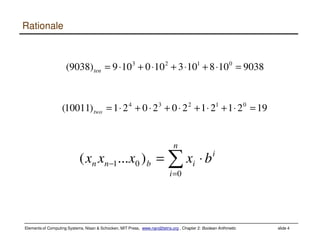
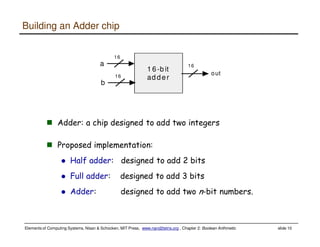
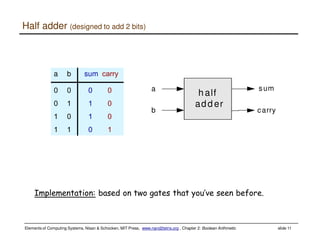
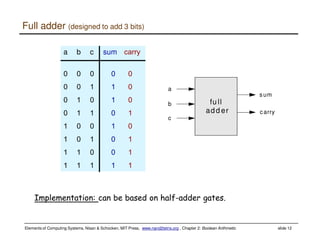
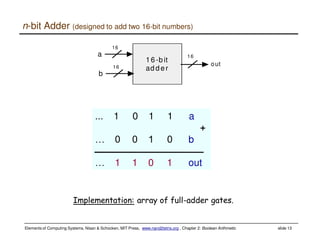
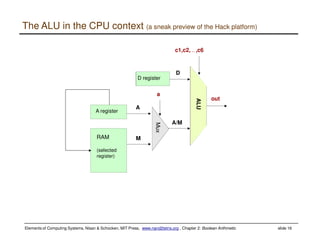
This document discusses Boolean arithmetic and the design of an adder chip. It explains how half adders and full adders can be used to build an n-bit adder to add two binary numbers. The document also introduces the arithmetic logic unit (ALU) and how it can perform operations like addition, subtraction, AND, and OR using control bits and the logic of half and full adders. The ALU is a key component of the central processing unit (CPU) that allows computers to perform arithmetic and logical operations on data.