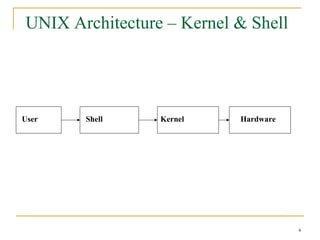
Unix is an operating system that provides an interface between users and hardware. It manages storage, I/O devices, and allows for multi-tasking and multi-user access. The Unix operating system originated in 1969 and has evolved over time with contributions from various universities and companies. It uses a kernel to manage interactions between users, applications, and hardware. The shell is the interface that users interact with to run commands and programs on the system.



![Command Line Format
Syntax:
$ command [-options] [arguments]
1. Separation
2. Order
3. Multiple options
4. Multiple arguments
6](https://image.slidesharecdn.com/unixfundamentals-120808022821-phpapp02/85/Unix-fundamentals-6-320.jpg)









![ chmod [options] file change access rights for named file
For example, to remove read write and execute permissions on the file
biglist for the group and others, type
% chmod go-rwx biglist
This will leave the other permissions unaffected.
To give read and write permissions on the file biglist to all,
% chmod a+rw biglist](https://image.slidesharecdn.com/unixfundamentals-120808022821-phpapp02/85/Unix-fundamentals-16-320.jpg)


![chown - Change File Ownership
Syntax:
chown owner [:group] filename ...
Changes owner of a
file(s) and, optionally, the
Example: group ID
$ id
uid=101 (user1), gid=101 (group1)
$ cp f1 /tmp/user2/f1
$ ls -l /tmp/user2/f1
-rw-r----- 1 user1 group1 3967 Jan 24 13:13 f1
$ chown user2 /tmp/user2/f1
$ ls -l /tmp/user2/f1
-rw-r----- 1 user2 class 3967 Jan 24 13:13 f1
Only the owner of a file (or root) can change the ownership of the file.
19](https://image.slidesharecdn.com/unixfundamentals-120808022821-phpapp02/85/Unix-fundamentals-19-320.jpg)

![su - Switch User Id
Syntax:
su [user_name]
Change your effective user ID and group ID
Example:
$ ls -l f1
-rwxr-x--- 1 user1 group1 3967 Jan 24 23:13 class_setup
$ id
uid=303 (user1), gid=300 (group1)
$ su – user2
Password:
$ id
uid=400 (user2), gid=300 (group1)
21](https://image.slidesharecdn.com/unixfundamentals-120808022821-phpapp02/85/Unix-fundamentals-21-320.jpg)


![Starting and Ending a vi
Session
vi [filename] Start a vi edit session of file
Example:
$ vi testfile
- If the file doesn’t exist, it will be created
- Otherwise vi will open the existing file
All modifications are made to the copy of the file brought into
memory.
:wq or :x or <shift-zz> write and quit
:w write
:q quit
:q! Quit without saving
24](https://image.slidesharecdn.com/unixfundamentals-120808022821-phpapp02/85/Unix-fundamentals-24-320.jpg)







