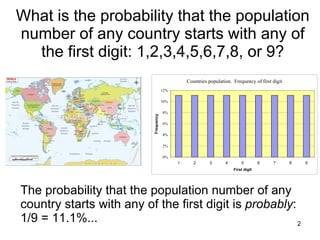
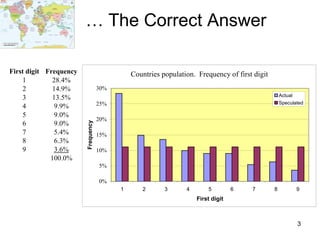
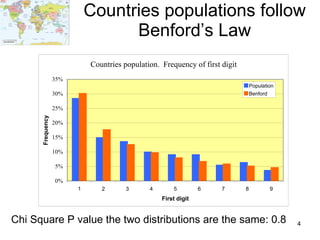
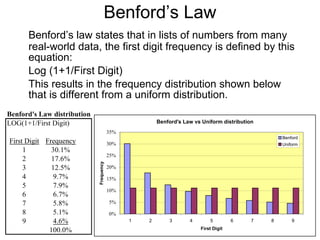
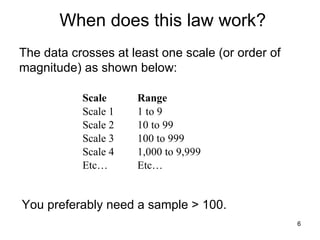
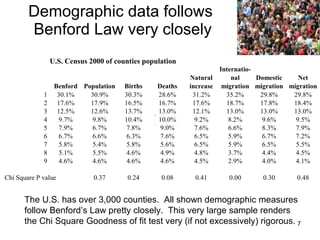
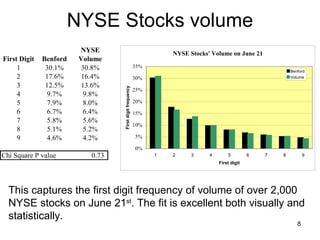
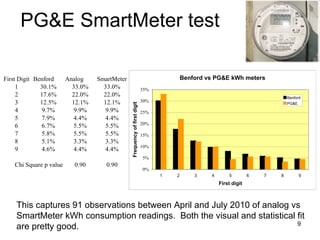
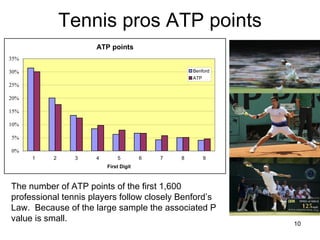
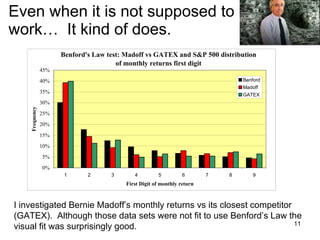
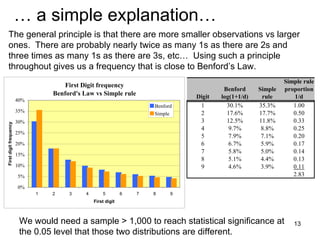
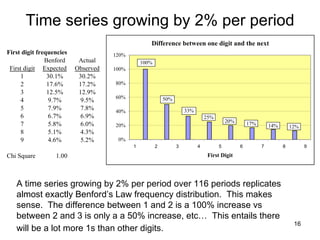
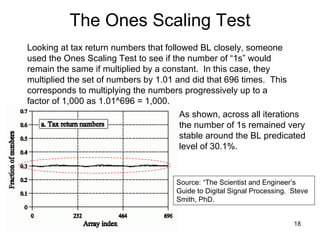
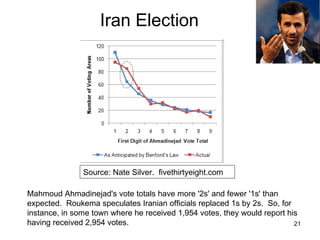
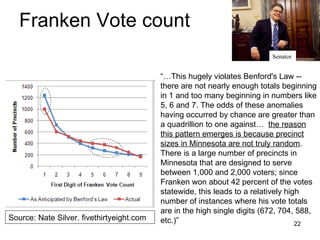
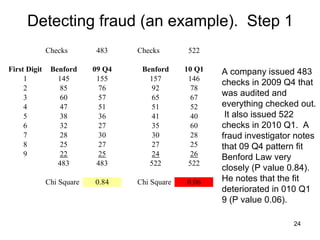
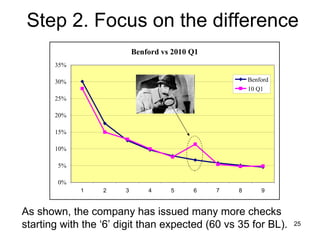
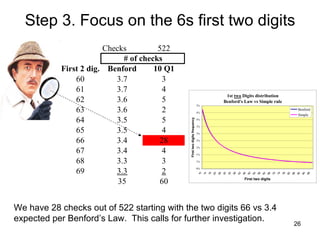
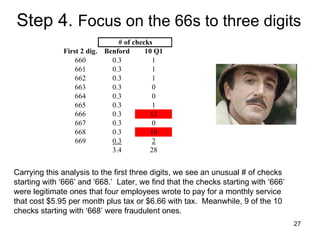
Benford's law states that in many real-world data sets, the distribution of first digits is not uniform, but rather follows a specific logarithmic pattern. This document discusses how Benford's law can be applied to detect anomalies and potential fraud in data sets involving areas like political elections, tax returns, insurance claims, and financial records. Specific examples are given showing how analyzing deviations from Benford's law helped uncover cases of electoral fraud, accounting fraud, and check fraud involving millions of dollars. The key is that Benford's law helps identify unexpected patterns within data that are worth further investigation for potential fraudulent activities.