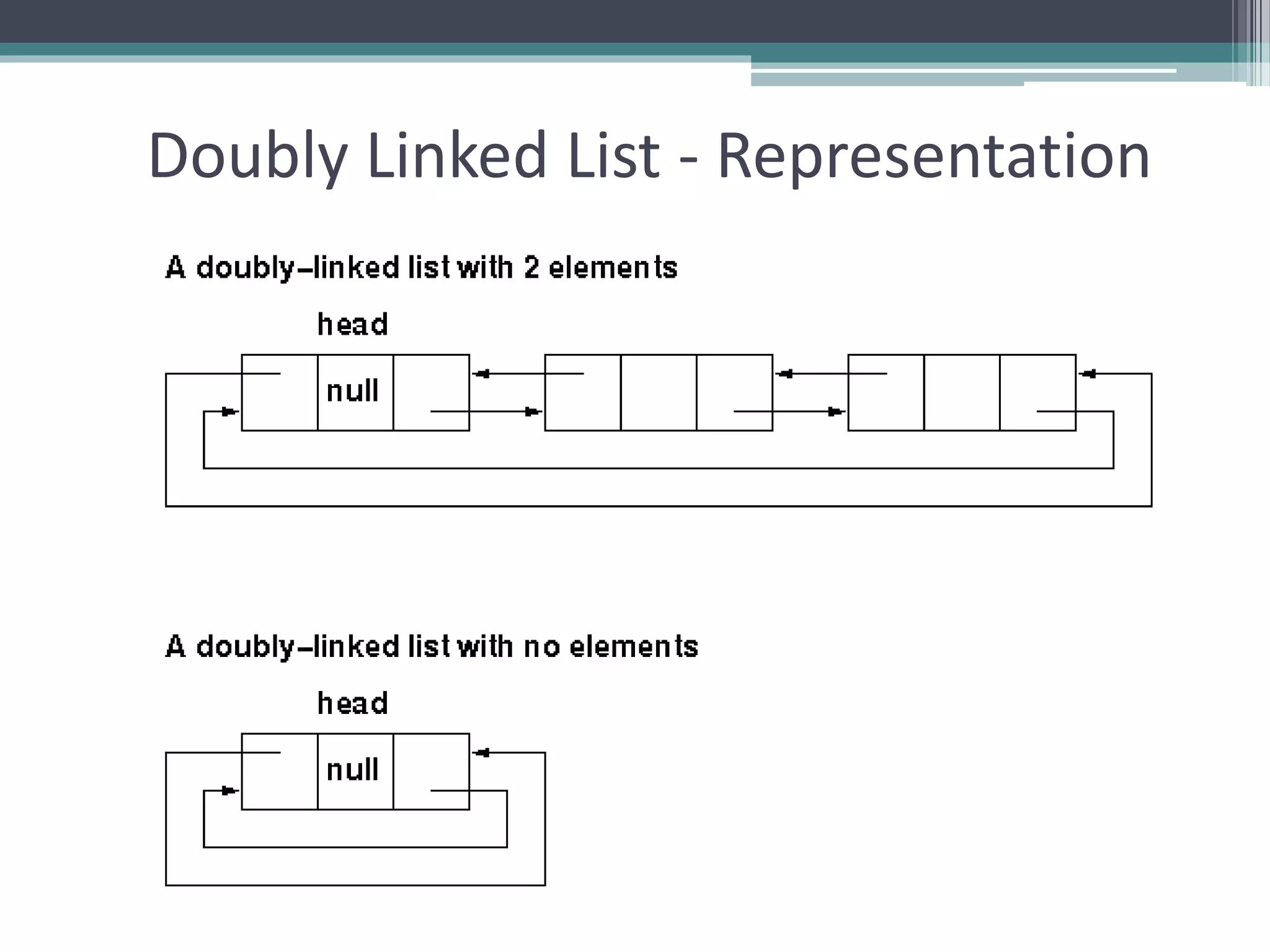
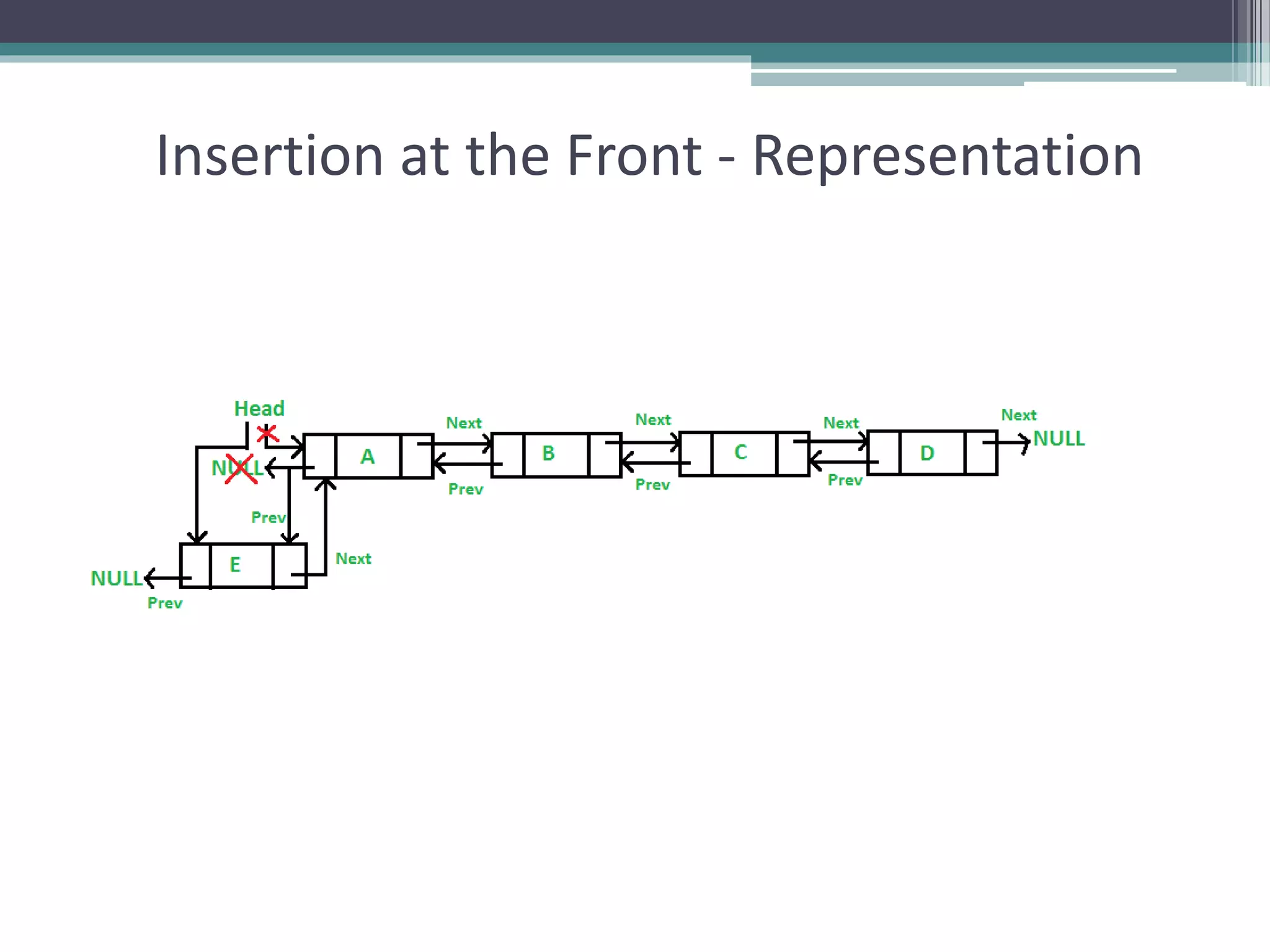
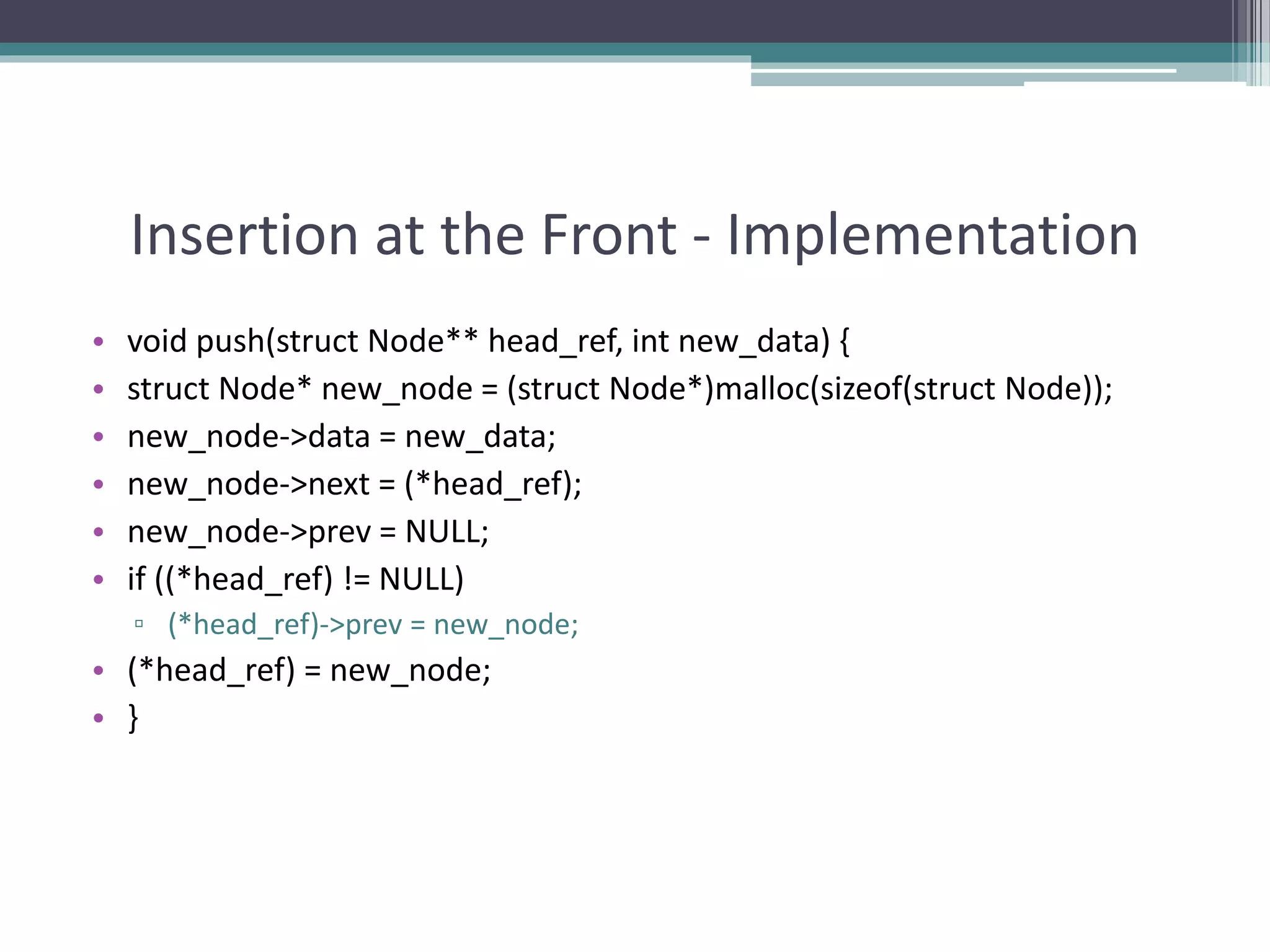
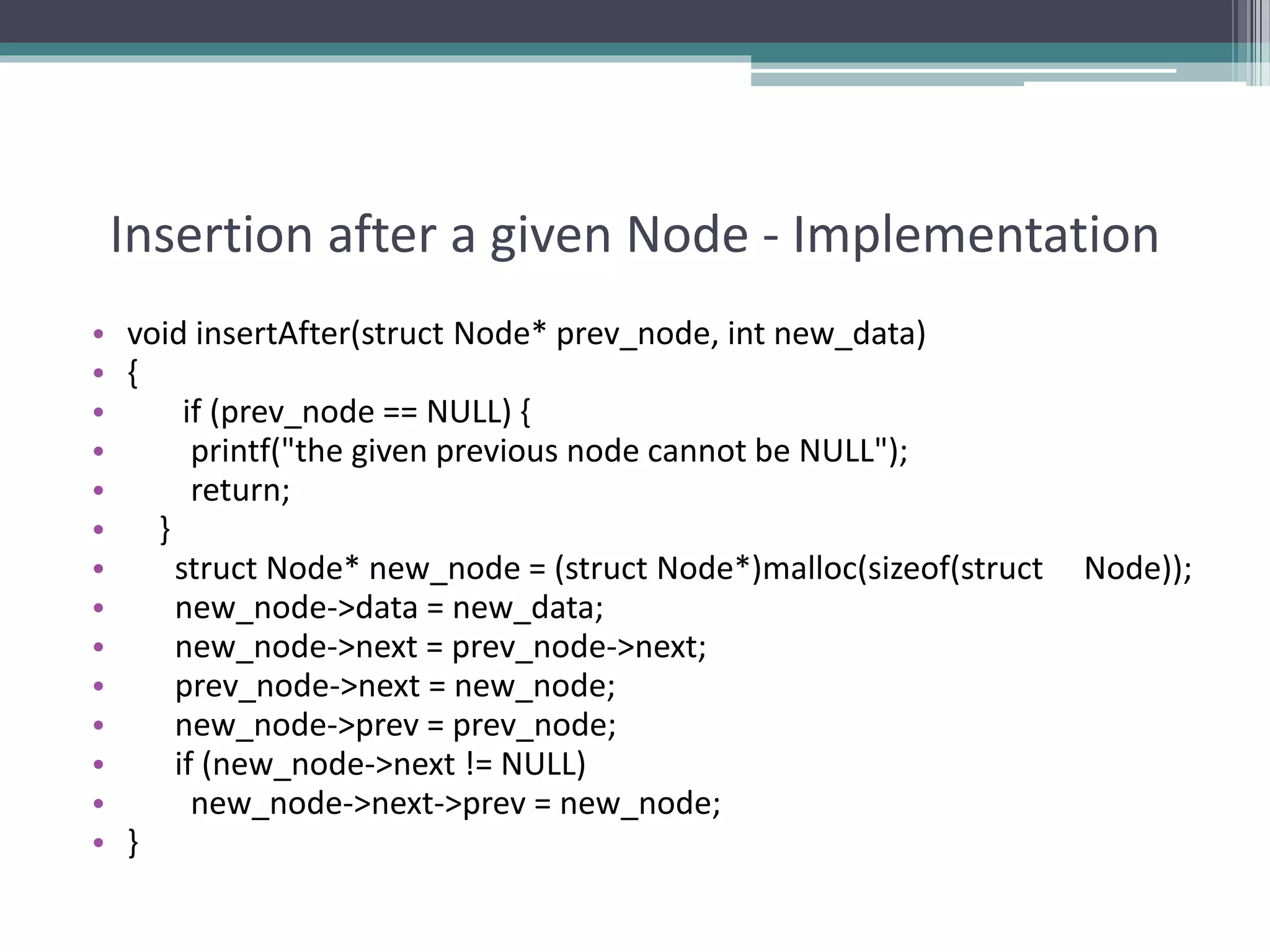
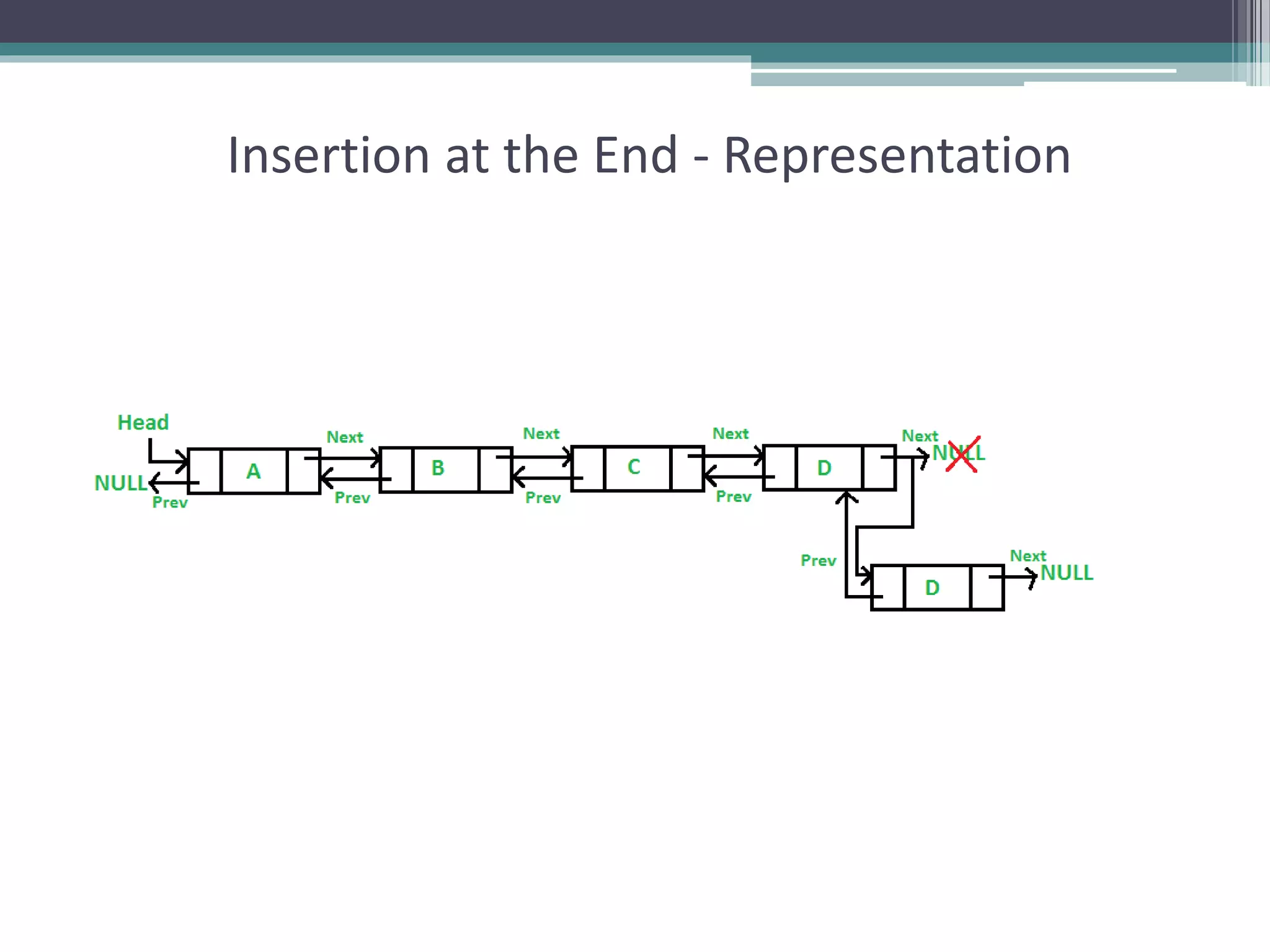
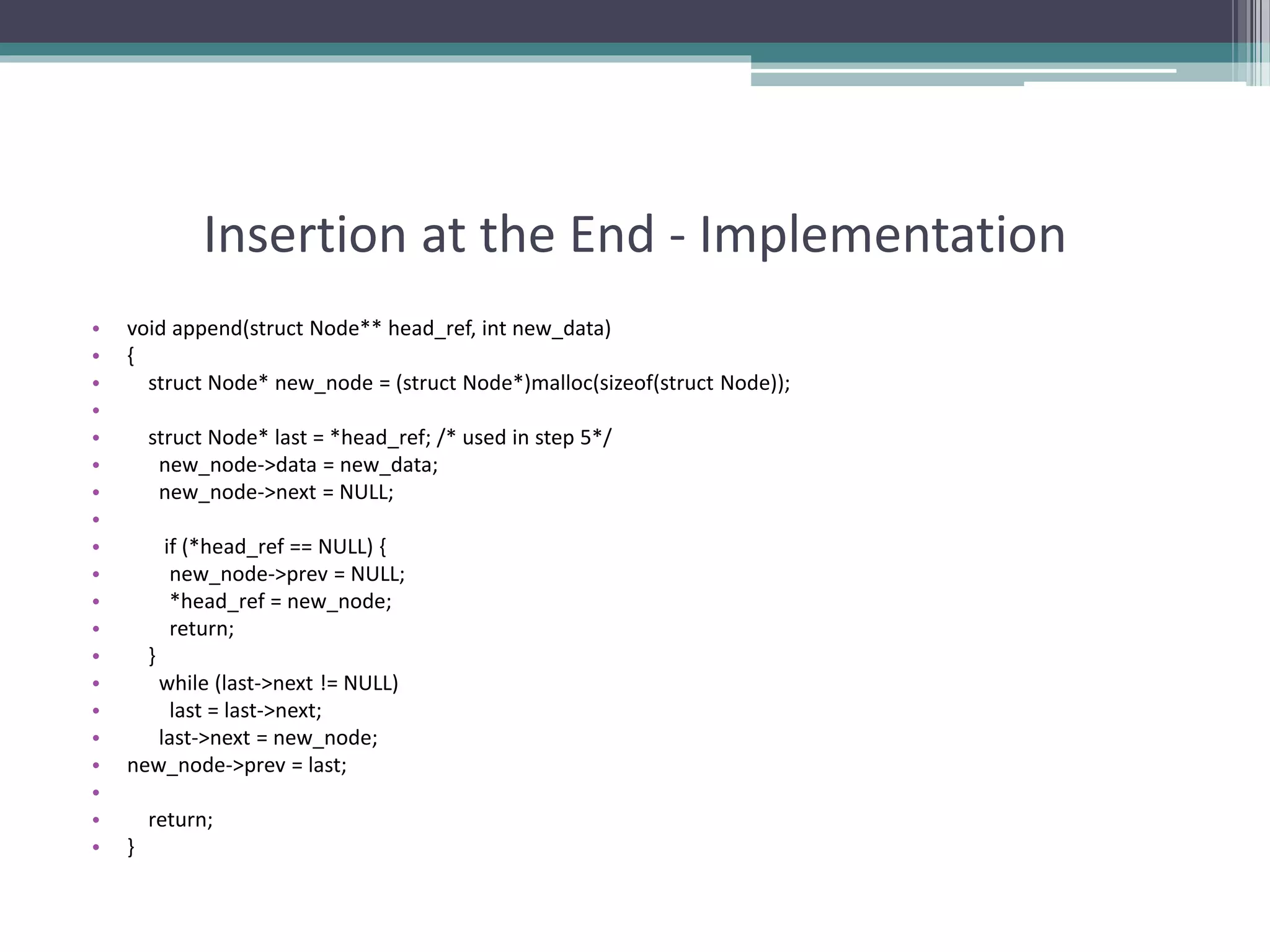
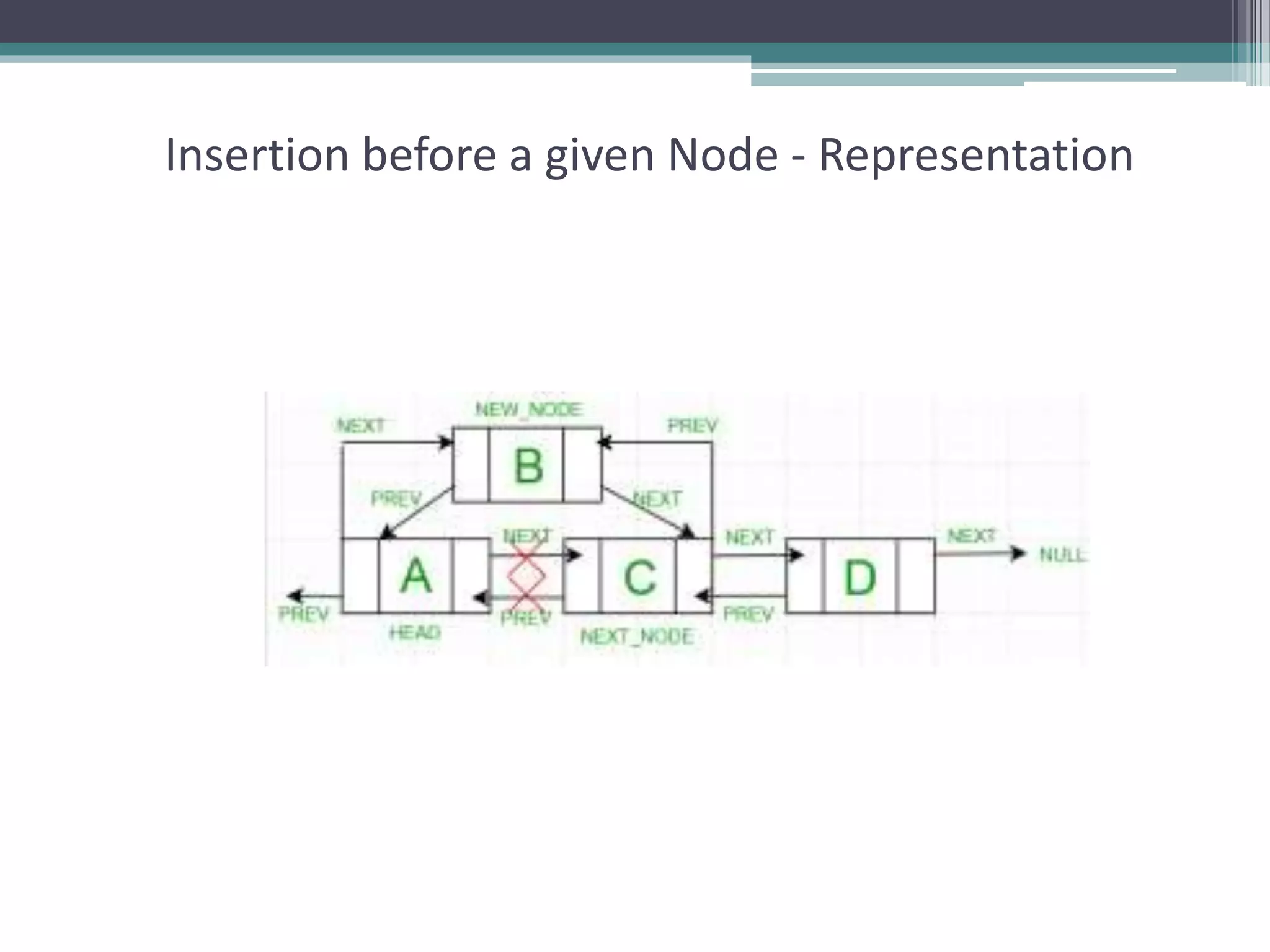
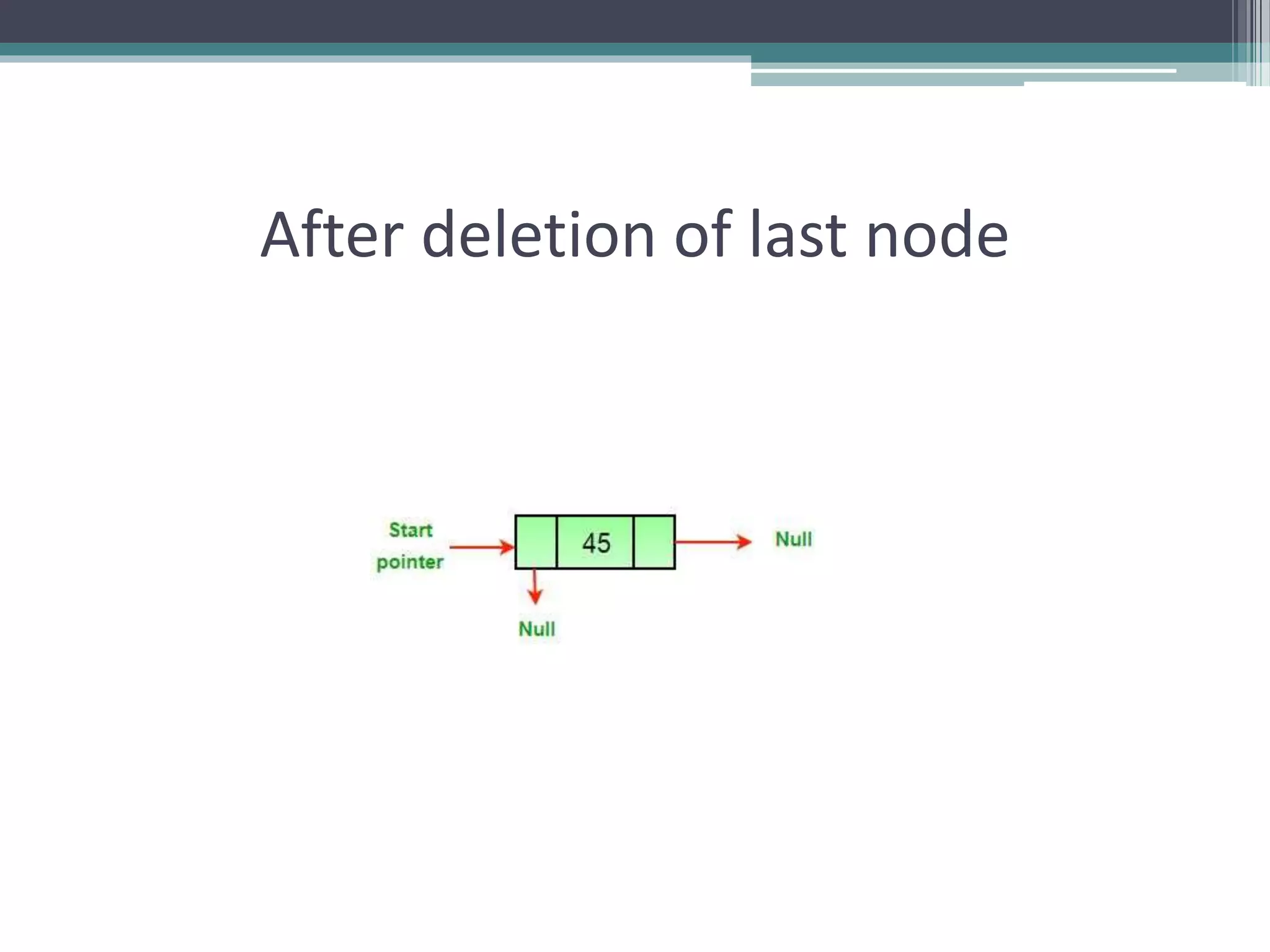
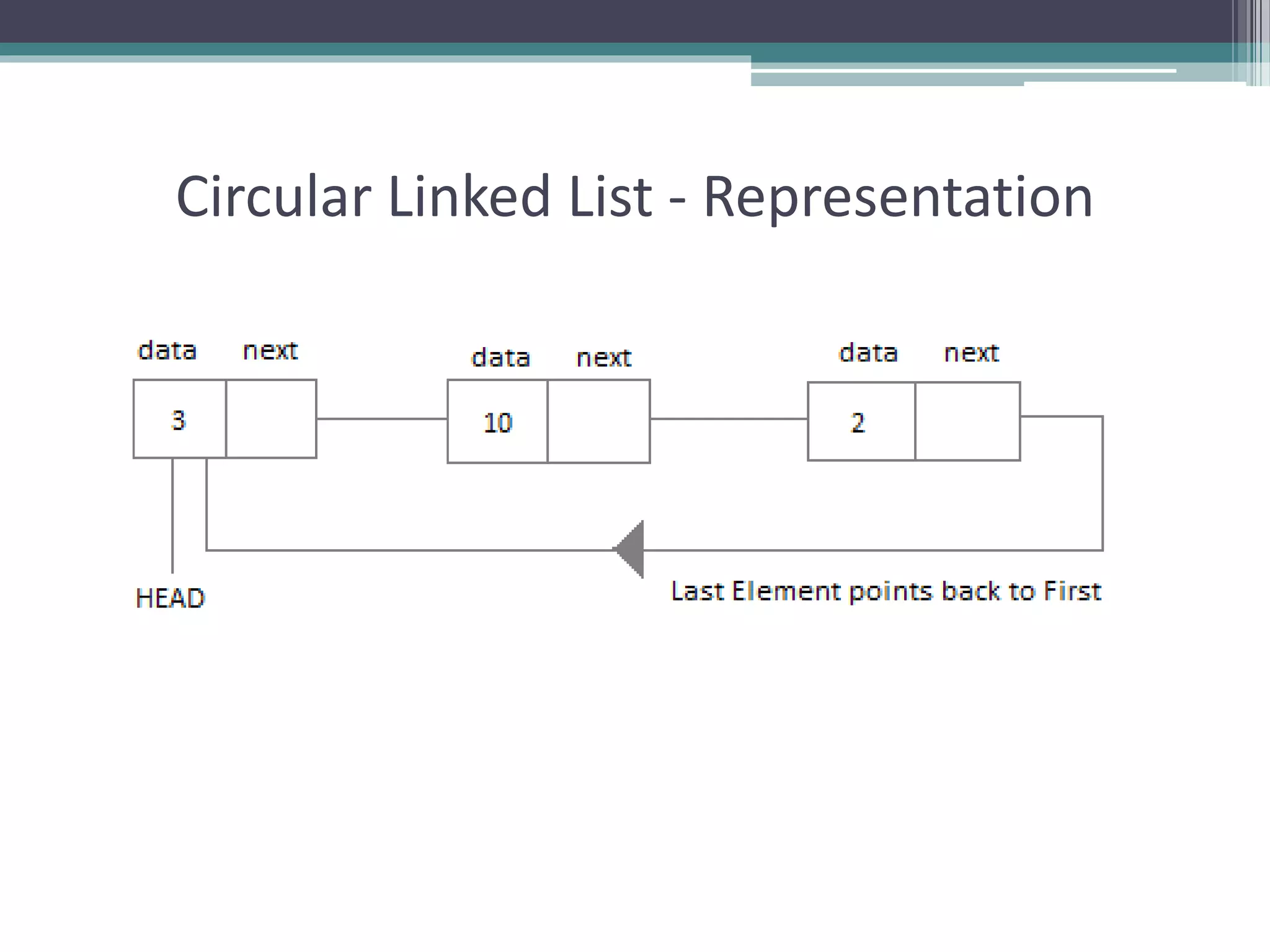
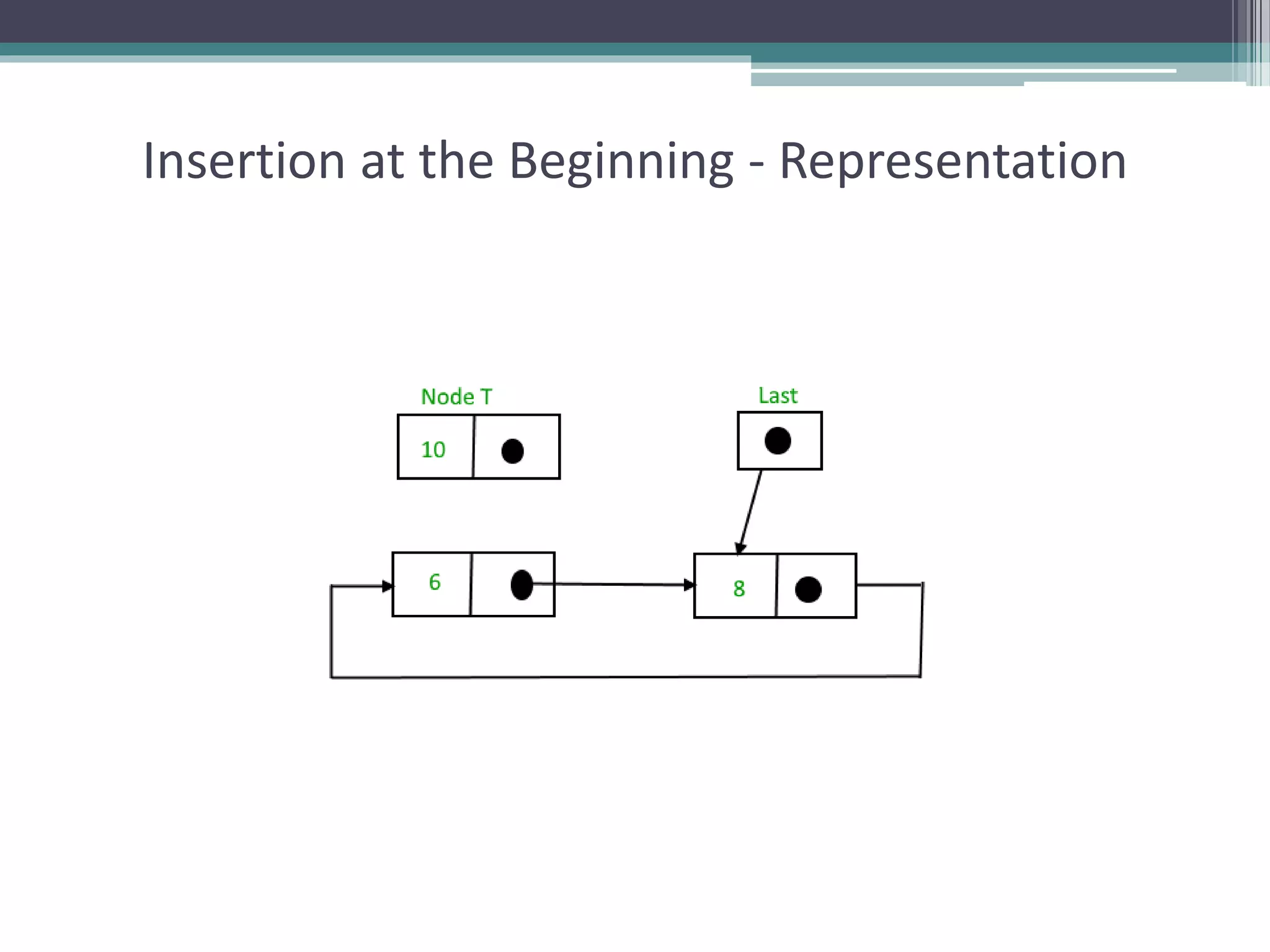
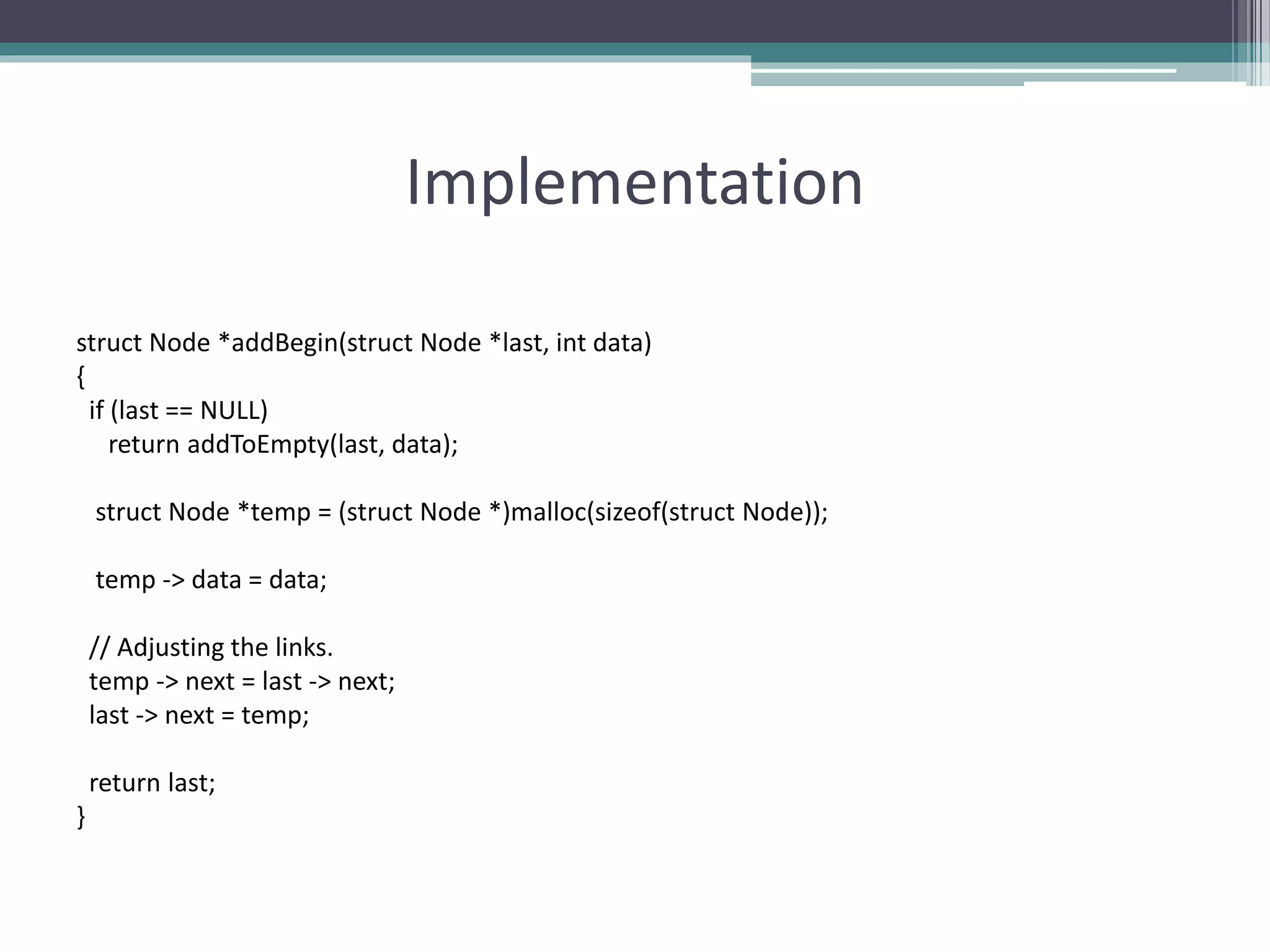
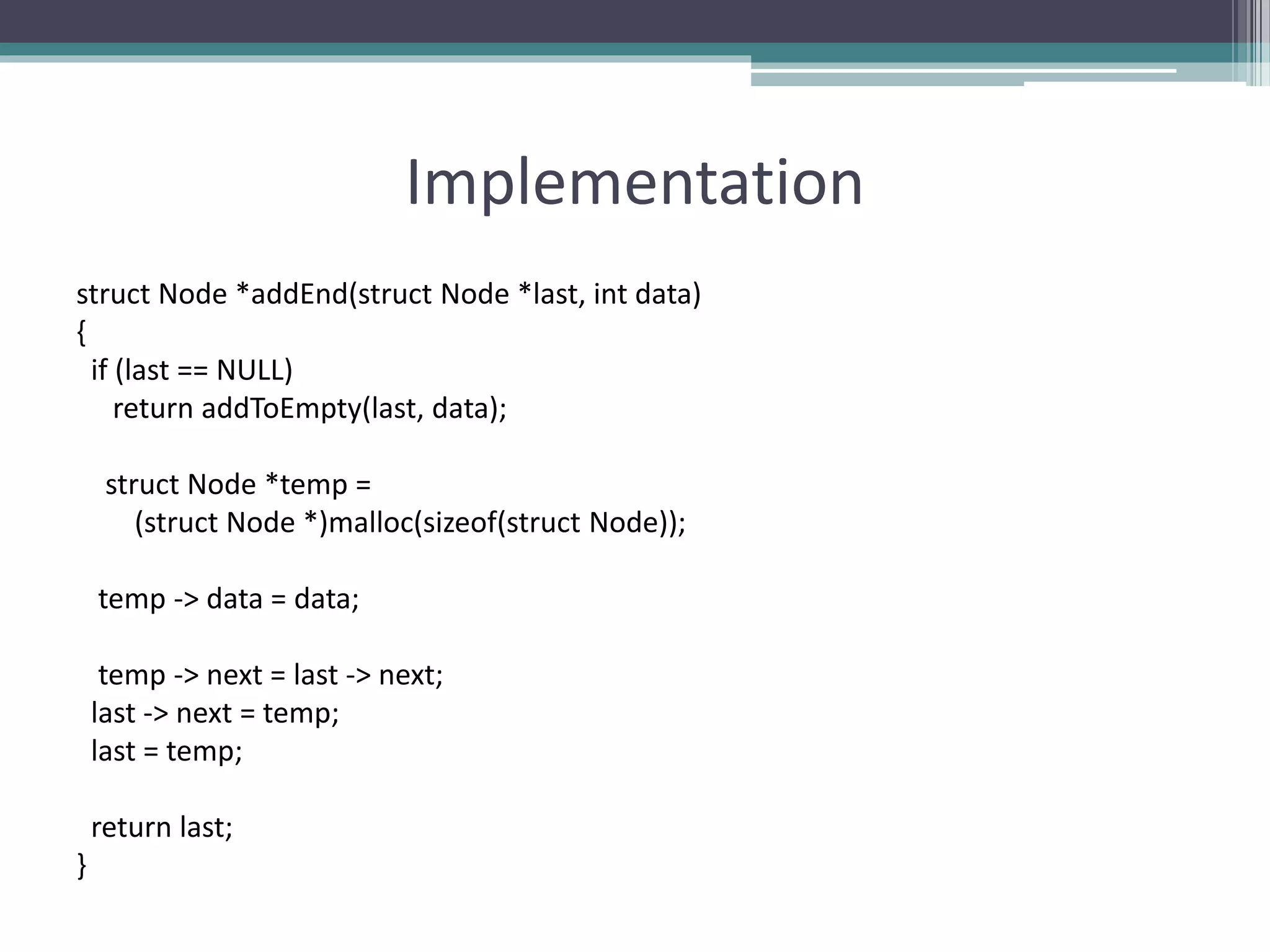
The document discusses double and circular linked lists. It covers inserting and deleting nodes from doubly linked lists and circular linked lists. Specifically, it describes how to insert nodes at different positions in a doubly linked list, such as at the front, after a given node, at the end, and before a given node. It also explains how to delete nodes from a doubly linked list. For circular linked lists, it outlines how to insert nodes in an empty list, at the beginning, at the end, and between nodes. It also provides the steps to delete nodes from a circular linked list.