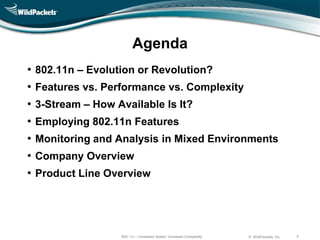
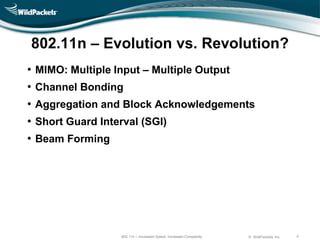
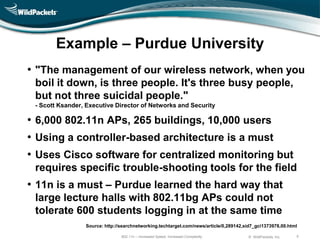
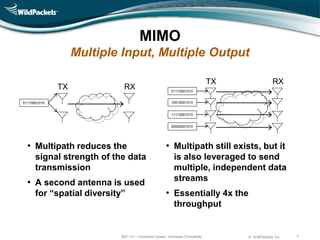
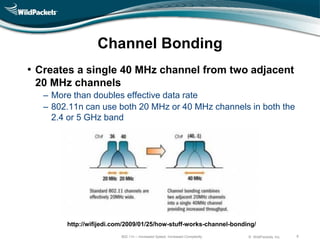
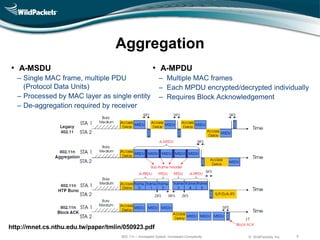
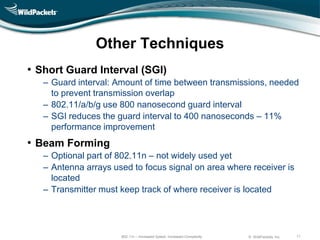
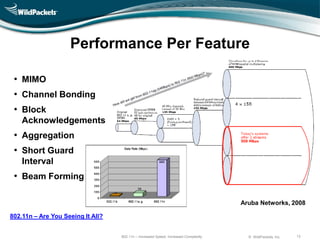
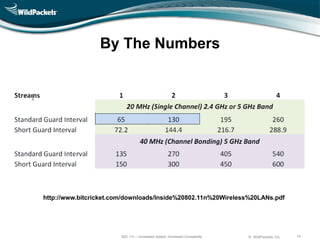
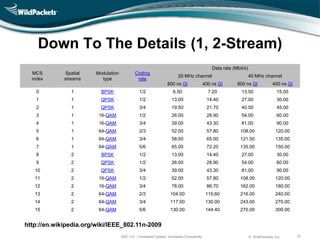
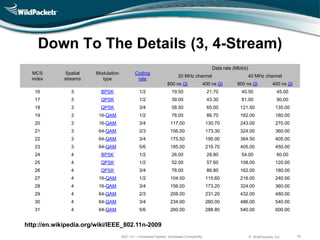
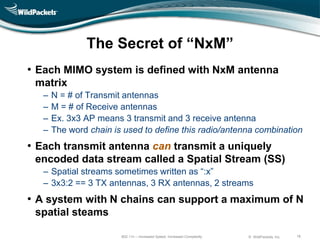
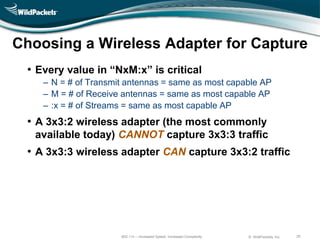
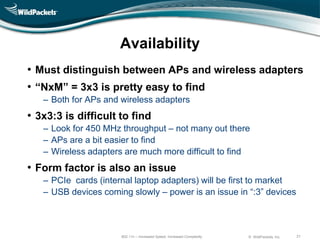
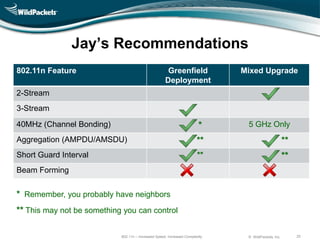
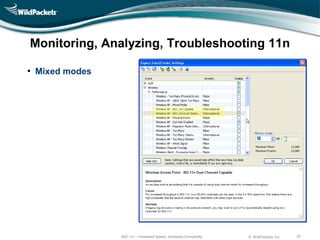
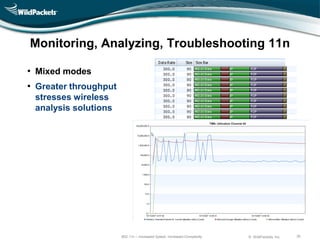
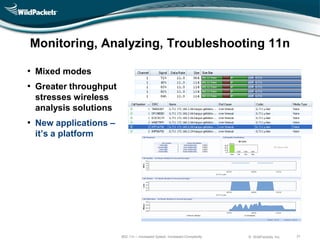
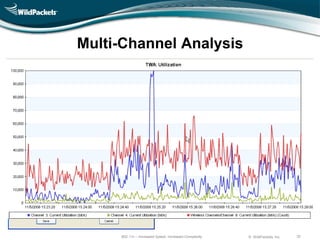
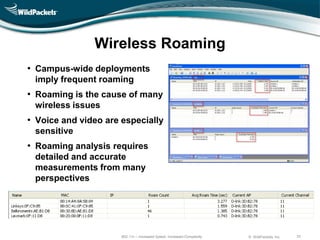
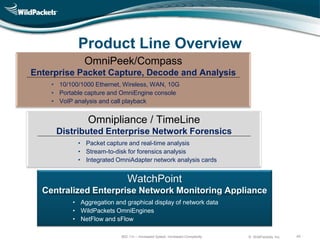
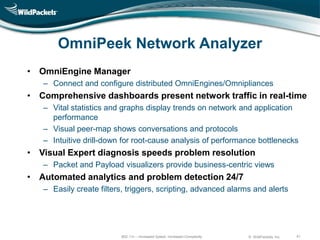
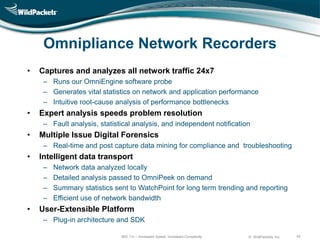
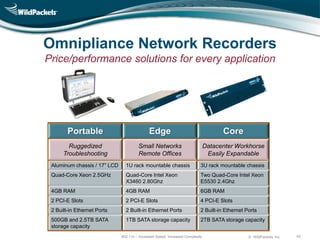
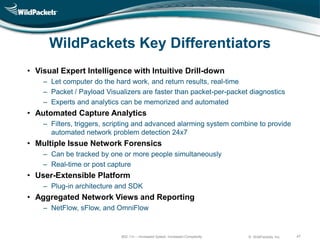
The document discusses the advancements and complexities of the 802.11n wireless networking standard, including features like MIMO, channel bonding, and frame aggregation which enhance speed but increase operational intricacies. It emphasizes the importance of using 802.11n features for effective network management and analysis in various real-world environments, particularly in educational institutions. Additionally, it provides an overview of company capabilities in network monitoring and analysis tools to support the deployment of this technology.