Report
Share
Recommended
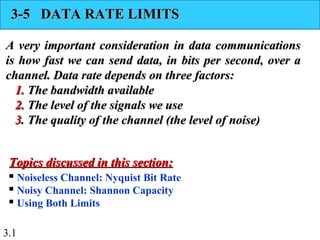
DATA RATE LIMITS

In this we discuss about DATA RATE LIMITS
Two theoretical formulas were developed to calculate the data rate:
Nyquist bit rate for a noiseless channel
BitRate = 2 * bandwidth * log 2 L
2: Shannon Capacity for a noisy channel
Capacity = bandwidth * log 2 (1 + SNR)
...............
PERFORMANCE (Network PERFORMANCE) :
Bandwidth: ( Bandwidth in Hertz and Bandwidth in Bits per Seconds) :
Throughput:
These above topics covered in this slide
Thanks You!
Network delay

What is network Delay?
Different type of network delay are explained in this powerpoint
Types of Load distributing algorithm in Distributed System

Types of Load Distributing Algorithms in Distributed System
1) Sender Initiated Load Distributing Algorithm
2) Receiver Initiated Load Distributing Algorithm
3) Symmetric Load Distributing Algorithm
4) Adaptive Load Distributing Algorithm
Quality of service

Contents:
Data Traffic
Congestion
Congestion Control
Quality of Service
Techniques to improve QOS
How QOS is implemented within the Internet
References..
Query processing in Distributed Database System

This is an PPT of DBMS. It include the following topic"Query processing in Distributed Database System".
Recommended
DATA RATE LIMITS

In this we discuss about DATA RATE LIMITS
Two theoretical formulas were developed to calculate the data rate:
Nyquist bit rate for a noiseless channel
BitRate = 2 * bandwidth * log 2 L
2: Shannon Capacity for a noisy channel
Capacity = bandwidth * log 2 (1 + SNR)
...............
PERFORMANCE (Network PERFORMANCE) :
Bandwidth: ( Bandwidth in Hertz and Bandwidth in Bits per Seconds) :
Throughput:
These above topics covered in this slide
Thanks You!
Network delay

What is network Delay?
Different type of network delay are explained in this powerpoint
Types of Load distributing algorithm in Distributed System

Types of Load Distributing Algorithms in Distributed System
1) Sender Initiated Load Distributing Algorithm
2) Receiver Initiated Load Distributing Algorithm
3) Symmetric Load Distributing Algorithm
4) Adaptive Load Distributing Algorithm
Quality of service

Contents:
Data Traffic
Congestion
Congestion Control
Quality of Service
Techniques to improve QOS
How QOS is implemented within the Internet
References..
Query processing in Distributed Database System

This is an PPT of DBMS. It include the following topic"Query processing in Distributed Database System".
Data communication and networks by B. Forouzan

In this ppt , We will discuss about the different type of networks and different type of Topologies . LAN, WAN , MAN and internet today .
Distributed system Tanenbaum chapter 1,2,3,4 notes 

Distributed system chapter 1,2,3,4 notes from Distributed system principle and paradigms Andrew s Tanenbaum book.
Cloud Computing Concepts - Peer to peer systems- Napster - Gnutella

P2P systems started emerging in the early 2000s, started with a variety of very popular systems such as #Napster and #Gnutella.
The first very large-scale distributed systems #Napster and #Gnutella had millions, tens of millions, in some cases hundreds of millions of clients communicate with each other at the same time.
Distributed system

DSM system
Shared memory
On chip memory
Bus based multiprocessor
Working through cache
Write through cache
Write once protocol
Ring based multiprocessor
Protocol used
Similarities and differences b\w ring based and bus based
Physical Layer Numericals - Data Communication & Networking

Data Communication & Networking - Physical Layer Numericals - Chapter 3 -Data and Signals
FOSS, history and philosophy

My presentation in software freedom day 2010. A typical introduction about the
Computer architecture virtual memory

Computer architecture virtual memory seminar
Mustansiriya University
Department of Education
Computer Science
Wireless Communication Networks and Systems 1st Edition Beard Solutions Manual

Full download : http://alibabadownload.com/product/wireless-communication-networks-and-systems-1st-edition-beard-solutions-manual/
Wireless Communication Networks and Systems 1st Edition Beard Solutions Manual
Digital Image Processing - Image Enhancement

Digital Image Processing - Image Enhancement (NOTES) Material or Tips for Engineering students ...................
More Related Content
What's hot
Data communication and networks by B. Forouzan

In this ppt , We will discuss about the different type of networks and different type of Topologies . LAN, WAN , MAN and internet today .
Distributed system Tanenbaum chapter 1,2,3,4 notes 

Distributed system chapter 1,2,3,4 notes from Distributed system principle and paradigms Andrew s Tanenbaum book.
Cloud Computing Concepts - Peer to peer systems- Napster - Gnutella

P2P systems started emerging in the early 2000s, started with a variety of very popular systems such as #Napster and #Gnutella.
The first very large-scale distributed systems #Napster and #Gnutella had millions, tens of millions, in some cases hundreds of millions of clients communicate with each other at the same time.
Distributed system

DSM system
Shared memory
On chip memory
Bus based multiprocessor
Working through cache
Write through cache
Write once protocol
Ring based multiprocessor
Protocol used
Similarities and differences b\w ring based and bus based
Physical Layer Numericals - Data Communication & Networking

Data Communication & Networking - Physical Layer Numericals - Chapter 3 -Data and Signals
FOSS, history and philosophy

My presentation in software freedom day 2010. A typical introduction about the
Computer architecture virtual memory

Computer architecture virtual memory seminar
Mustansiriya University
Department of Education
Computer Science
Wireless Communication Networks and Systems 1st Edition Beard Solutions Manual

Full download : http://alibabadownload.com/product/wireless-communication-networks-and-systems-1st-edition-beard-solutions-manual/
Wireless Communication Networks and Systems 1st Edition Beard Solutions Manual
Digital Image Processing - Image Enhancement

Digital Image Processing - Image Enhancement (NOTES) Material or Tips for Engineering students ...................
What's hot (20)
Distributed system Tanenbaum chapter 1,2,3,4 notes 

Distributed system Tanenbaum chapter 1,2,3,4 notes
Cloud Computing Concepts - Peer to peer systems- Napster - Gnutella

Cloud Computing Concepts - Peer to peer systems- Napster - Gnutella
Physical Layer Numericals - Data Communication & Networking

Physical Layer Numericals - Data Communication & Networking
Wireless Communication Networks and Systems 1st Edition Beard Solutions Manual

Wireless Communication Networks and Systems 1st Edition Beard Solutions Manual
Basics of data communication and computer networking (262 kb)

Basics of data communication and computer networking (262 kb)
Similar to Ch3 4 v1
Data Communication & Computer network: Channel capacity

These slides cover the fundamentals of data communication & networking. It covers Channel Capacity It is useful for engineering students & also for the candidates who want to master data communication & computer networking.
Chap3

To be transmitted, data must be transformed to electromagnetic signals
Data can be analog or digital. Analog data are continuous and take continuous values. Digital data have discrete states and take on discrete values.
Signals can be analog or digital. Analog signals can have an infinite number of values in a range; digital signals can have only a limited number of values.
Data Communication Principles

This slide covers the brief introduction to signals, Conversion(ADC, DAC ) and Multiplexing techniques
ch3-1-v1-14102022-105042pm.ppt

Data and signals are fundamental concepts in the field of communication and information technology. In general, data refers to any information that can be represented in a digital format, while a signal is an analog or digital representation of data that can be transmitted over a communication channel.
There are many ways to present data and signals, and the choice depends on the specific application and requirements of the system. In this answer, we will discuss some common methods used for data and signal presentation.
Analog Signals:
Analog signals are continuous and can take any value within a certain range. Examples of analog signals include sound waves, voltage or current signals in electrical circuits, and temperature measurements. Analog signals can be presented graphically using waveform plots or oscilloscopes. The amplitude of the signal is plotted on the vertical axis, while time is plotted on the horizontal axis.
Digital Signals:
Digital signals, on the other hand, are discrete and take on only a finite set of values. These values are represented by binary digits (bits), which can take on the values of 0 or 1. Digital signals are used in many digital communication systems, such as computers, telecommunication networks, and the internet. Digital signals can be presented in several ways, such as waveform plots, histograms, and eye diagrams.
Textual Data:
Textual data refers to data that is represented by characters, such as letters, numbers, and symbols. Textual data can be presented in many ways, such as plain text, tables, spreadsheets, and databases. Textual data can also be formatted in different ways, such as font size, style, and color.
Graphical Data:
Graphical data refers to data that is presented in a graphical form, such as charts, graphs, and diagrams. Graphical data is commonly used to represent trends, patterns, and relationships between different variables. Common types of graphical data include bar charts, line graphs, scatter plots, and pie charts.
Multimedia Data:
Multimedia data refers to data that includes various types of media, such as images, videos, and audio. Multimedia data can be presented in many different formats, such as JPEG, MPEG, and WAV. Multimedia data can also be compressed and transmitted over networks using various compression techniques, such as JPEG compression and MP3 compression.
In conclusion, data and signals can be presented in many ways, depending on the specific application and requirements of the system. The choice of presentation method will depend on factors such as the type of data or signal being presented, the accuracy and resolution required, and the constraints of the communication system.
Similar to Ch3 4 v1 (20)
Data Rate Limits A class element for university student

Data Rate Limits A class element for university student
Data Communication & Computer network: Channel capacity

Data Communication & Computer network: Channel capacity
More from sayyed sabir
Automatic door using arduino

code for this project
int in1 = 2;
int in2 = 3;
int sensor = 8;
int led = 13;
void setup()
{
pinMode(in1, OUTPUT);
pinMode(in2, OUTPUT);
pinMode(sensor, INPUT);
pinMode(led, OUTPUT);
digitalWrite(in1,LOW);
digitalWrite(in2,LOW);
//digitalWrite(sensor,LOW);
digitalWrite(led,LOW);
while(millis()<13000)
{
digitalWrite(led,HIGH);
delay(500);
digitalWrite(led,LOW);
delay(500);
}
digitalWrite(led,LOW);
digitalWrite(in1,LOW);
digitalWrite(in2,HIGH);
}
void loop()
{
if(digitalRead(sensor)==HIGH)
{
digitalWrite(in1,HIGH);
digitalWrite(in2,LOW);
digitalWrite(led,HIGH);
delay(1500);
digitalWrite(in1,LOW);
digitalWrite(in2,LOW);
digitalWrite(in1,LOW);
digitalWrite(in2,HIGH);
digitalWrite(led,LOW);
delay(1500);
digitalWrite(in1,LOW);
digitalWrite(in2,LOW);
}
}
More from sayyed sabir (20)
Recently uploaded
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

In today's fast-changing business world, Companies that adapt and embrace new ideas often need help to keep up with the competition. However, fostering a culture of innovation takes much work. It takes vision, leadership and willingness to take risks in the right proportion. Sachin Dev Duggal, co-founder of Builder.ai, has perfected the art of this balance, creating a company culture where creativity and growth are nurtured at each stage.
UiPath Test Automation using UiPath Test Suite series, part 4

Welcome to UiPath Test Automation using UiPath Test Suite series part 4. In this session, we will cover Test Manager overview along with SAP heatmap.
The UiPath Test Manager overview with SAP heatmap webinar offers a concise yet comprehensive exploration of the role of a Test Manager within SAP environments, coupled with the utilization of heatmaps for effective testing strategies.
Participants will gain insights into the responsibilities, challenges, and best practices associated with test management in SAP projects. Additionally, the webinar delves into the significance of heatmaps as a visual aid for identifying testing priorities, areas of risk, and resource allocation within SAP landscapes. Through this session, attendees can expect to enhance their understanding of test management principles while learning practical approaches to optimize testing processes in SAP environments using heatmap visualization techniques
What will you get from this session?
1. Insights into SAP testing best practices
2. Heatmap utilization for testing
3. Optimization of testing processes
4. Demo
Topics covered:
Execution from the test manager
Orchestrator execution result
Defect reporting
SAP heatmap example with demo
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on the notifications, alerts, and approval requests using Slack for Bonterra Impact Management. The solutions covered in this webinar can also be deployed for Microsoft Teams.
Interested in deploying notification automations for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
Connector Corner: Automate dynamic content and events by pushing a button

Here is something new! In our next Connector Corner webinar, we will demonstrate how you can use a single workflow to:
Create a campaign using Mailchimp with merge tags/fields
Send an interactive Slack channel message (using buttons)
Have the message received by managers and peers along with a test email for review
But there’s more:
In a second workflow supporting the same use case, you’ll see:
Your campaign sent to target colleagues for approval
If the “Approve” button is clicked, a Jira/Zendesk ticket is created for the marketing design team
But—if the “Reject” button is pushed, colleagues will be alerted via Slack message
Join us to learn more about this new, human-in-the-loop capability, brought to you by Integration Service connectors.
And...
Speakers:
Akshay Agnihotri, Product Manager
Charlie Greenberg, Host
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
JMeter webinar - integration with InfluxDB and Grafana

Watch this recorded webinar about real-time monitoring of application performance. See how to integrate Apache JMeter, the open-source leader in performance testing, with InfluxDB, the open-source time-series database, and Grafana, the open-source analytics and visualization application.
In this webinar, we will review the benefits of leveraging InfluxDB and Grafana when executing load tests and demonstrate how these tools are used to visualize performance metrics.
Length: 30 minutes
Session Overview
-------------------------------------------
During this webinar, we will cover the following topics while demonstrating the integrations of JMeter, InfluxDB and Grafana:
- What out-of-the-box solutions are available for real-time monitoring JMeter tests?
- What are the benefits of integrating InfluxDB and Grafana into the load testing stack?
- Which features are provided by Grafana?
- Demonstration of InfluxDB and Grafana using a practice web application
To view the webinar recording, go to:
https://www.rttsweb.com/jmeter-integration-webinar
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

As AI technology is pushing into IT I was wondering myself, as an “infrastructure container kubernetes guy”, how get this fancy AI technology get managed from an infrastructure operational view? Is it possible to apply our lovely cloud native principals as well? What benefit’s both technologies could bring to each other?
Let me take this questions and provide you a short journey through existing deployment models and use cases for AI software. On practical examples, we discuss what cloud/on-premise strategy we may need for applying it to our own infrastructure to get it to work from an enterprise perspective. I want to give an overview about infrastructure requirements and technologies, what could be beneficial or limiting your AI use cases in an enterprise environment. An interactive Demo will give you some insides, what approaches I got already working for real.
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

“AGI should be open source and in the public domain at the service of humanity and the planet.”
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
Search and Society: Reimagining Information Access for Radical Futures

The field of Information retrieval (IR) is currently undergoing a transformative shift, at least partly due to the emerging applications of generative AI to information access. In this talk, we will deliberate on the sociotechnical implications of generative AI for information access. We will argue that there is both a critical necessity and an exciting opportunity for the IR community to re-center our research agendas on societal needs while dismantling the artificial separation between the work on fairness, accountability, transparency, and ethics in IR and the rest of IR research. Instead of adopting a reactionary strategy of trying to mitigate potential social harms from emerging technologies, the community should aim to proactively set the research agenda for the kinds of systems we should build inspired by diverse explicitly stated sociotechnical imaginaries. The sociotechnical imaginaries that underpin the design and development of information access technologies needs to be explicitly articulated, and we need to develop theories of change in context of these diverse perspectives. Our guiding future imaginaries must be informed by other academic fields, such as democratic theory and critical theory, and should be co-developed with social science scholars, legal scholars, civil rights and social justice activists, and artists, among others.
"Impact of front-end architecture on development cost", Viktor Turskyi

I have heard many times that architecture is not important for the front-end. Also, many times I have seen how developers implement features on the front-end just following the standard rules for a framework and think that this is enough to successfully launch the project, and then the project fails. How to prevent this and what approach to choose? I have launched dozens of complex projects and during the talk we will analyze which approaches have worked for me and which have not.
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
PHP Frameworks: I want to break free (IPC Berlin 2024)

In this presentation, we examine the challenges and limitations of relying too heavily on PHP frameworks in web development. We discuss the history of PHP and its frameworks to understand how this dependence has evolved. The focus will be on providing concrete tips and strategies to reduce reliance on these frameworks, based on real-world examples and practical considerations. The goal is to equip developers with the skills and knowledge to create more flexible and future-proof web applications. We'll explore the importance of maintaining autonomy in a rapidly changing tech landscape and how to make informed decisions in PHP development.
This talk is aimed at encouraging a more independent approach to using PHP frameworks, moving towards a more flexible and future-proof approach to PHP development.
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
Knowledge engineering: from people to machines and back

Keynote at the 21st European Semantic Web Conference
Recently uploaded (20)
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...
UiPath Test Automation using UiPath Test Suite series, part 4

UiPath Test Automation using UiPath Test Suite series, part 4
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...
FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf

FIDO Alliance Osaka Seminar: Passkeys at Amazon.pdf
Connector Corner: Automate dynamic content and events by pushing a button

Connector Corner: Automate dynamic content and events by pushing a button
GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...

GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using Deplo...
JMeter webinar - integration with InfluxDB and Grafana

JMeter webinar - integration with InfluxDB and Grafana
Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024

Kubernetes & AI - Beauty and the Beast !?! @KCD Istanbul 2024
GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...

GenAISummit 2024 May 28 Sri Ambati Keynote: AGI Belongs to The Community in O...
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
Search and Society: Reimagining Information Access for Radical Futures

Search and Society: Reimagining Information Access for Radical Futures
"Impact of front-end architecture on development cost", Viktor Turskyi

"Impact of front-end architecture on development cost", Viktor Turskyi
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
PHP Frameworks: I want to break free (IPC Berlin 2024)

PHP Frameworks: I want to break free (IPC Berlin 2024)
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
Knowledge engineering: from people to machines and back

Knowledge engineering: from people to machines and back
Ch3 4 v1
- 1. 3.1 3-5 DATA RATE LIMITS3-5 DATA RATE LIMITS A very important consideration in data communicationsA very important consideration in data communications is how fast we can send data, in bits per second, over ais how fast we can send data, in bits per second, over a channel. Data rate depends on three factors:channel. Data rate depends on three factors: 1.1. The bandwidth availableThe bandwidth available 2.2. The level of the signals we useThe level of the signals we use 33. The quality of the channel (the level of noise). The quality of the channel (the level of noise) Noiseless Channel: Nyquist Bit Rate Noisy Channel: Shannon Capacity Using Both Limits Topics discussed in this section:Topics discussed in this section:
- 2. 3.2 Increasing the levels of a signal increases the probability of an error occurring, in other words it reduces the reliability of the system. Why?? Note
- 3. 3.3 Capacity of a System The bit rate of a system increases with an increase in the number of signal levels we use to denote a symbol. A symbol can consist of a single bit or “n” bits. The number of signal levels = 2n . As the number of levels goes up, the spacing between level decreases -> increasing the probability of an error occurring in the presence of transmission impairments.
- 4. 3.4 Nyquist Theorem Nyquist gives the upper bound for the bit rate of a transmission system by calculating the bit rate directly from the number of bits in a symbol (or signal levels) and the bandwidth of the system (assuming 2 symbols/per cycle and first harmonic). Nyquist theorem states that for a noiseless channel: C = 2 B log22n C= capacity in bps B = bandwidth in Hz
- 5. 3.5 Does the Nyquist theorem bit rate agree with the intuitive bit rate described in baseband transmission? Solution They match when we have only two levels. We said, in baseband transmission, the bit rate is 2 times the bandwidth if we use only the first harmonic in the worst case. However, the Nyquist formula is more general than what we derived intuitively; it can be applied to baseband transmission and modulation. Also, it can be applied when we have two or more levels of signals. Example 3.33
- 6. 3.6 Consider a noiseless channel with a bandwidth of 3000 Hz transmitting a signal with two signal levels. The maximum bit rate can be calculated as Example 3.34
- 7. 3.7 Consider the same noiseless channel transmitting a signal with four signal levels (for each level, we send 2 bits). The maximum bit rate can be calculated as Example 3.35
- 8. 3.8 We need to send 265 kbps over a noiseless channel with a bandwidth of 20 kHz. How many signal levels do we need? Solution We can use the Nyquist formula as shown: Example 3.36 Since this result is not a power of 2, we need to either increase the number of levels or reduce the bit rate. If we have 128 levels, the bit rate is 280 kbps. If we have 64 levels, the bit rate is 240 kbps.
- 9. 3.9 Shannon’s Theorem Shannon’s theorem gives the capacity of a system in the presence of noise. C = B log2(1 + SNR)
- 10. 3.10 Consider an extremely noisy channel in which the value of the signal-to-noise ratio is almost zero. In other words, the noise is so strong that the signal is faint. For this channel the capacity C is calculated as Example 3.37 This means that the capacity of this channel is zero regardless of the bandwidth. In other words, we cannot receive any data through this channel.
- 11. 3.11 We can calculate the theoretical highest bit rate of a regular telephone line. A telephone line normally has a bandwidth of 3000. The signal-to-noise ratio is usually 3162. For this channel the capacity is calculated as Example 3.38 This means that the highest bit rate for a telephone line is 34.860 kbps. If we want to send data faster than this, we can either increase the bandwidth of the line or improve the signal-to-noise ratio.
- 12. 3.12 The signal-to-noise ratio is often given in decibels. Assume that SNRdB = 36 and the channel bandwidth is 2 MHz. The theoretical channel capacity can be calculated as Example 3.39
- 13. 3.13 For practical purposes, when the SNR is very high, we can assume that SNR + 1 is almost the same as SNR. In these cases, the theoretical channel capacity can be simplified to Example 3.40 For example, we can calculate the theoretical capacity of the previous example as
- 14. 3.14 We have a channel with a 1-MHz bandwidth. The SNR for this channel is 63. What are the appropriate bit rate and signal level? Solution First, we use the Shannon formula to find the upper limit. Example 3.41
- 15. 3.15 The Shannon formula gives us 6 Mbps, the upper limit. For better performance we choose something lower, 4 Mbps, for example. Then we use the Nyquist formula to find the number of signal levels. Example 3.41 (continued)
- 16. 3.16 The Shannon capacity gives us the upper limit; the Nyquist formula tells us how many signal levels we need. Note
