This document provides an overview of basic Unix commands including ls, cd, pwd, mkdir, rm, rmdir, cp, find, touch, echo, cat, who, and du. It explains what each command is used for and provides examples of common usages. The document serves as a beginner's guide to learning Unix commands.


![rm is often aliased to "rm -i" so as to avoid accidental deletion of files. If a user still
wishes to delete a large number of files without confirmation, they can manually cancel
out the -i argument by adding the -f option.
"rm -rf" (variously, "rm -rf /", "rm -rf *", and others) is frequently used in jokes and
anecdotes about Unix disasters. The "rm -rf /" variant of the command, if run by an
administrator, would cause the contents of every mounted disk on the computer to be
deleted.
rmdir
is a command which will remove an empty directory on a Unix-system. It cannot be
capitalized. Normal usage is straightforward where one types:
rmdir name_of_directory
Where name_of_directory corresponds with the name of the directory one wishes to
delete. There are options to this command such as -p which removes parent directories if
they are also empty.
For example:
rmdir –p foo/bar/baz
Will first remove baz/, then bar/ and finally foo/ thus removing the entire directory tree
specified in the command argument.
Often rmdir will not remove a directory if there is still files present in the directory. To
force the removal of the directory even if files are present usually the -rf flag can be used.
For example:
rmdir -Rf for/bar/baz
cp
is the command entered in a Unix shell to copy a file from one place to another, possibly
on a different filesystem. The original file remains unchanged, and the new file may have
the same or a different name.
To Copy a File to another File
cp [ -f ] [ -h ] [ -i ] [ -p ][ -- ] SourceFile TargetFile
To Copy a File to a Directory
cp [ -f ] [ -h ] [ -i ] [ -p ] [ -r | -R ] [ -- ] SourceFile ... TargetDirectory
To Copy a Directory to a Directory
cp [ -f ] [ -h ] [ -i ] [ -p ] [ -- ] { -r | -R } SourceDirectory ... TargetDirectory
-f (force) – specifies removal of the target file if it cannot be opened for write operations.](https://image.slidesharecdn.com/unix-basics-for-testers-090929073704-phpapp01/85/Unix-Basics-For-Testers-3-320.jpg)


![Search all directories
find / -name "myfile" -type f -print
This searches every file on the computer for a file with the name myfile. It is generally
not a good idea to look for data files this way. This can take a considerable amount of
time, so it is best to specify the directory more precisely.
Specify a directory
find /home/brian -name "myfile" -type f -print
This searches for files named myfile in the /home/brian directory, which is the home
directory for the user brian. You should always specify the directory to the deepest level
you can remember.
Find any one of differently named files
find . ( -name "*jsp" -or -name "*java" ) -type f -ls
This prints extended information on any file whose name ends with either 'jsp' or 'java'.
Note that the parentheses are required. Also note that the operator "or" can be abbreviated
as "o". The "and" operator is assumed where no operator is given. In many shells the
parentheses must be escaped with a backslash, "(" and ")", to prevent them from being
interpreted as special shell characters.
touch
is a program on Unix and Unix-like systems used to change a file's date- and time-stamp.
It can also be used to create an empty file. The command-syntax is:
touch [options] <file_name>
If the file exists, its access and modification time-stamps are set to the system's current
date and time, as if the file had been changed. To touch a file simulates a change to the
file. If the file does not exist, an empty file of that name is created with its access and
modification time-stamps set to the system's current date and time. If no file path is
specified, the current directory is assumed.
touch can be invoked with options to change its behaviour, which may vary from one
Unix to another. One option makes it possible to set the file's time-stamp to something
other than the current system date and time, but this action is normally restricted to the
owner of the file or the system's superuser.
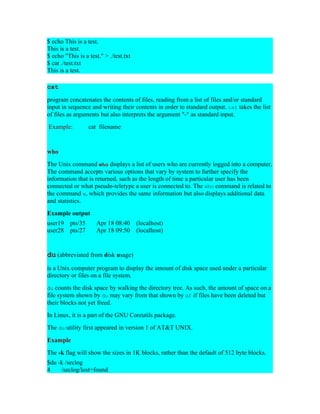
echo
is a command in Unix (and by extension, its descendants, such as Linux) and MS-DOS
that places a string on the terminal. It is typically used in shell scripts and batch programs
to output status text to the screen or a file.](https://image.slidesharecdn.com/unix-basics-for-testers-090929073704-phpapp01/85/Unix-Basics-For-Testers-6-320.jpg)