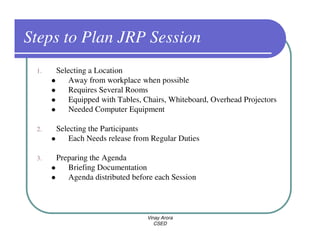
The document discusses various techniques for fact finding and requirement discovery in systems analysis. It describes sampling existing documentation, observation, questionnaires, interviews, prototyping, and joint requirements planning as key methods. It provides guidelines for conducting interviews and JRP sessions effectively. The overall goal of requirement discovery is to identify business and system requirements through formal research and information gathering processes.