This document provides an introduction to using UNIX. It outlines the course aims of explaining what UNIX is used for and how to navigate files and directories. The agenda covers a brief history of UNIX, logging on, working with files and directories, commands like vi editor, and customizing the login environment. It describes the kernel, commands/utilities, and shell that make up the UNIX operating system model. It also explains the file structure, special characters, and transferring files between Windows and UNIX.

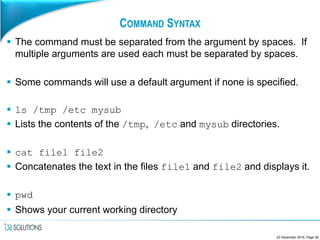
![COMMAND SYNTAX
The following syntax is common to the majority of UNIX and Linux
commands:
<command> [ <options> ] [ <arguments> ]
Options modify what the command will do. Arguments are what the
command will act against.
Different commands will take different options, some of which
maybe upper or lower case, depending on the command.
Normally when a command completes successfully there will be no
response back to the screen, you will just get your command prompt
back.
23 December 2016, Page 29](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-29-320.jpg)

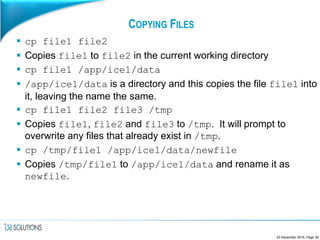
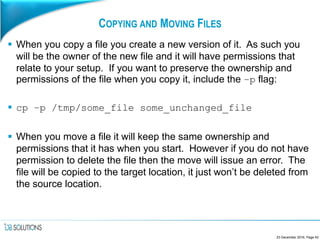
![COPYING FILES
Use the cp command to copy files:
cp [-i] <file-list> <destination>
The destination can be either a file or a directory. If a directory is
specified then multiple files can be listed in the <file-list>.
If a destination file is specified then it will be overwritten if it exists,
unless you specify the –i flag. If specified this causes cp to prompt
to overwrite an existing file.
23 December 2016, Page 38](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-38-320.jpg)
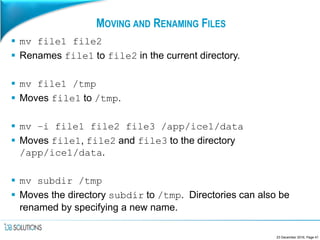
![MOVING AND RENAMING FILES
Use the mv command to move and rename files:
mv [-i] <file-list> <destination>
The destination can be either a file or a directory. If a directory is
specified then multiple files can be listed in the <file-list>.
When a directory is specified then the listed files will be moved to
that directory.
If the destination is a file then only a single file can be specified in
the <file-list> and the file will be renamed.
As with cp files will be overwritten unless the –i flag is specified.
23 December 2016, Page 40](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-40-320.jpg)
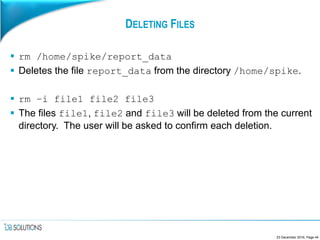
![DELETING FILES
Use the rm command to delete files:
rm [-i] <file-list>
All listed files are deleted. If the –I option is used then the user is
prompted to confirm the deletion of each file before it occurs. Each
file is deleted as it is confirmed. If you change your mind part way
through a long list of files the earlier files will already have been
deleted!
DELETED FILES CAN NOT BE RECOVERED UNLESS DONE SO
FROM A BACKUP. THERE IS NO RECYCLE BIN!
23 December 2016, Page 43](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-43-320.jpg)

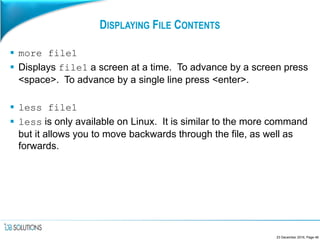
![DISPLAYING FILE CONTENTS
There are various commands that you can use to view the contents
of files. The following slides deal with the commonly used ones.
cat file1 file2
Concatenates the text in the files file1 and file2. The entire
contents of the files are output to the screen. If there are more rows
in the file than there are lines on the screen then the excess output
will scroll off the top of the screen.
head [–n] file1
Displays the top n lines of file1 to the screen. If n is not specified
then the top 10 rows are shown.
23 December 2016, Page 46](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-46-320.jpg)
![DISPLAYING FILE CONTENTS
tail [–n –f] file1
The opposite of head, tail shows you the bottom n rows of a file.
Again if n is not specified then the bottom 10 rows will be shown. If
you wish to see lines being appended to the bottom of the file (such
as a log file) then the –f flag can be used.
tail –f /logs/script.log
Shows you lines as they are appended to the file
/logs/script.log. The command will not return until you hit
<ctrl> + <c>.
23 December 2016, Page 47](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-47-320.jpg)

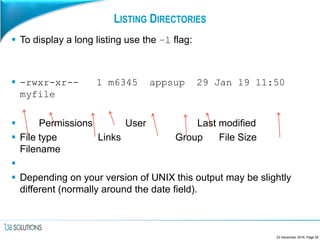
![LISTING DIRECTORIES
Directory contents can be listed using the same ls command that is
used for files:
ls [<options>] [<filename-list>]
When a directory is specified its contents will be listed. If no
filename is specified then the current directory is listed. If only files
are specified then only details relating to those files will be shown.
23 December 2016, Page 53](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-53-320.jpg)
![CREATING DIRECTORIES
Use the mkdir command to create directories:
mkdir [-p] <directory-list>
mkdir scripts work
Creates directories called scripts and work in the current
directory.
mkdir /home/m6345/temp
Creates a directory called temp in /home/m6345. If /home/m6345
doesn’t exist an error will be reported.
mkdir –p /home/m9999/work_files
Creates a directory called work_files in /home/m9999. If either
/home or m9999 do not exist they will also be created.
23 December 2016, Page 60](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-60-320.jpg)
![FILENAME WILDCARDS
Most commands that deal with files will accept multiple filenames for
processing. If several files with similar names are to be referenced
this can be done in a single argument using wildcards.
• * represents zero or more matches of any character.
• ? represents a single occurrence of any character.
• [...] represent a single occurrence of any of the characters listed between the
brackets.
The exception to this is if you want to see hidden files. If either of
the first two wildcard characters are used the . must be specified.
23 December 2016, Page 65](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-65-320.jpg)
![FILENAME WILDCARDS
ls –l s*
Lists all files beginning with s in the current directory.
mv .???? /tmp
Moves all hidden files with 5 character names (including the leading
.) to the directory /tmp.
cp * /home/m6345
Copies all files in the current directory (except hidden files) to the
directory /home/m6345.
rm *[0-4]
Deletes all files (except hidden files) that end in the numbers 0, 1, 2,
3 or 4.
23 December 2016, Page 66](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-66-320.jpg)
![FILENAME WILDCARDS
To handle those times when you want everything that does NOT
match you can use an exclamation mark in the [..] wildcard
notation. It has to be specified as the first character in the class:
ls –l [!A-Z]*
Lists all non-hidden files that DO NOT start with the an uppercase
character.
23 December 2016, Page 67](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-67-320.jpg)







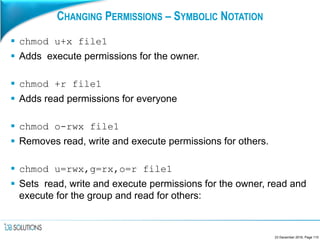
![CHANGING PERMISSIONS – SYMBOLIC NOTATION
Symbolic notation has three elements:
[<who>]<operator><permissions>
Where:
• <who> is any combination of the letters u (owner), g (group) and o (others). The letter
a represents the combination ugo and this is assumed if <who> is omitted.
• <operator> is either + (add), - (remove) or = (set).
• <permissions> is any combination of the letters r, w and x.
23 December 2016, Page 109](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-109-320.jpg)
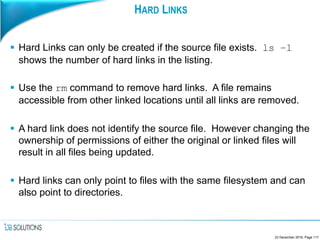
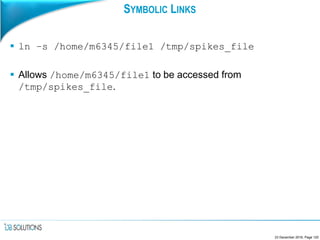
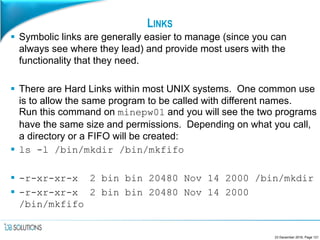
![LINKING FILES
A single file can be accessed from multiple locations with the use of
links. You might do this for instance to provide the same profile to a
number of different users.
In many of the standard Perl binary locations link back to one binary
(check out /bin/perl for instance).
The command to create links is:
ln [-s] <source-file> < link-destination>
Two types of link can be made, Hard links and Symbolic links.
Symbolic links are created by including the –s flag in the command
call.
23 December 2016, Page 116](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-116-320.jpg)

![PROCESSES
The operating system will keep track of all running processes and
records information such as the process owner, a unique process ID
(PID) and the parent process ID (PPID). (The PPID is used to ‘wake
up’ the parent call when the child completes).
To view the process table use the ps command.
ps [<options>]
To show all the processes for the current user, run ps with no
options. It will tell you the PID, the terminal the process is running
on, the amount of CPU being used and the name of the process.
23 December 2016, Page 129](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-129-320.jpg)
![KILLING PROCESSES
Use the kill command to kill a process:
kill [<signal>] <pid-number>
There are many signals that can be used but the common ones are:
1HUP “Hang-up” Sent to all of a user’s processes when they log
out.
2INT “Interupt” Sent to a foreground process when a user hits
<ctrl>+<c>
9KILL “Kill” Sent to processes by the kill -9 command.
Terminates the process immediately, not allowing it to
tidy up.
15 TERM “Termination” Instructs the process to terminate cleanly.
A complete list can be found by running kill –l.
23 December 2016, Page 131](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-131-320.jpg)
![JOB CONTROL
To view all the jobs you currently have running use:
jobs [-l]
Lists all the jobs you have running in background mode or
suspended along with their job number (which is allocated by the
shell). The –l flag will include the jobs PID in the listing.
Once you know a job’s number you can bring it to the foreground:
fg [%<job-number>]
If the job number is omitted then the last job suspended will be
brought forward.
23 December 2016, Page 136](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-136-320.jpg)
![JOB CONTROL
To kill a job running in the background use:
kill –STOP %<job-number>
On some systems the alias stop can also be used:
stop %<job-number>
To put a job that is suspended into background mode use:
bg [%<job-number]
If no job number is included then the last suspended job will be put
into background mode.
A lower priority is given to background jobs .
23 December 2016, Page 137](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-137-320.jpg)


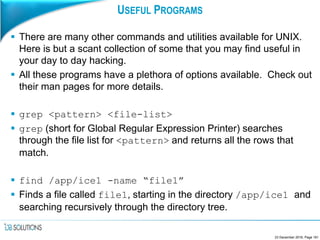
![USEFUL PROGRAMS
sort <file>
Sorts a file into alphabetical order. DO NOT redirect the output to
your input file as the file will be overwritten! Check out the –o
option.
cut –f1 –f3 <file>
Takes input and cuts it into fields and outputs fields 1 and 3. By
default fields are delimited by whitespace, however you can change
that using –d.
finger [-m] <user-id>
Looks up a user in the /etc/passwd file. Specifying –m means
that only exact matches will be printed.
23 December 2016, Page 162](https://image.slidesharecdn.com/abeginnersintroductiontounix-161223173520/85/A-beginners-introduction-to-unix-162-320.jpg)