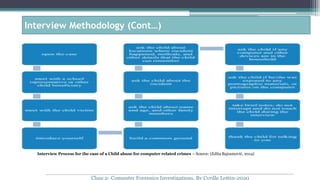
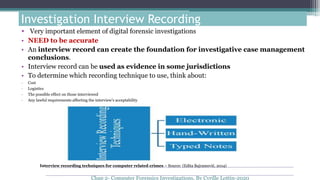
Investigation interviews are an important part of digital forensic investigations but require experience to obtain confessions. Before starting interviews, investigators must thoroughly research the facts of the case and background information on interview subjects. During interviews, investigators should carefully question subjects while following proper methodology and recording all discussions to maintain legal defensibility.