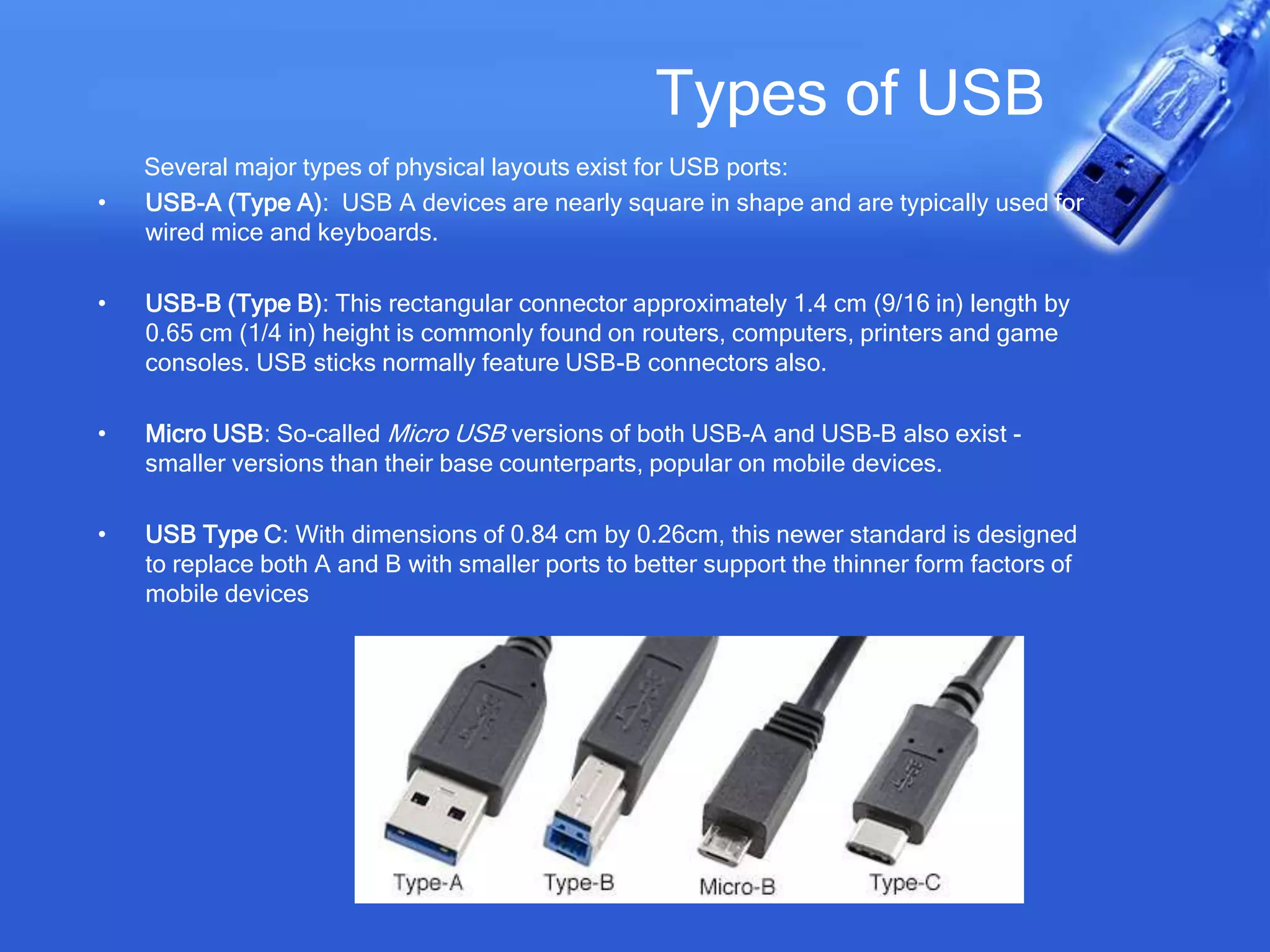
This document provides an overview of USB (Universal Serial Bus). It discusses what USB is, the need for USB, versions of USB including USB 1.x, 2.0, 3.0 and 3.1, types of USB ports, the USB architecture including devices, hosts and interconnects, data transmission over USB using transactions between endpoints and pipes, USB descriptors that provide device information, and common USB usages.