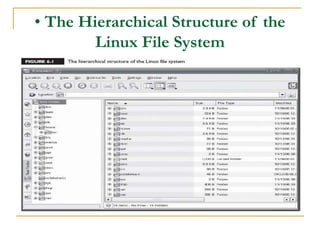
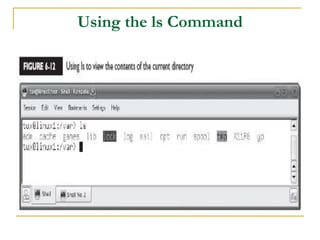
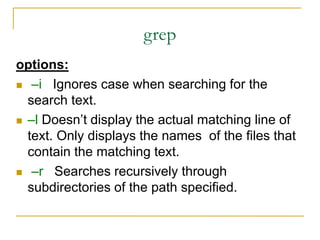
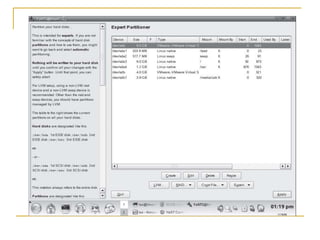
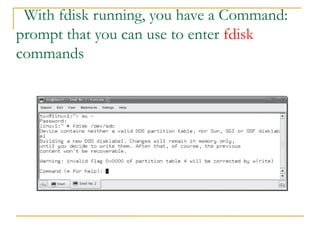
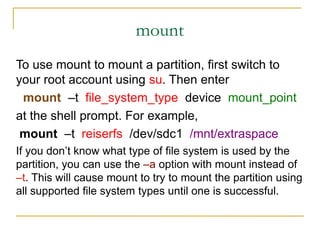
This document discusses managing the Linux file system. It describes the Linux file system structure, including the main directories like /bin, /home, /etc. It also covers common file system tasks like navigating directories, managing files and directories by creating, deleting, copying and moving files. Additional topics covered include managing disk partitions by creating partitions with fdisk and formatting partitions with file systems using mkfs, mounting partitions, and checking file systems with fsck.