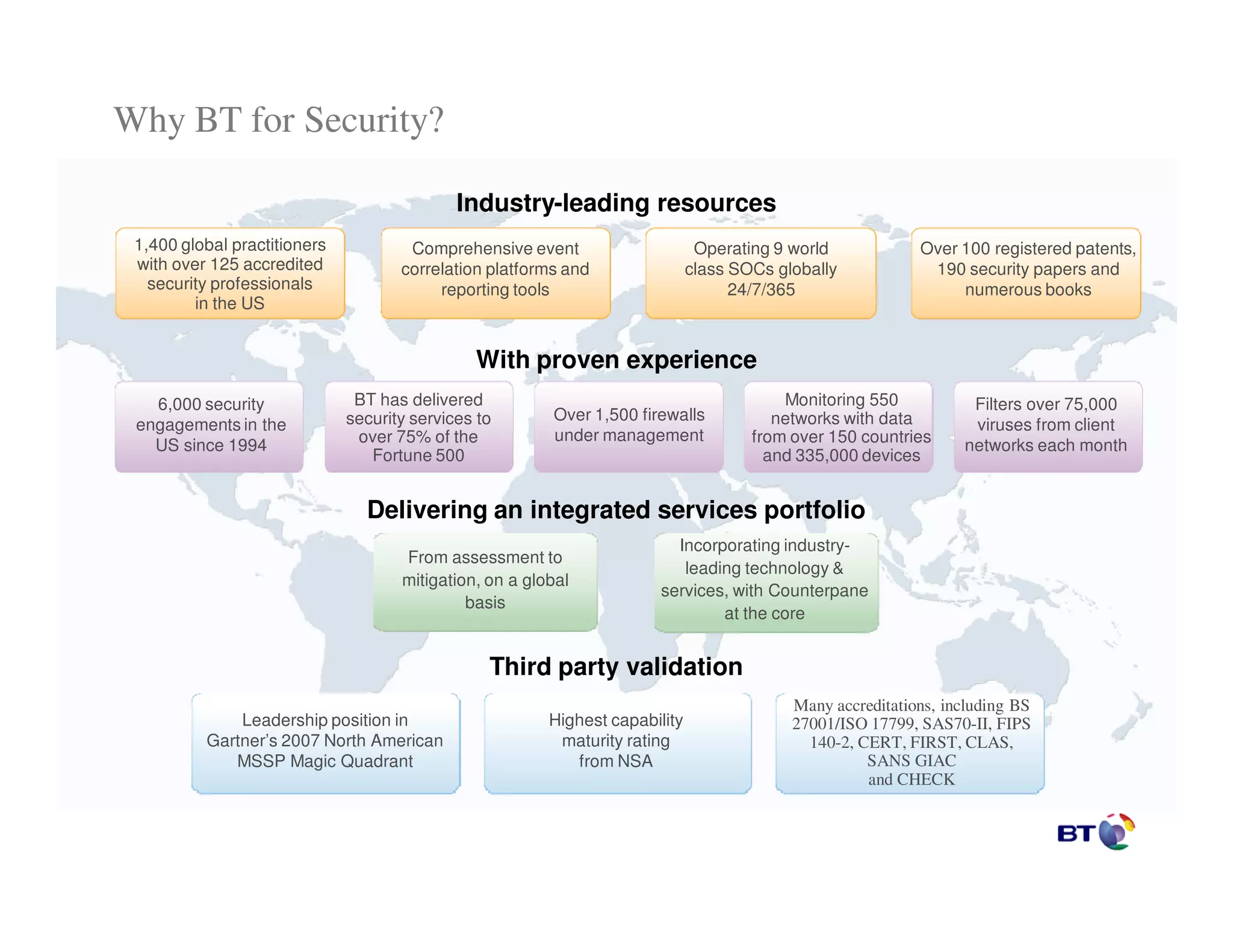
The document outlines the extensive security services provided by a leading firm, emphasizing its global reach, comprehensive monitoring capabilities, and numerous industry accreditations. It highlights the firm's experience with over 1,500 clients, utilizing advanced technology and operational practices to manage and protect networks effectively. Additionally, the firm has a strong reputation in the cybersecurity sector, supported by numerous security papers and a portfolio of patents.