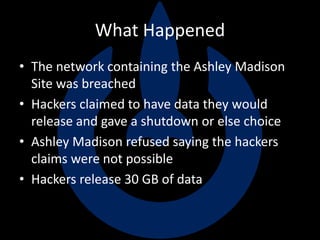
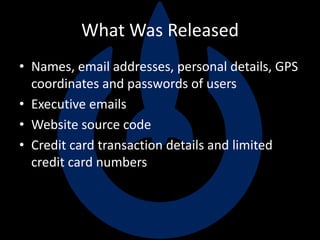
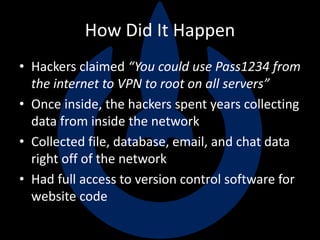
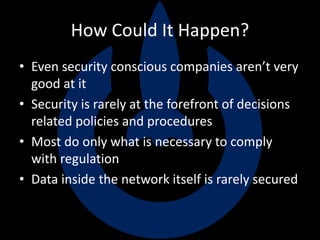
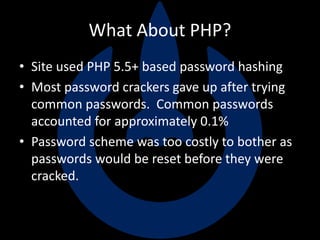
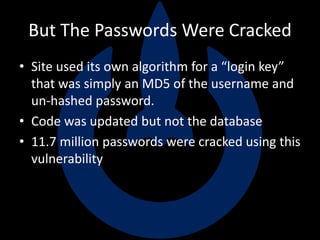
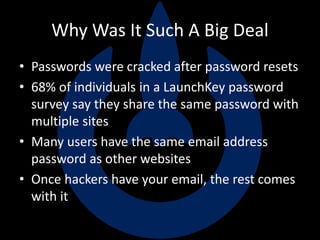
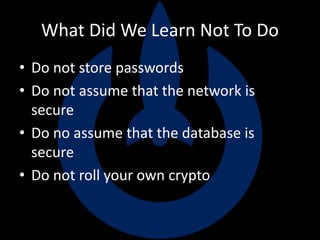
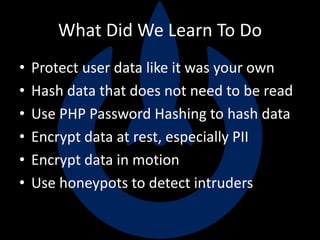
The Ashley Madison hack revealed major security issues that compromised millions of users' personal data. Hackers were able to access Ashley Madison's entire network over several years, collecting database, email, code, and other files. They were ultimately able to crack passwords due to the site storing an MD5 hash of usernames and unhashed passwords. The hack demonstrated the importance of securely storing and handling sensitive user data, using strong password hashing, encrypting data at rest and in motion, and carefully monitoring networks for intrusions.