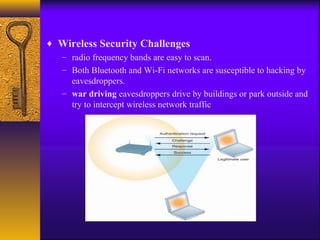
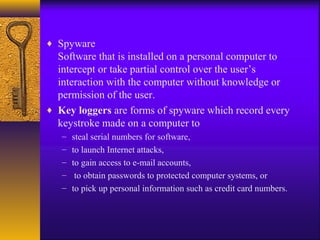
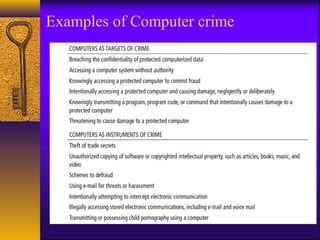
This document discusses information system security and computer-related issues. It covers topics like computer waste, crime, privacy and ethical issues. Specific types of computer waste and mistakes are examined, along with policies and procedures to prevent them. Computer crime is explored, including the computer as a tool for crime and as an object of crime. Issues like identity theft, cyberterrorism, and vulnerabilities are summarized. Internal threats from employees are also mentioned.