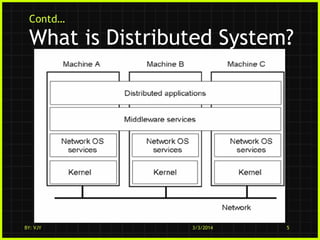
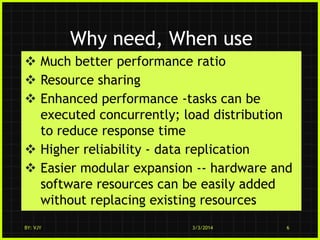
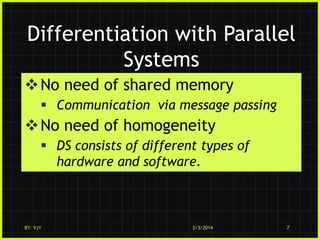
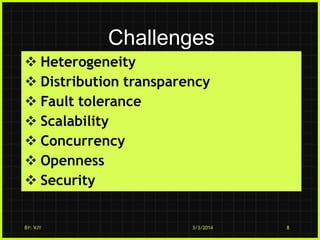
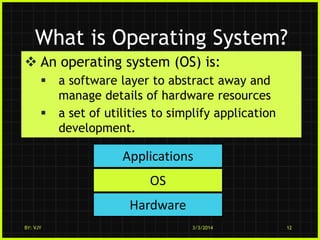
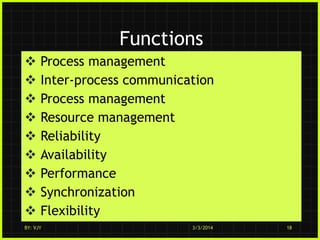
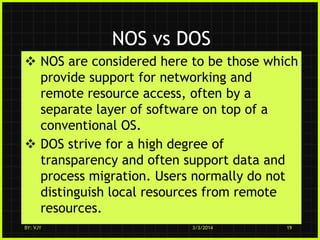
This document discusses distributed operating systems. It begins by defining a distributed system as multiple connected CPUs that appear as a single system to users. A distributed operating system provides the essential services of a traditional operating system but runs across multiple independent CPUs. It aims to be transparent to users. Examples given of distributed operating systems include Amoeba, Solaris, and MOSIX. The document outlines the features, functions, and goals of distributed operating systems, such as resource sharing, accessibility, concurrency, scalability, and fault tolerance.