The document provides information about assembly language and computer memory modes. It discusses:
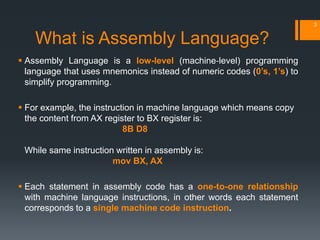
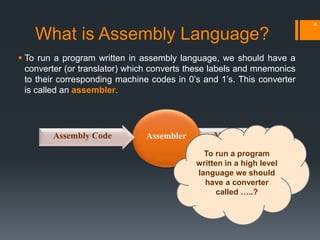
- What assembly language is and how it corresponds to machine code through an assembler.
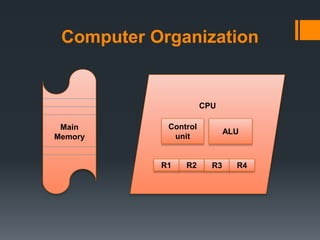
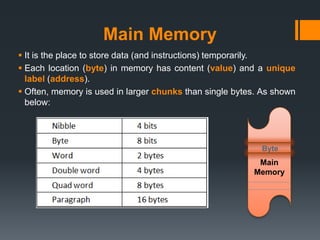
- Computer organization including main memory, CPU, registers, and ALU.
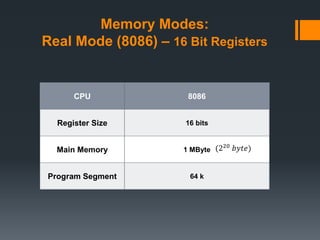
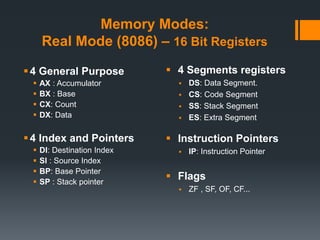
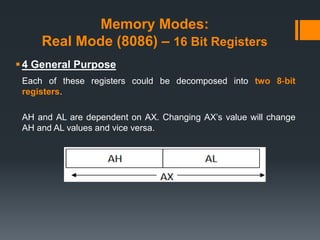
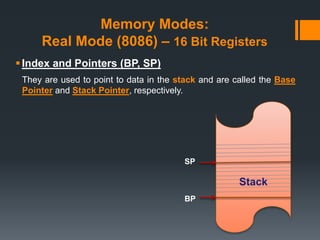
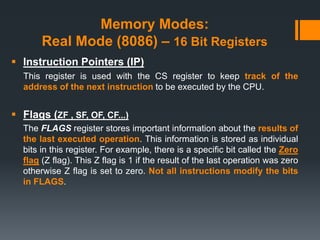
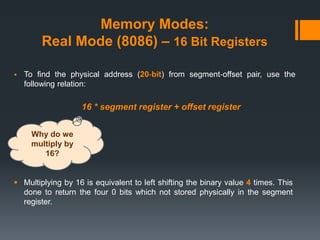
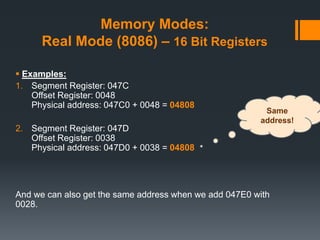
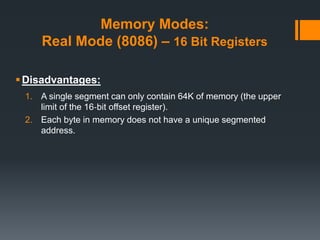
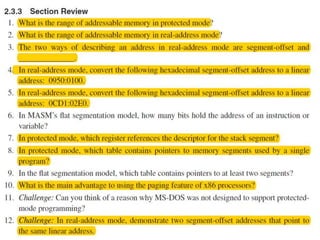
- Memory modes for the 8086 CPU including 16-bit registers and limitations of the 1MB real mode.
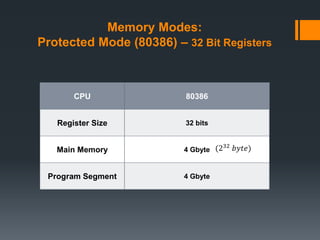
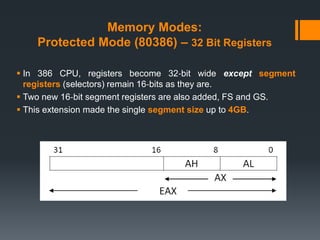
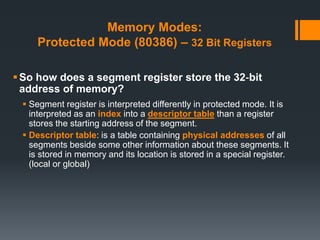
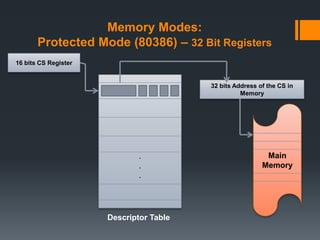
- Memory modes for the 80386 CPU including 32-bit registers, protected mode, descriptor tables, and virtual memory allowing 4GB program segments through page-based segmentation.