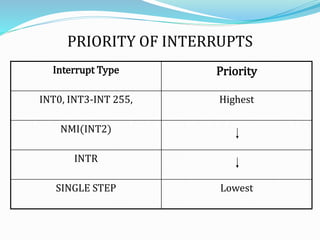
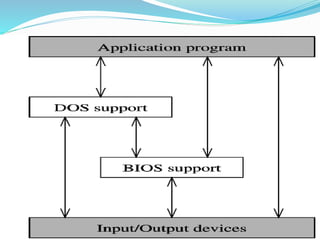
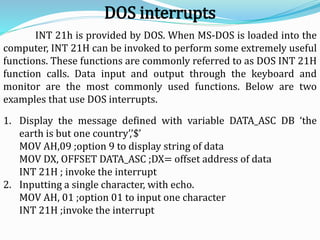
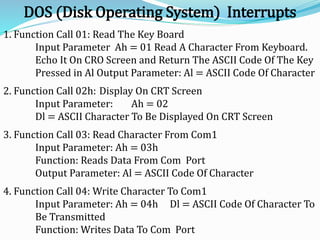
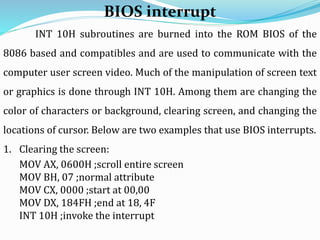
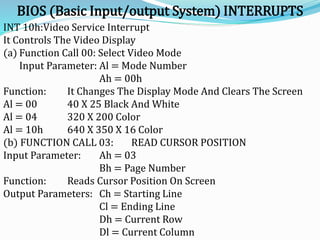
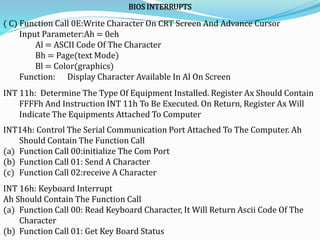
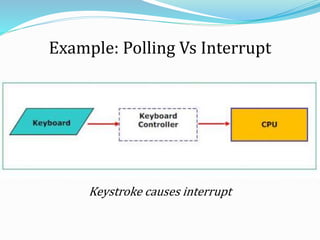
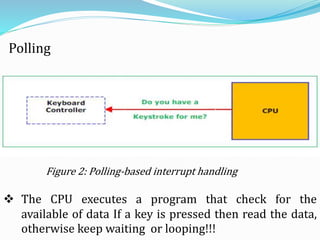
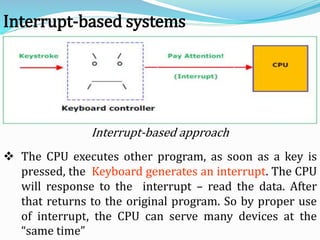
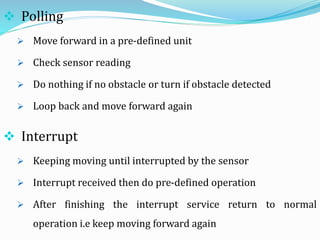
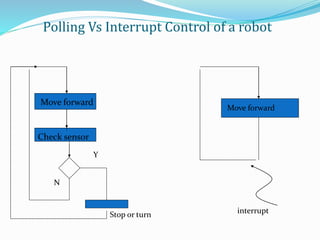
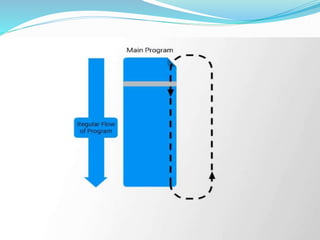
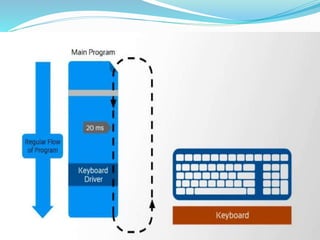
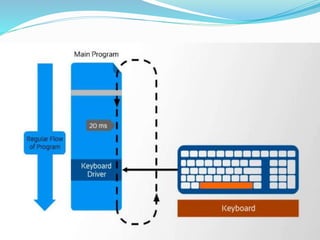
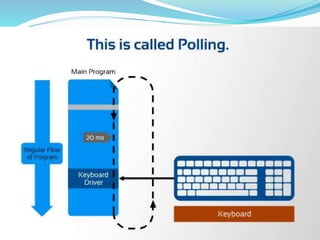
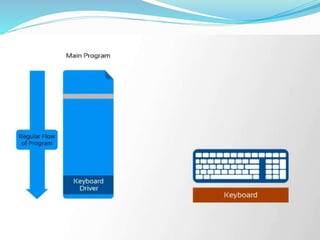
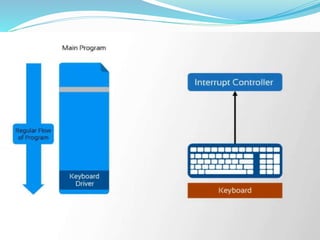
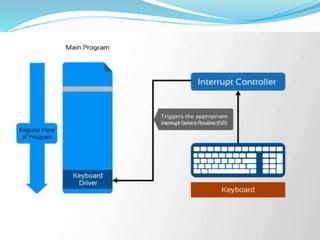
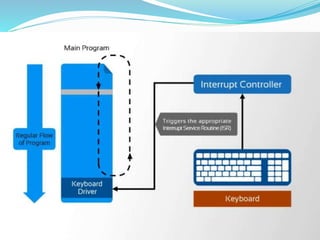
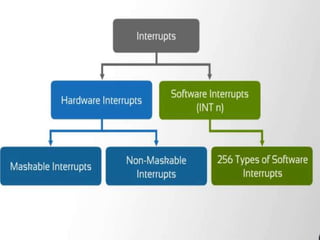
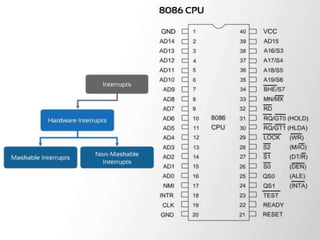
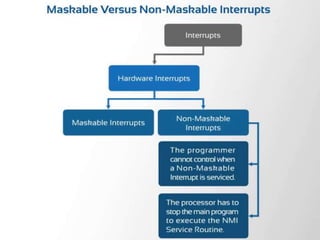
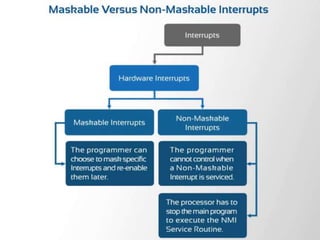
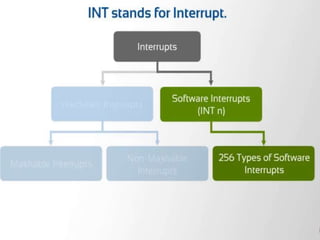
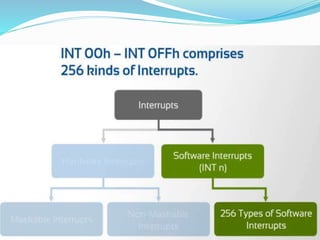
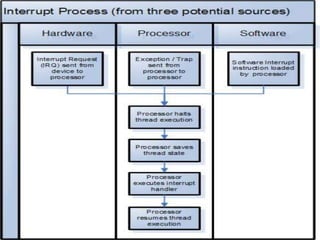
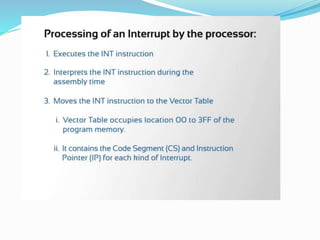
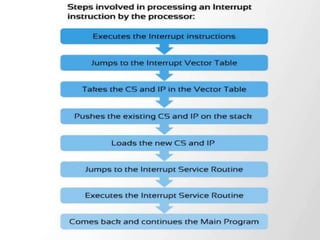
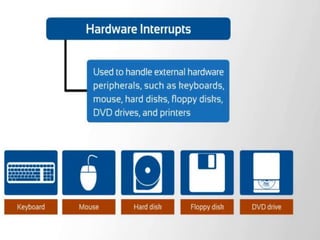
This document discusses interrupts in microprocessors and provides examples of their use. It defines an interrupt as an event that temporarily halts normal program execution to service another event, like an I/O device requiring attention. Interrupts provide an alternative to polling that allows a CPU to serve multiple devices simultaneously. The document then gives examples of using interrupts to control a robot's movement in response to sensors as compared to polling, and provides overviews of DOS and BIOS interrupts for I/O functions like reading keyboards, displaying to screens, and communicating with serial ports.
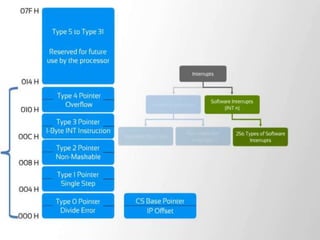

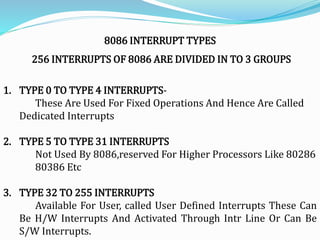
![Type – 0 Divide Error Interrupt
Quotient Is Large Cant Be Fit In Al/Ax Or Divide By Zero
Type –1 Single Step Interrupt
Used For Executing The Program In Single Step Mode By Setting Trap Flag
To Set Trap Flag PUSHF
MOV BP,SP
OR [BP+0],0100H;SET BIT8
POPF
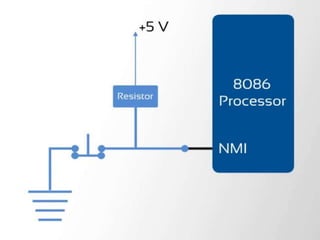
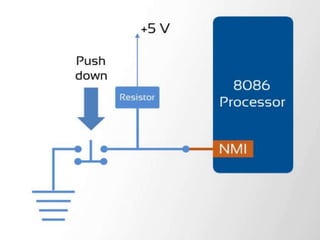
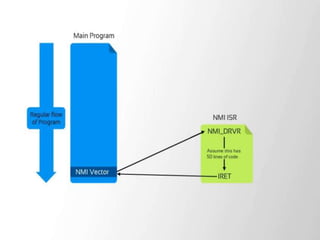
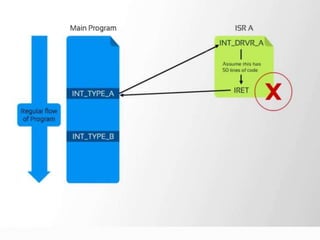
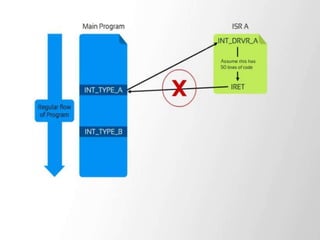
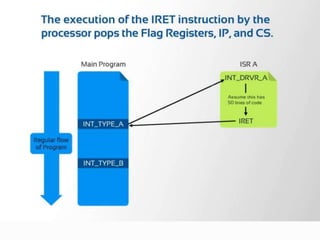
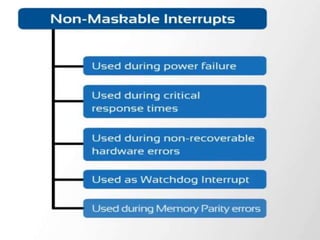
Type – 2 Non Maskable Interrupt
This Interrupt Is Used For Executing Isr Of Nmi Pin (Positive Egde Signal). Nmi
Cant Be Masked By S/W
Type – 3 Break Point Interrupt
Used For Providing Break Points In The Program
Type – 4 Over Flow Interrupt
Used To Handle Any Overflow Error After Signed Arithmetic](https://image.slidesharecdn.com/interruptsbyvijay-140417010549-phpapp01/85/8086-Interrupts-With-DOS-and-BIOS-by-vijay-58-320.jpg)