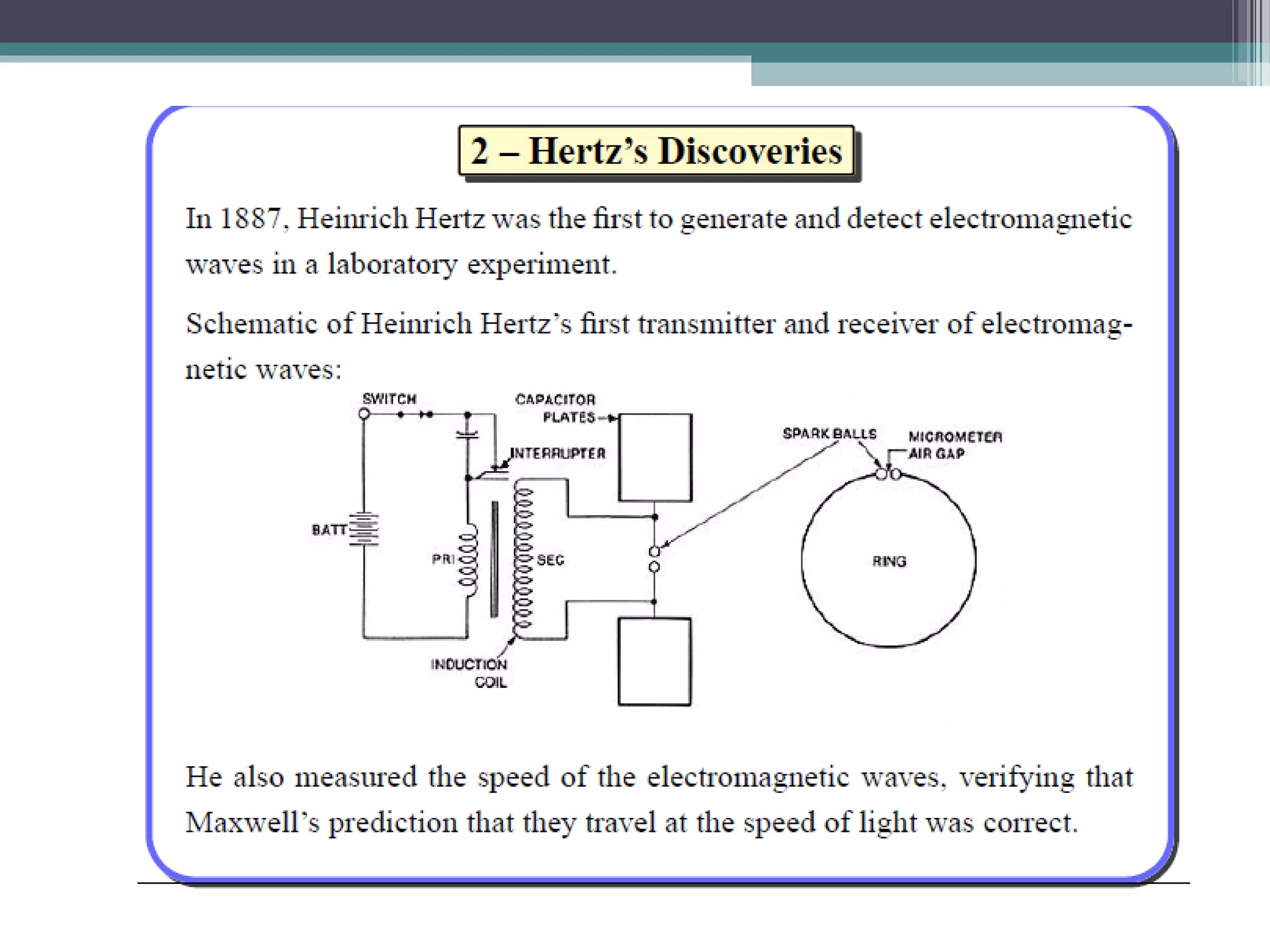
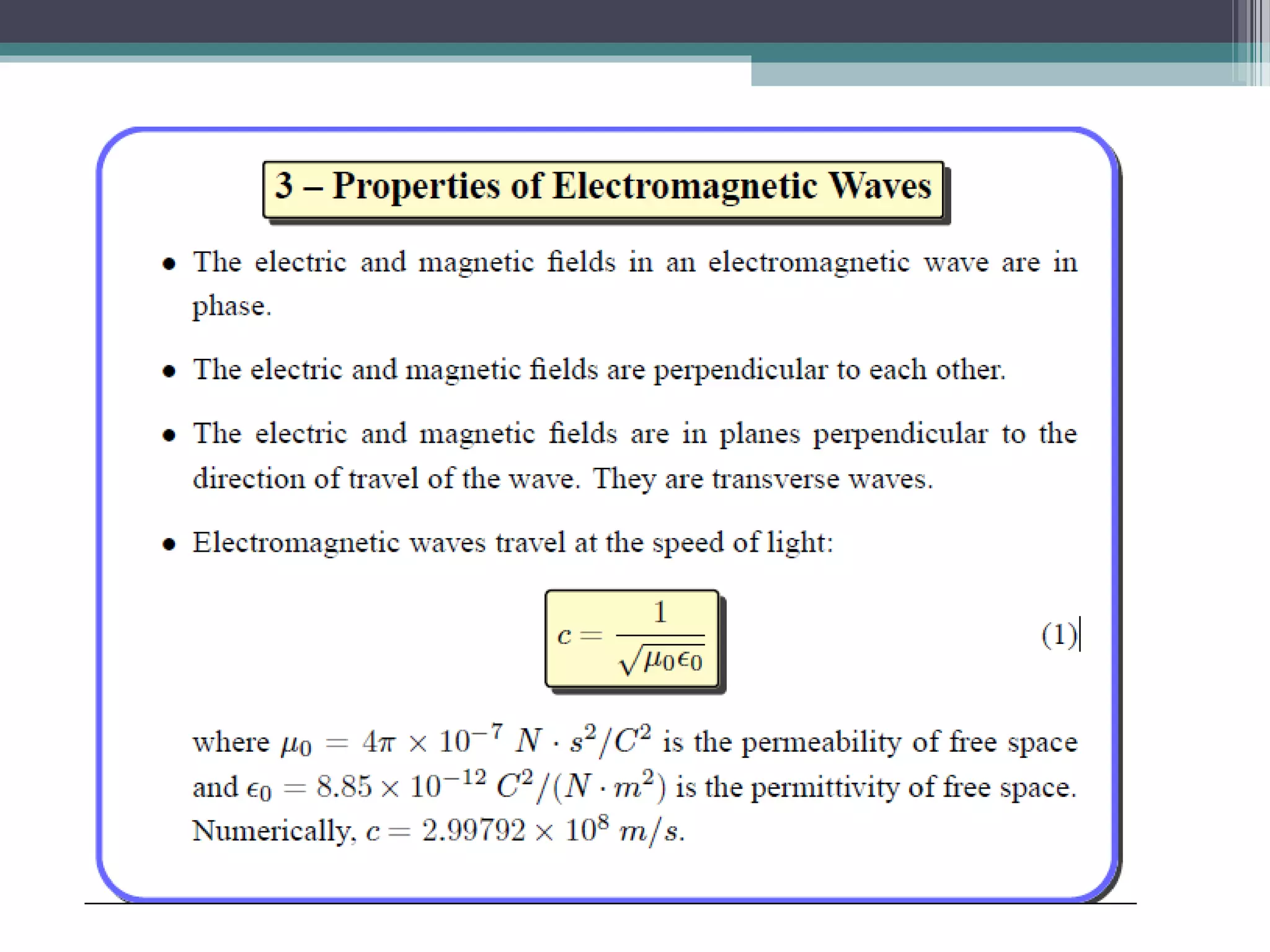
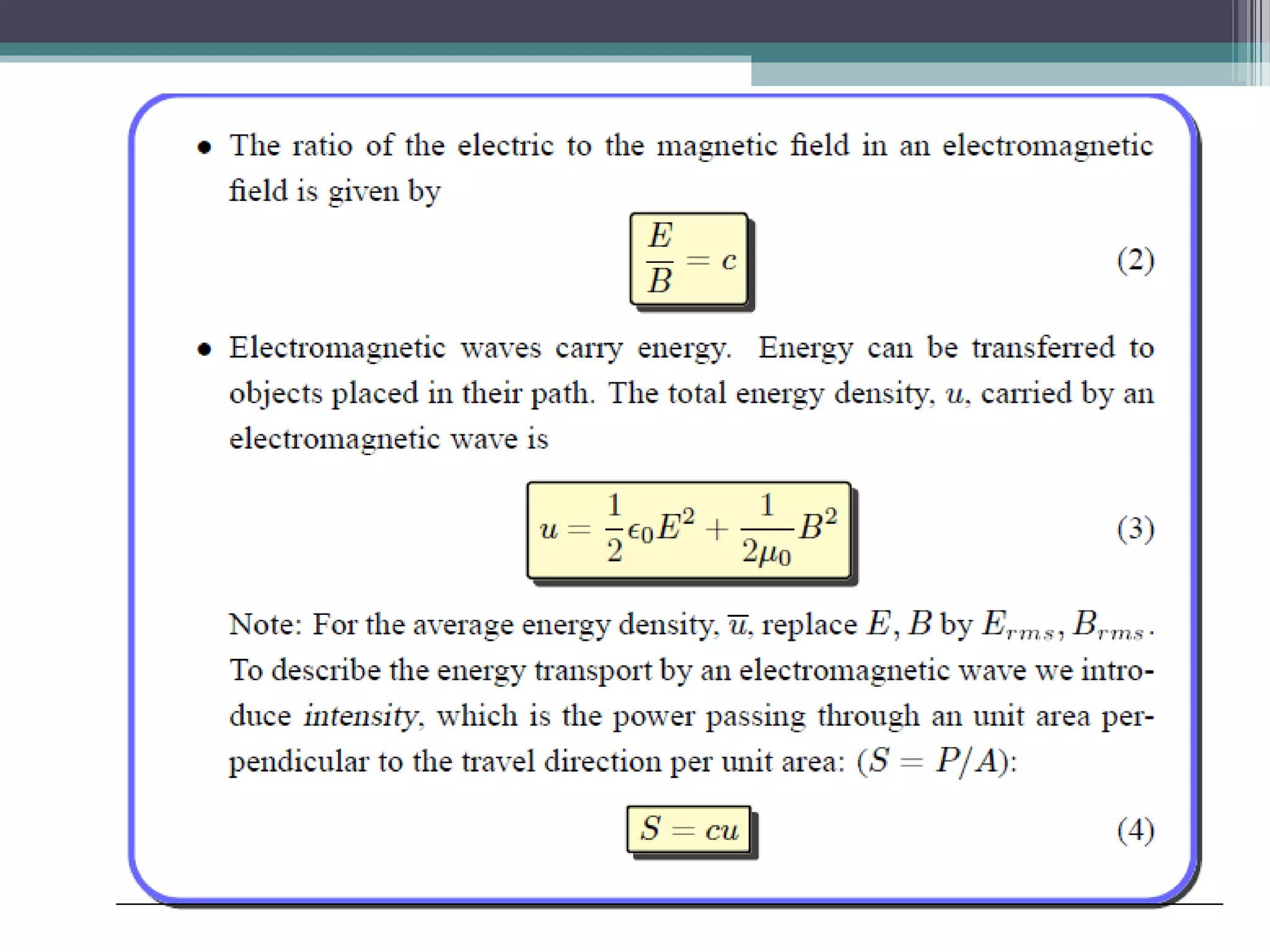
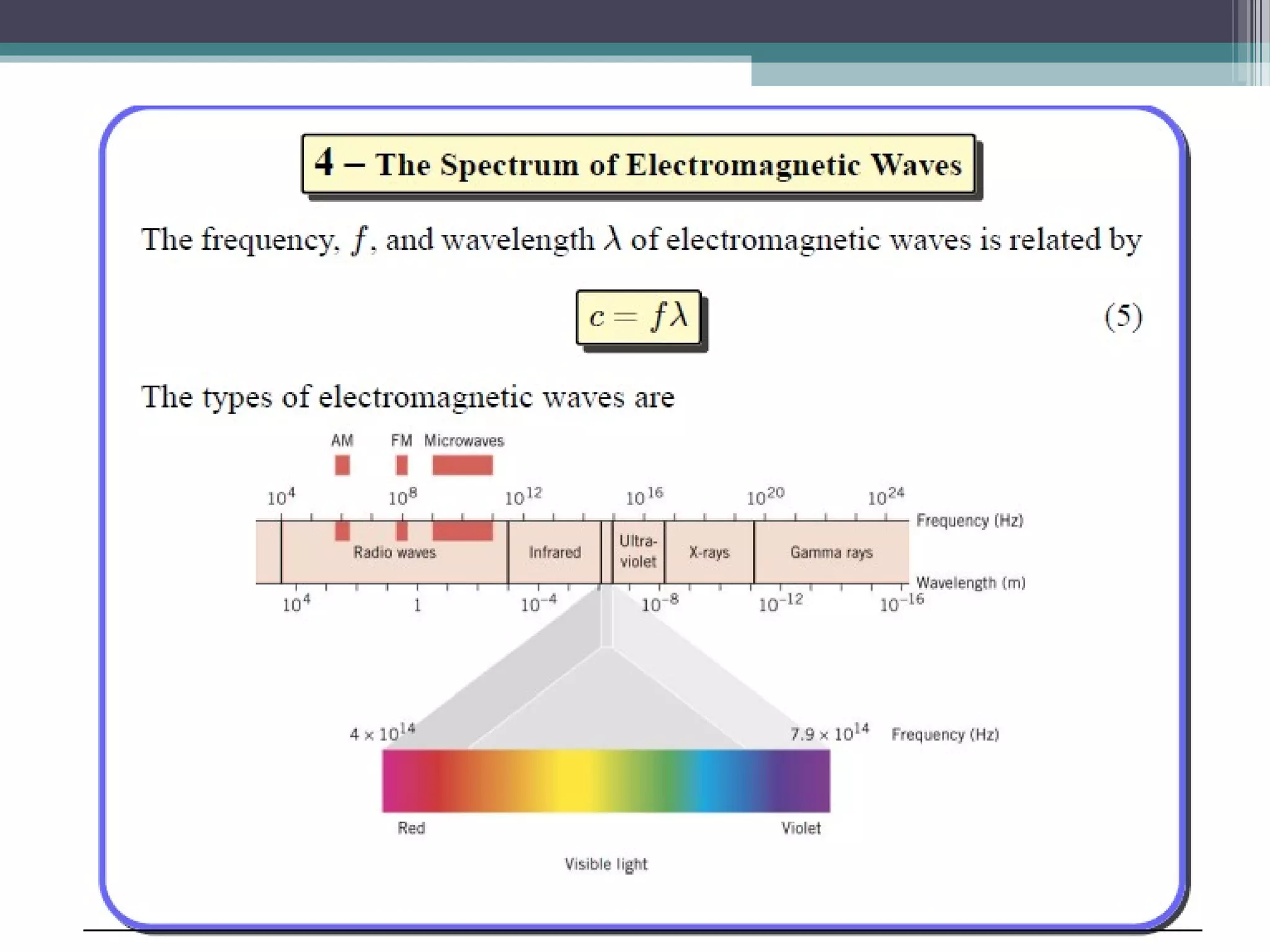
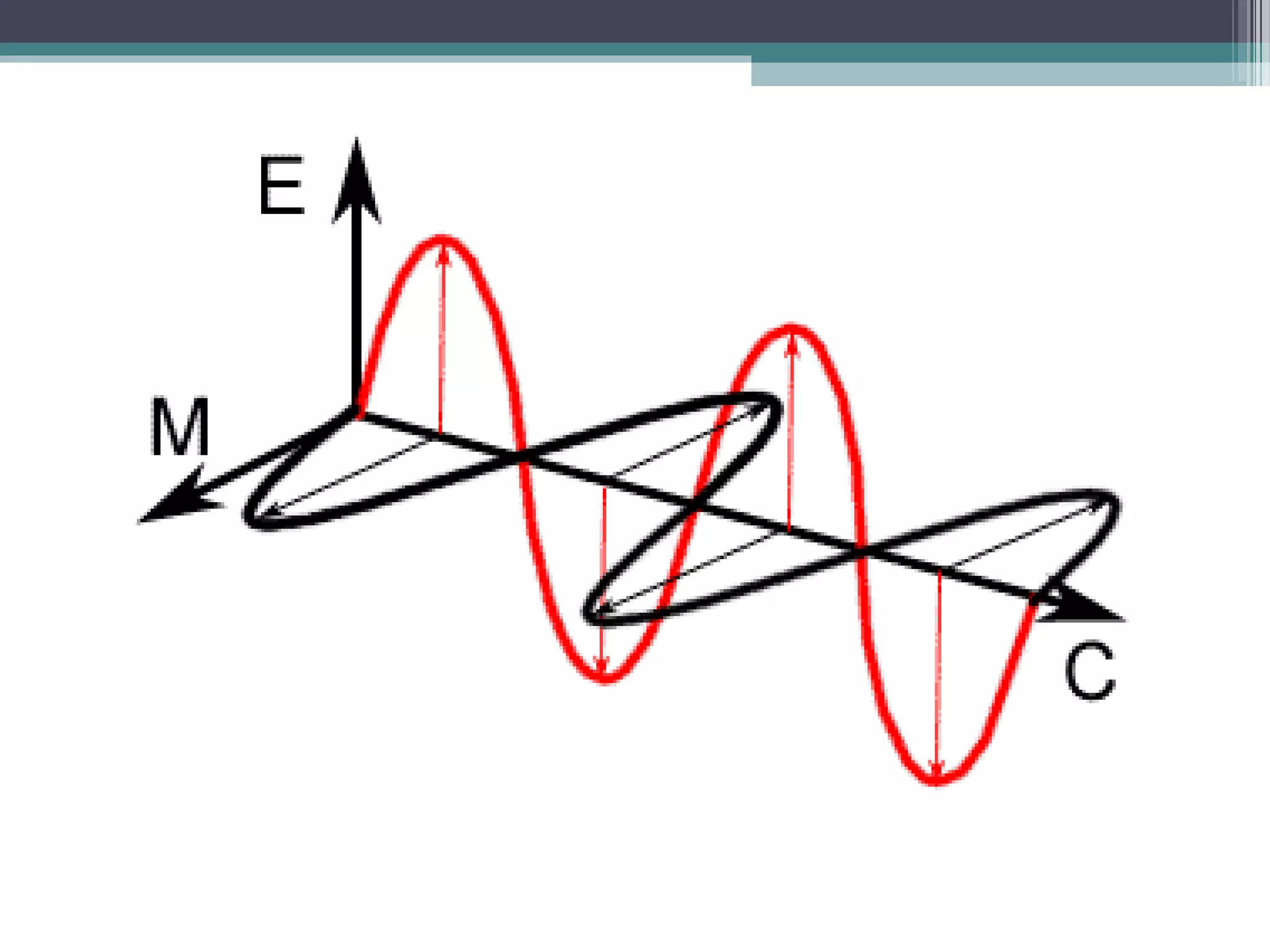
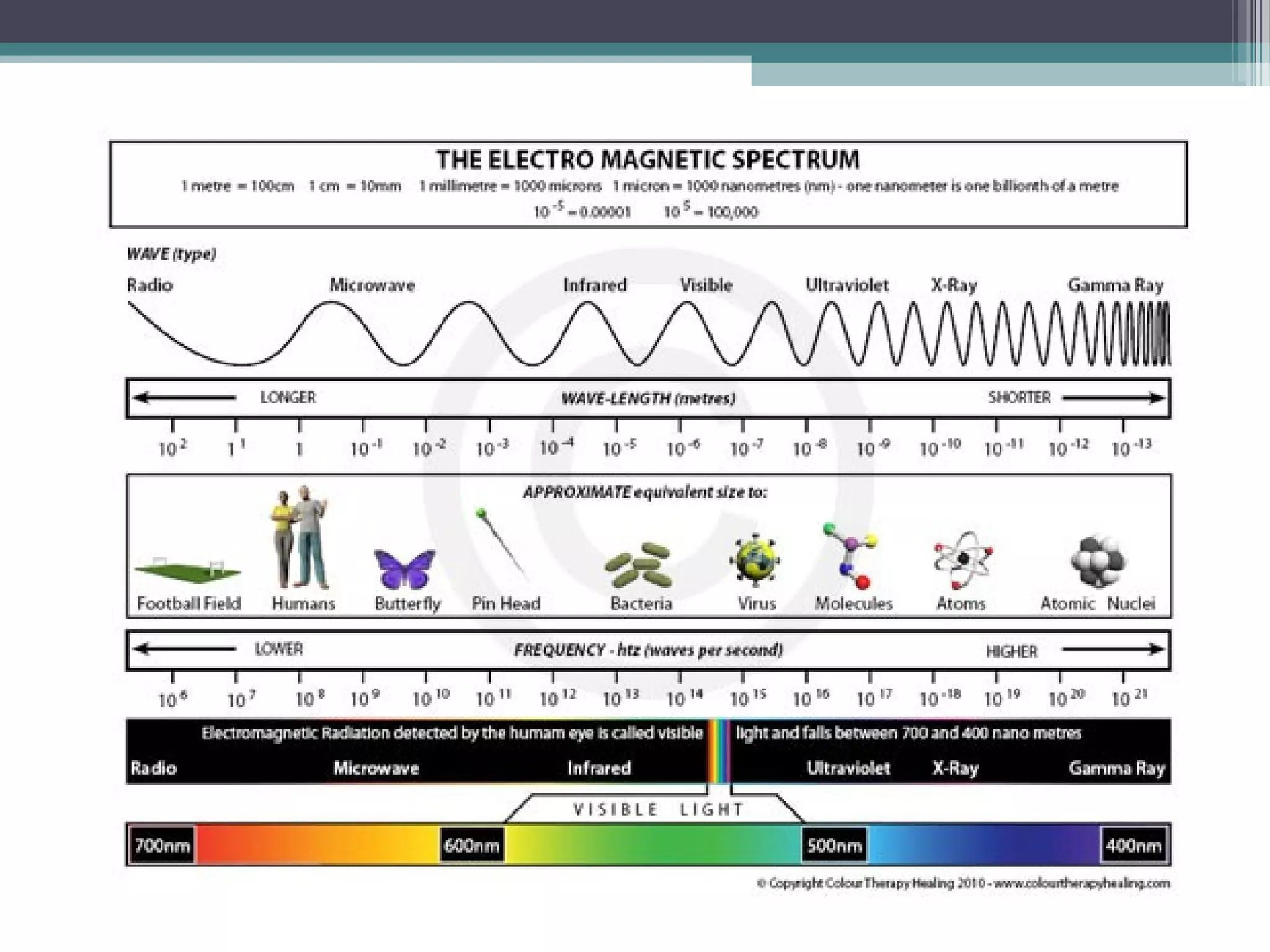
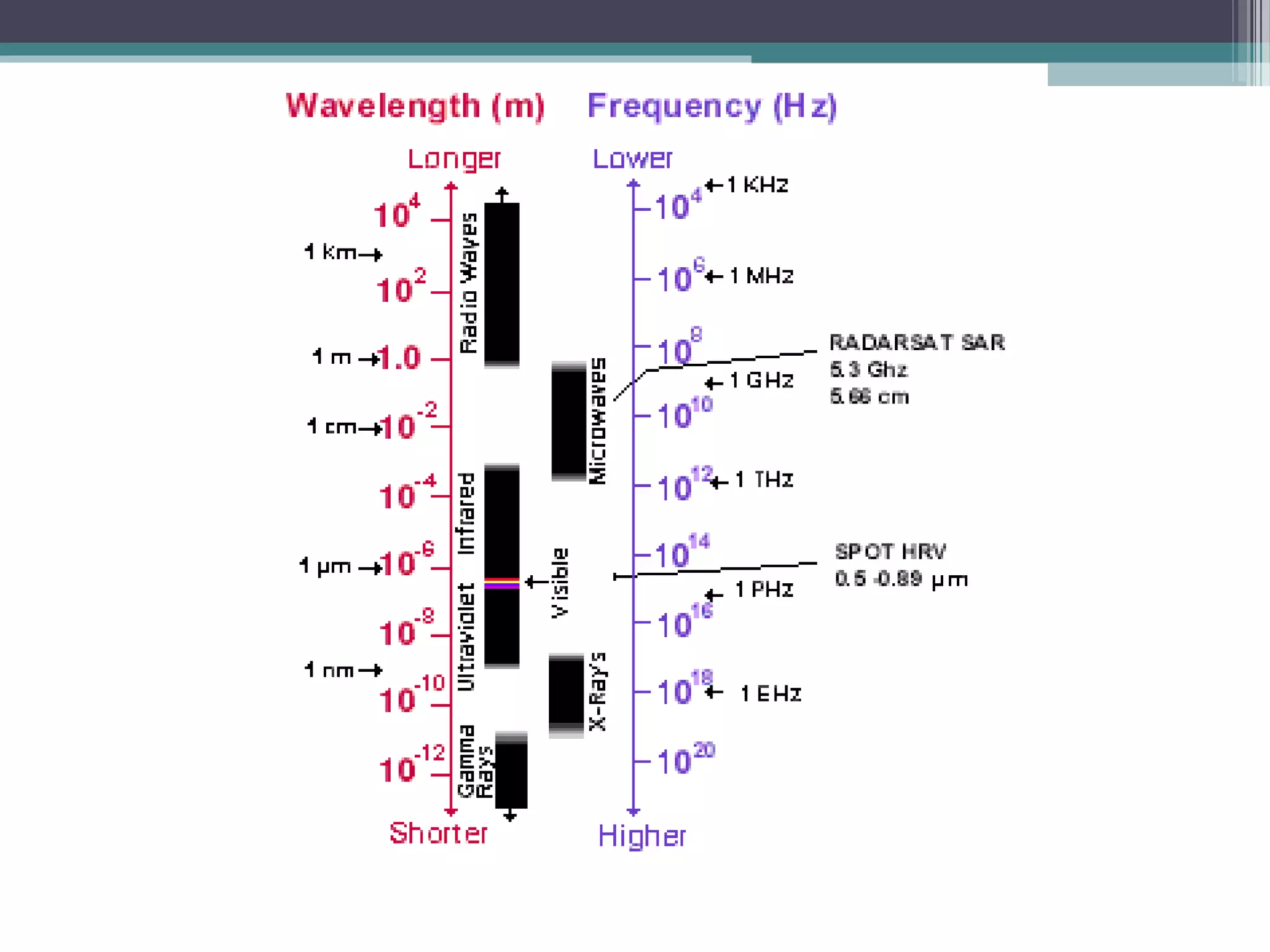
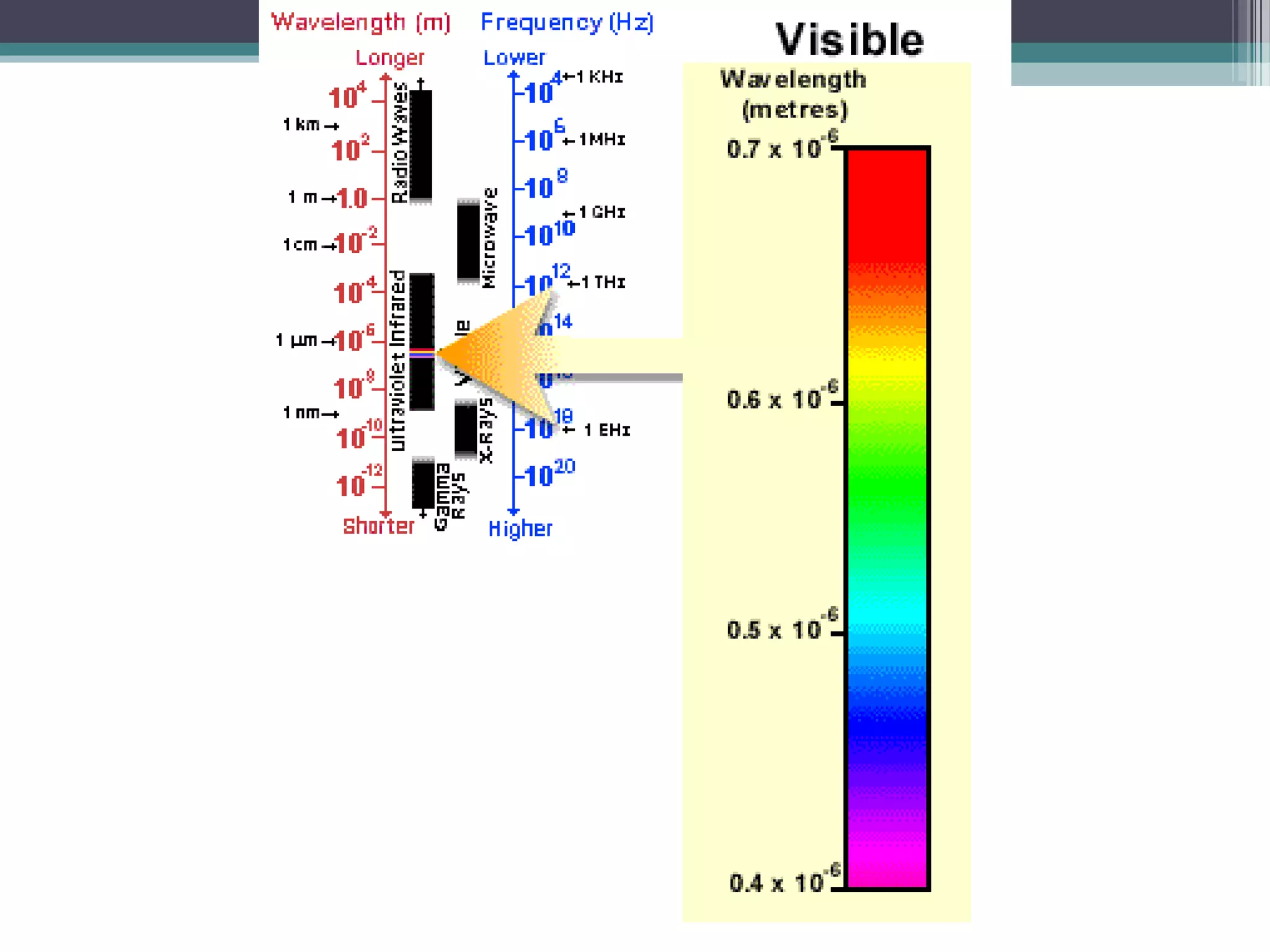
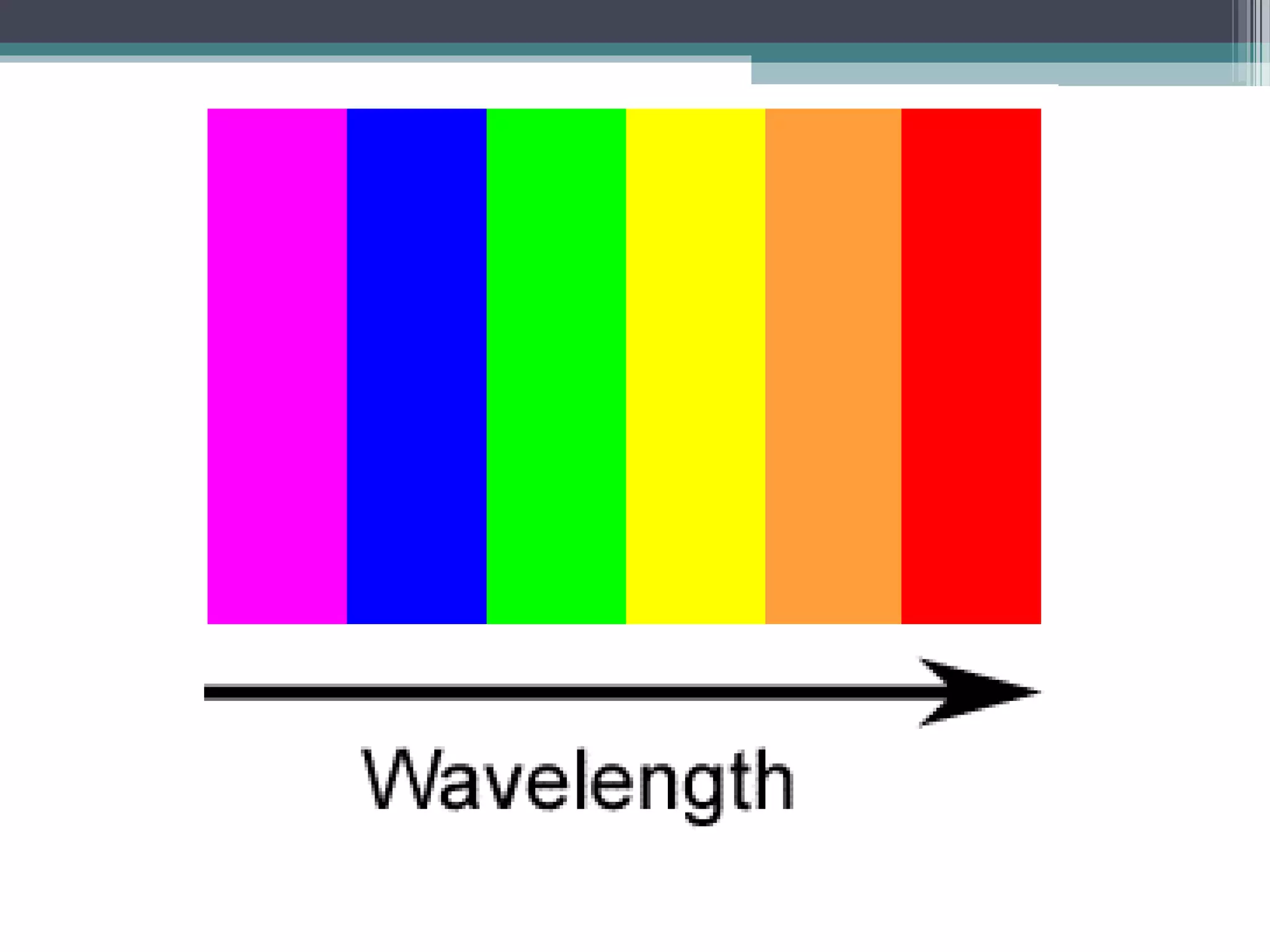
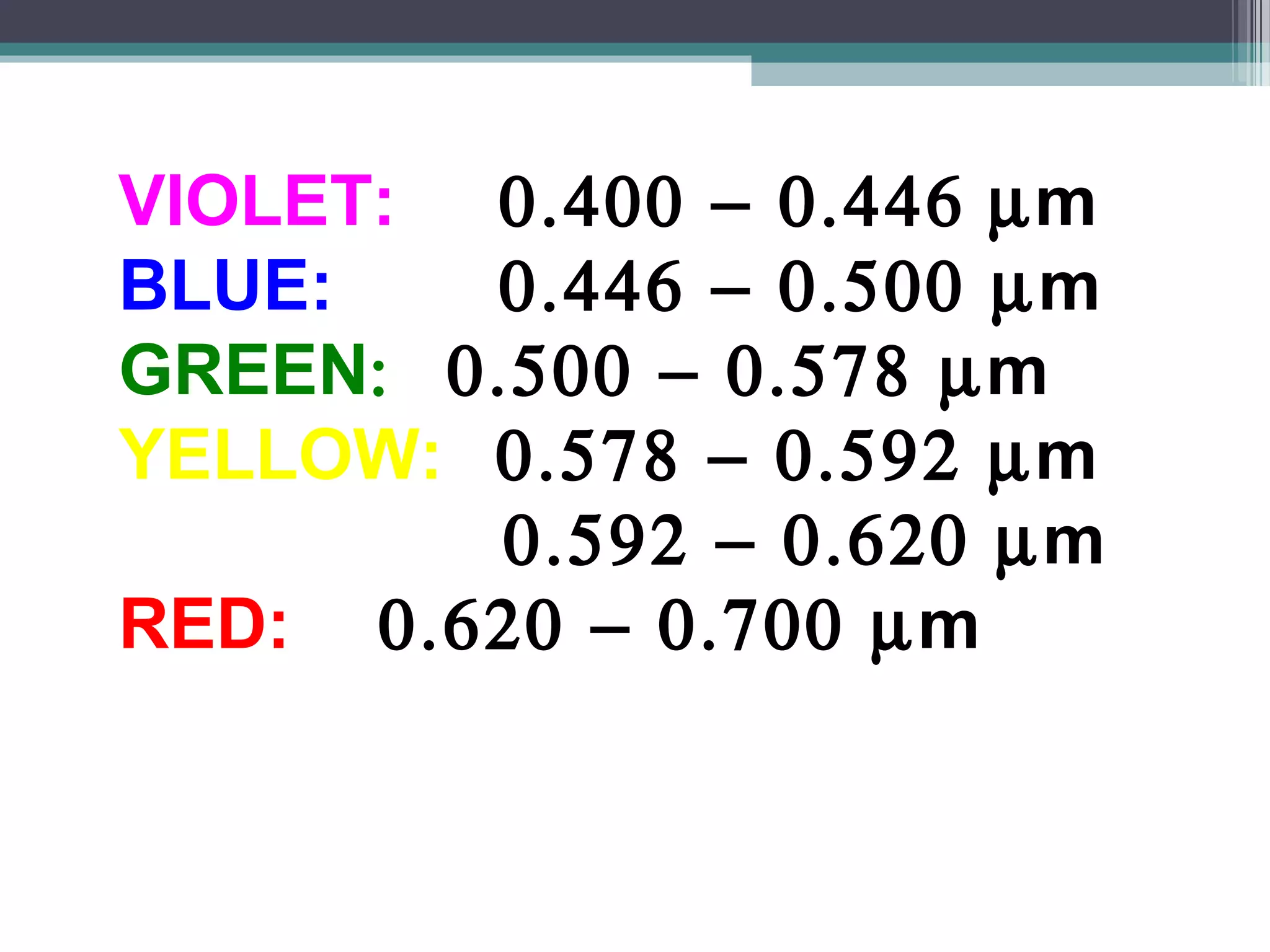
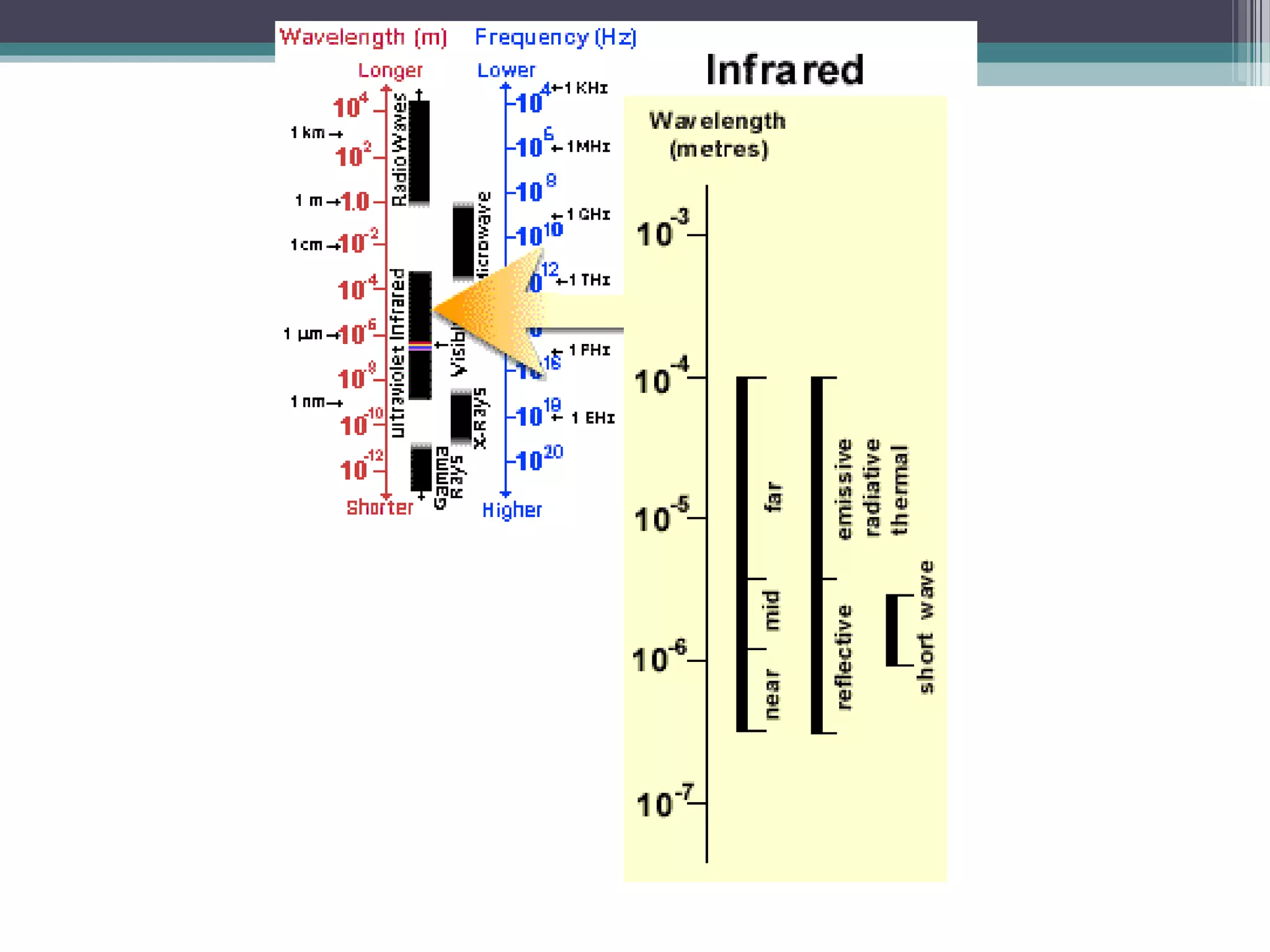
This document discusses microwaves and electromagnetic radiation. It defines microwaves as electromagnetic waves with frequencies between 500 MHz and 300 GHz. Microwaves are used for communication, radar, and heating. The document also discusses the electromagnetic spectrum and different types of electromagnetic radiation such as visible light, infrared, ultraviolet, x-rays, and radio waves. It notes hazards of electromagnetic radiation to personnel, ordnance, and fuel.