This document provides tips and recommendations for hardening a WordPress site against hacking and security threats. It discusses typical paths of infection like insecure server configurations or outdated code. It recommends various security measures including keeping backups, using strong passwords, updating software regularly, and restricting access to admin areas and important files. It also suggests security plugins that can help scan sites for vulnerabilities, limit login attempts, backup data, and more. The document emphasizes that while no site is completely hack-proof, administrators can make sites much more difficult to compromise through diligent security practices.



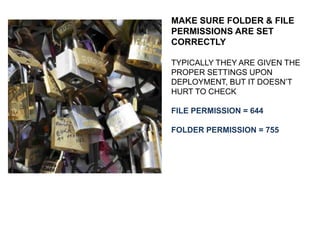
![BY DEFAULT A WORDPRESS DEPLOYMENT DOES NOT INCLUDE
AN .htaccess FILE
ONCE PERMALINKS ARE ACTIVATED IT WILL BE CREATED, BUT
WITH THIS CODE ONLY:
# BEGIN WordPress
<IfModule mod_rewrite.c>
RewriteEngine On
RewriteBase /”site-folder-name”/
RewriteRule ^index.php$ - [L]
RewriteCond %{REQUEST_FILENAME} !-f
RewriteCond %{REQUEST_FILENAME} !-d
RewriteRule . /”SITE-DIRECTORY-NAME”/index.php [L]
</IfModule>
# END WordPress](https://image.slidesharecdn.com/wordpress-hardening-140106123231-phpapp01/85/Wordpress-Security-Hardening-Steps-23-320.jpg)
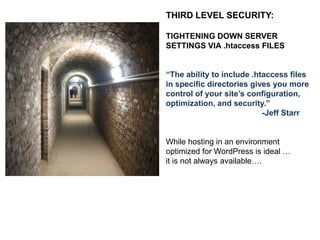
![NEXT: INCLUDE THE FOLLOWING (outside the WP generated code)
#PROTECT HTACCESS FILE
<files .htaccess>
order allow,deny
deny from all
</files>
# SECURE WP-CONFIG.PHP
<Files wp-config.php>
Order Deny,Allow
Deny from all
</Files>
# BLOCK THE INCLUDE-ONLY FILES.
RewriteEngine On
RewriteBase /
RewriteRule ^wp-admin/includes/ - [F,L]
RewriteRule !^wp-includes/ - [S=3]
RewriteRule ^wp-includes/[^/]+.php$ - [F,L]
RewriteRule ^wp-includes/js/tinymce/langs/.+.php - [F,L]
RewriteRule ^wp-includes/theme-compat/ - [F,L]](https://image.slidesharecdn.com/wordpress-hardening-140106123231-phpapp01/85/Wordpress-Security-Hardening-Steps-24-320.jpg)
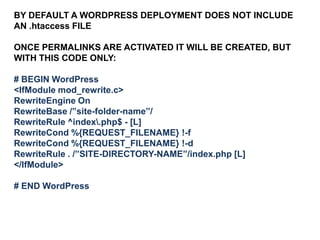
![AN ADDITIONAL RULE WORTH ADDING:
# CANONICAL FAVICONS - A COMMON POINT OF ATTACK
<IfModule mod_rewrite.c>
RewriteEngine On
RewriteBase /
RewriteCond %{REQUEST_URI} !^/favicon.ico$ [NC]
RewriteCond %{REQUEST_URI} /favicon(s)?.?(gif|ico|jpe?g?|png)?$ [NC]
RewriteRule (.*) http://SITEURL/favicon.ico [R=301,L]
</IfModule>](https://image.slidesharecdn.com/wordpress-hardening-140106123231-phpapp01/85/Wordpress-Security-Hardening-Steps-25-320.jpg)
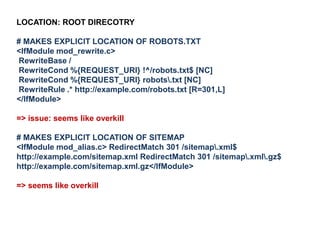
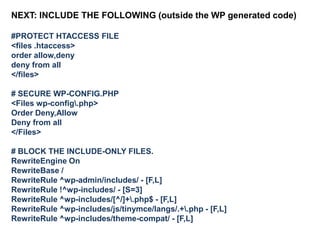
![LOCATION: ROOT DIRECTORY
#Denies “hotlinking” of images
<IfModule mod_rewrite.c>
RewriteEngine on
# ultimate hotlink protection
RewriteCond %{HTTP_REFERER} !^$
RewriteCond %{REQUEST_FILENAME} -f
RewriteCond %{REQUEST_FILENAME} .(gif|jpe?g?|png)$
[NC]
RewriteCond %{HTTP_REFERER}
!^https?://([^.]+.)?(ipstenu.org|taffys.org|halfelf.org|poohnau.us|elfshot.org)
[NC]
RewriteRule .(gif|jpe?g?|png)$
- [F,NC,L]
</ifModule>
=> issue: this disables the theme screenshot display so I don’t use it](https://image.slidesharecdn.com/wordpress-hardening-140106123231-phpapp01/85/Wordpress-Security-Hardening-Steps-29-320.jpg)
![LOCATION: ROOT DIRECTORY
# MAKES EXPLICIT LOCATION OF ROBOTS.TXT
<IfModule mod_rewrite.c>
RewriteBase /
RewriteCond %{REQUEST_URI} !^/robots.txt$ [NC]
RewriteCond %{REQUEST_URI} robots.txt [NC]
RewriteRule .* http://example.com/robots.txt [R=301,L]
</IfModule>
=> issue: seems like overkill
# MAKES EXPLICIT LOCATION OF SITEMAP
<IfModule mod_alias.c> RedirectMatch 301 /sitemap.xml$
http://example.com/sitemap.xml RedirectMatch 301 /sitemap.xml.gz$
http://example.com/sitemap.xml.gz</IfModule>
=> seems like overkill](https://image.slidesharecdn.com/wordpress-hardening-140106123231-phpapp01/85/Wordpress-Security-Hardening-Steps-30-320.jpg)