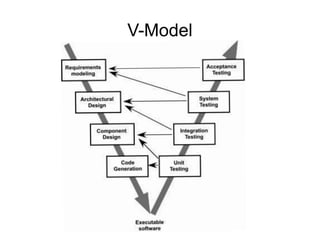
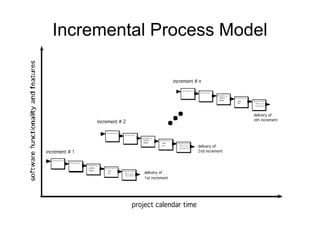
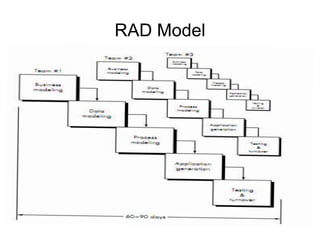
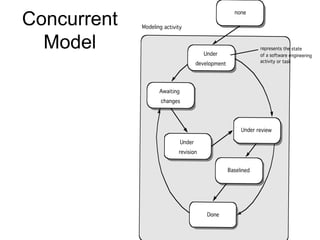
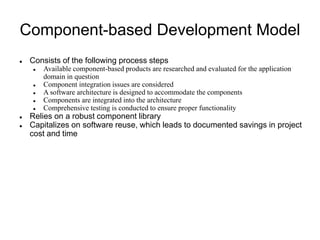
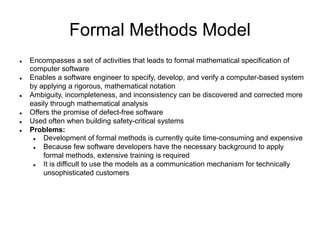
The document discusses various software engineering process models, including prescriptive, V-model, incremental, evolutionary, and RAD models, each with distinct characteristics and use cases. It highlights the importance of meticulously defined requirements and the iterative nature of software development to manage risks and adapt to changing needs. Specialized process models like component-based development, formal methods, and aspect-oriented software development (AOSD) are also briefly examined for their roles in enhancing software quality and efficiency.