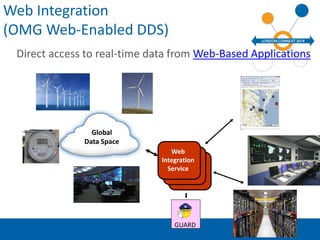
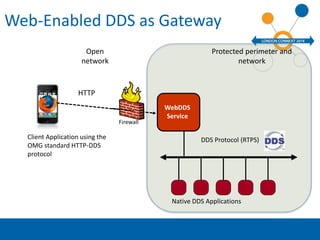
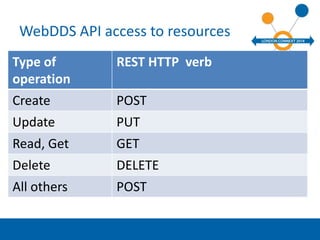
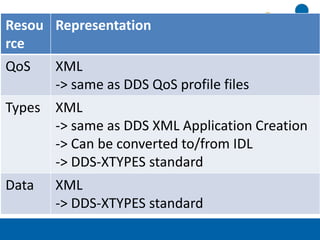
The document discusses web-enabled Data Distribution Service (DDS) technology developed by Real-Time Innovations, Inc., focusing on real-time data access via web-based applications. It details the architecture, scenarios for mobile and browser access, and provides an overview of the API for resource management. The document also includes information on data formats, application creation, and various supported operations through HTTP verbs.