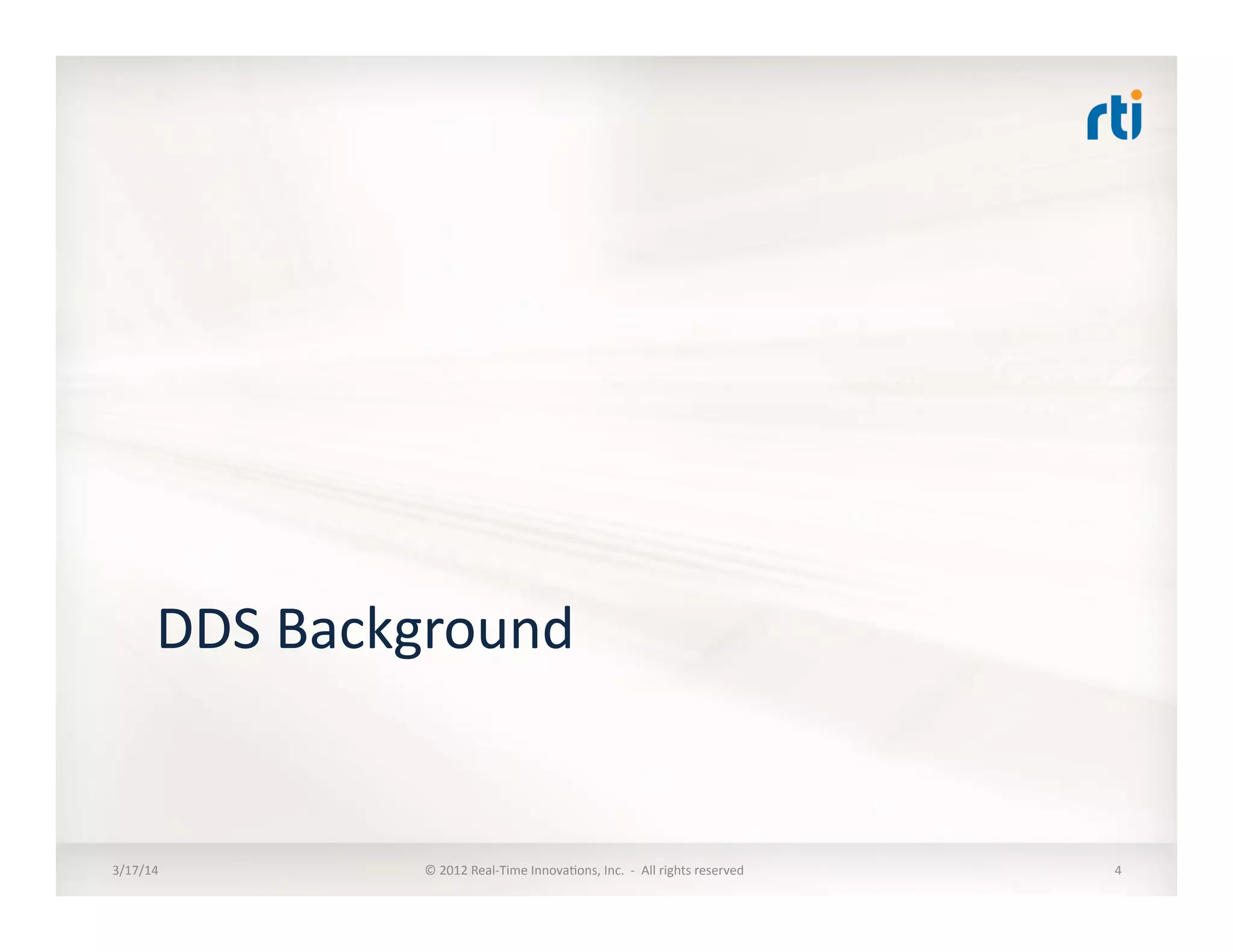
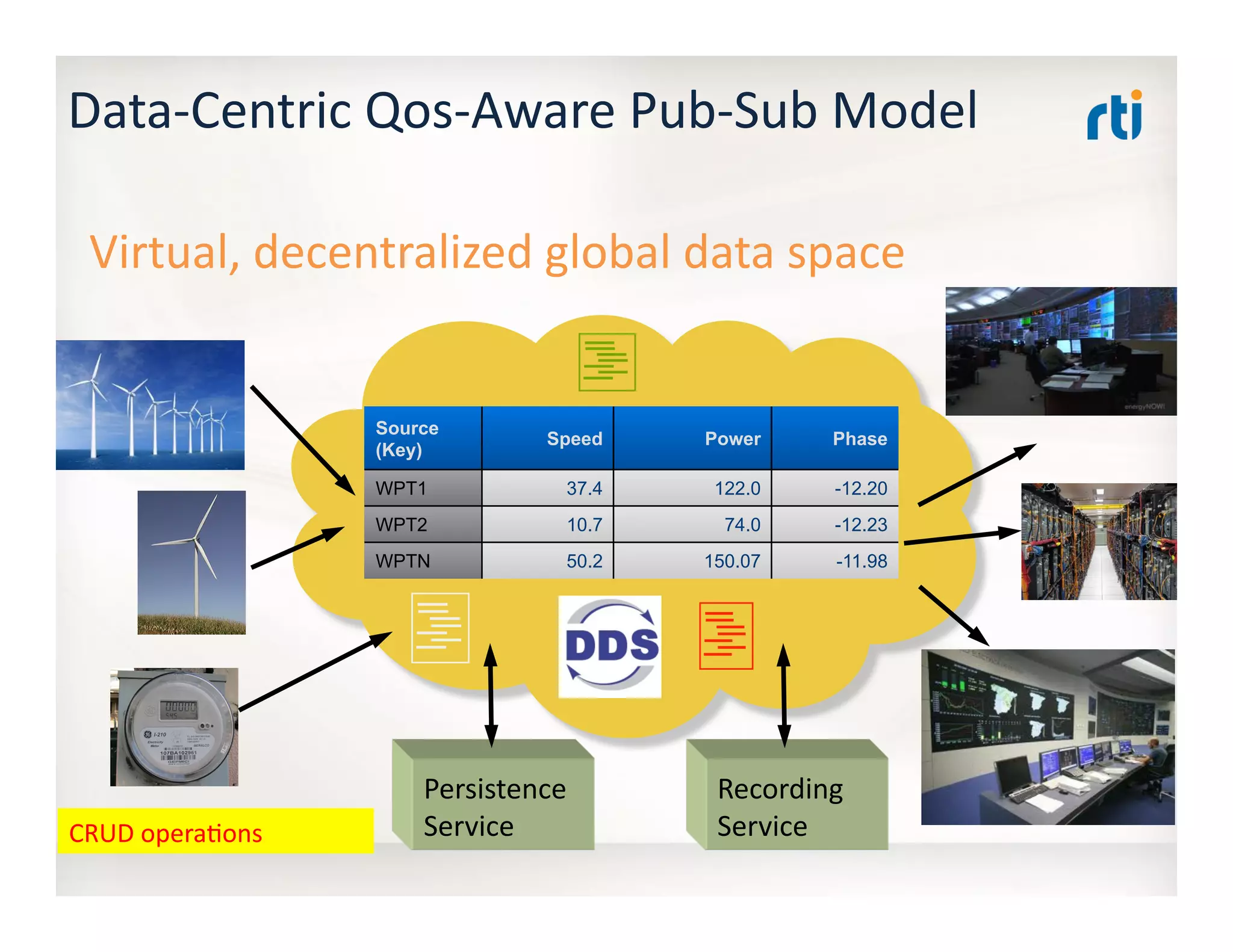
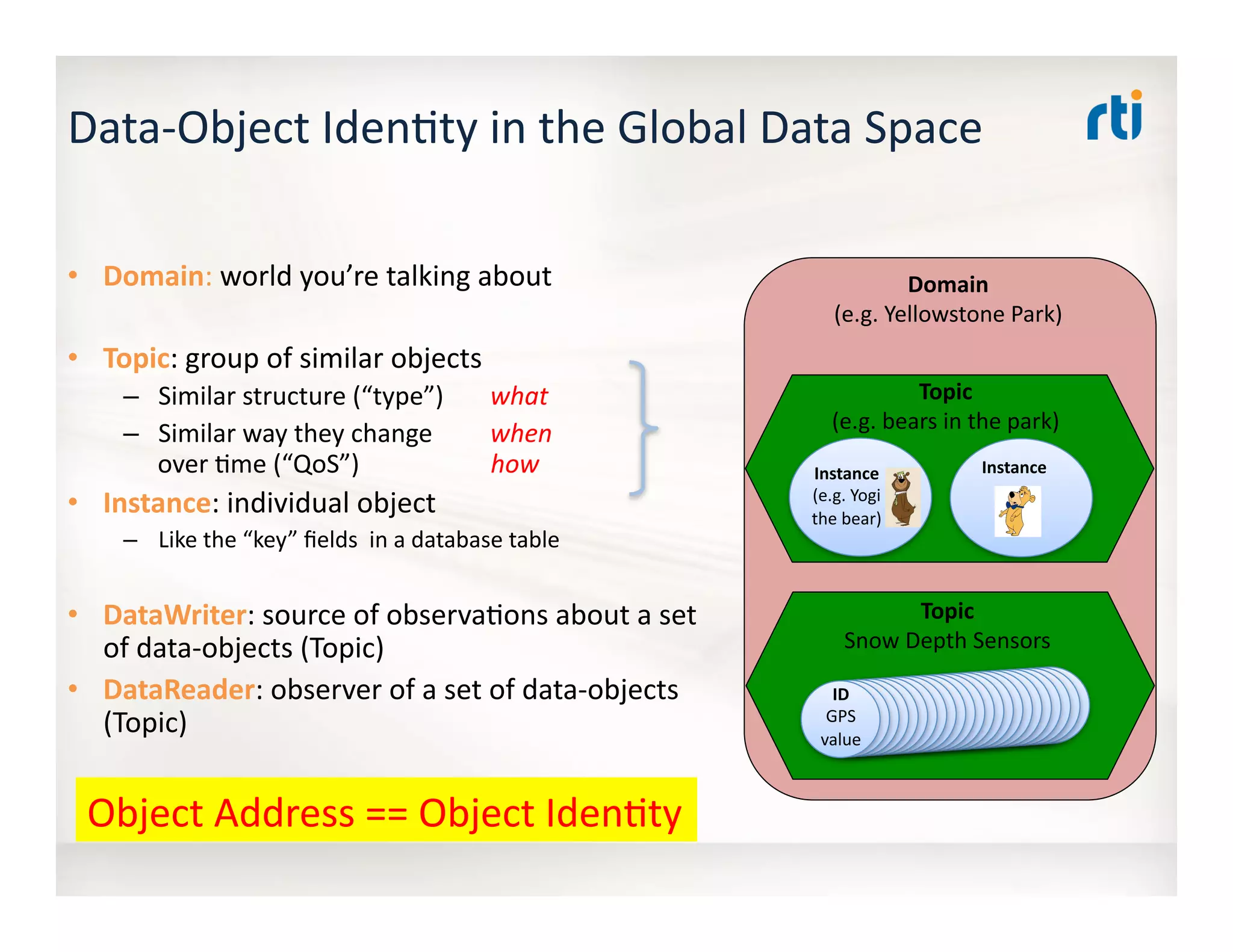
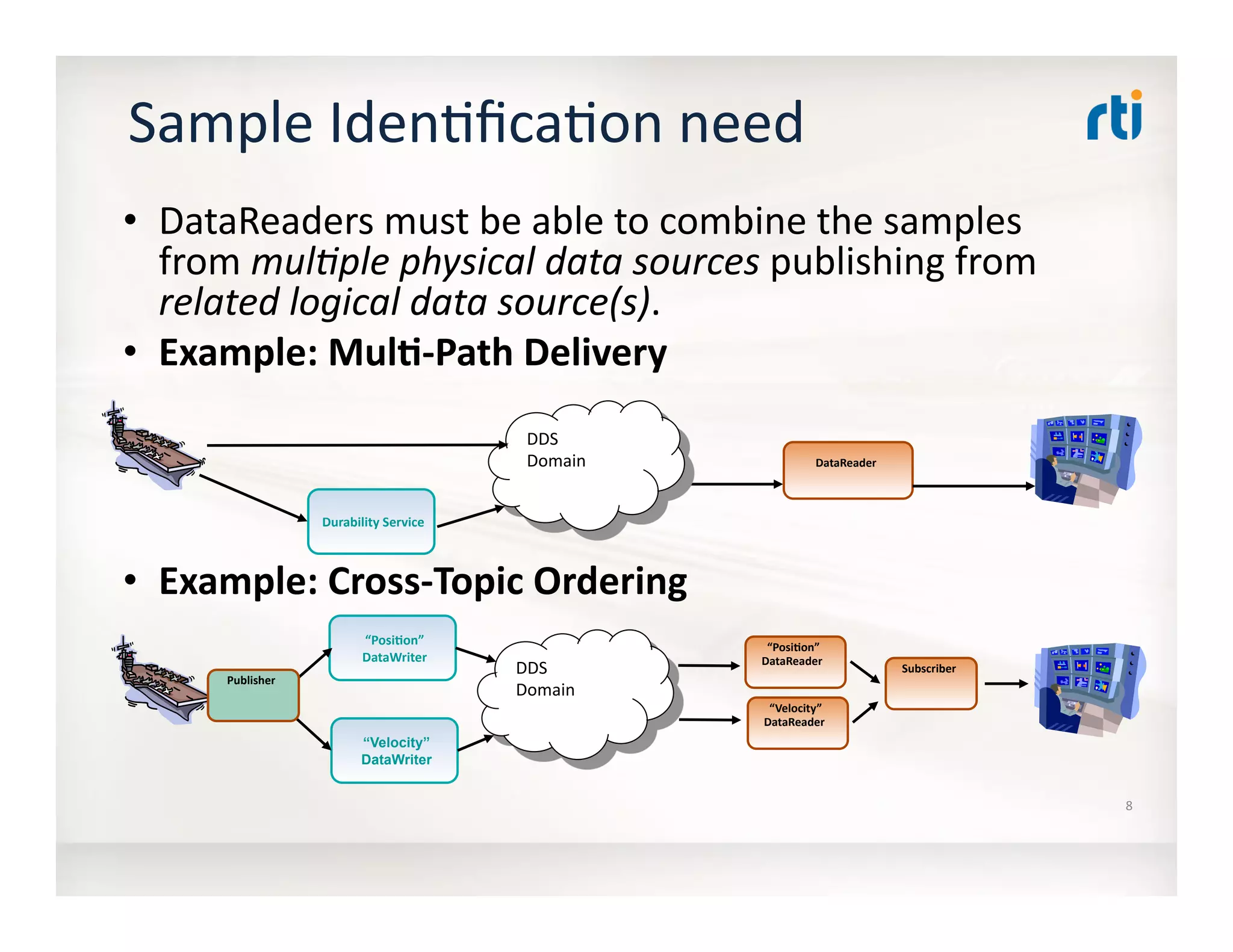
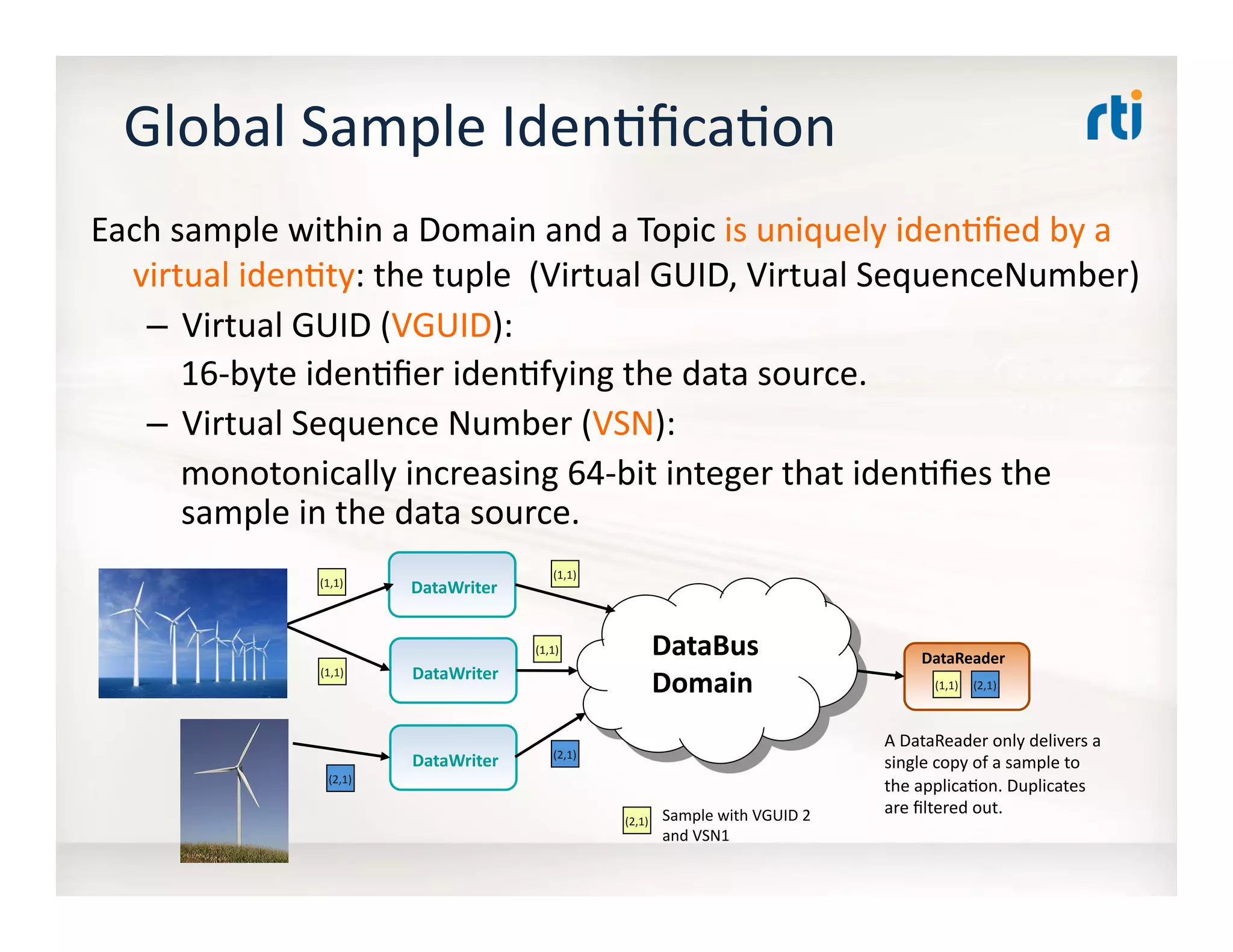
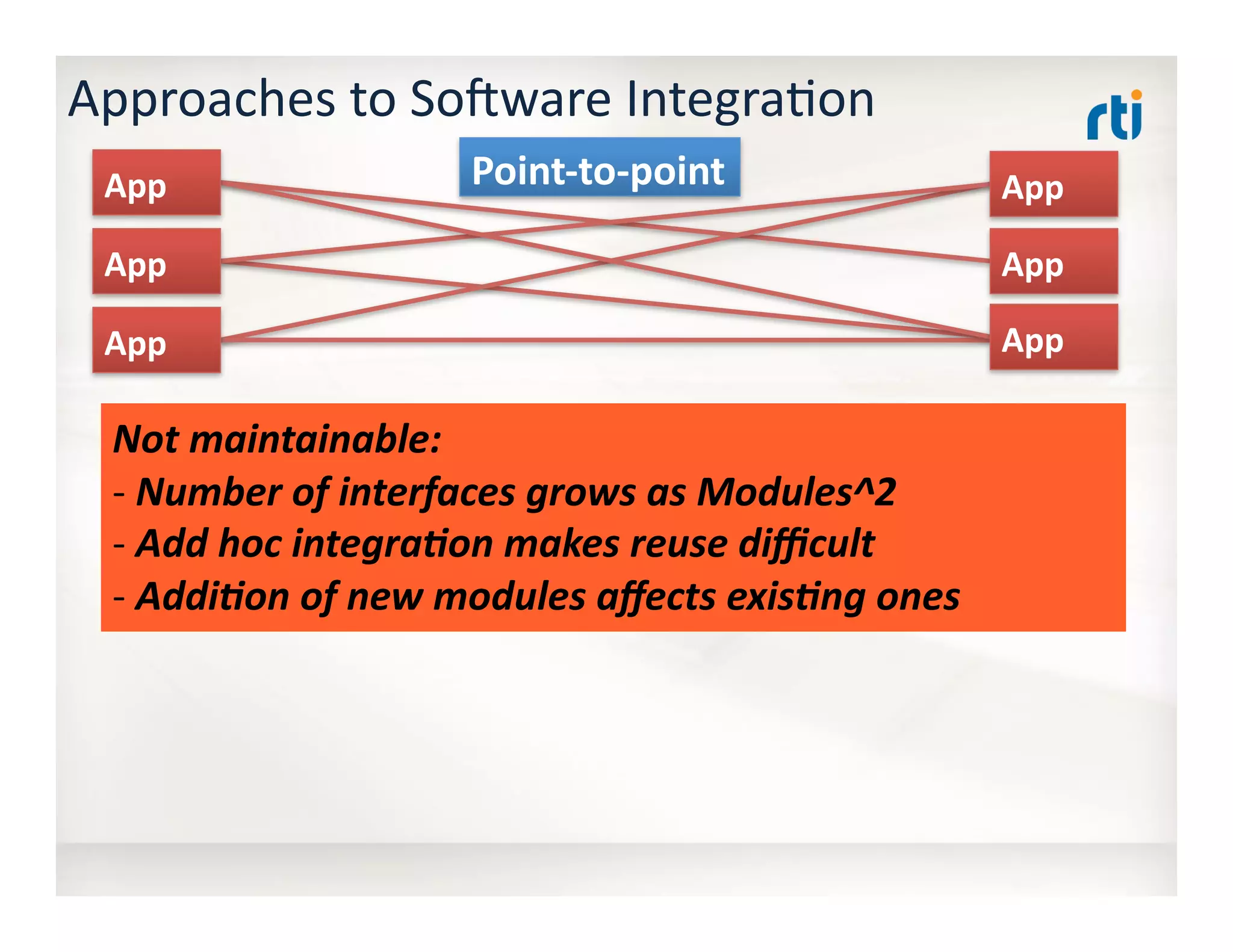
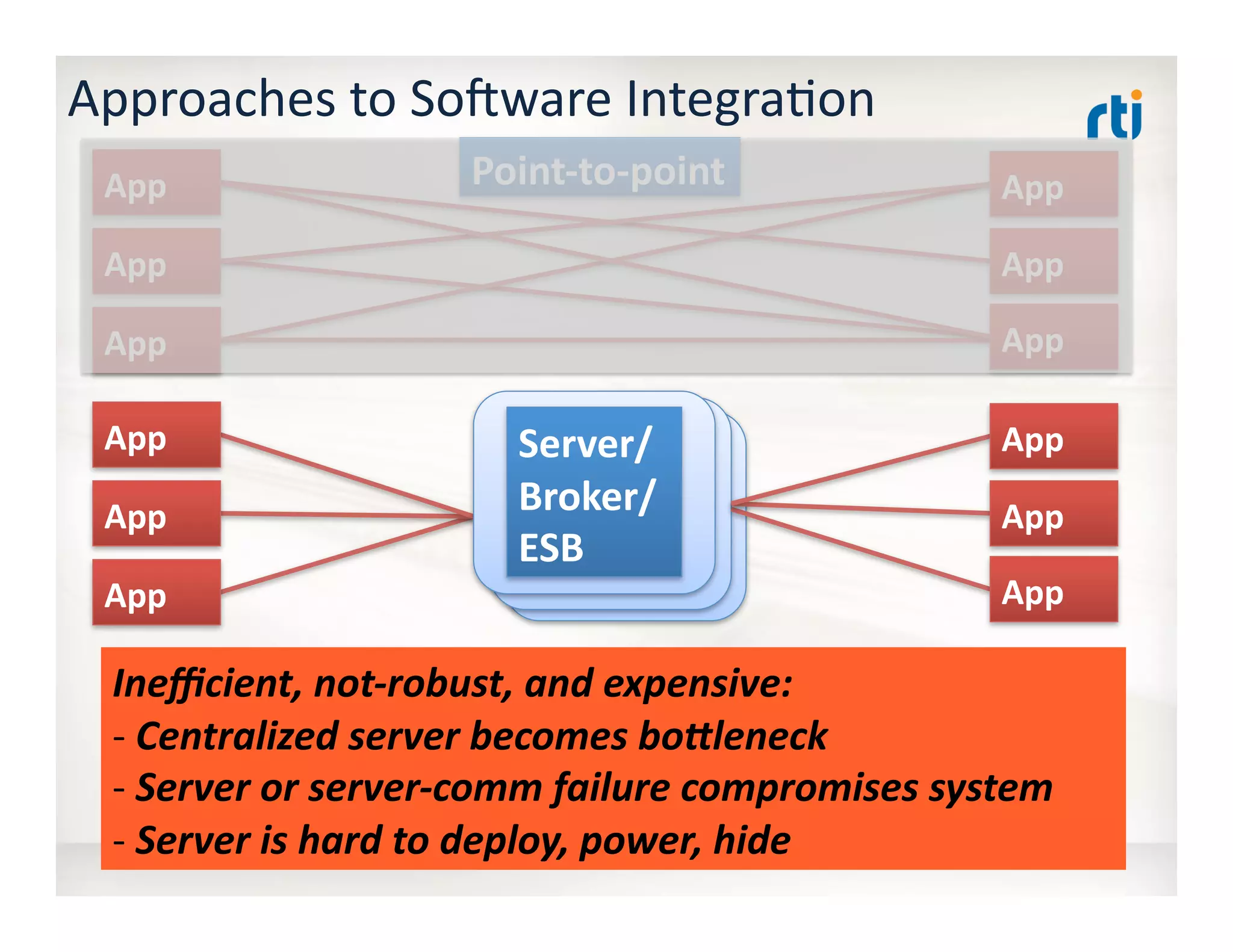
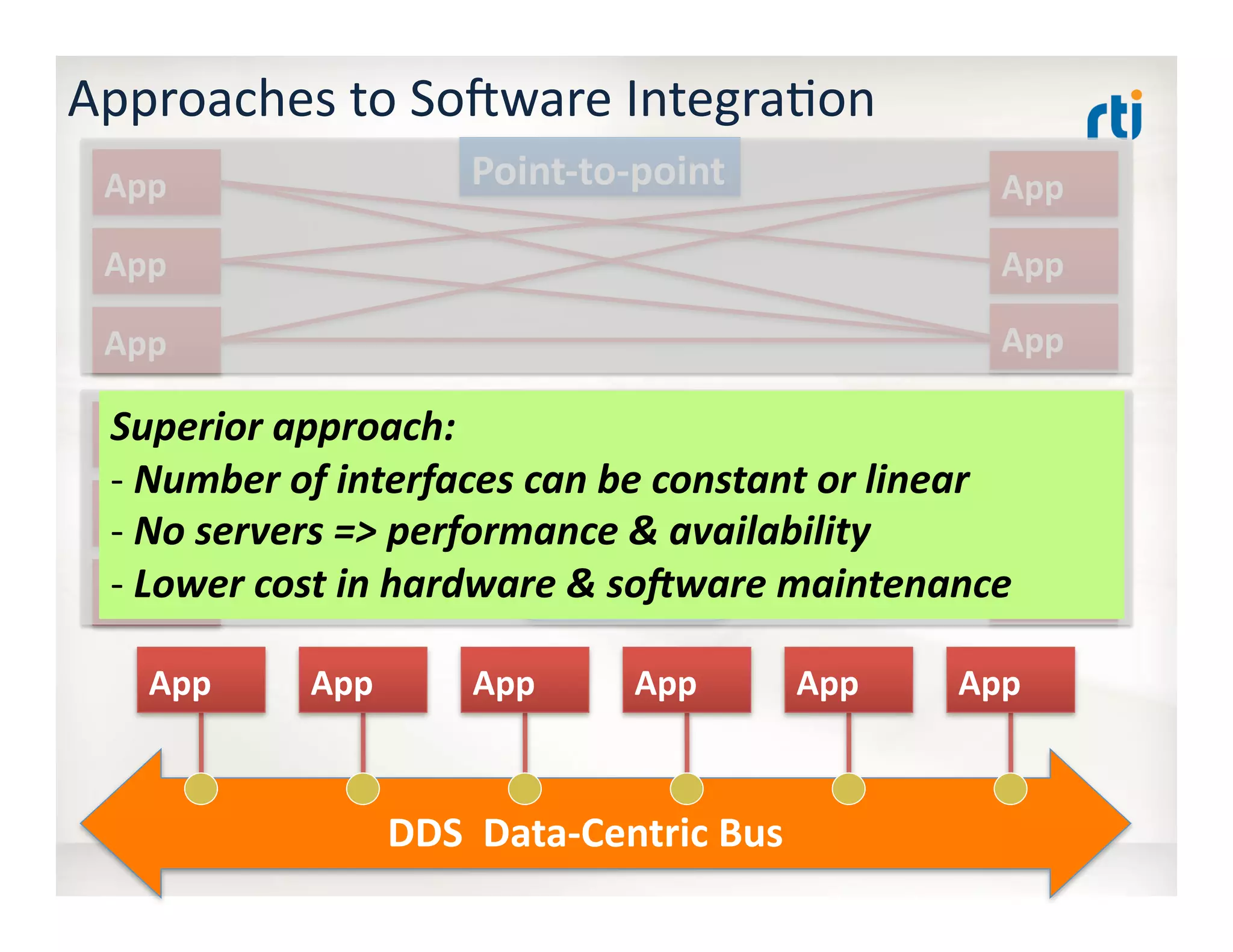
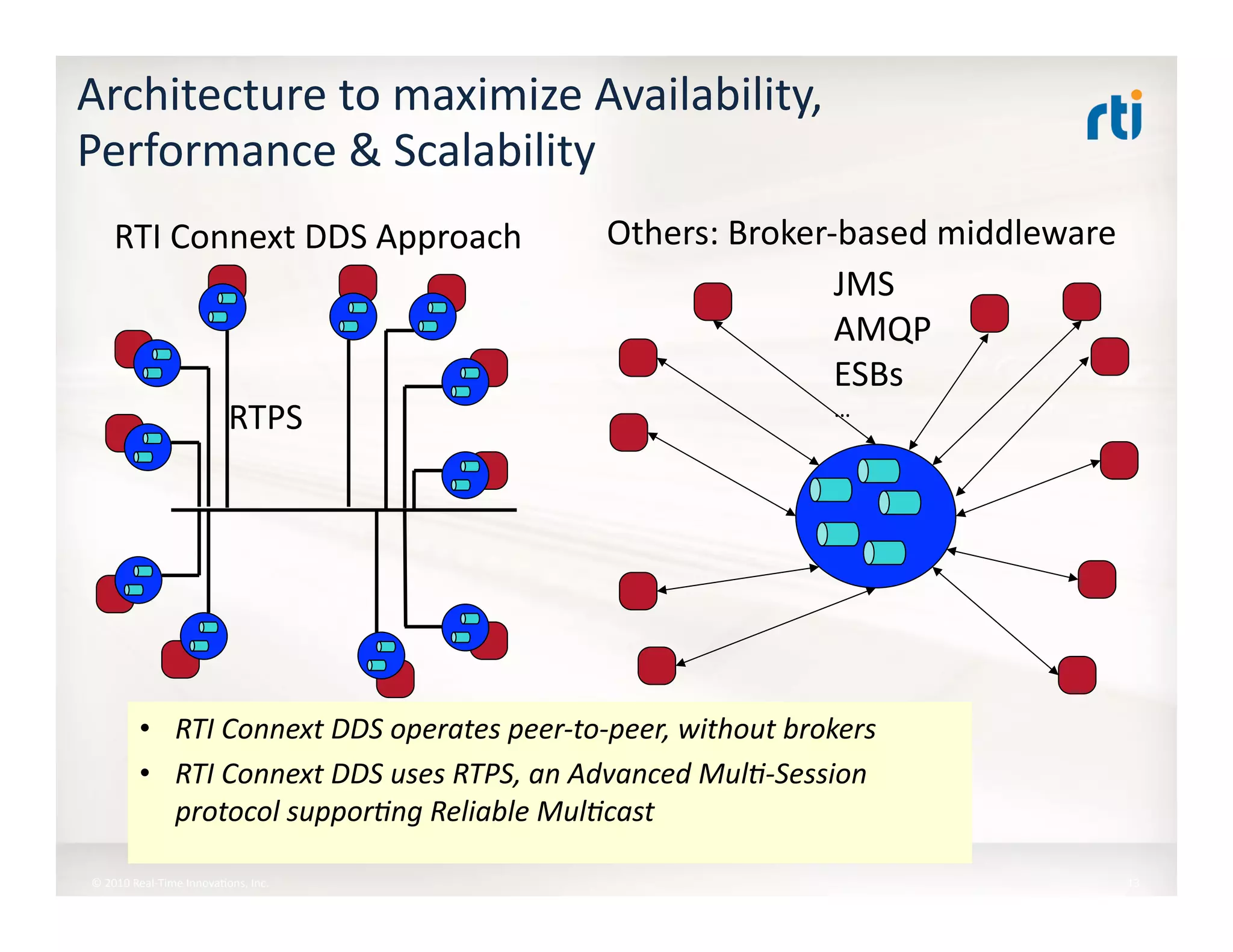
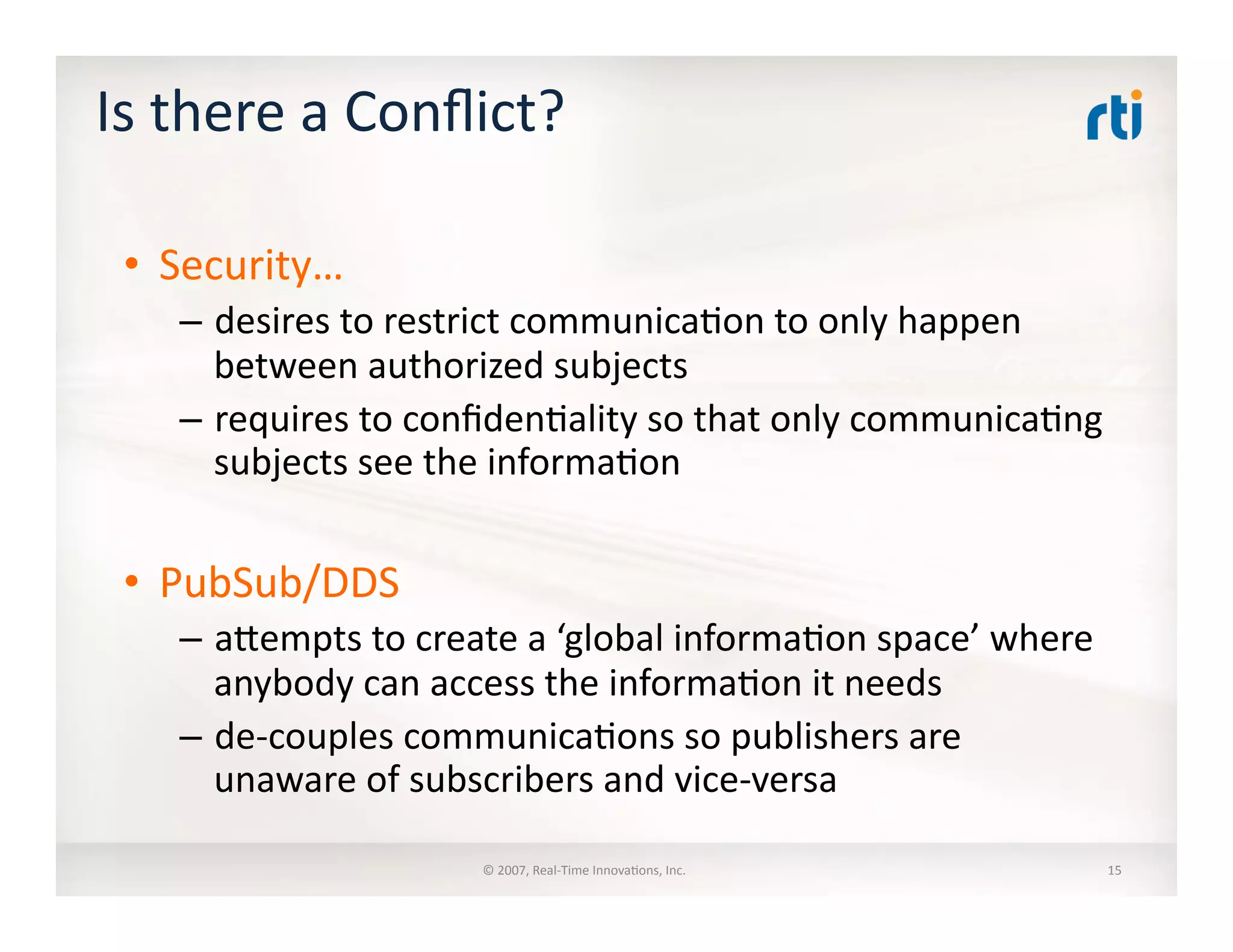
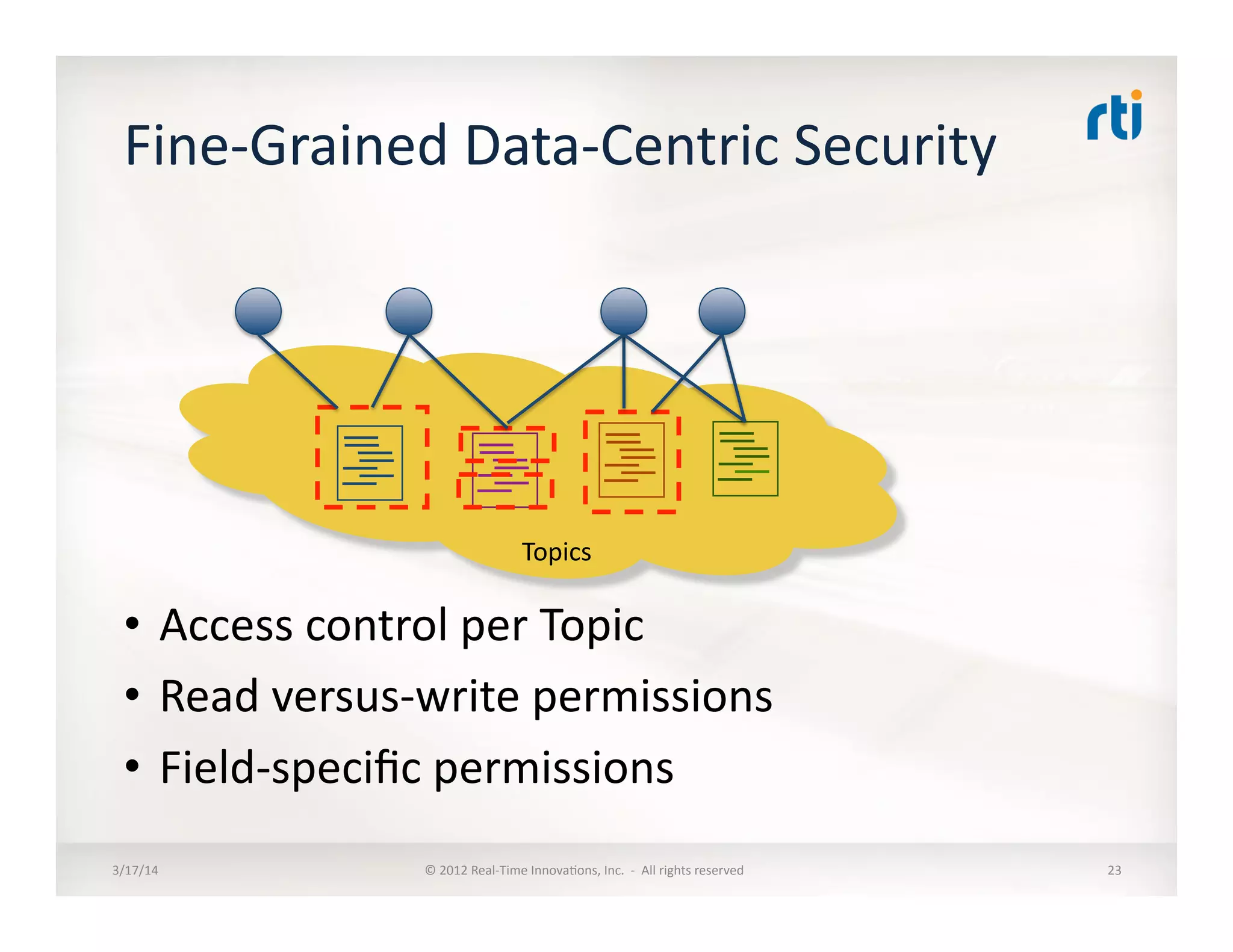
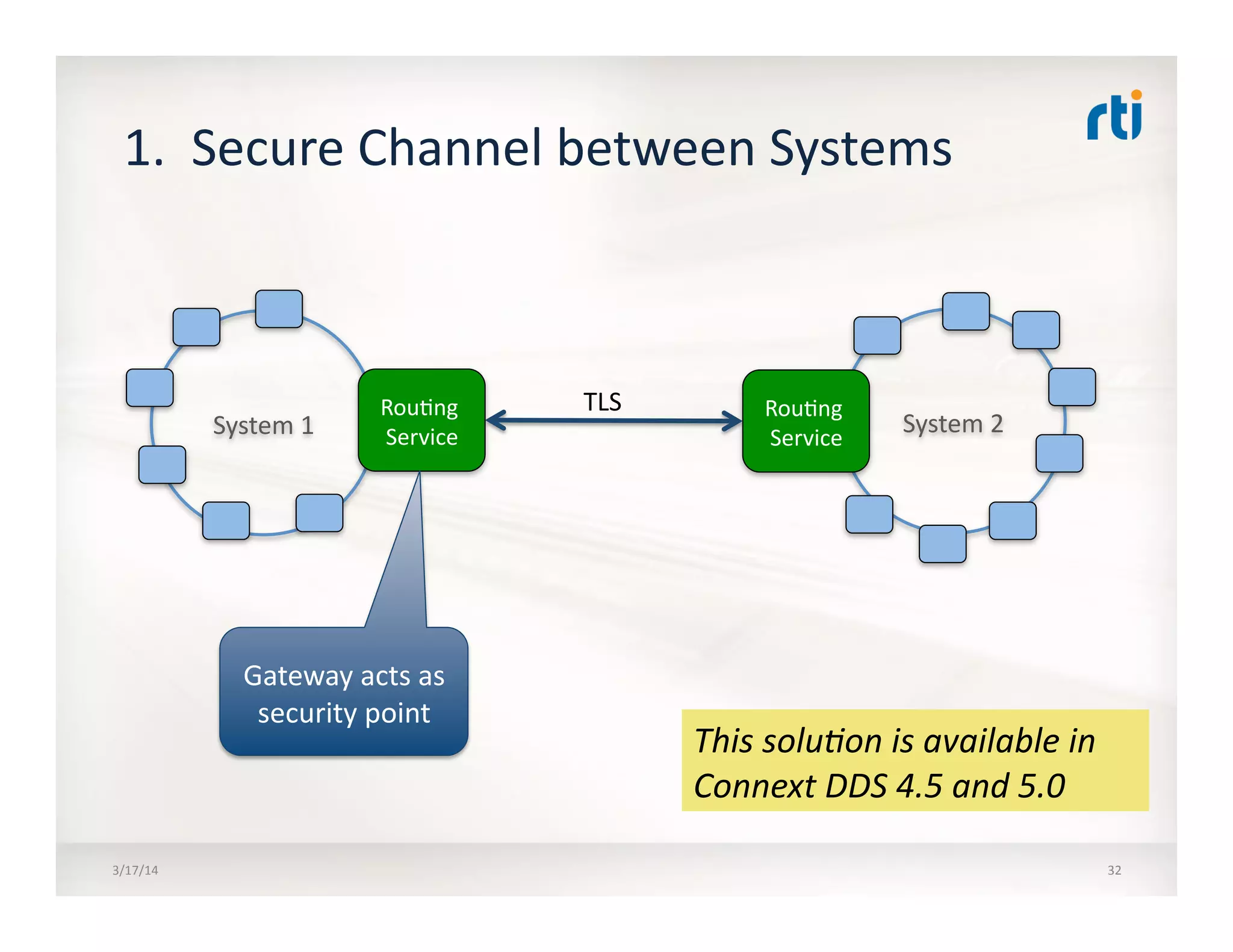
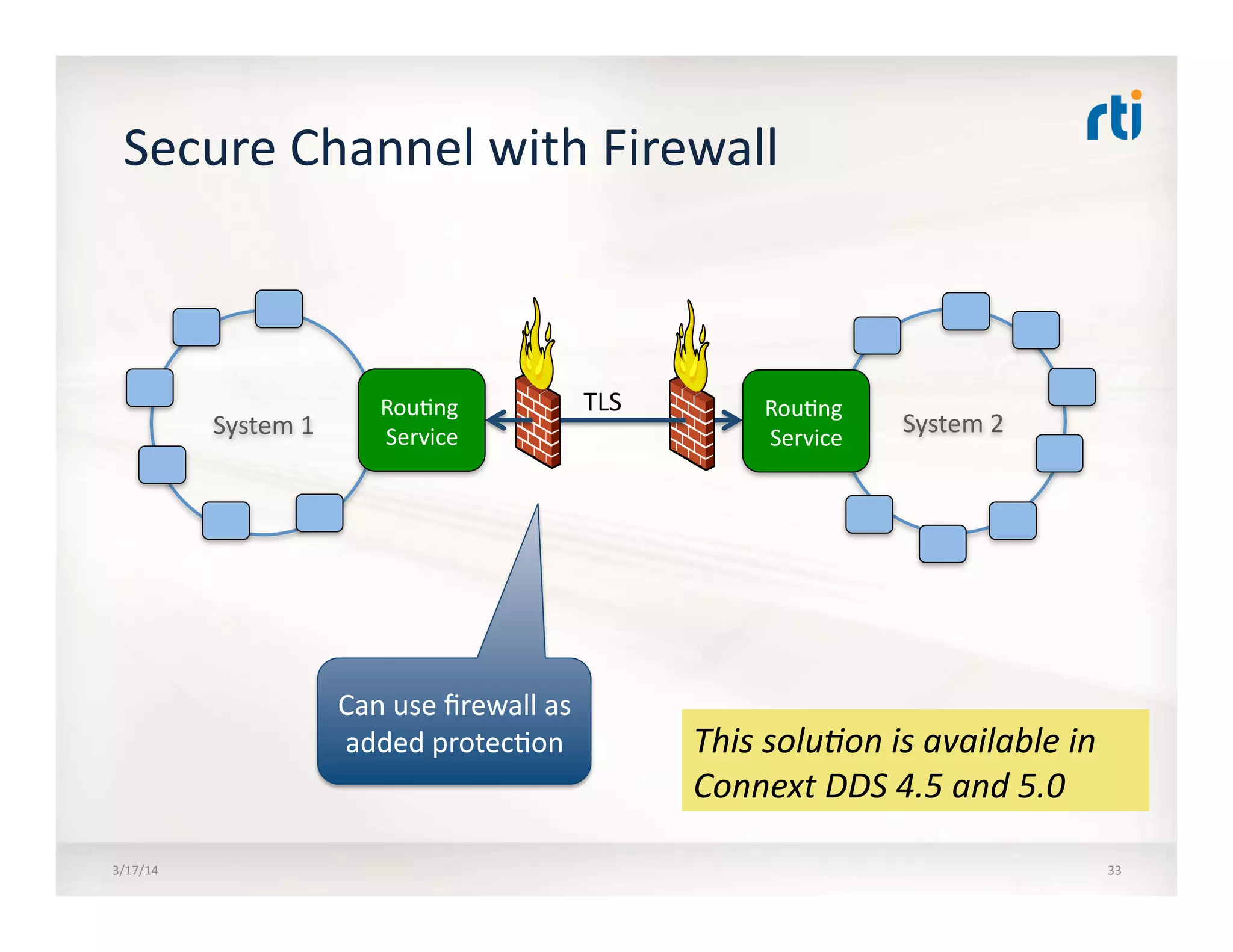
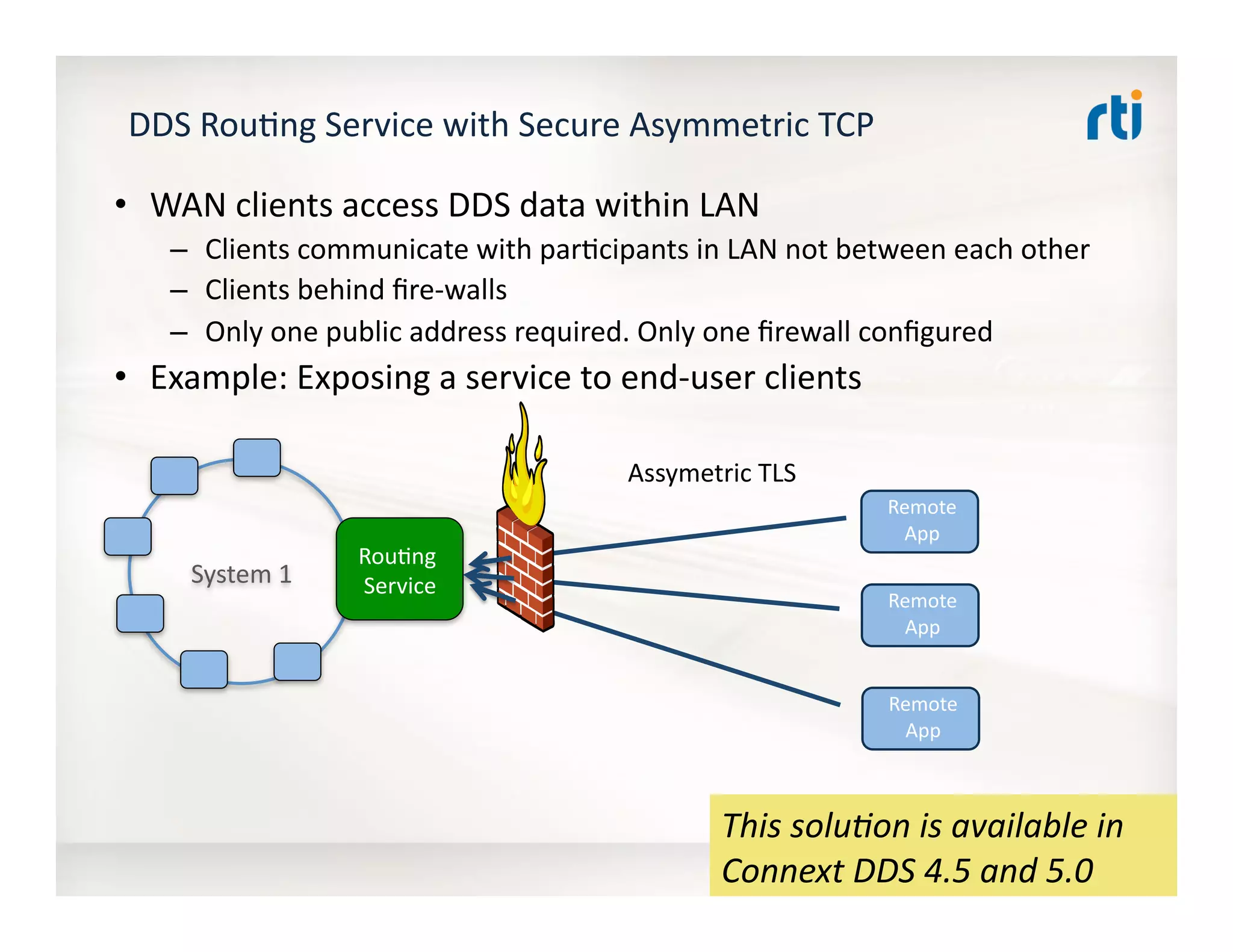
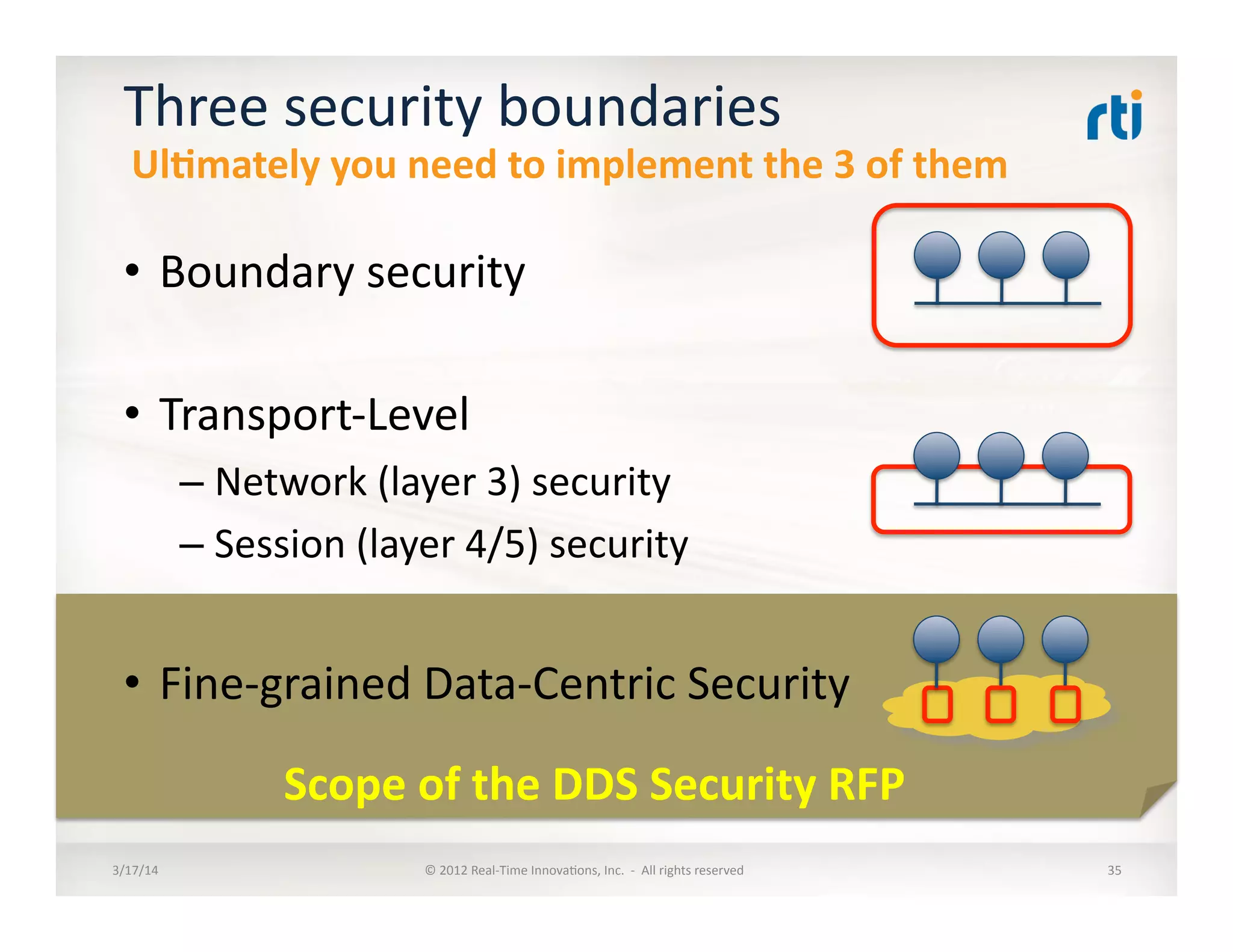
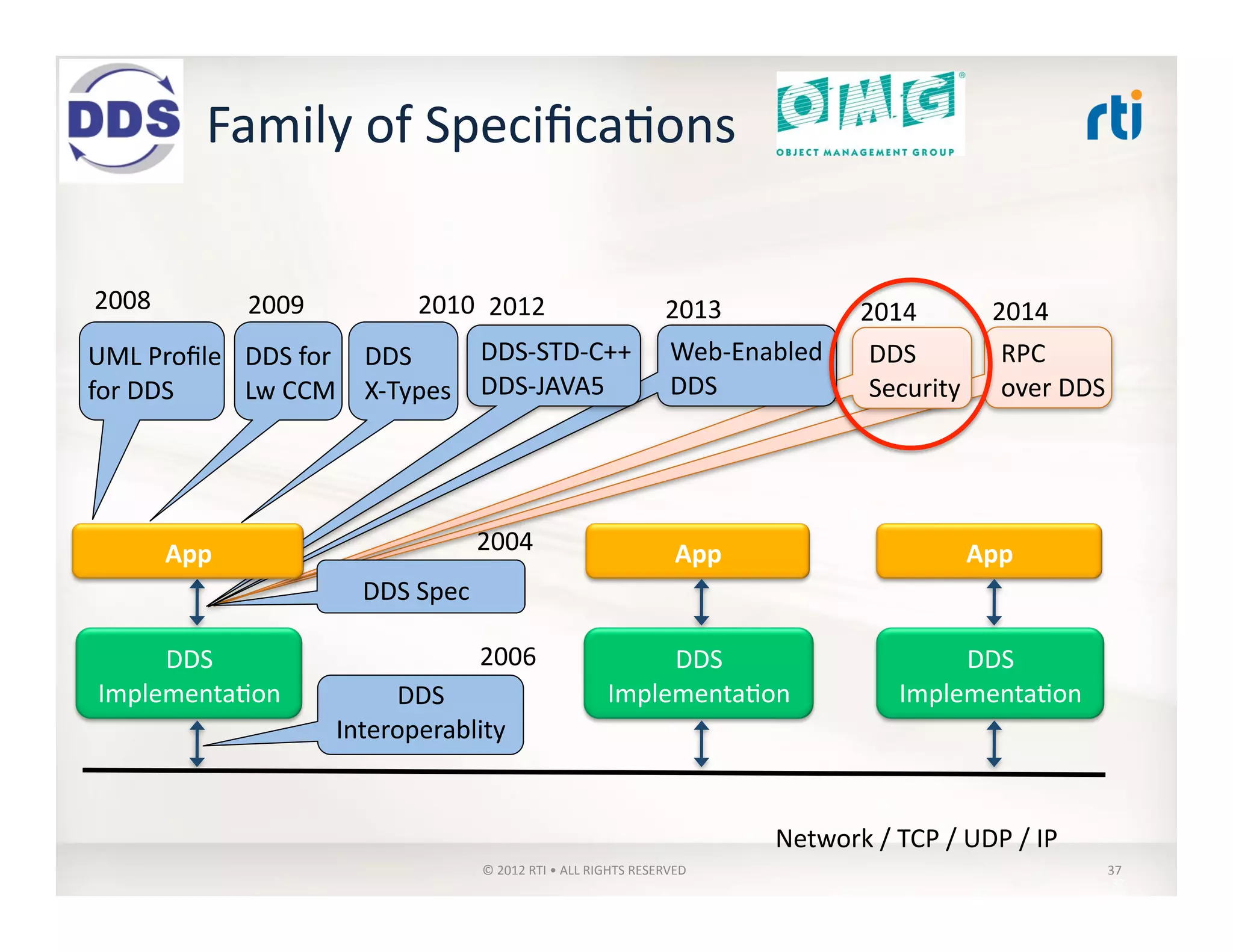
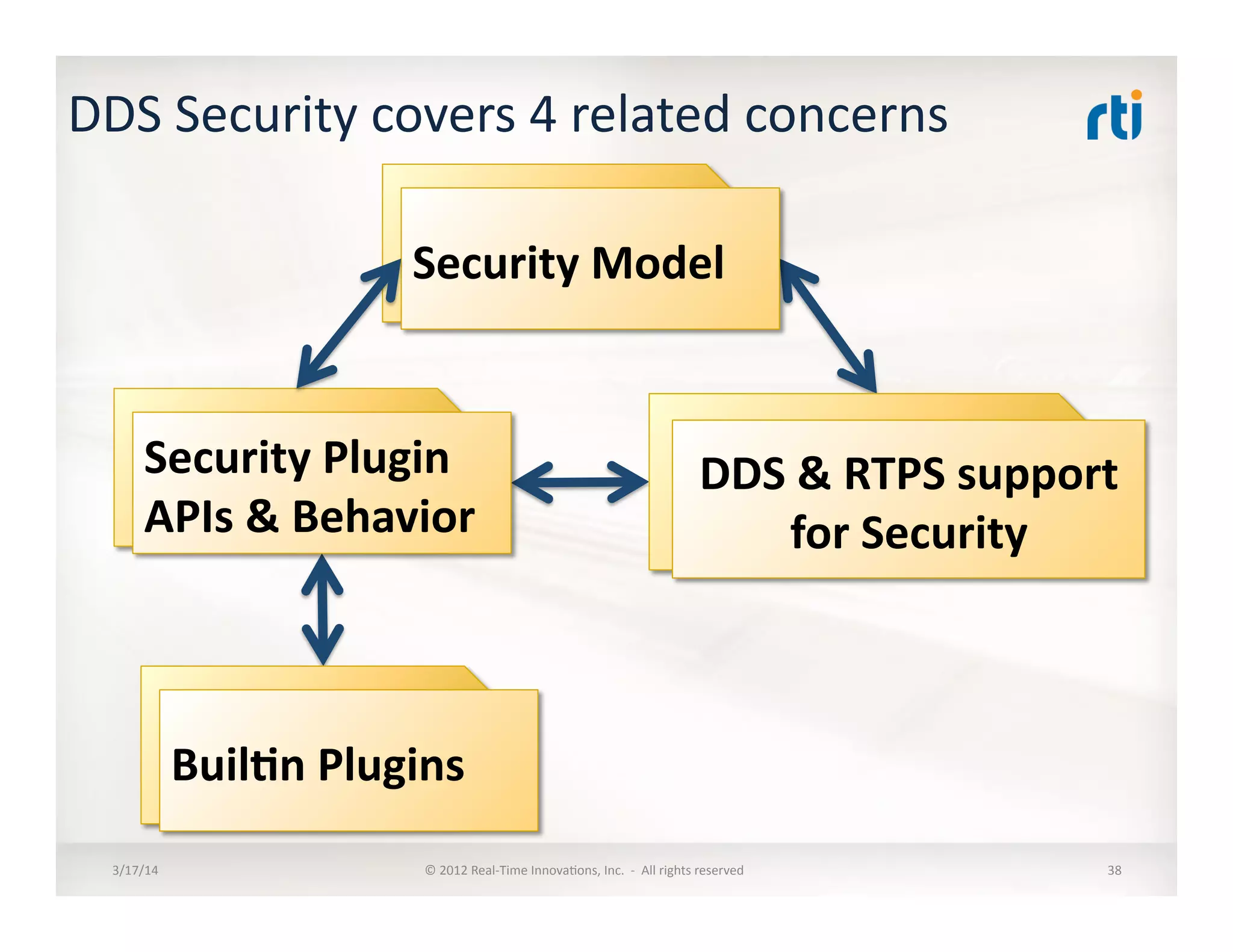
This document provides an overview of data distribution service (DDS) and security considerations for DDS. It discusses the data-centric publish-subscribe model of DDS, how data is identified in the global data space, and approaches to software integration like point-to-point and broker-based that DDS improves upon. The document also touches on key aspects of the DDS security specification and next steps.




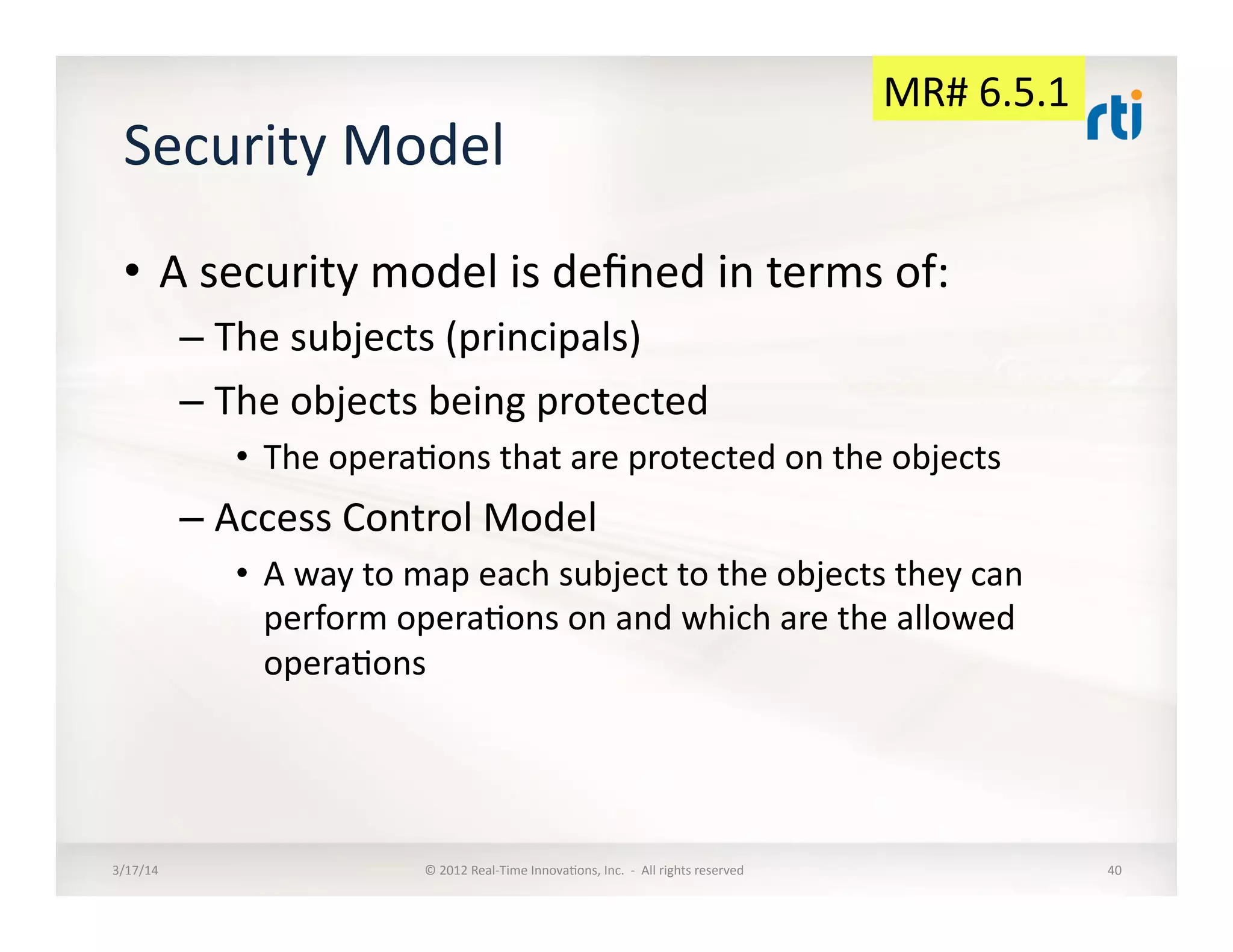
![Security
Model
Example:
UNIX
FileSystem
(simplified)
• Subjects:
Users,
specifically
processes
execu:ng
on
behalf
of
a
specific
userid
• Protected
Objects:
Files
and
Directories
• Protected
Opera:ons
on
Objects:
– Directory.list,
Directory.createFile,
Directory.createDir,
Directory.removeFile,
Directory.removeDir,
Directory.renameFile
– File.view,
File.modify,
File.execute
• Access
Control
Model:
– A
subject
is
given
a
userId
and
a
set
of
groupId
– Each
object
is
assigned
a
OWNER
and
a
GROUP
– Each
Object
is
given
a
combina:on
of
READ,
WRITE,
EXECUTE
permissions
for
the
assigned
OWNER
and
GROUP
– Each
protected
opera:on
is
mapped
to
a
check,
for
example
•
File.view
is
allowed
if
and
only
if
– File.owner
==
Subject.userId
AND
File.permissions(OWNER)
includes
READ
– OR
File.group
IS-‐IN
Subject.groupId[]
AND
File.permissions(GROUP)
includes
READ
3/17/14
©
2012
Real-‐Time
Innova:ons,
Inc.
-‐
All
rights
reserved
41](https://image.slidesharecdn.com/omgddssecurity201403-140327181858-phpapp01/75/OMG-Data-Distribution-Service-Security-41-2048.jpg)

![Buil:n
DDS:Crypto-‐AES-‐CTR-‐HMAC-‐DSA-‐DH
SPI
• Shared
secret
used
to
create
a
KeyExchangeKey
• KeyExchangeKey
used
to
send
following
Master
Key
Material
using
the
Buil:nPublica:onWriter:
– MasterKey
– MasterSalt
– MasterHMACSalt
• Based
on
this
the
following
Key
Material
is
computed:
– SessionSalt
:=
HMAC(MasterKey,"SessionSalt"
+
MasterSalt
+
SessionId
+
0x00)
[
Truncated
to
128
bits]
– SessionKey
:=
HMAC(MasterKey,"SessionKey"
+
MasterSalt
+
SessionId
+
0x01)
– SessionHMACKey
:=
HMAC(MasterKey,"SessionHMACKey"
+
MasterHMACSalt
+
SessionId)
Note:
SessionId
goes
on
the
EncryptedMessage
Envelope
• Encryp:on
uses
AES
in
Counter
(CTR)
mode
– The
session
counter
is
sent
on
EncryptedMessage
Envelope.
3/17/14
©
2012
Real-‐Time
Innova:ons,
Inc.
-‐
All
rights
reserved
84](https://image.slidesharecdn.com/omgddssecurity201403-140327181858-phpapp01/75/OMG-Data-Distribution-Service-Security-84-2048.jpg)
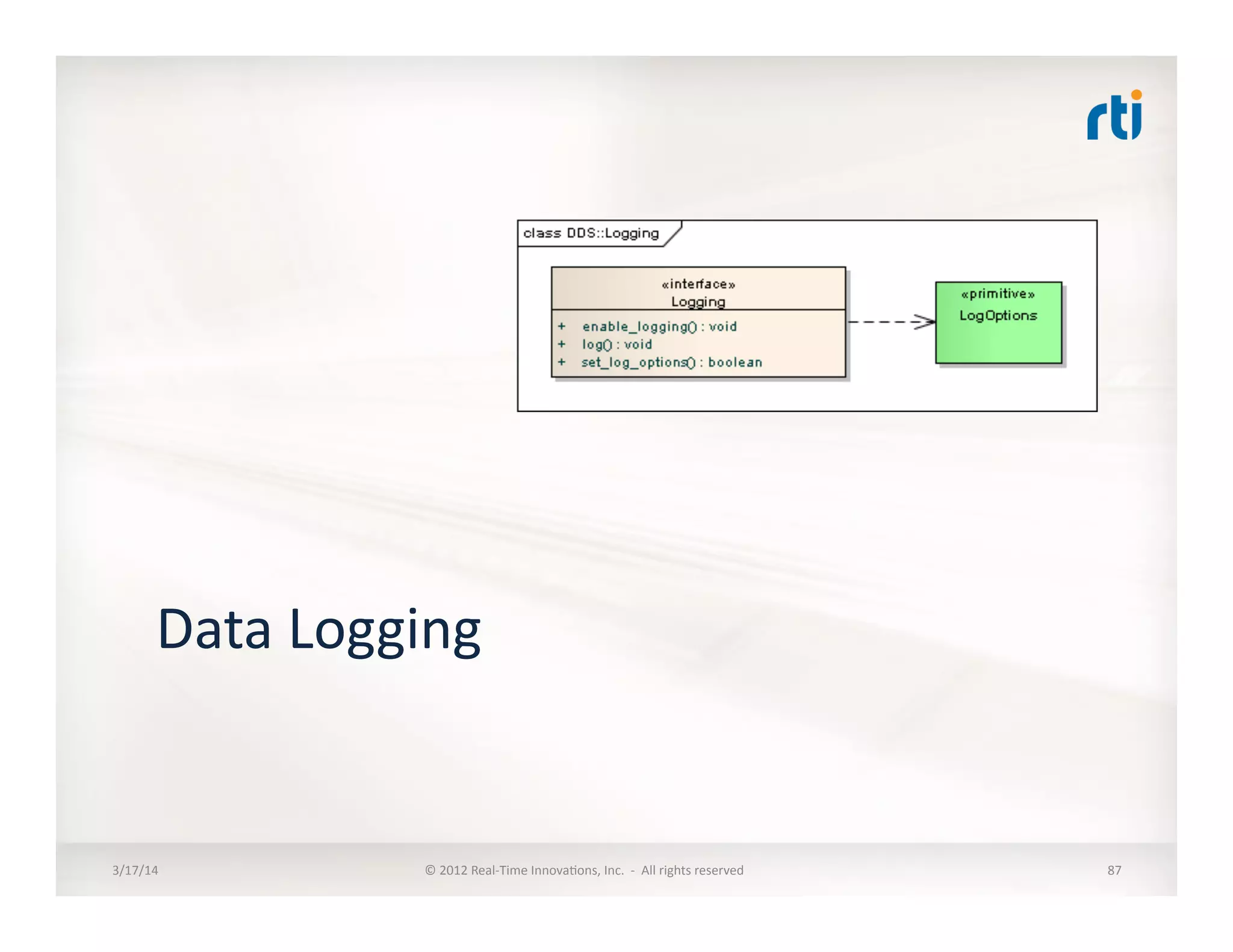
![DataLogging:
DDS:Logging:DDS_LogTopic
[Sec:on
s:ll
missing]
• Intent
is
to
use
a
dedicated
DDS
Topic
to
Log
the
security-‐relevant
messages
• DDS
Secure
Log
Topic
will
be
encrypted
3/17/14
©
2012
Real-‐Time
Innova:ons,
Inc.
-‐
All
rights
reserved
88](https://image.slidesharecdn.com/omgddssecurity201403-140327181858-phpapp01/75/OMG-Data-Distribution-Service-Security-88-2048.jpg)