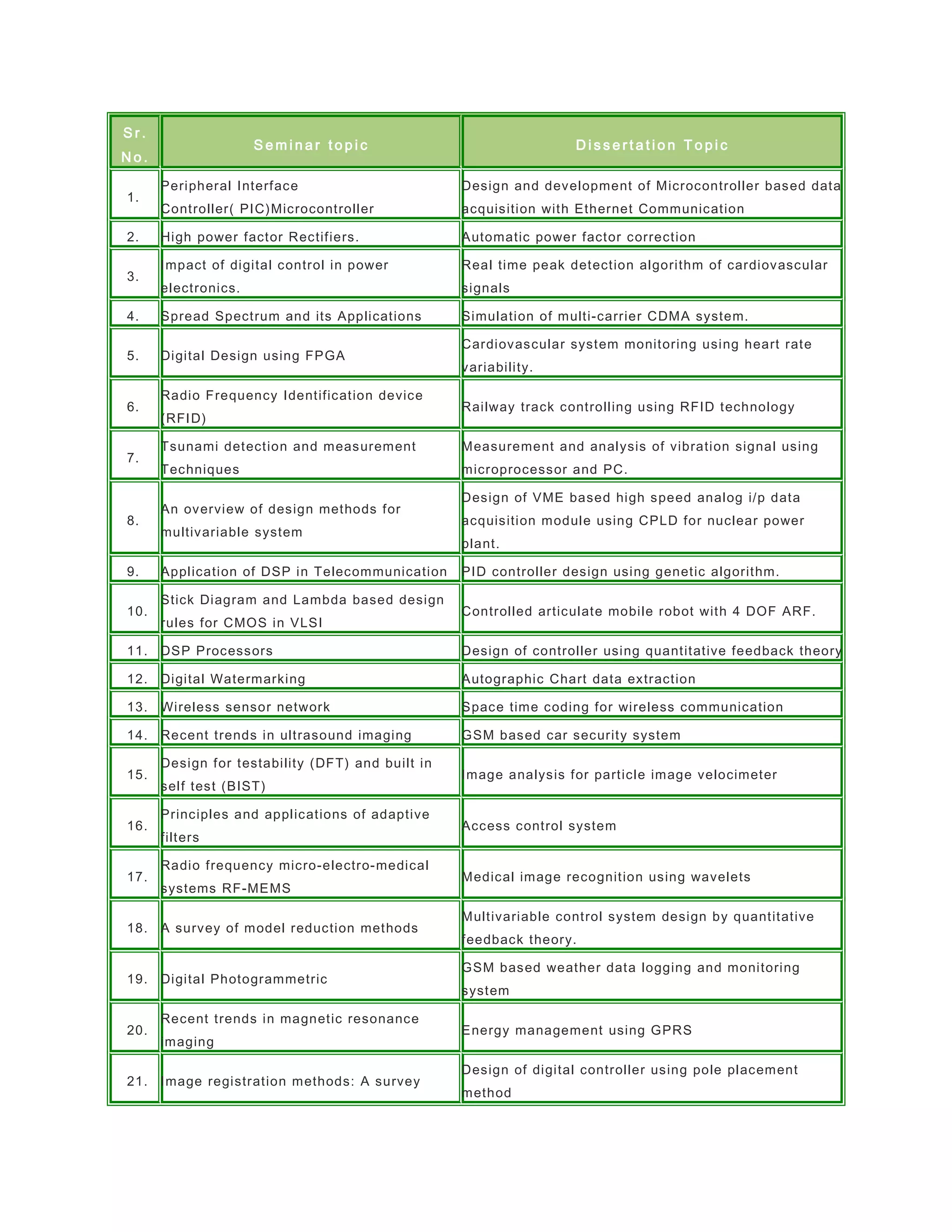
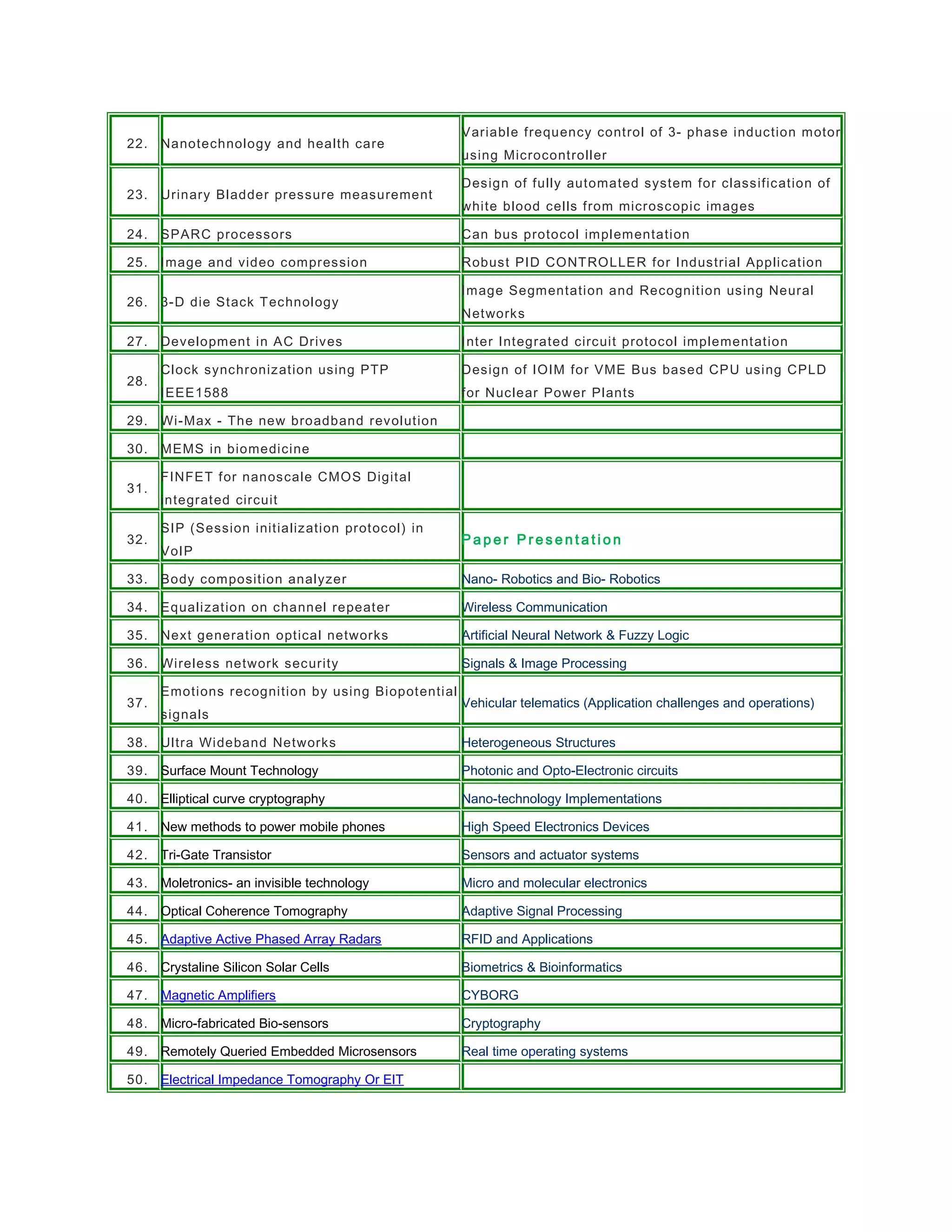
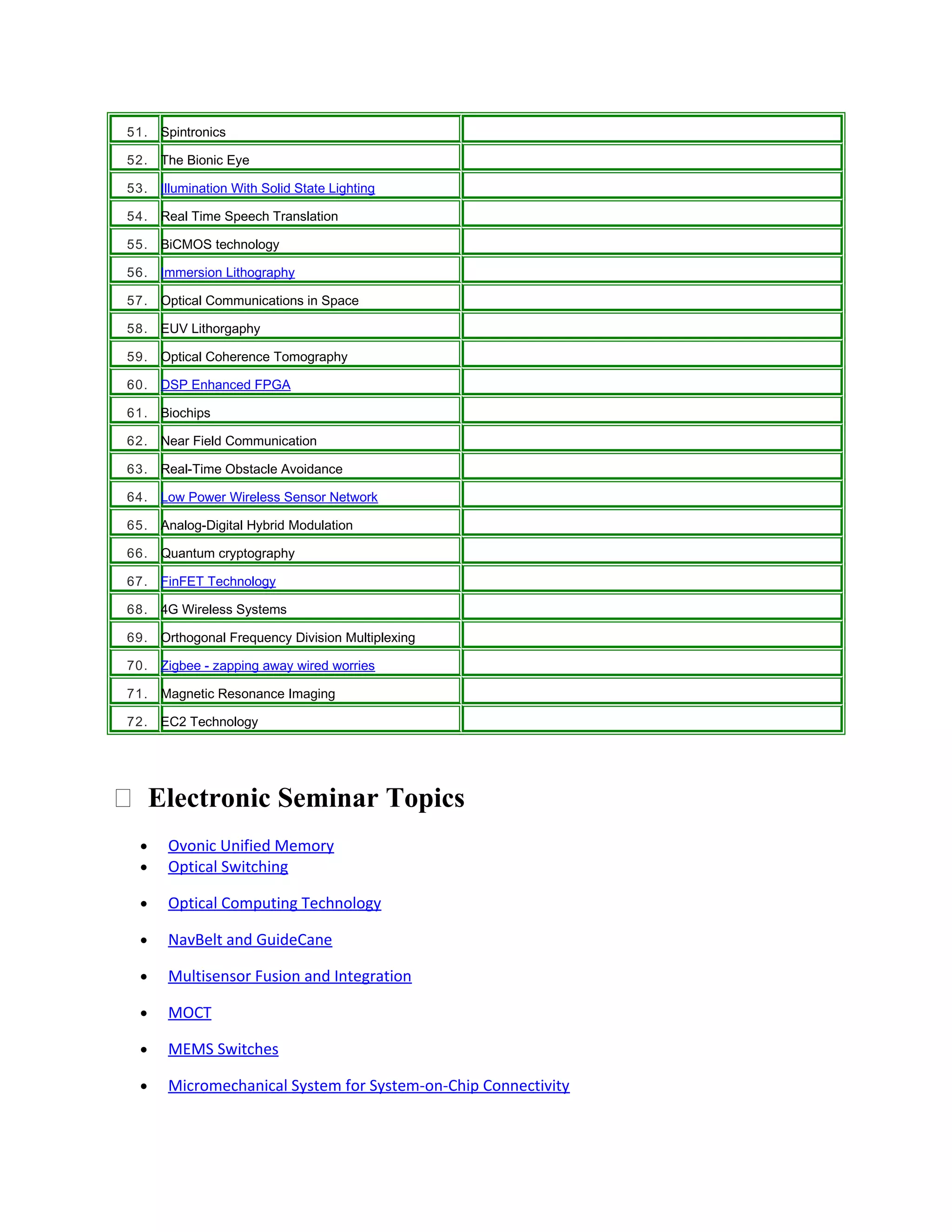
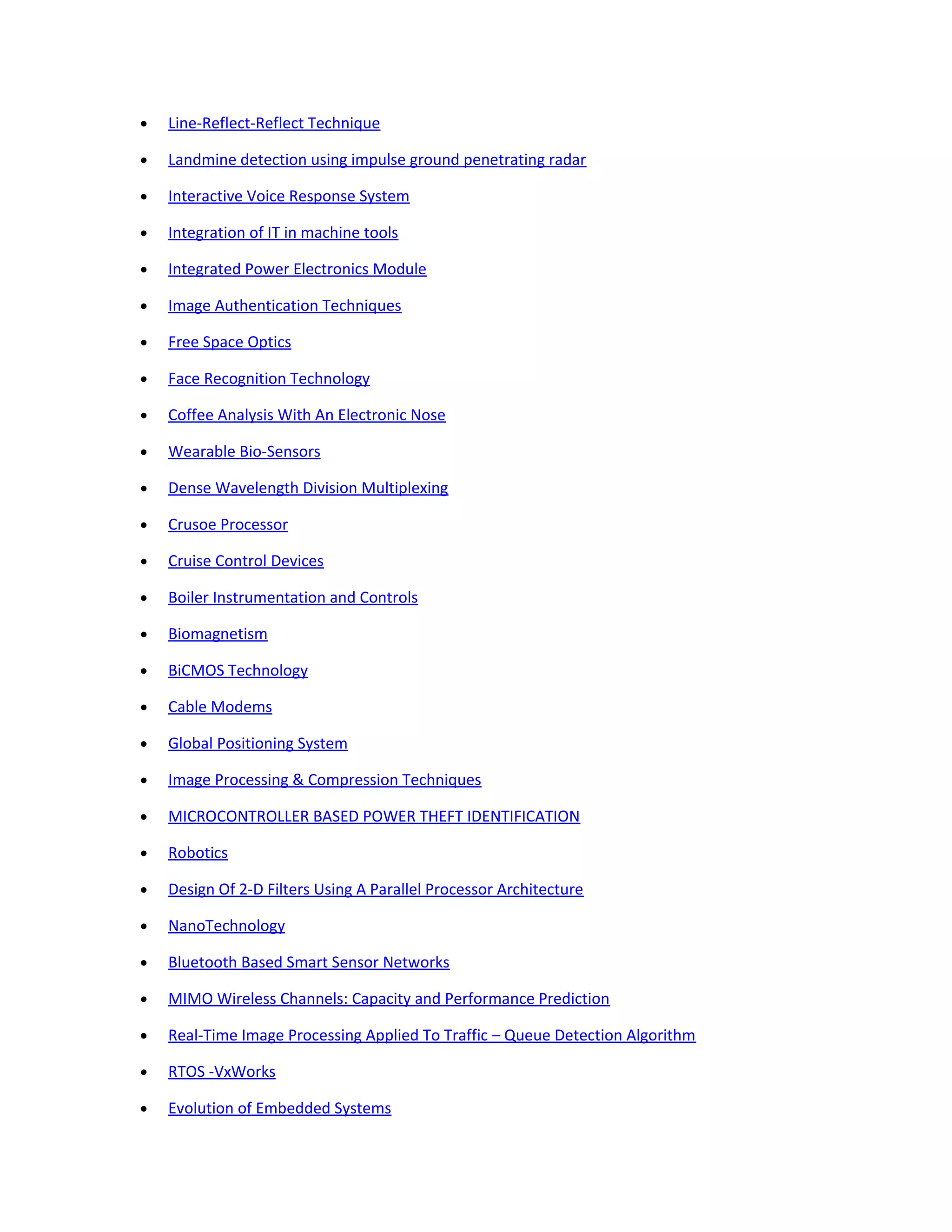
This document contains a list of 75 seminar topics related to electronics and computer science. Each topic includes a brief 1-2 sentence description of a potential dissertation related to the seminar topic. The topics cover a wide range of subjects including microcontrollers, power electronics, digital signal processing, telecommunications, wireless networks, embedded systems, and more.