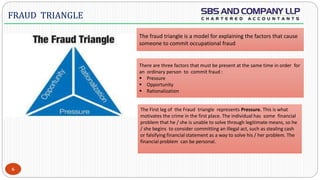
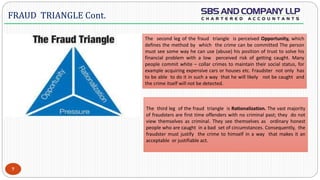
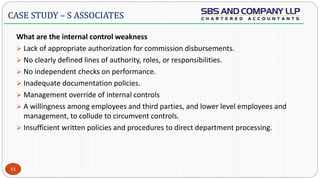
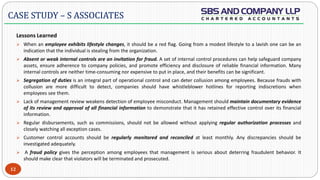
The document provides details about a case study on forensic audit. It discusses what forensic audit is, types of fraud, the fraud triangle model, and the Satyam fraud case. The Satyam case involved falsified financial statements, inflated revenues and profits, fake bank balances and fixed deposits totaling Rs. 7,800 crores. Weak internal controls and governance failures at Satyam such as unethical conduct, false books, dubious roles of directors, auditors and banks allowed the fraud to occur and go undetected for years.