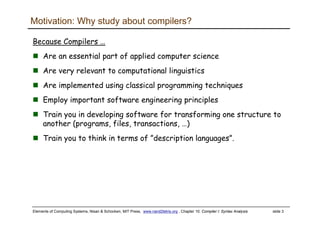
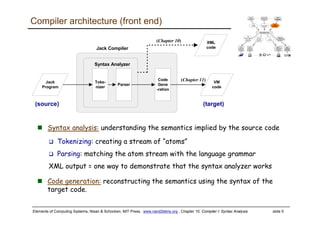
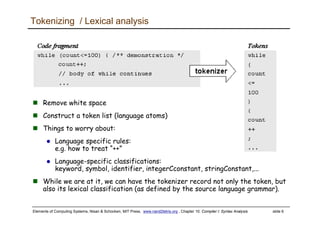
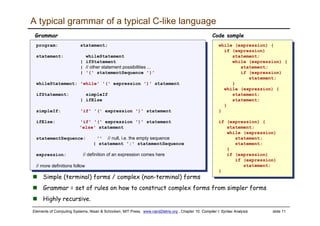
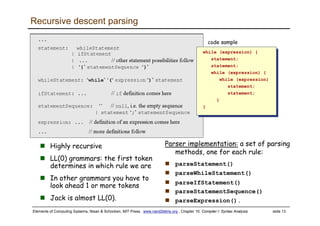
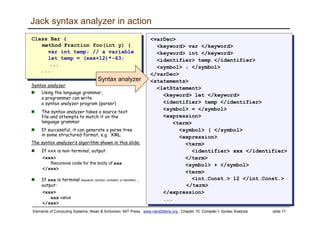
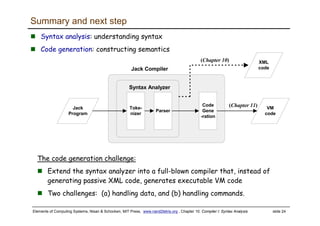
The document discusses the syntax analysis phase of compilers. It introduces tokenizing, which breaks source code into individual tokens, and parsing, which checks that the tokens conform to the language's grammar. It provides examples of Jack code being tokenized and parsed. The parsing process involves matching tokens to rules in a grammar using a recursive descent parser. The output of syntax analysis is typically a parse tree that represents the structural relationship between tokens. The document outlines proposed implementations for a Jack tokenizer and parser that would perform syntax analysis on Jack code and output an XML representation of the parse tree.