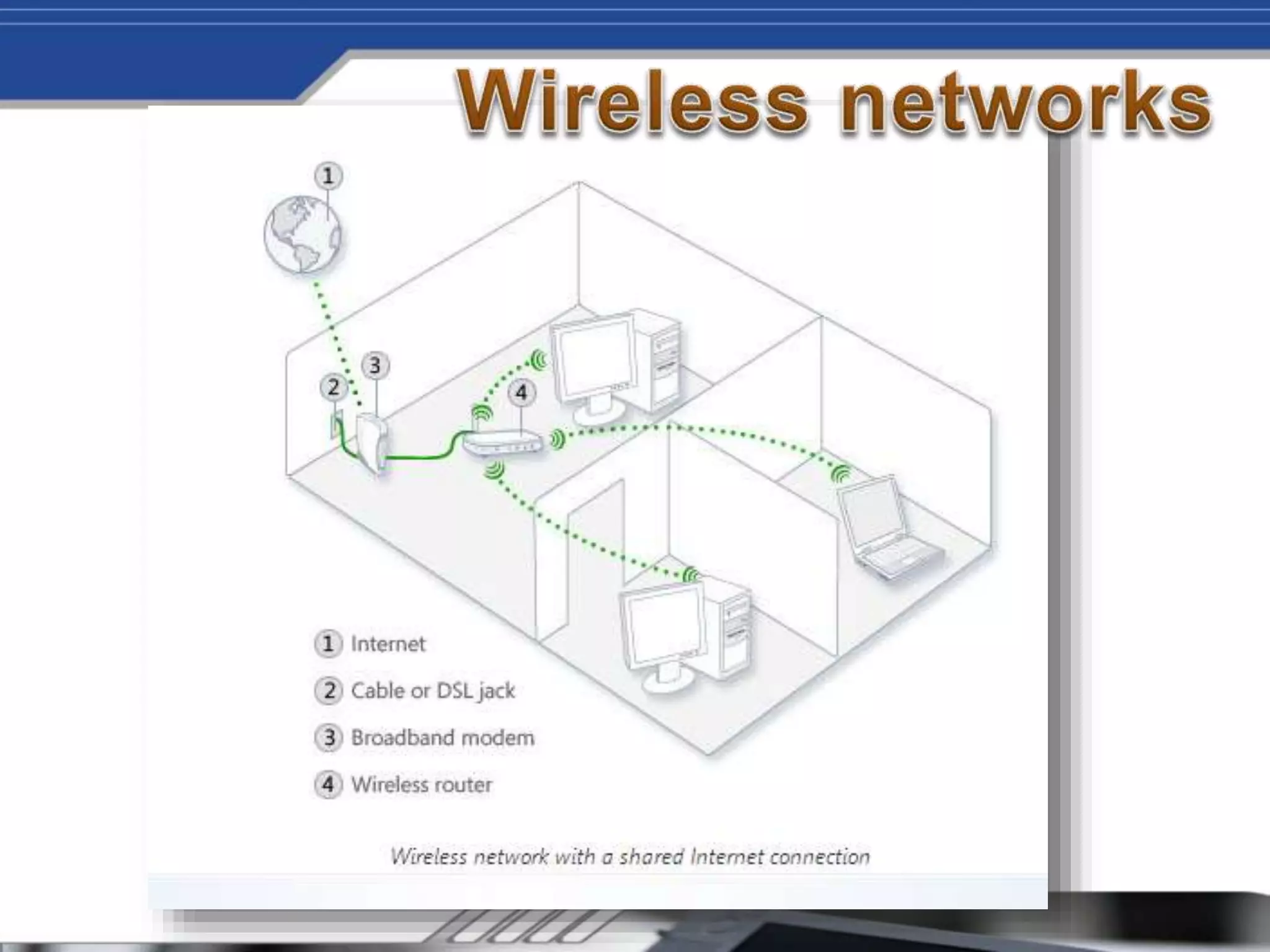
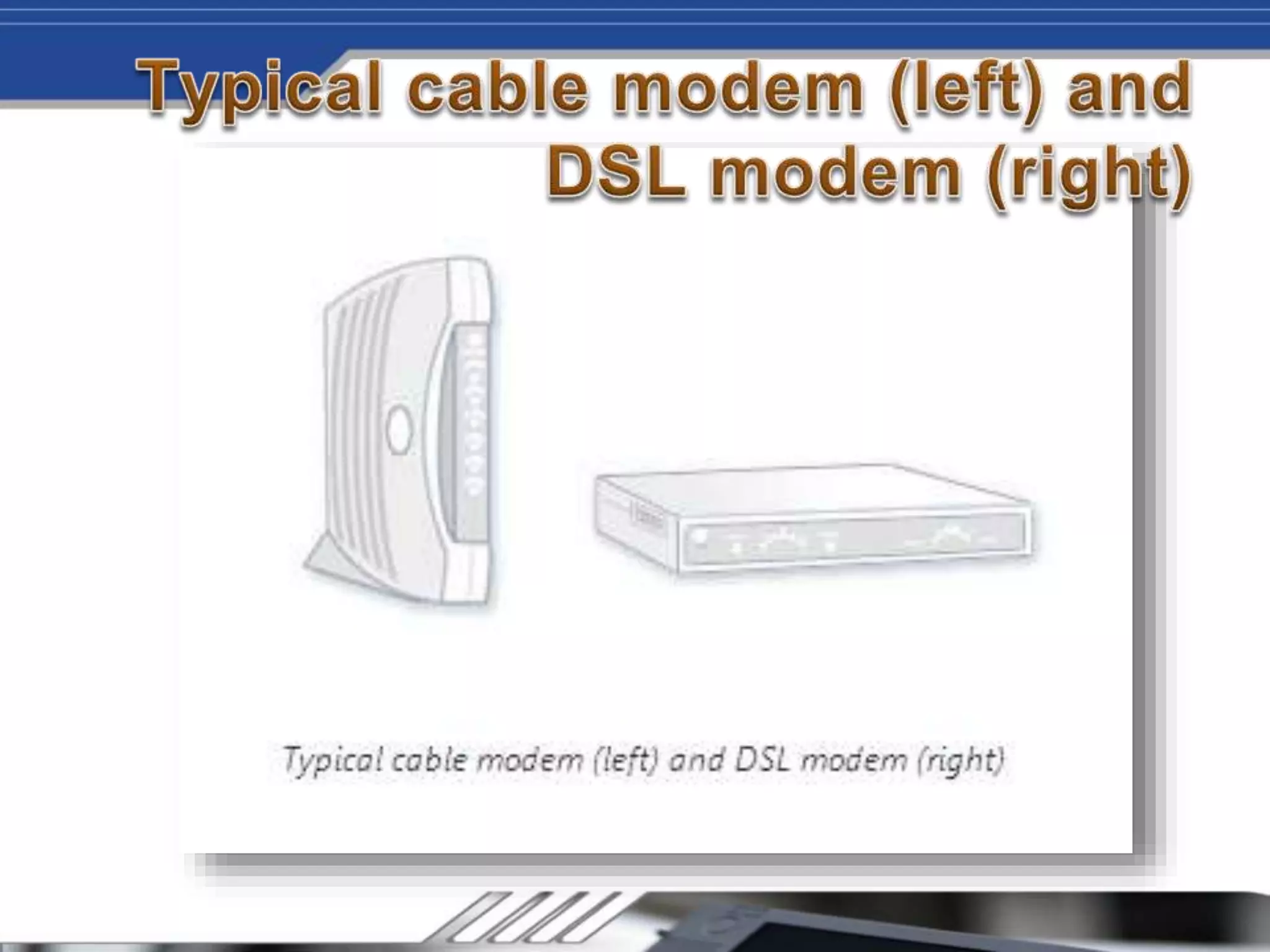
Wireless networks allow devices to connect to the Internet and each other without cables by using radio signals. Setting up a wireless network involves getting a broadband Internet connection, a wireless router, and wireless network adapters for devices if needed. The router sends information between the network and Internet via radio signals instead of wires. It's recommended to use an 802.11g wireless router for a fast and strong wireless signal. Additional steps include installing any necessary wireless adapters into devices.