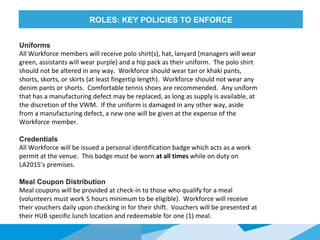
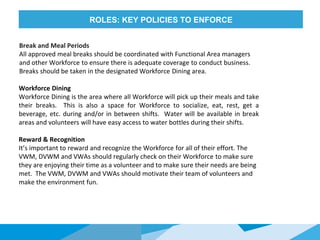
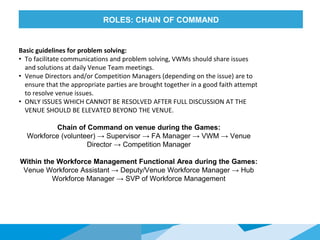
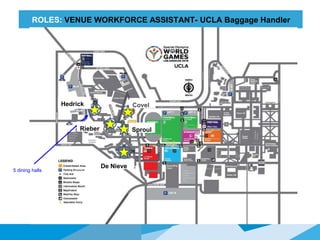
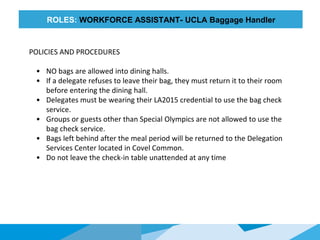
This document provides an overview of training for Venue Workforce Managers, Deputy Managers, and Assistants for the Special Olympics World Games. The training agenda covers the Games Organizing Committee, Volunteer Workforce Management roles and responsibilities, and key policies. Trainees will learn about their specific roles, such as checking in volunteers and distributing meal tickets. The document introduces the Venue Workforce Management teams for various venues. Key policies around uniforms, credentials, meals, and check-in procedures are also outlined.