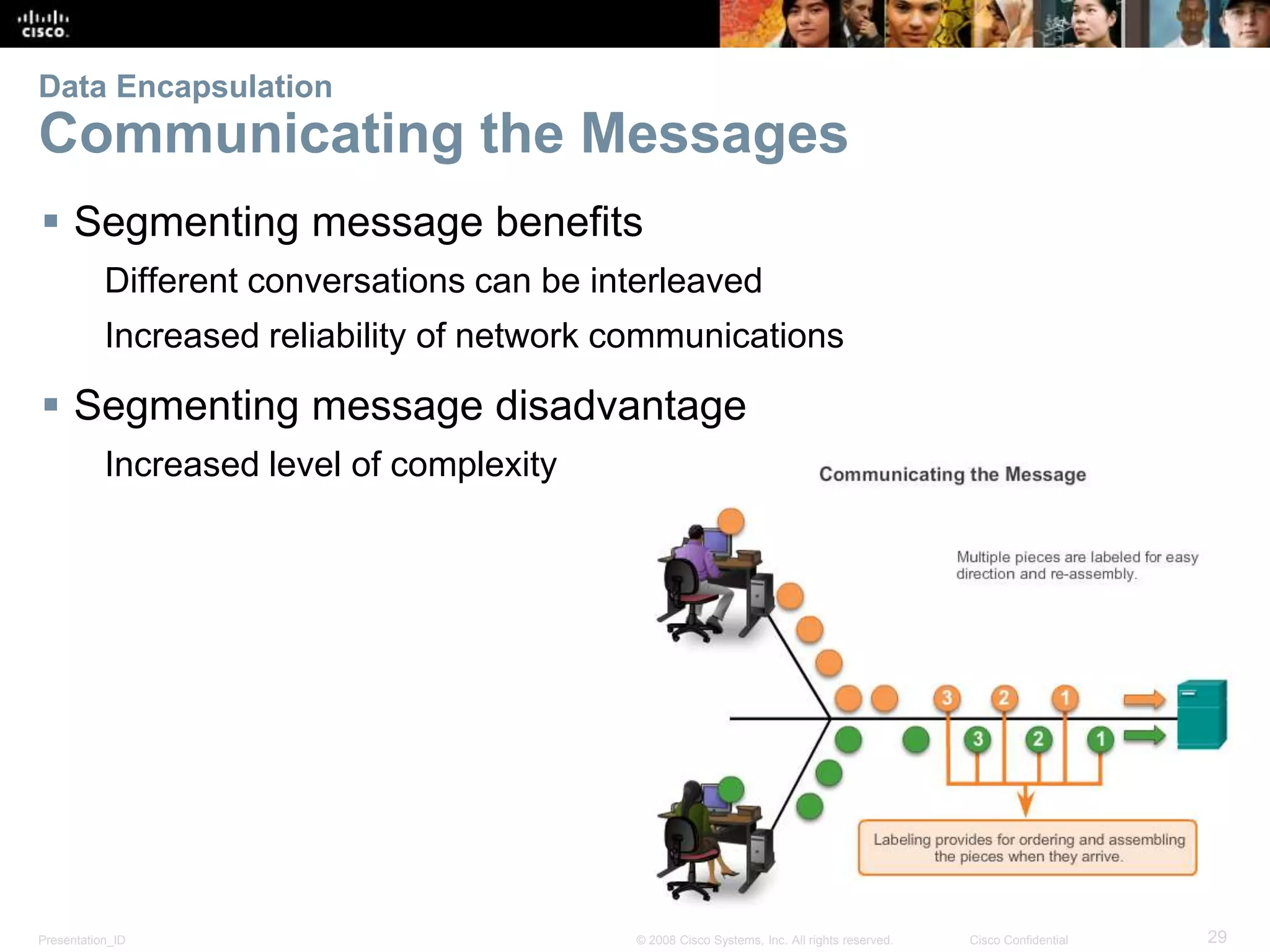
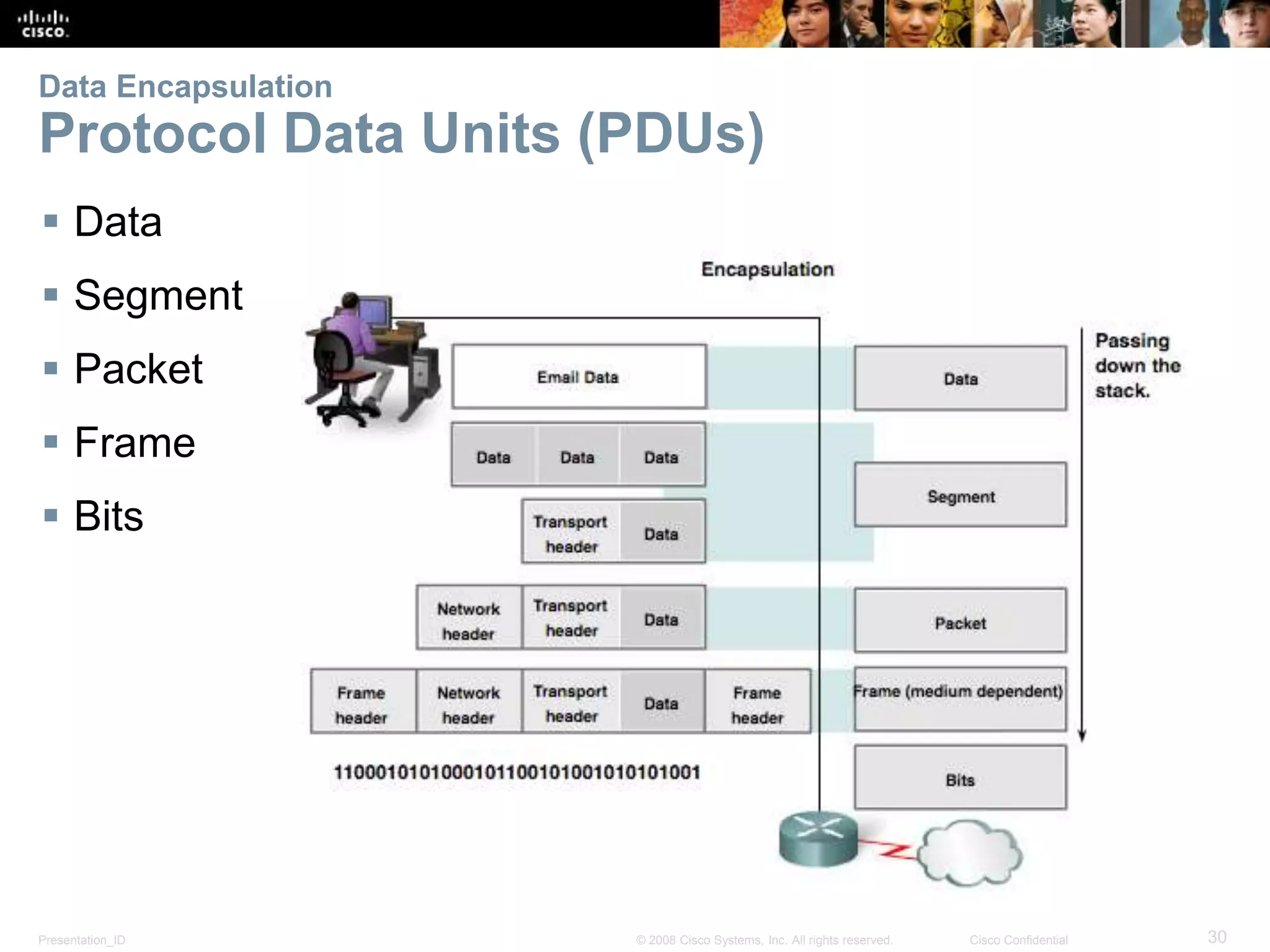
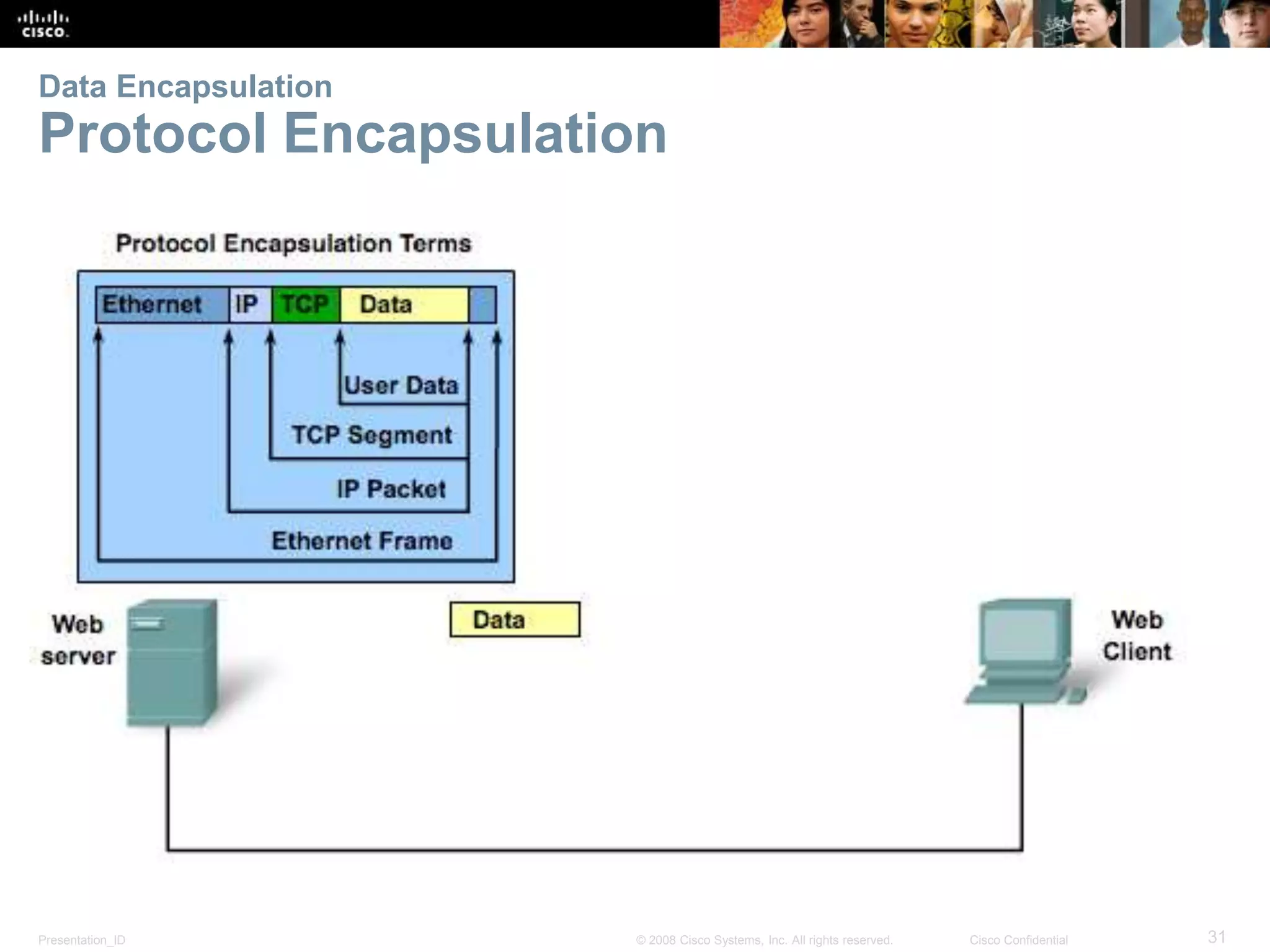
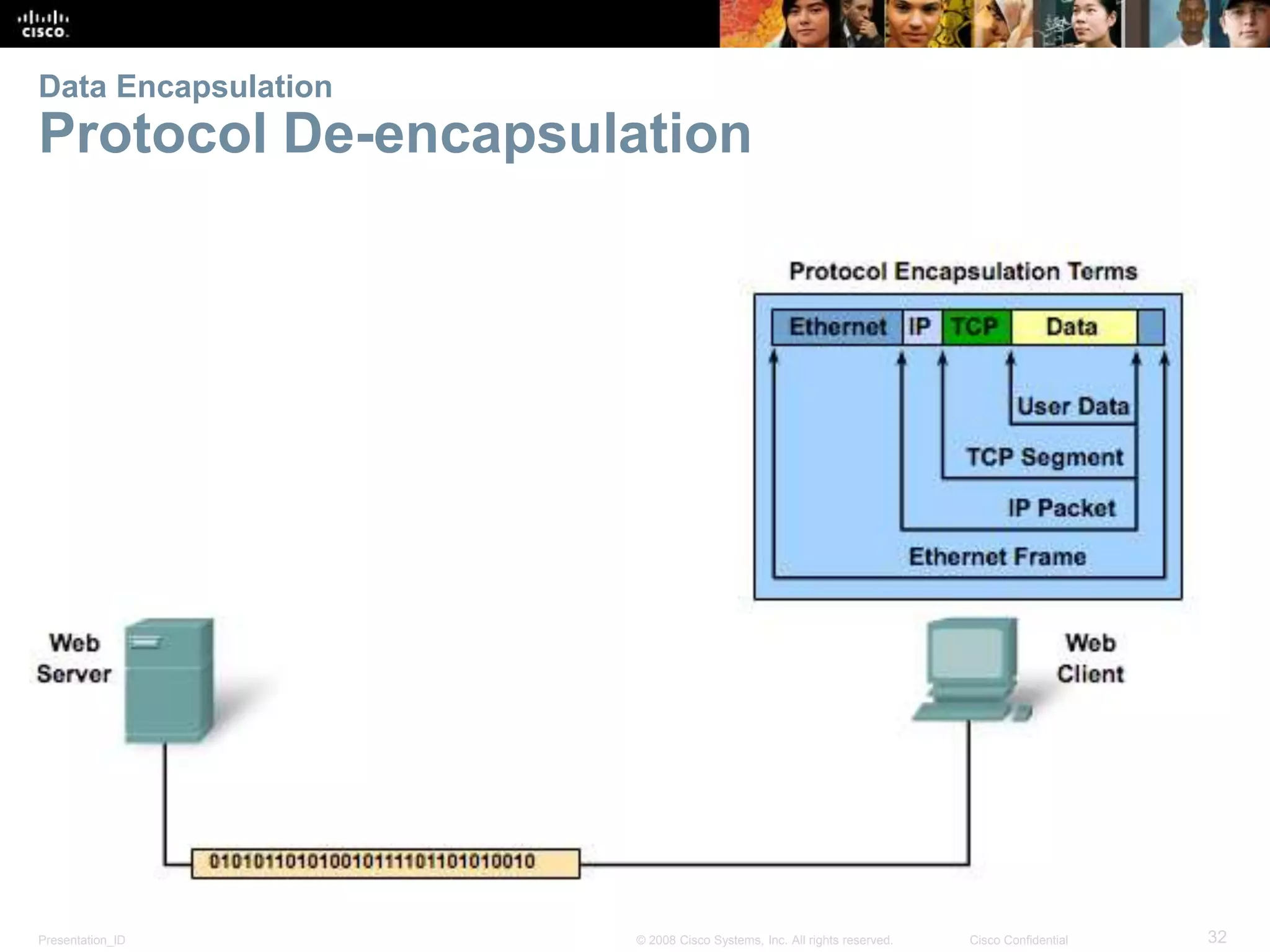
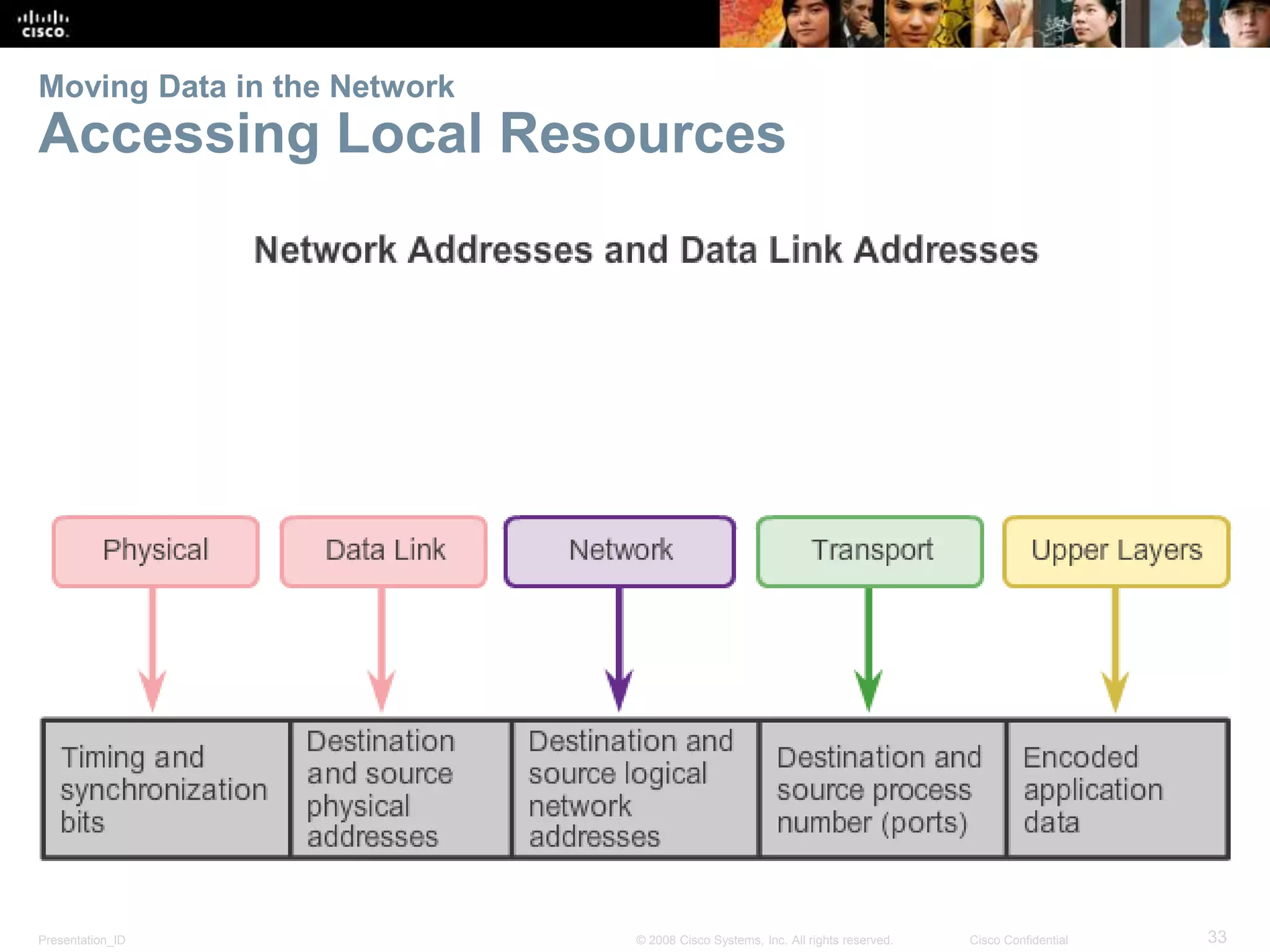
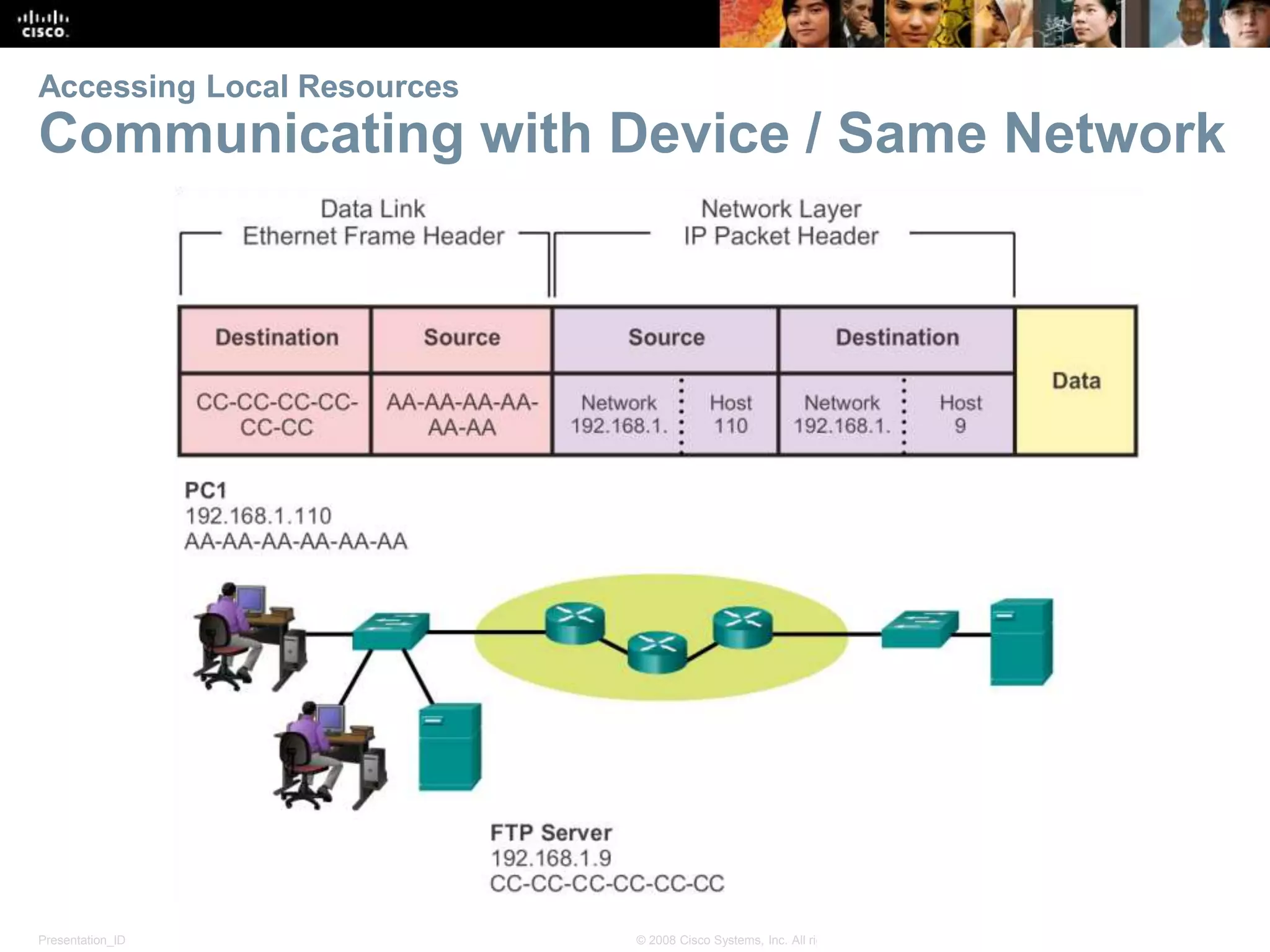
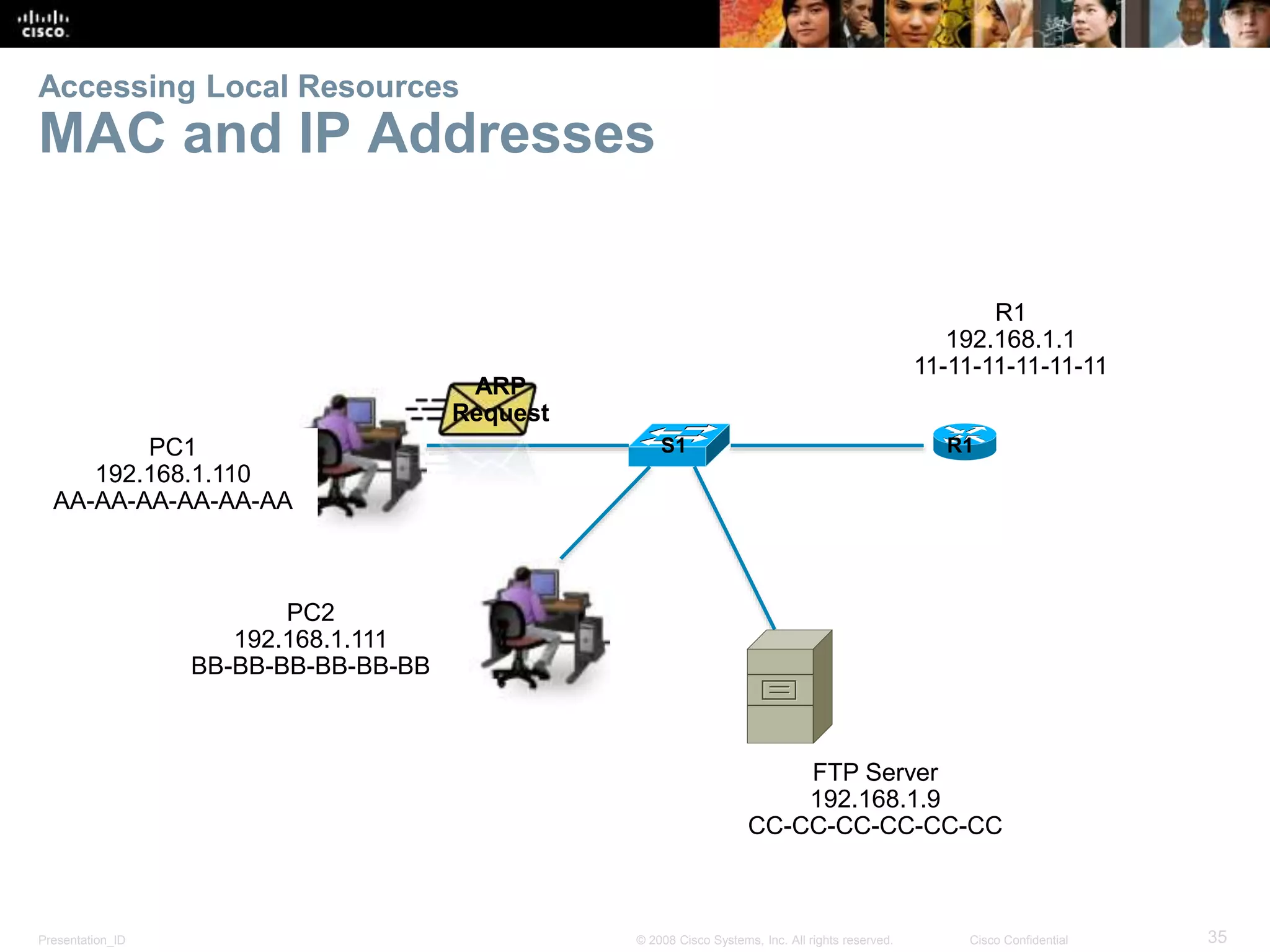
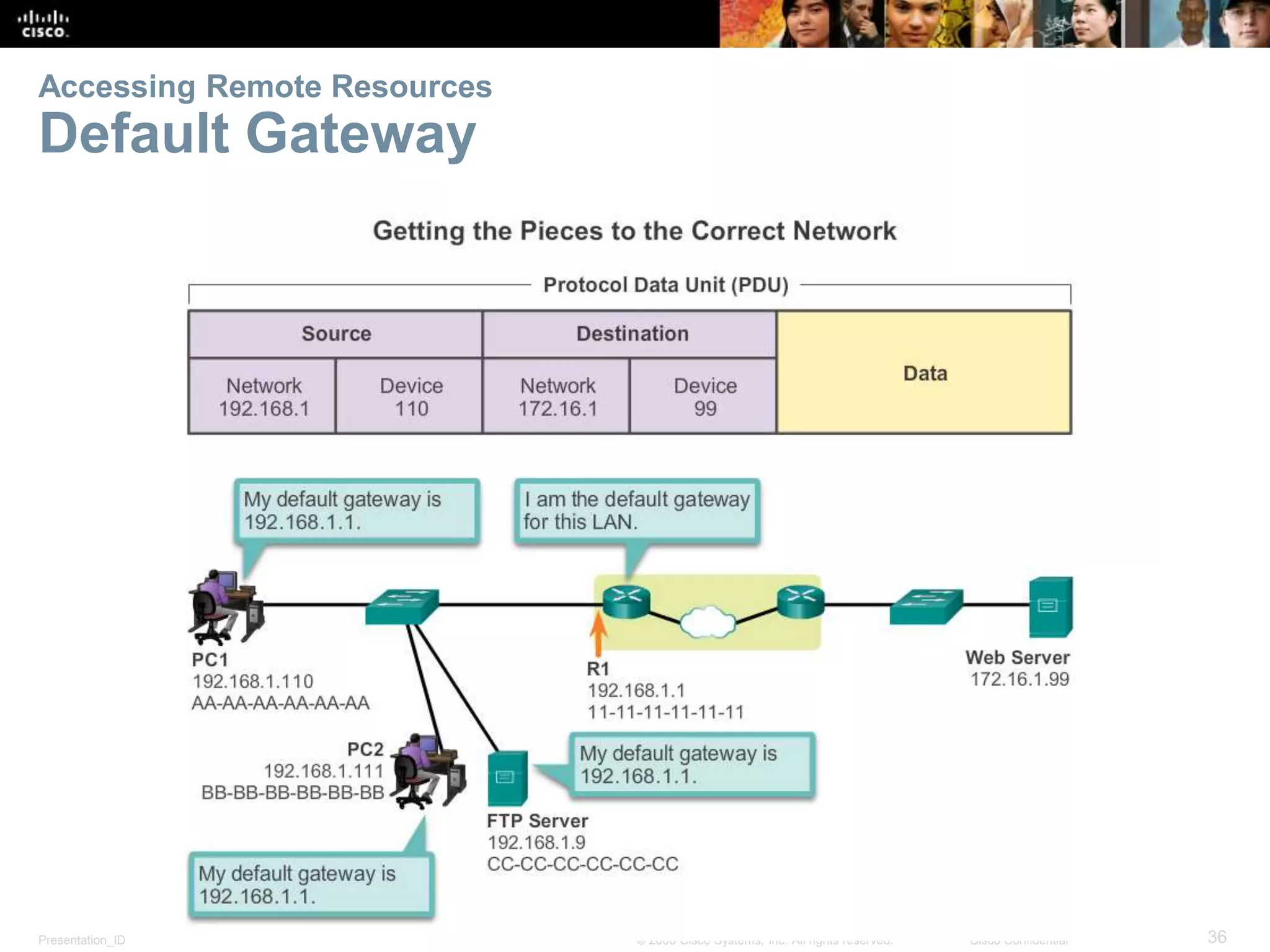
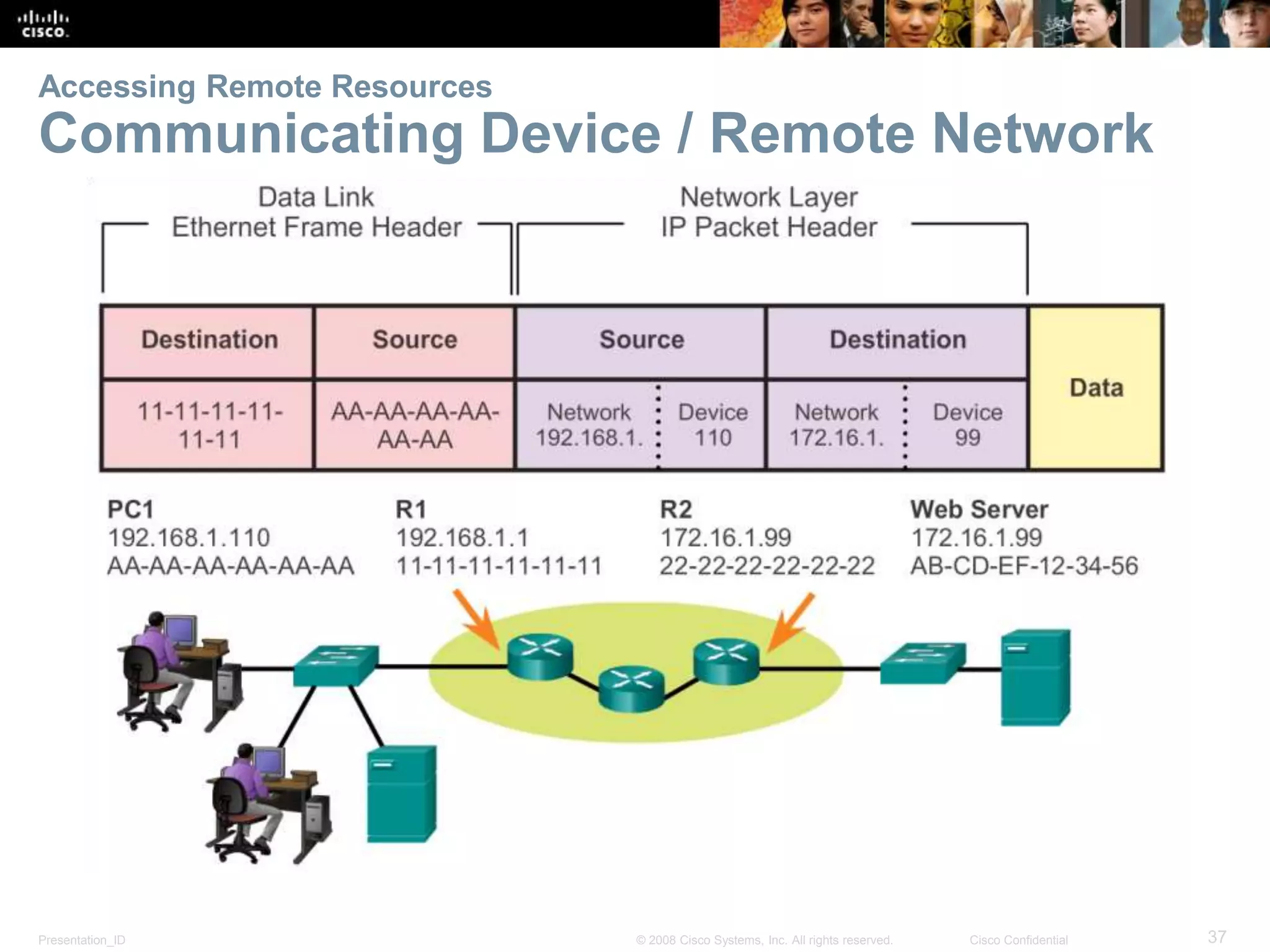
The document outlines the fundamentals of network protocols and communication, emphasizing the importance of rules and standards that facilitate data exchange. It discusses the TCP/IP protocol suite's development, the roles of various standards organizations, and how devices communicate within local and remote networks. Key concepts include data encapsulation, the OSI model, and how protocol data units (PDUs) function in network communications.