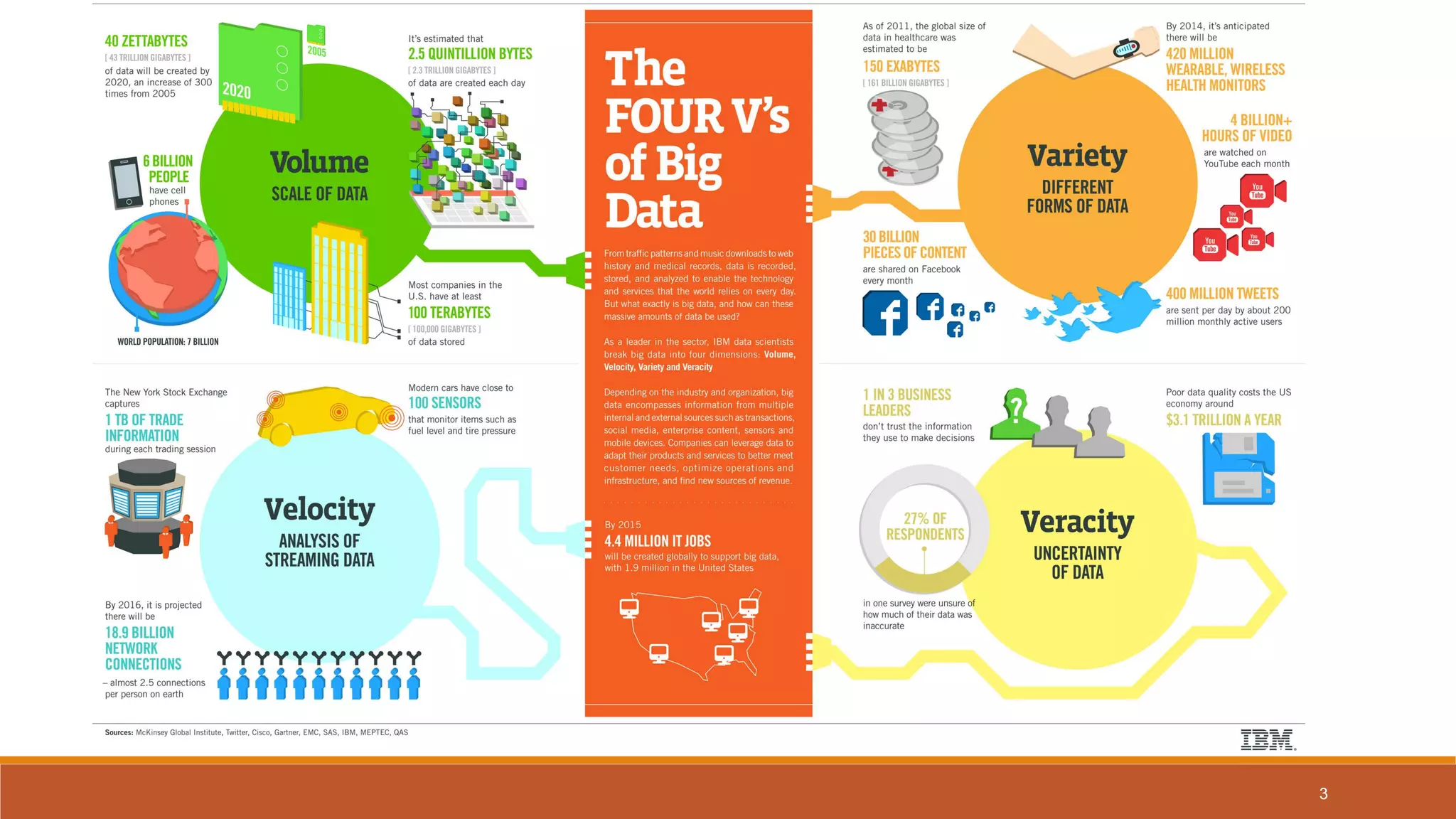
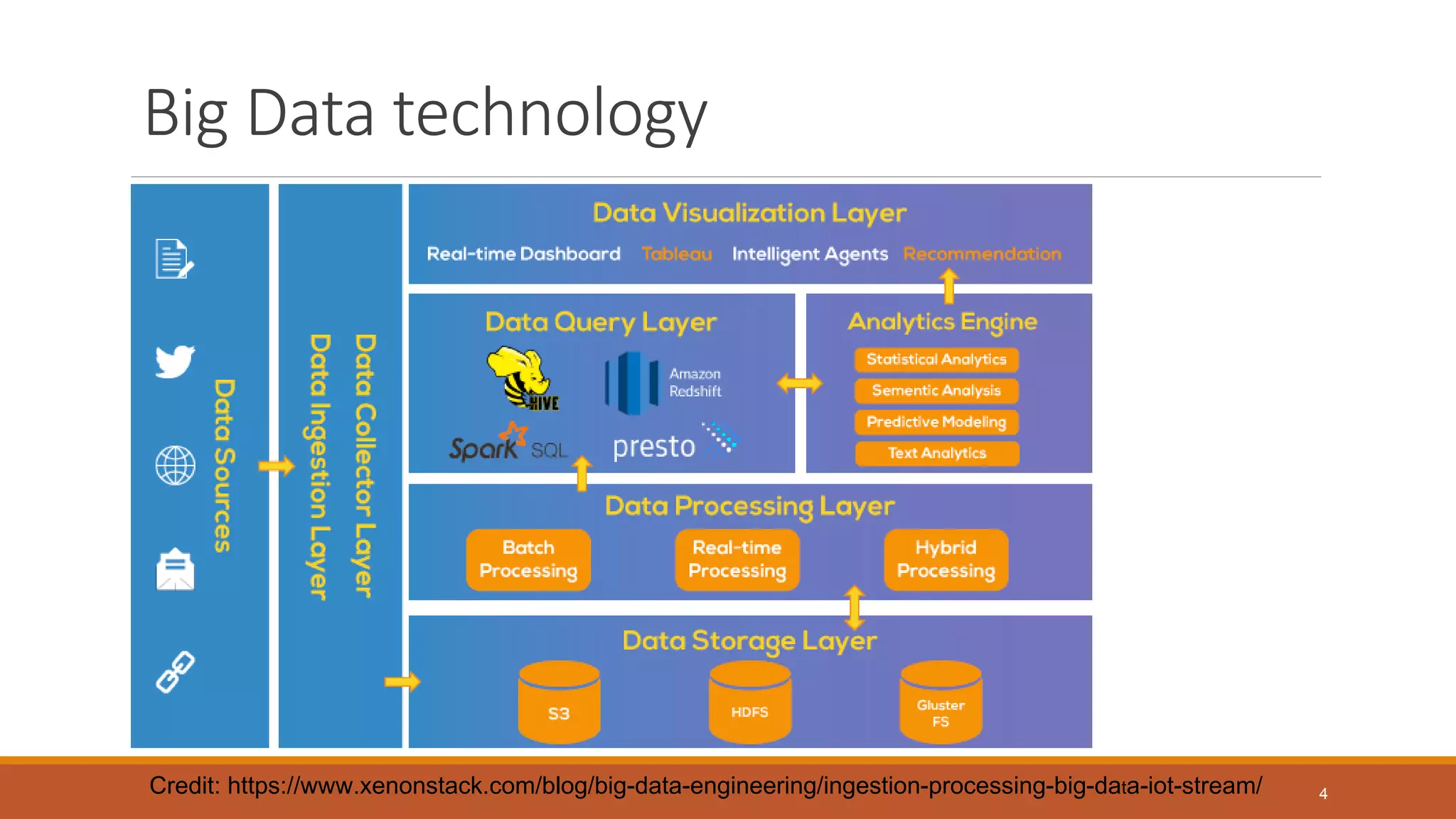
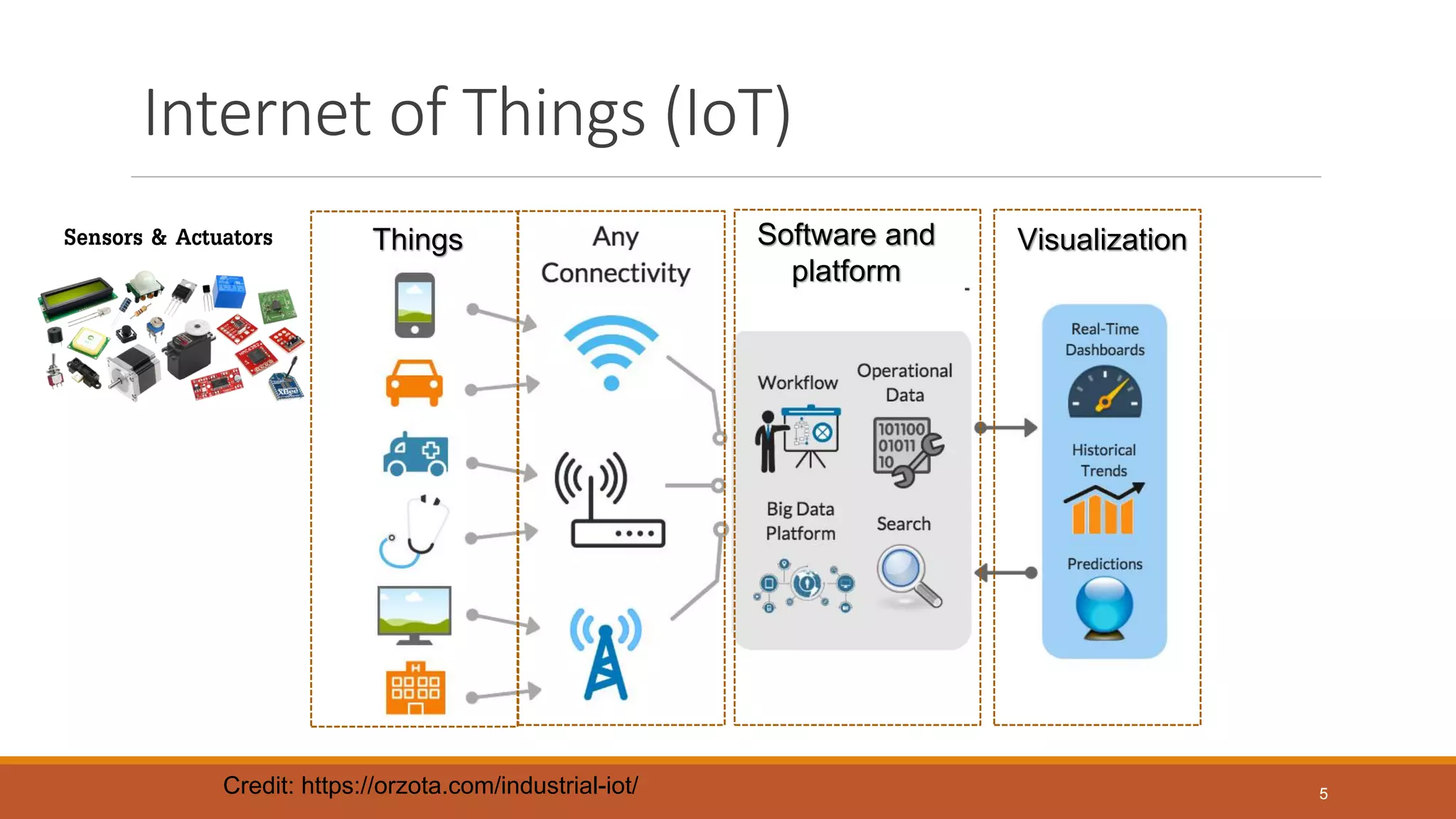
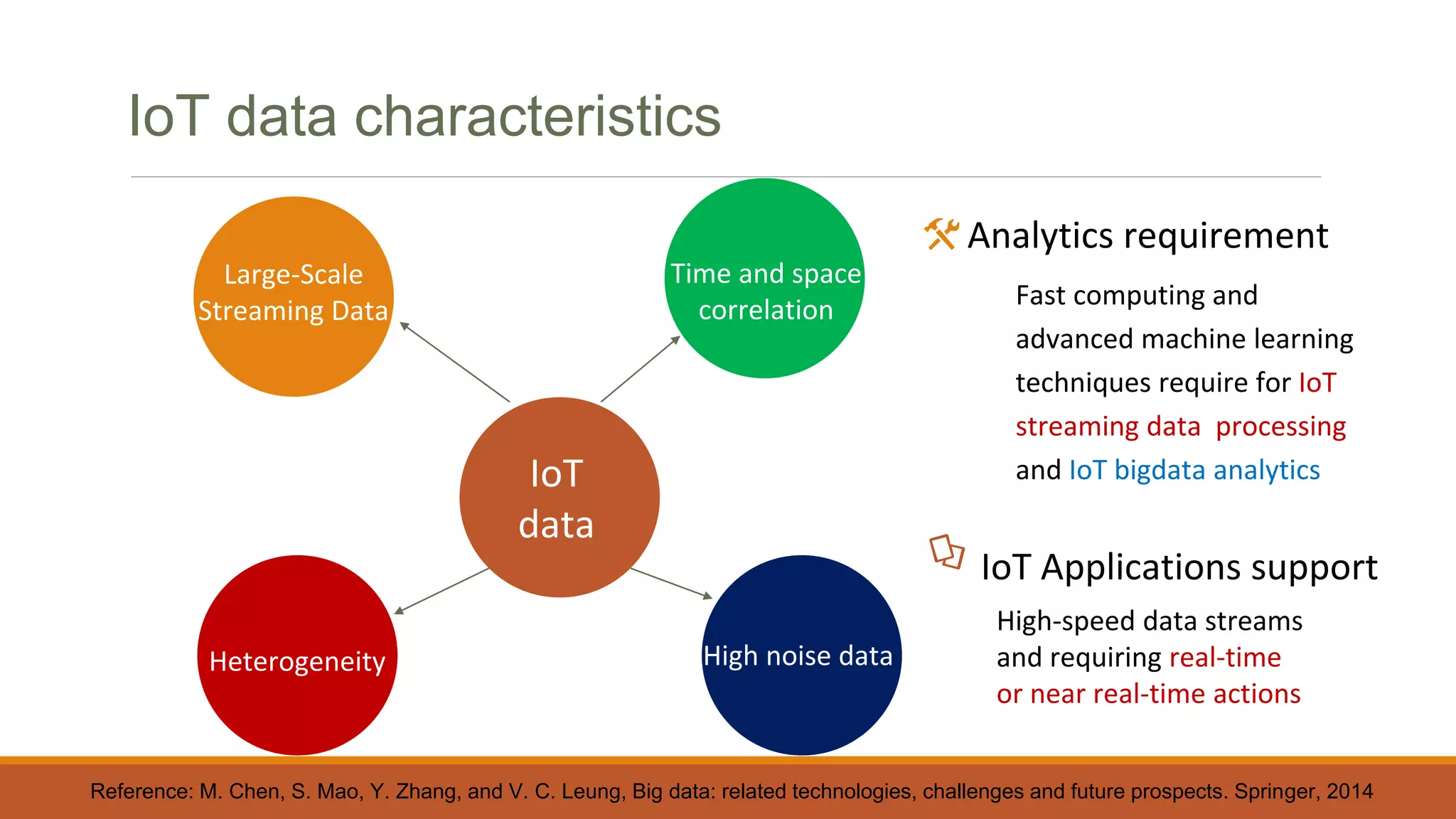
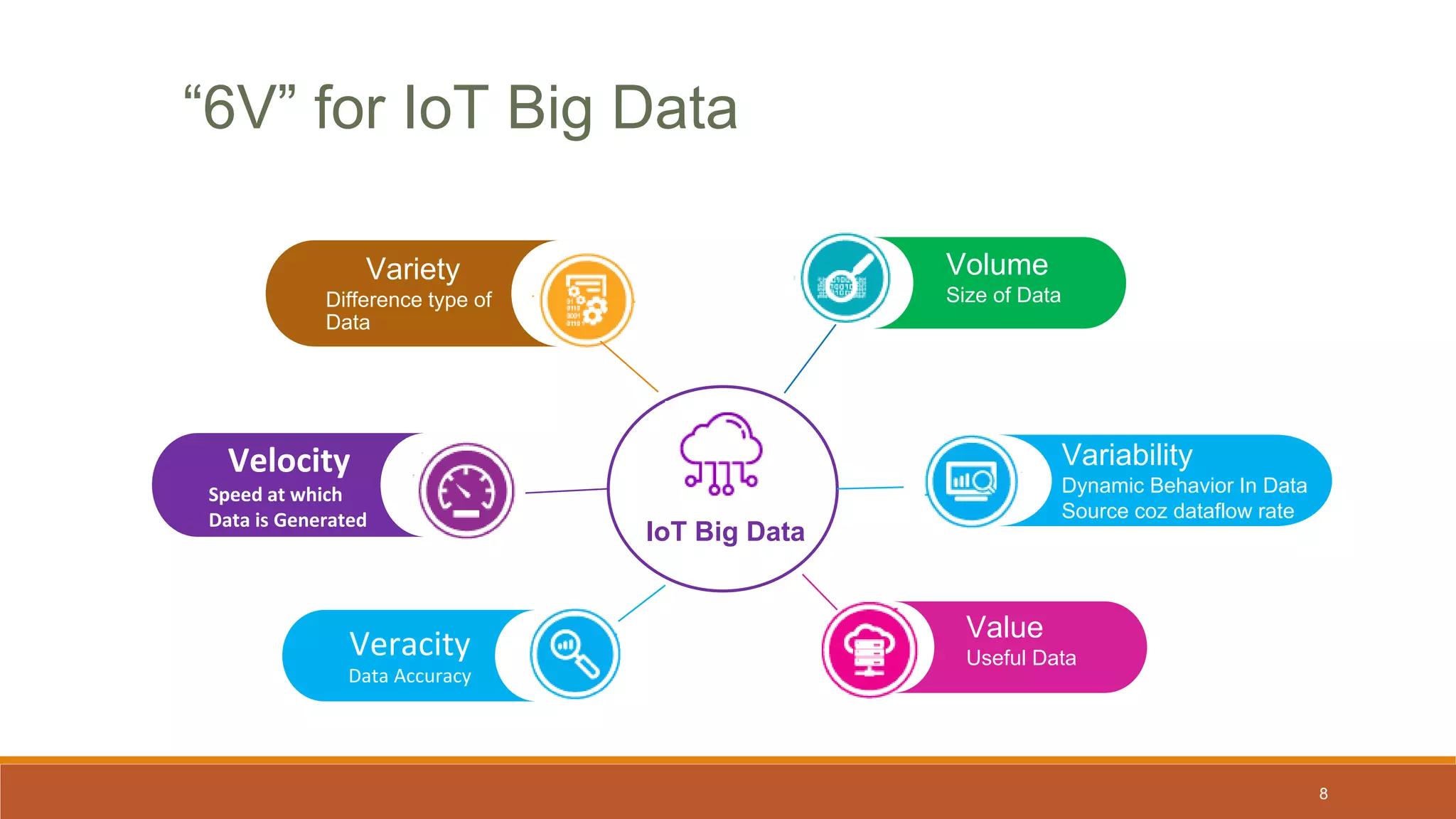
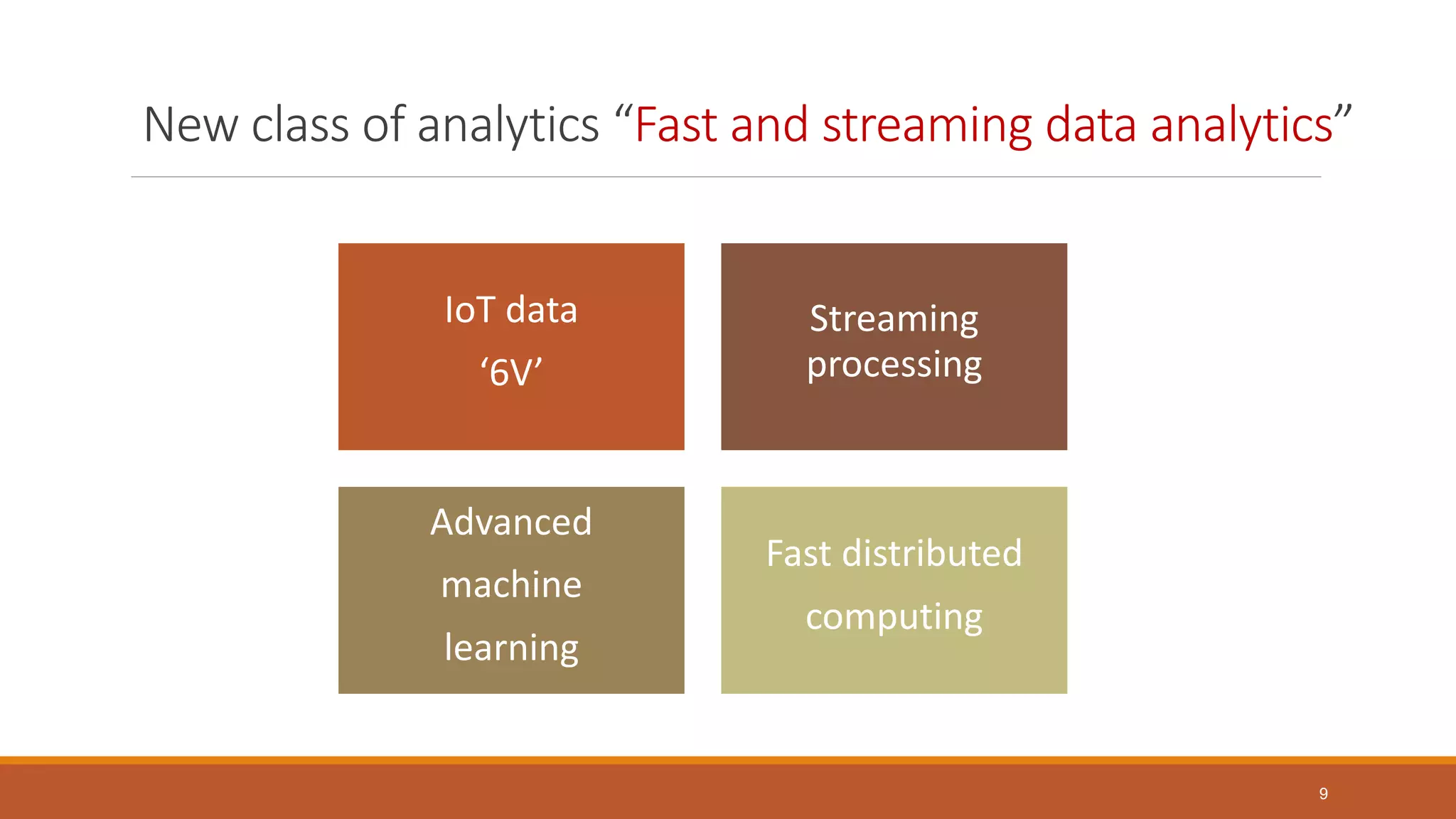
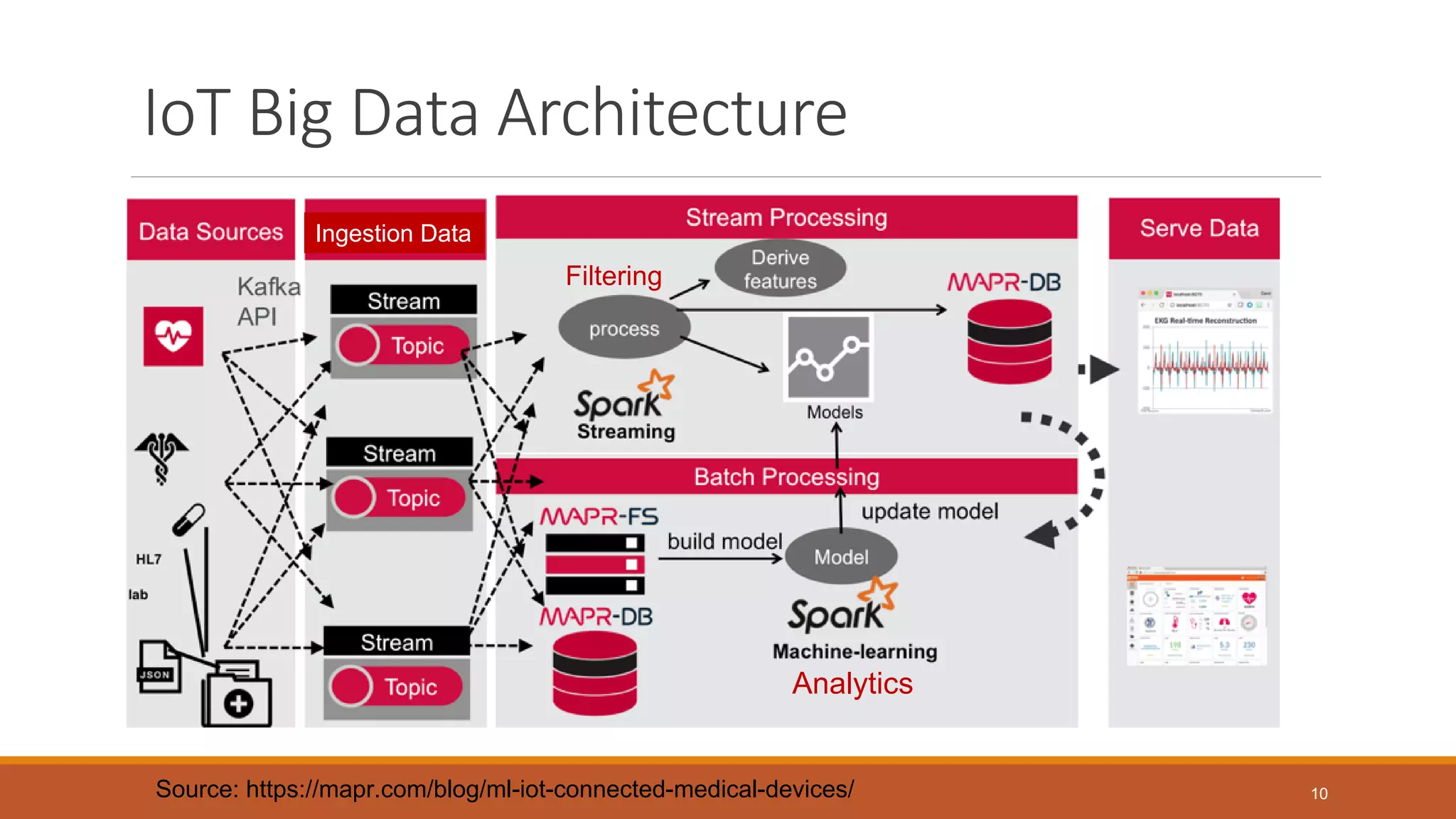
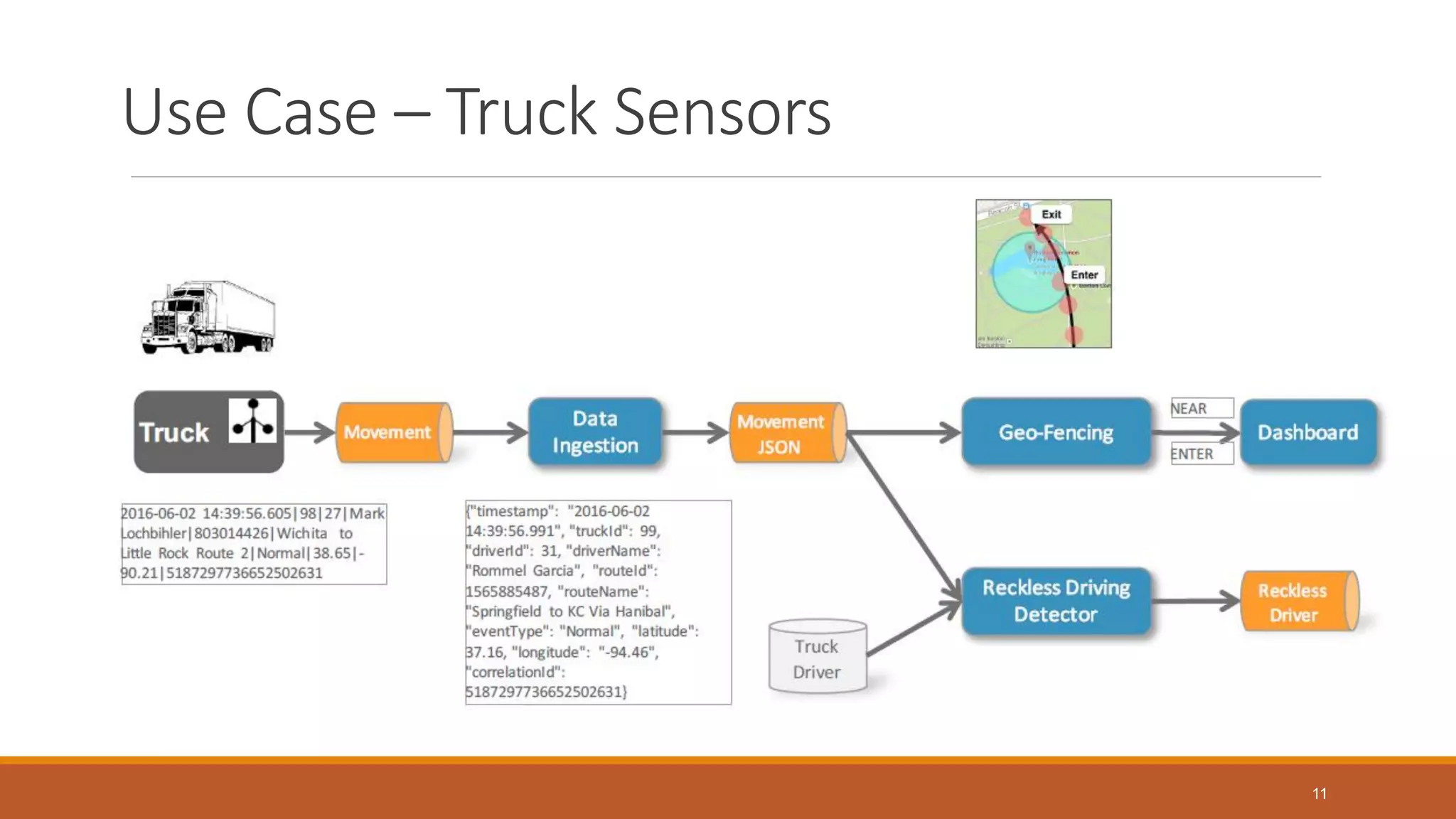
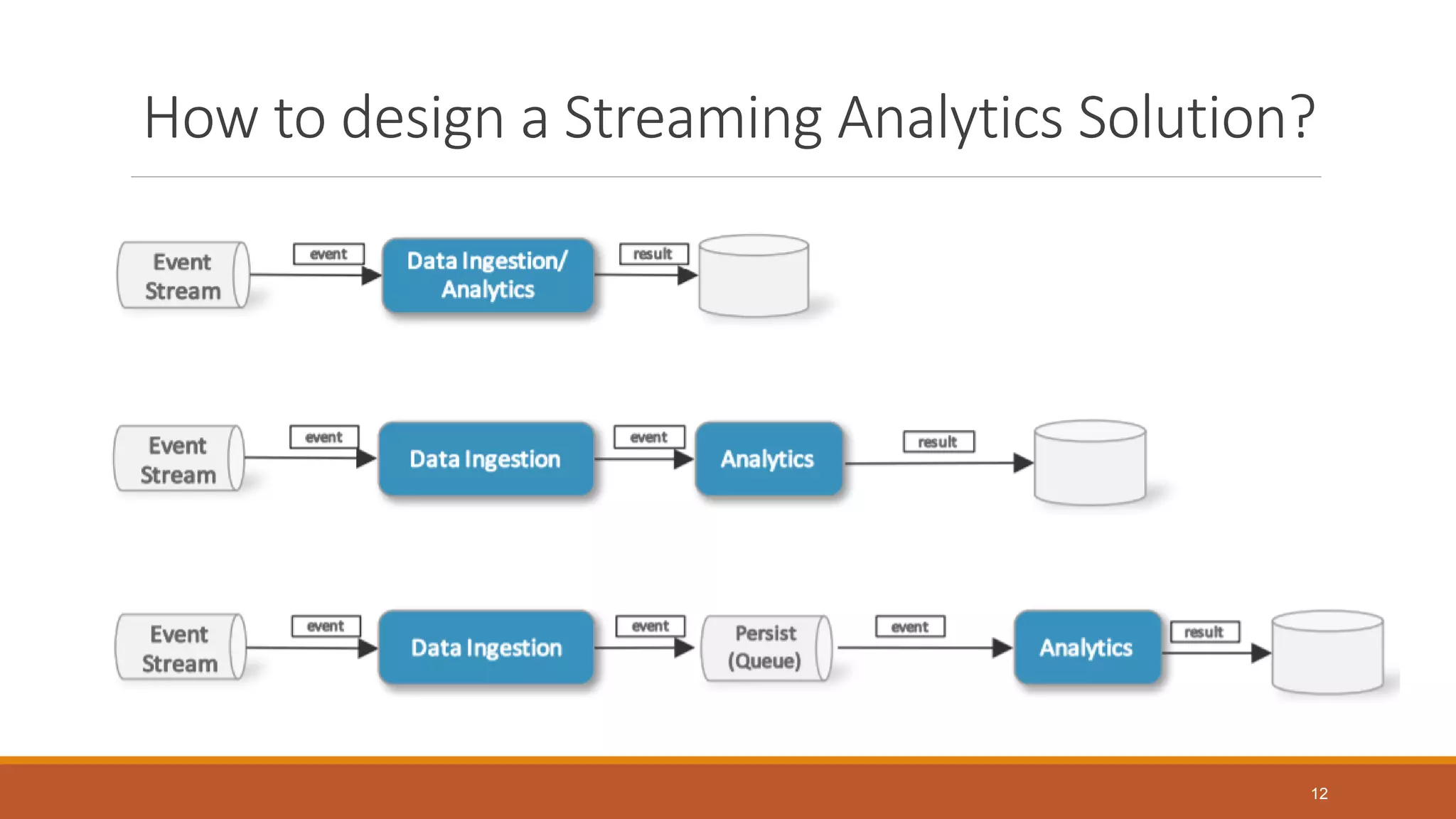
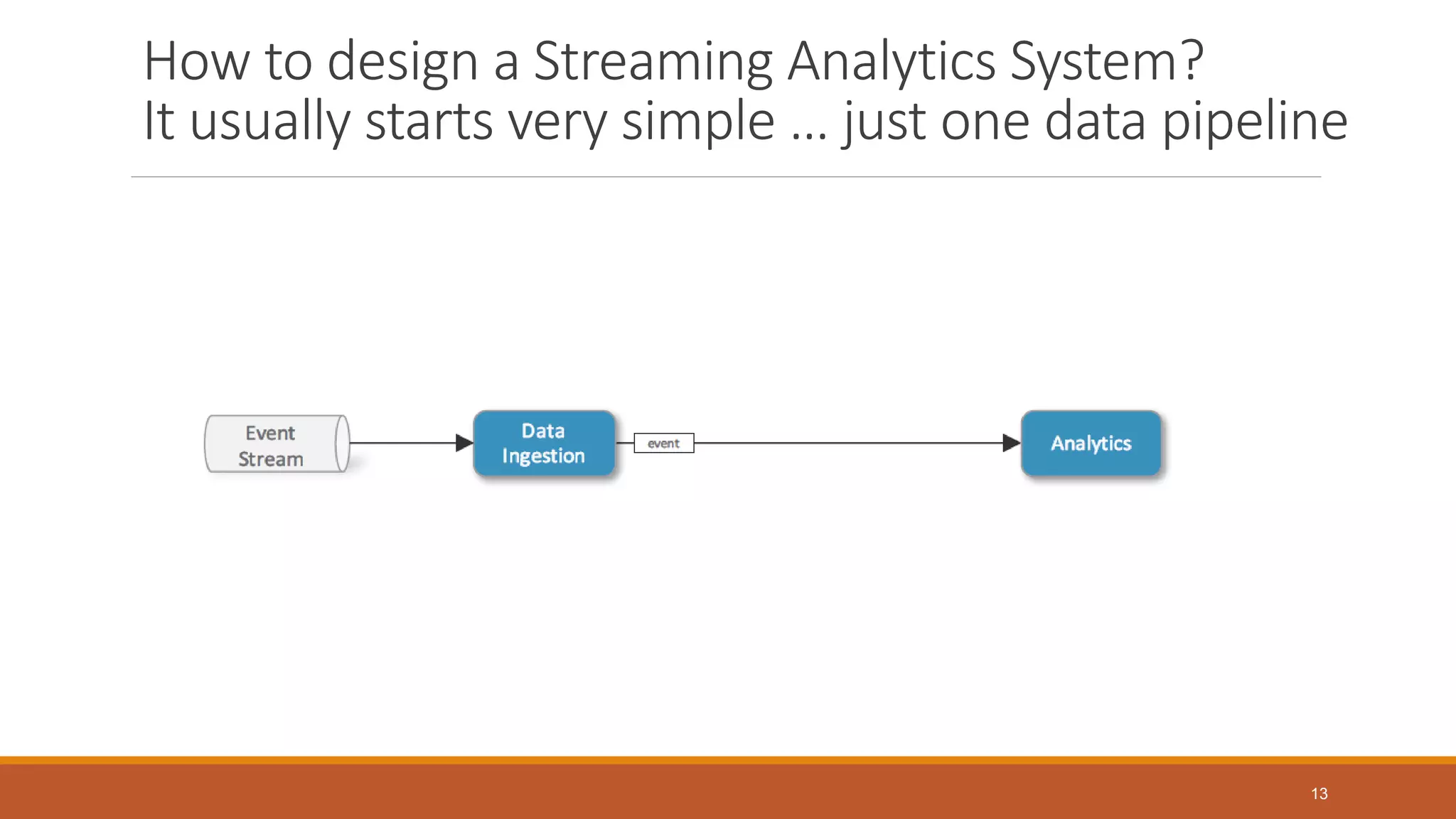
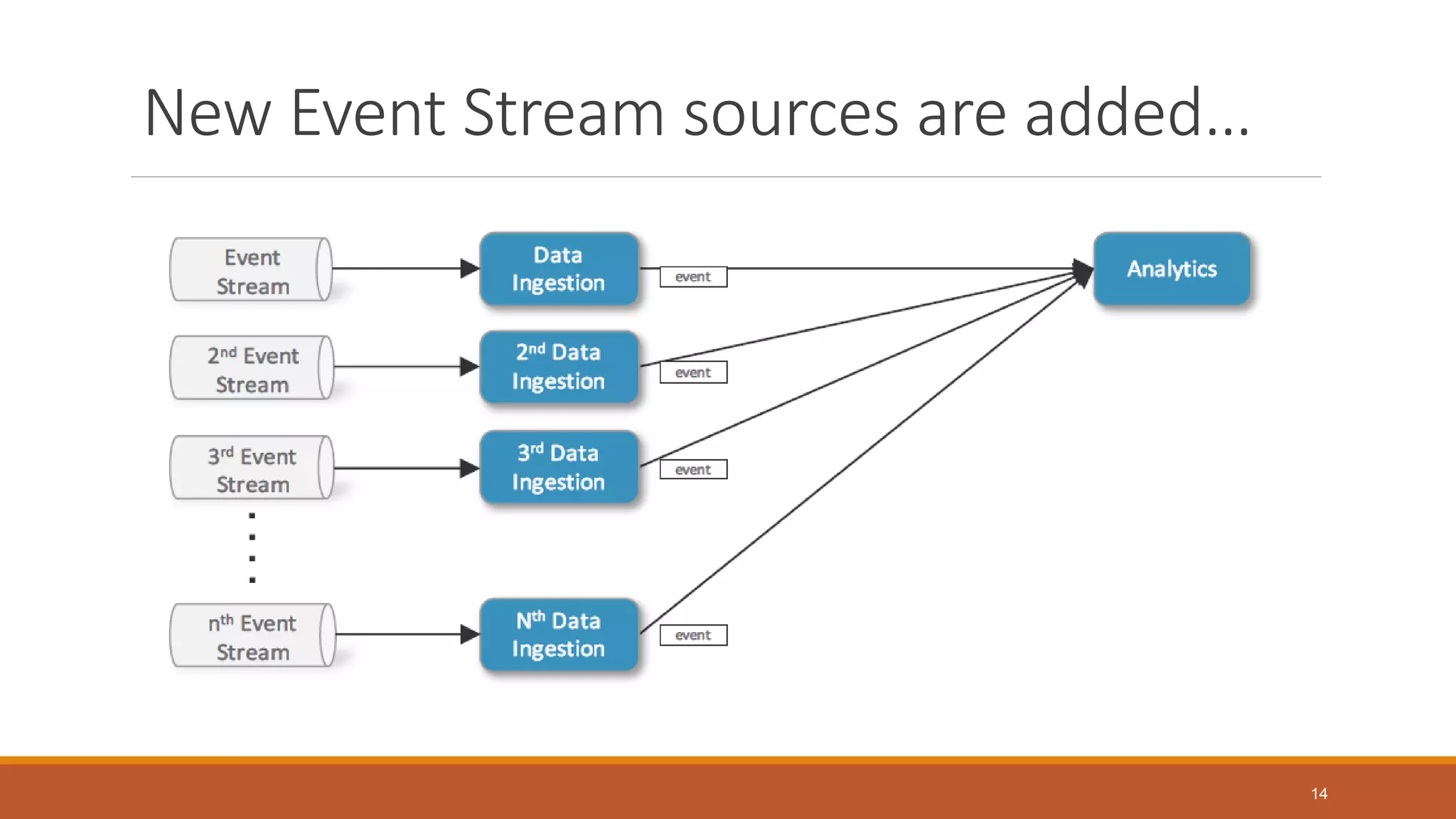
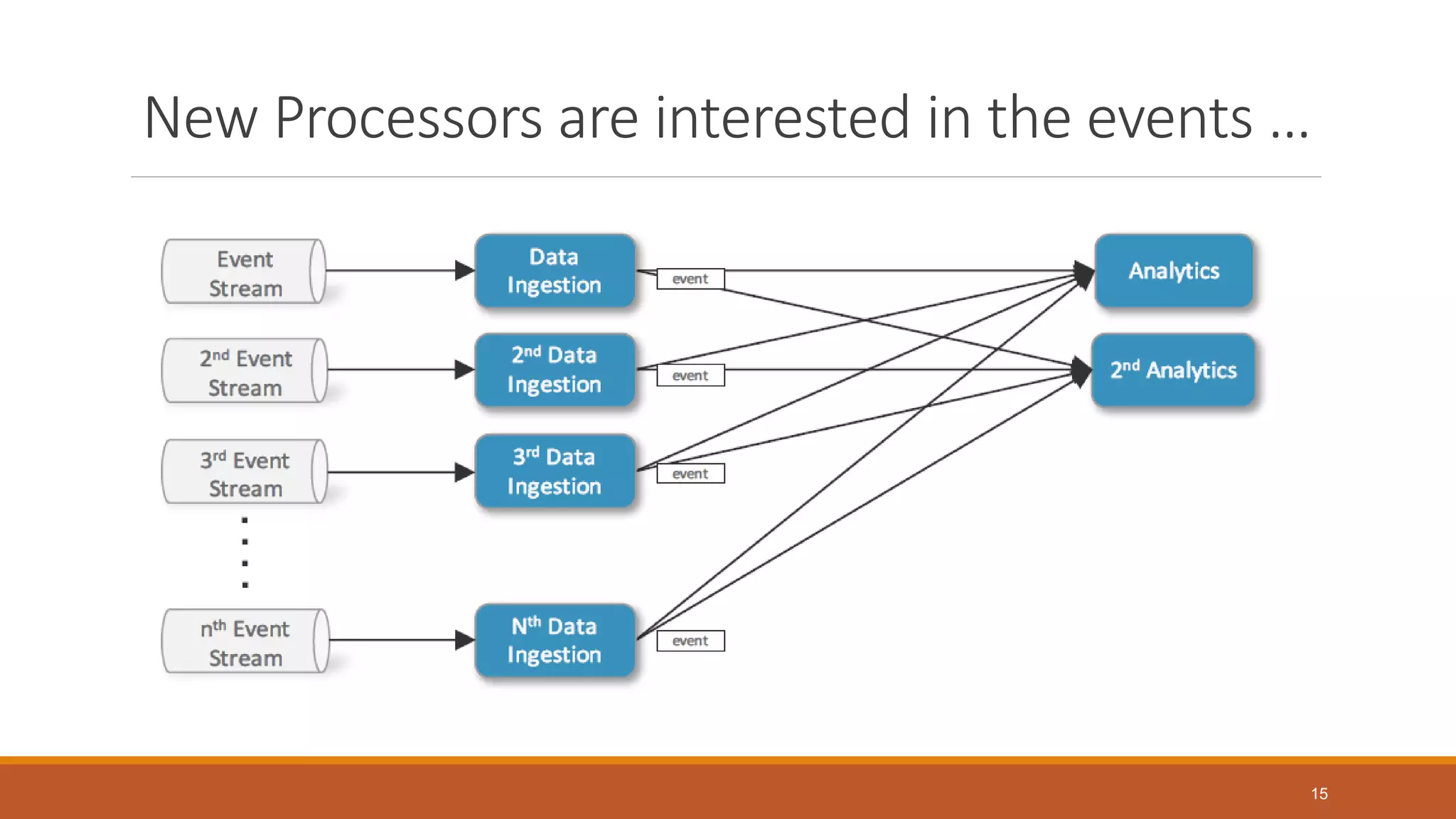
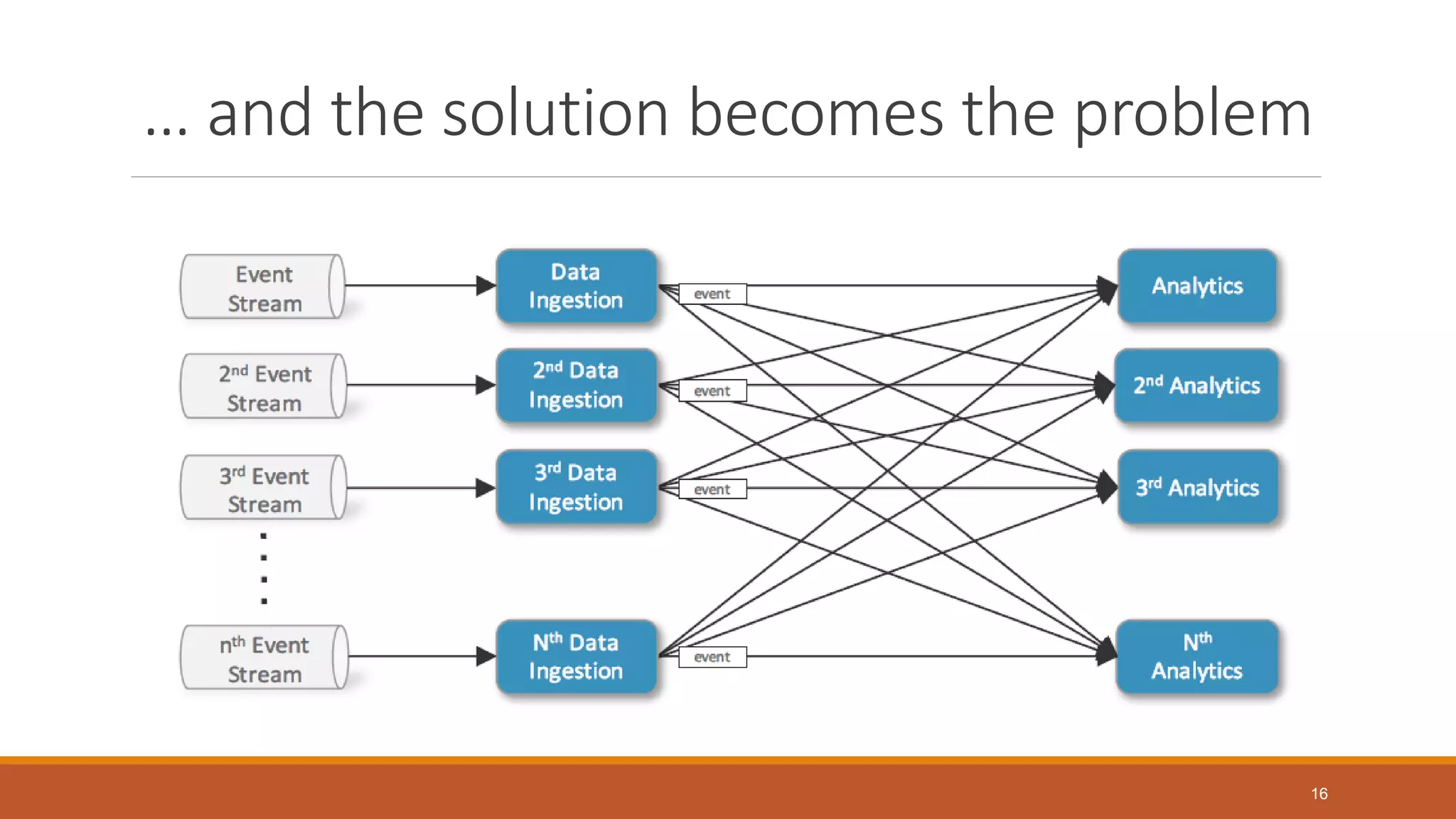
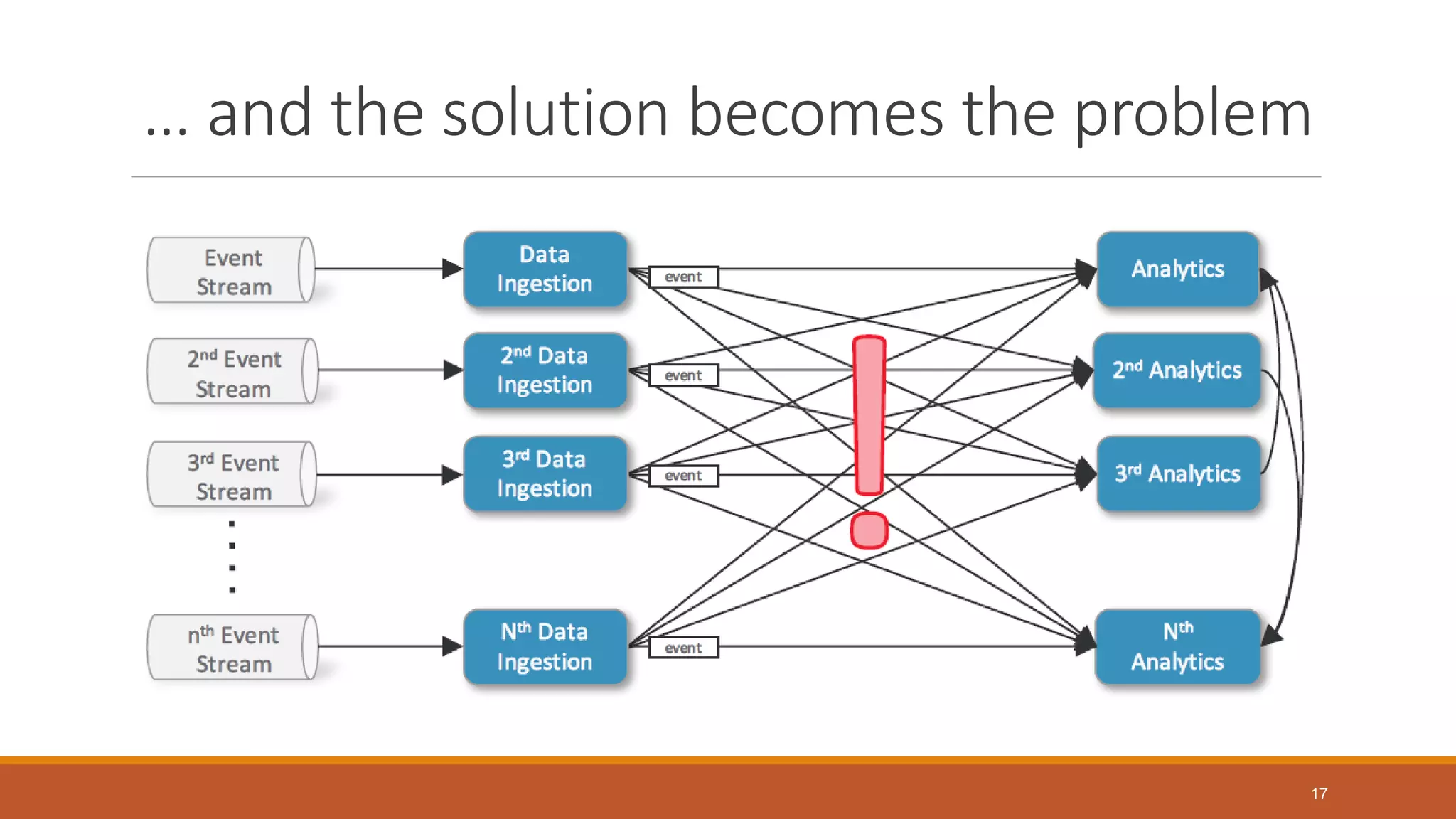
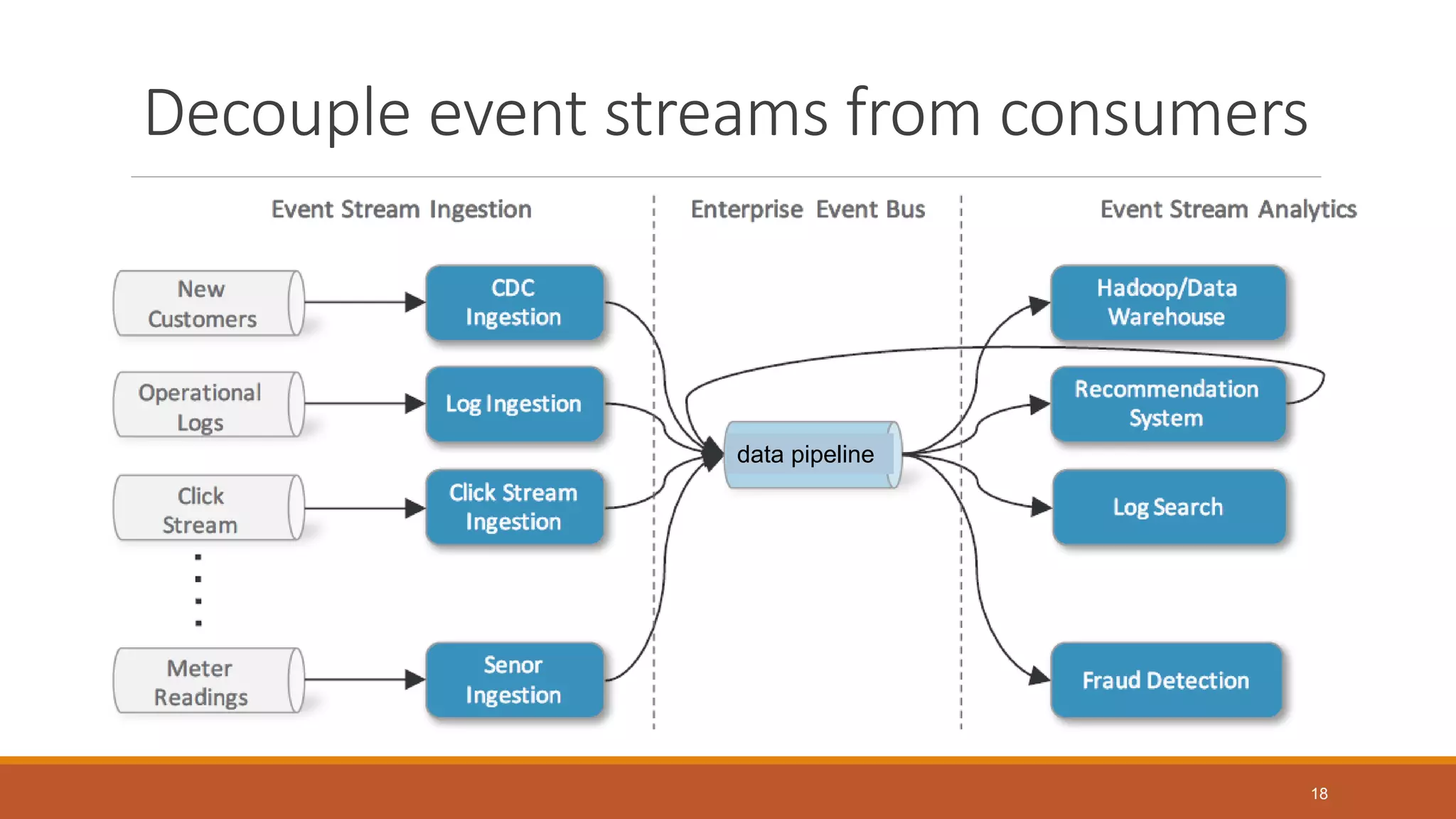
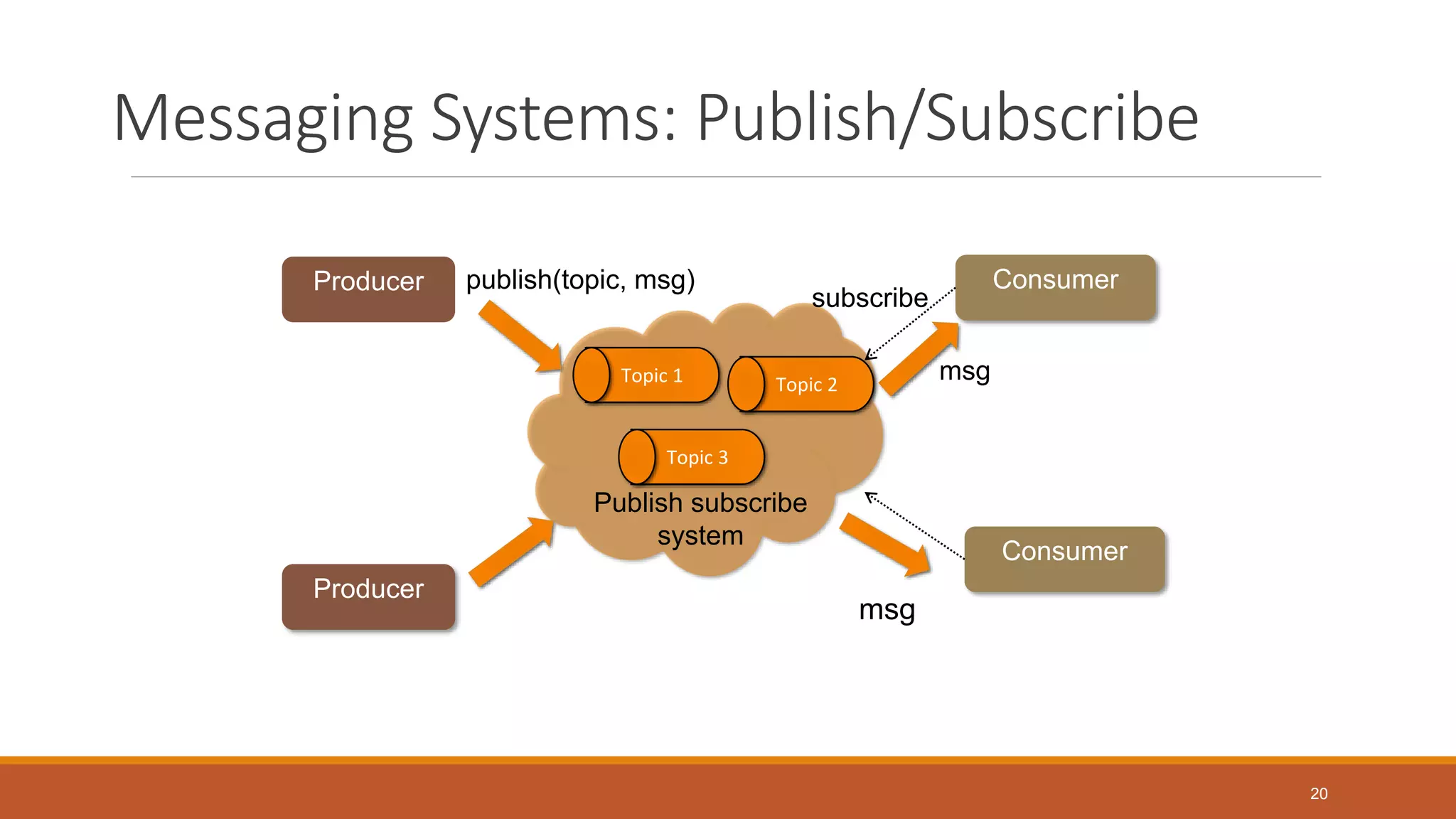
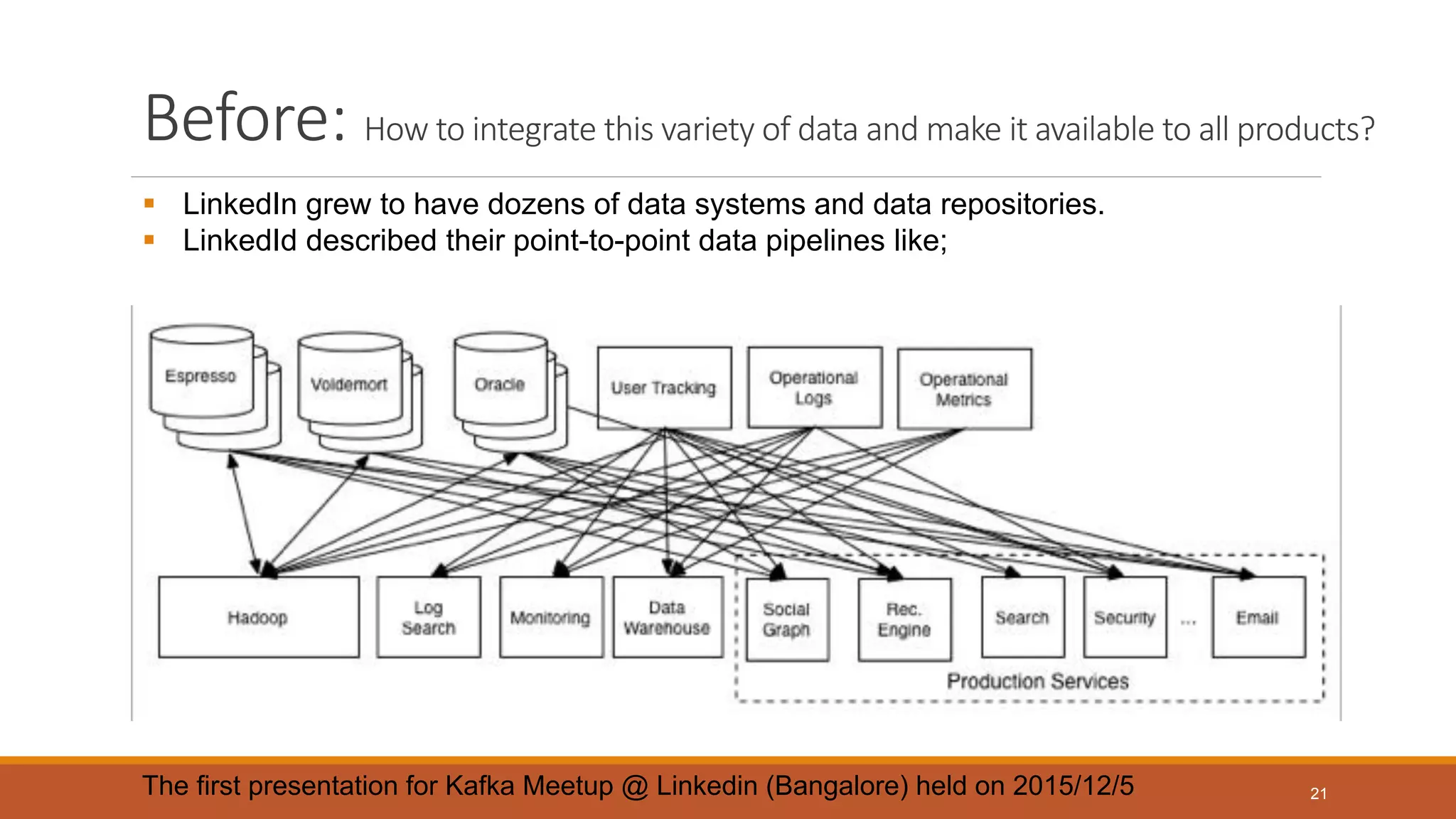
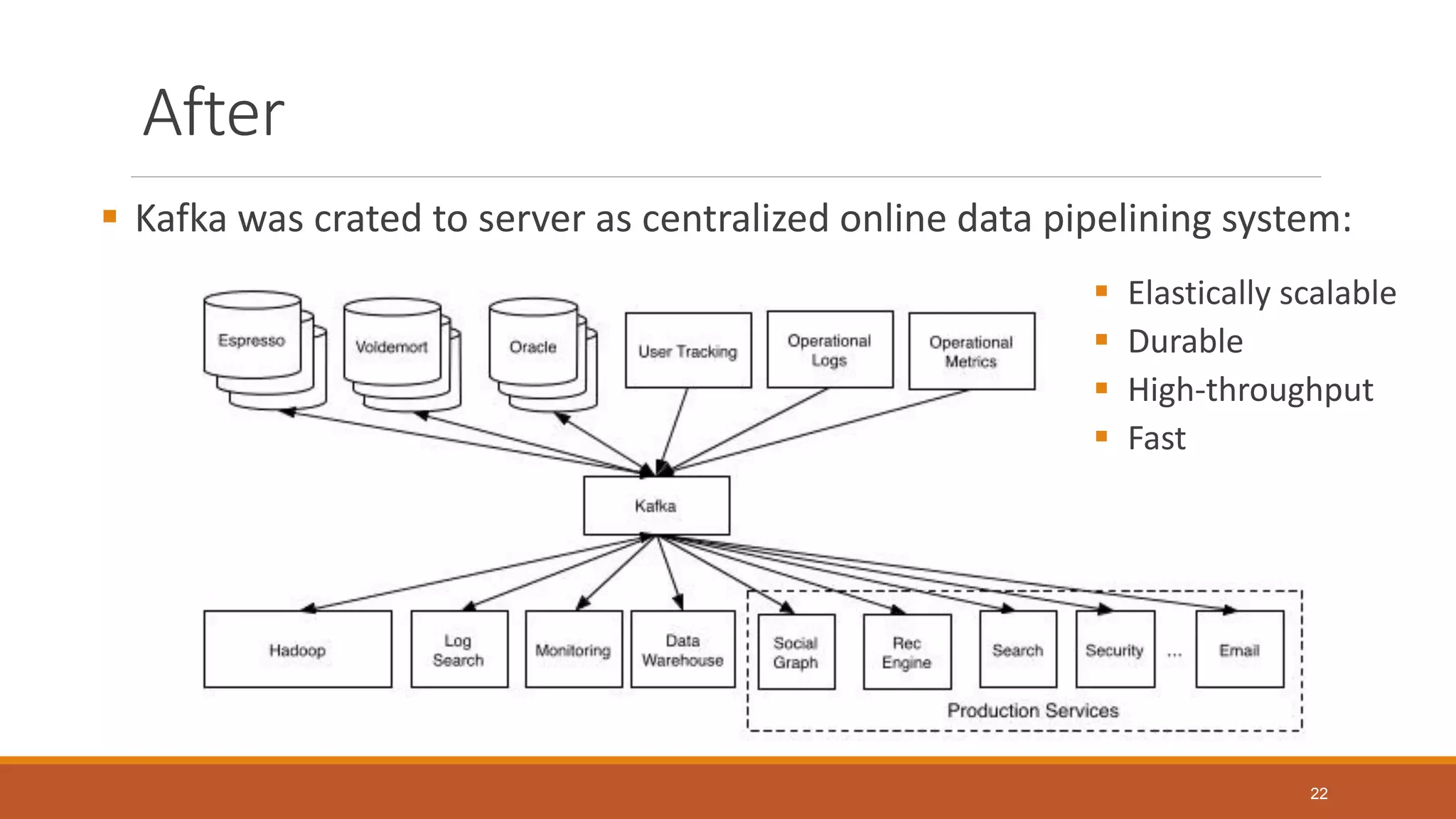
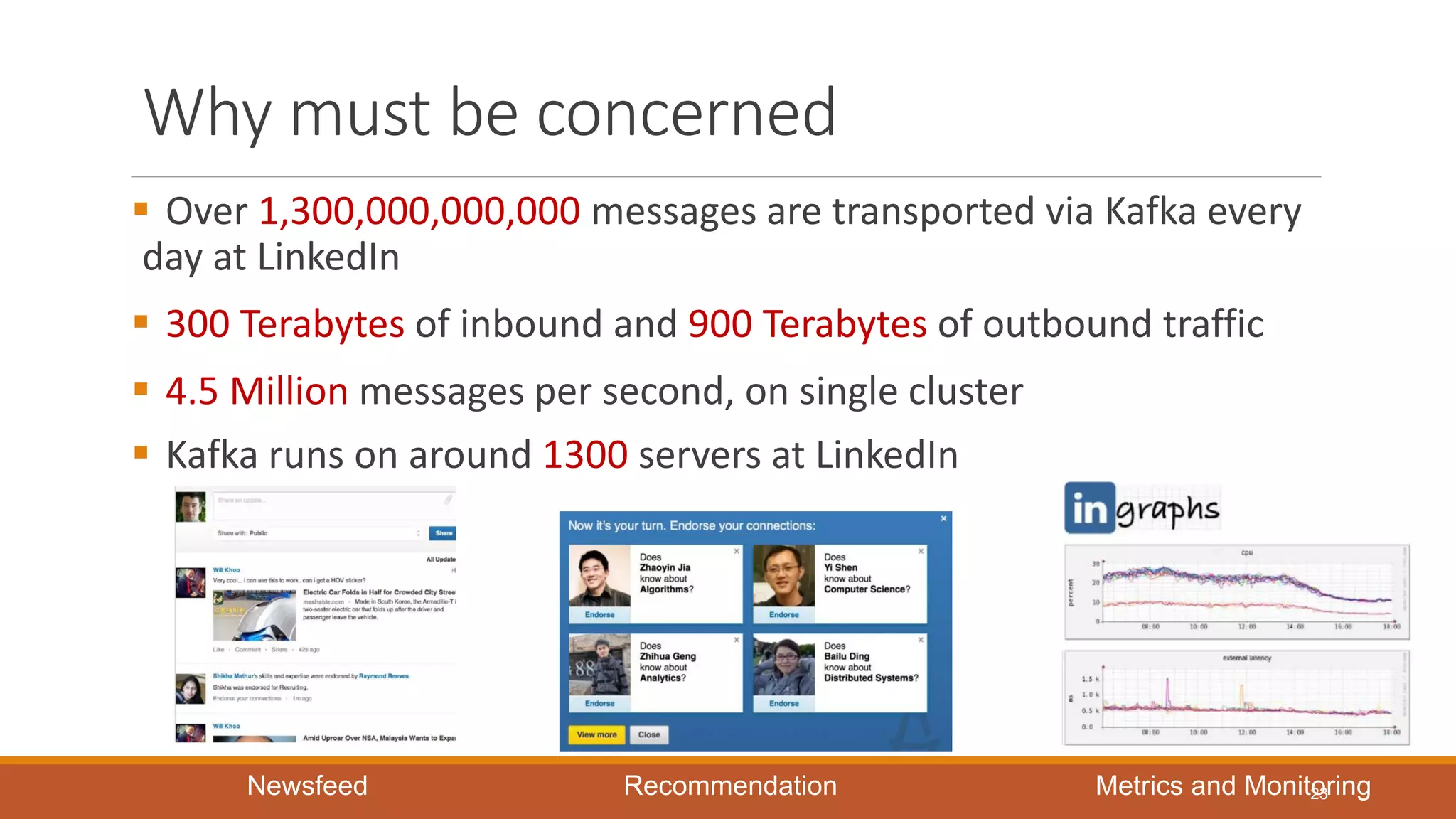
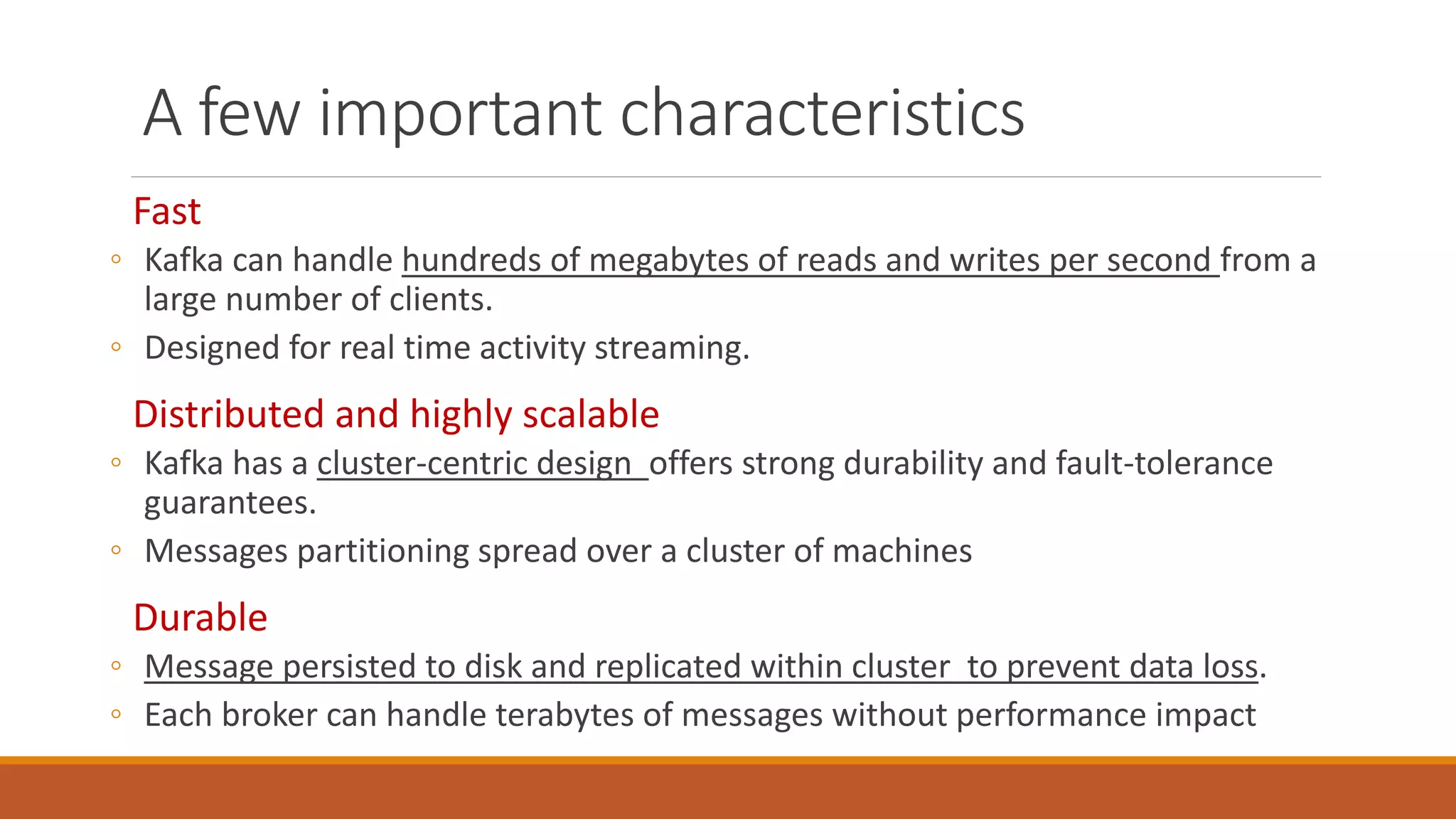
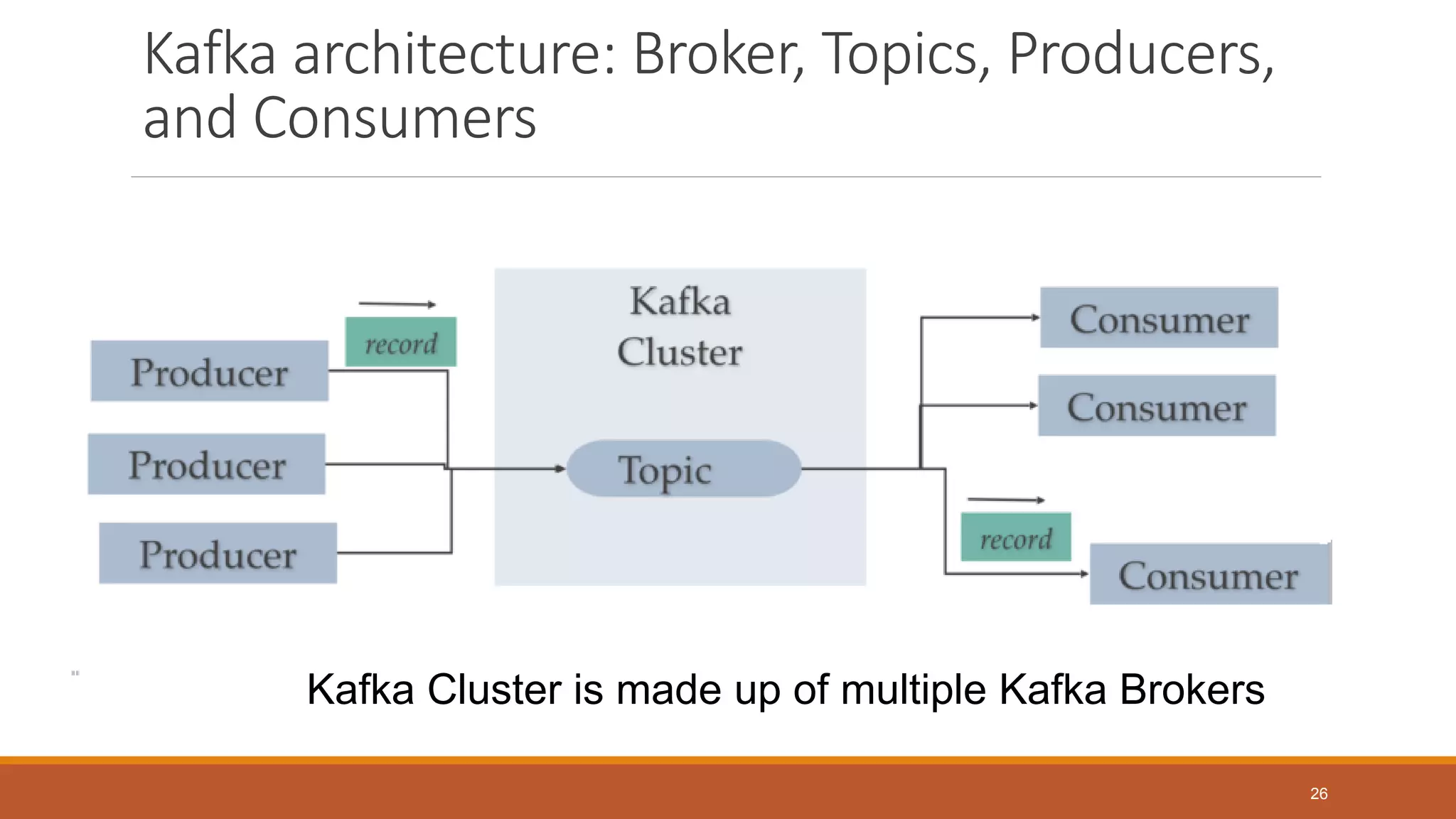
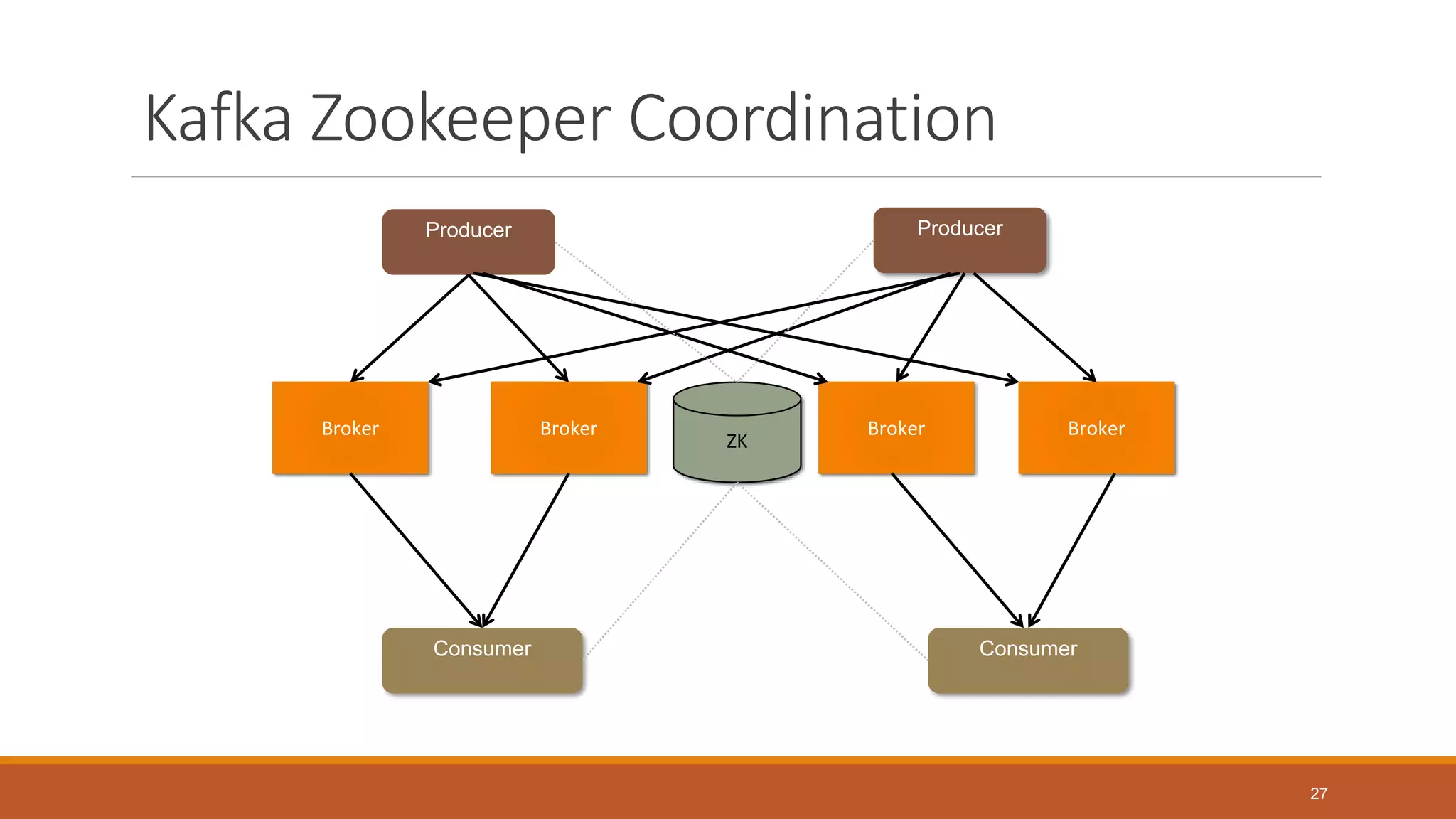
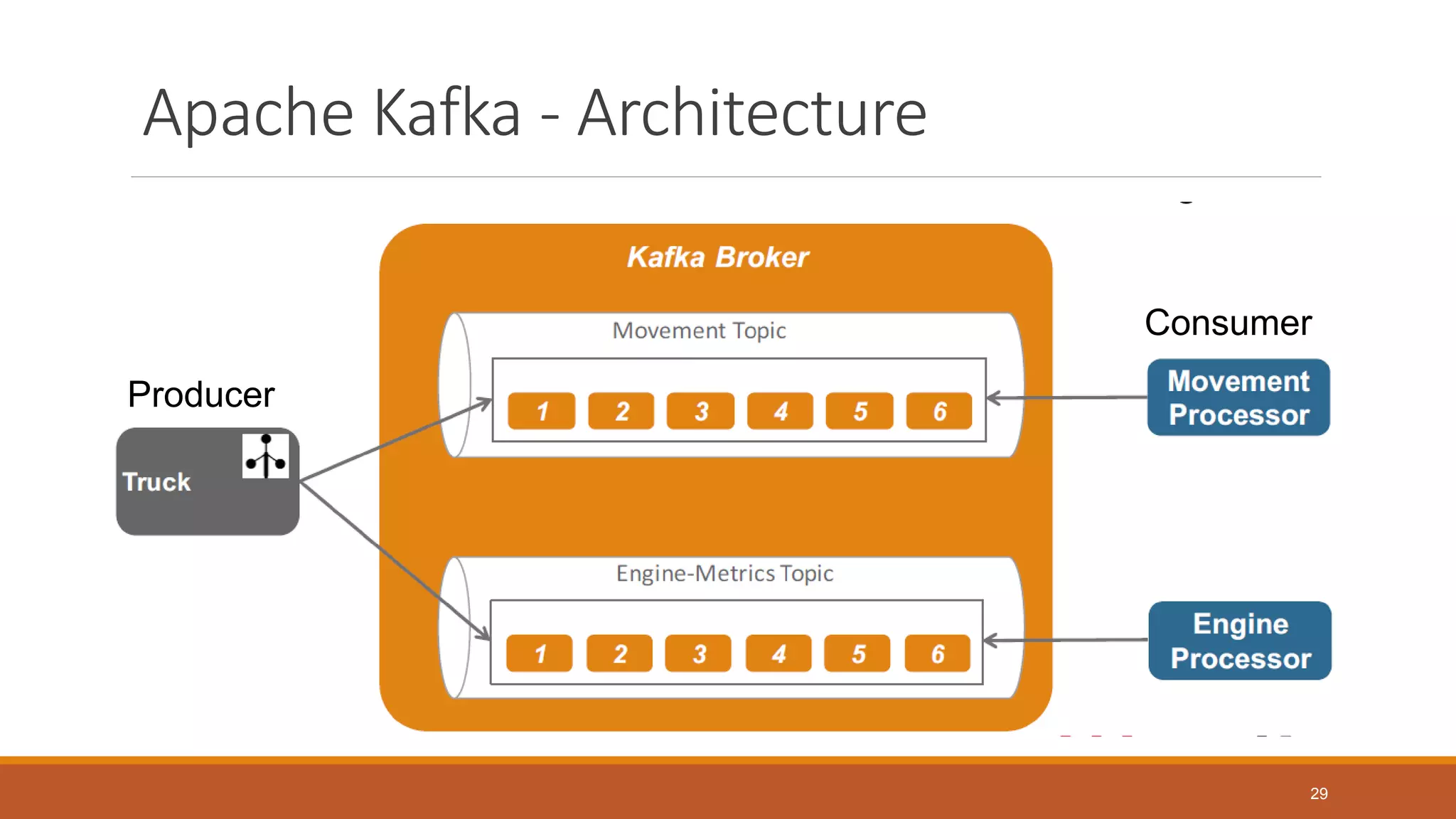
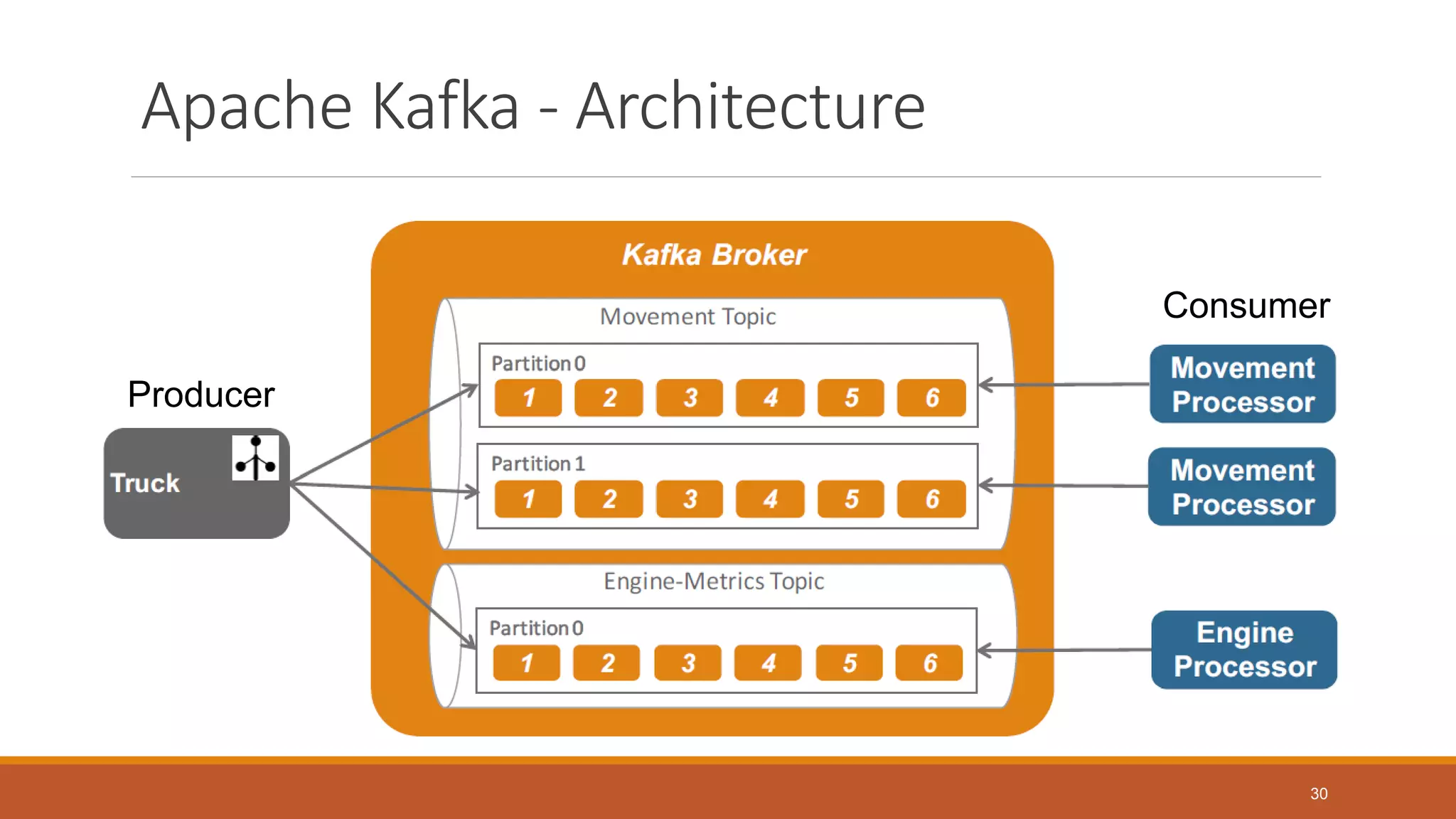
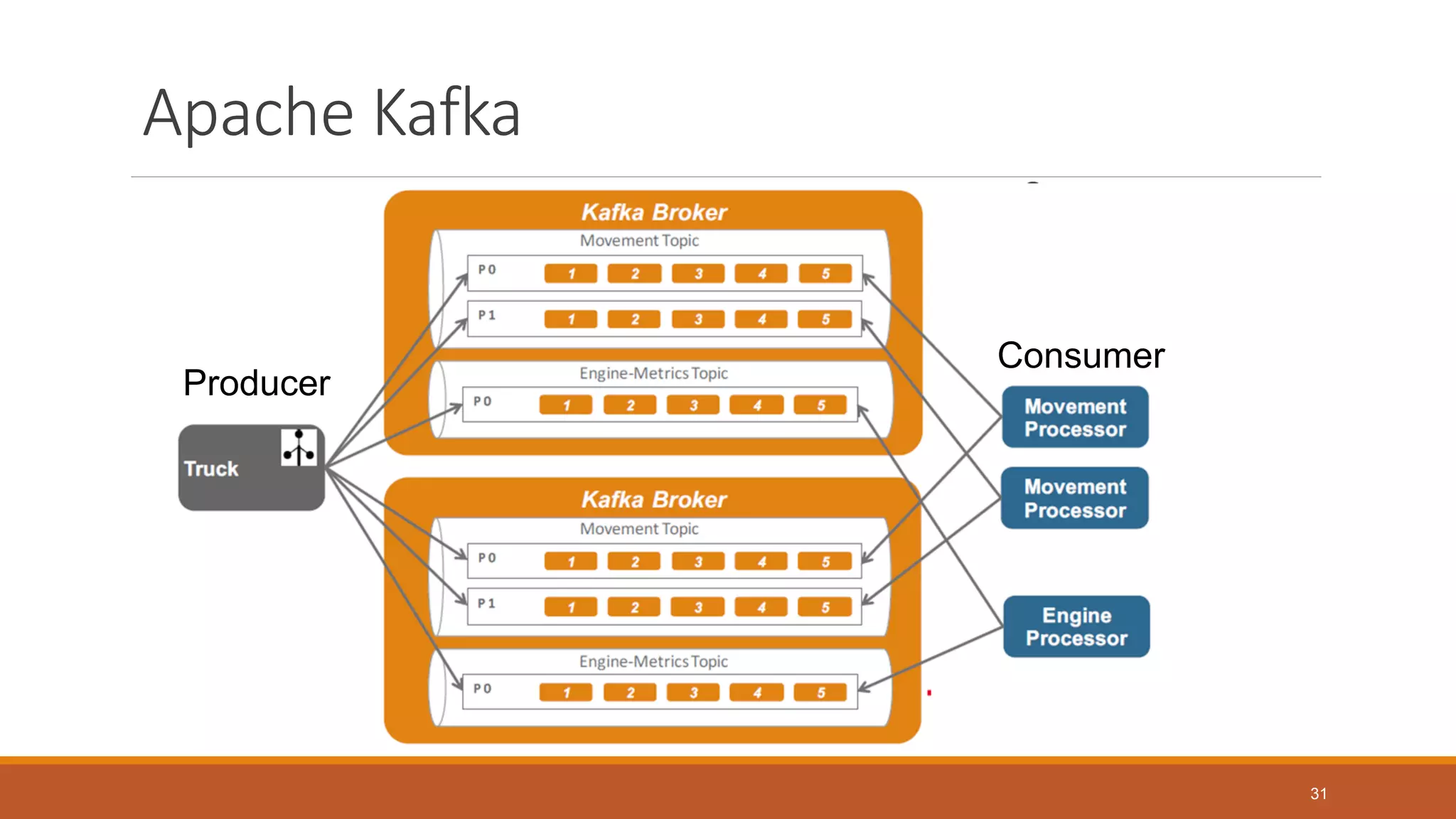
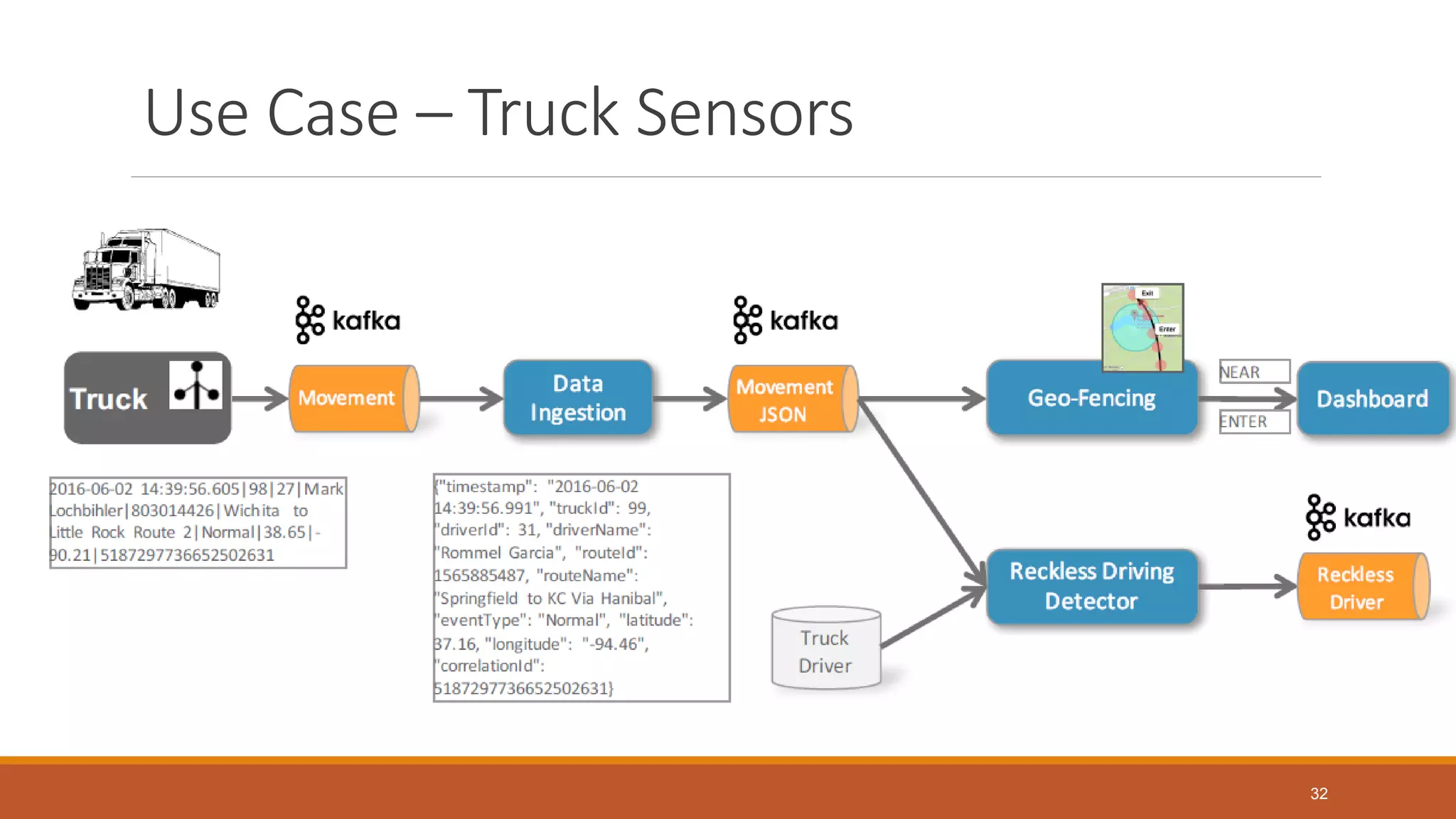
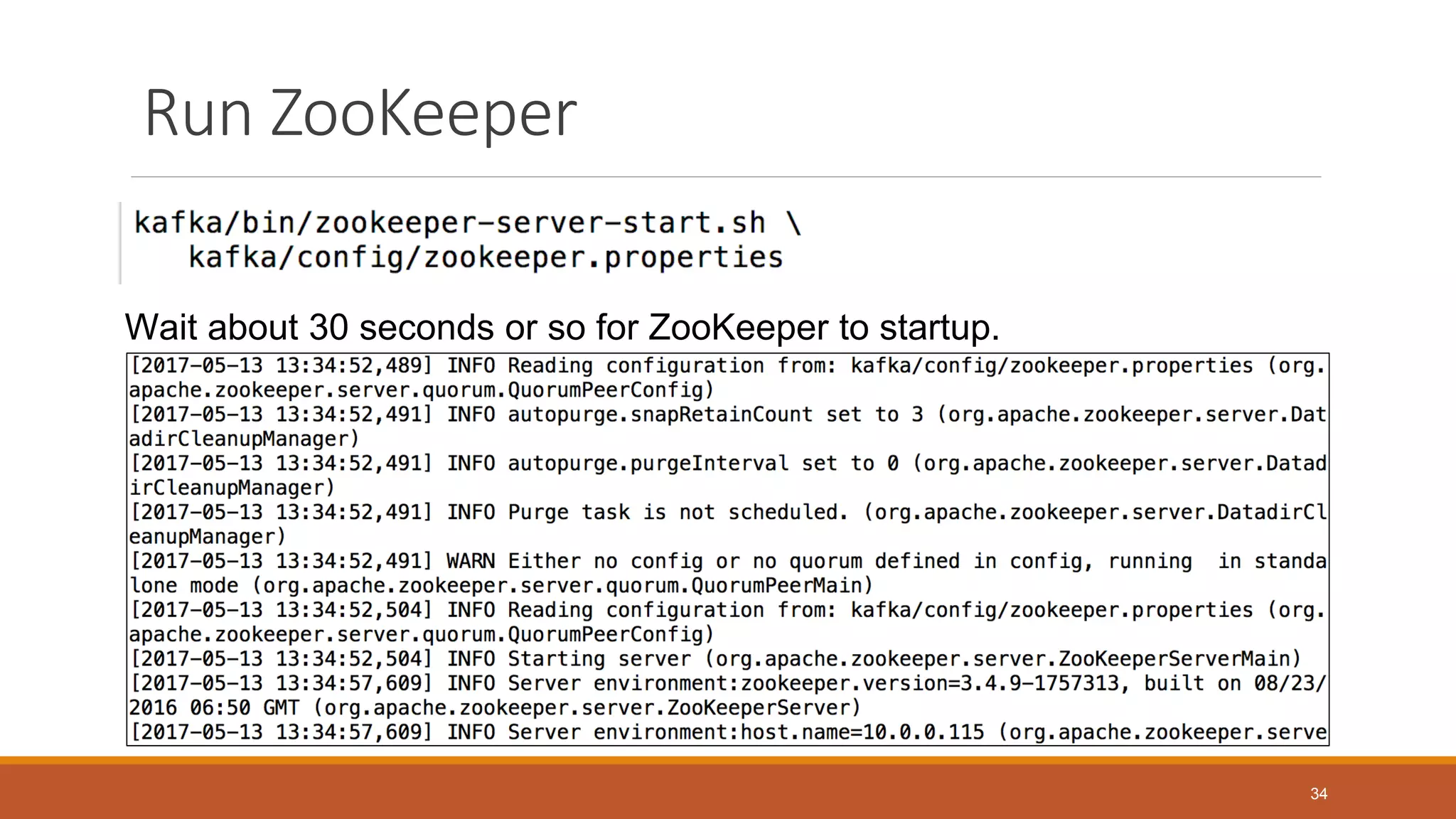
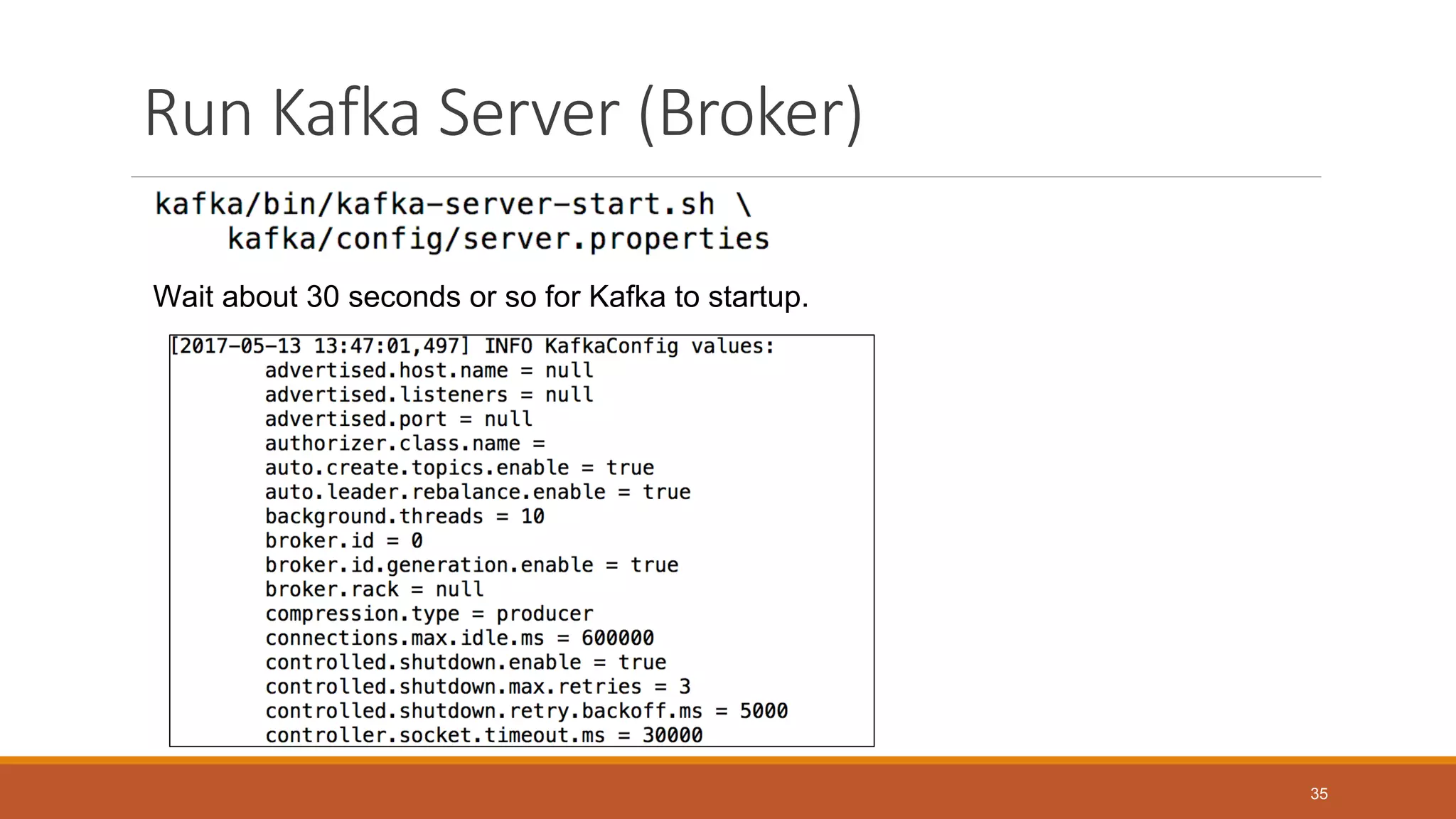
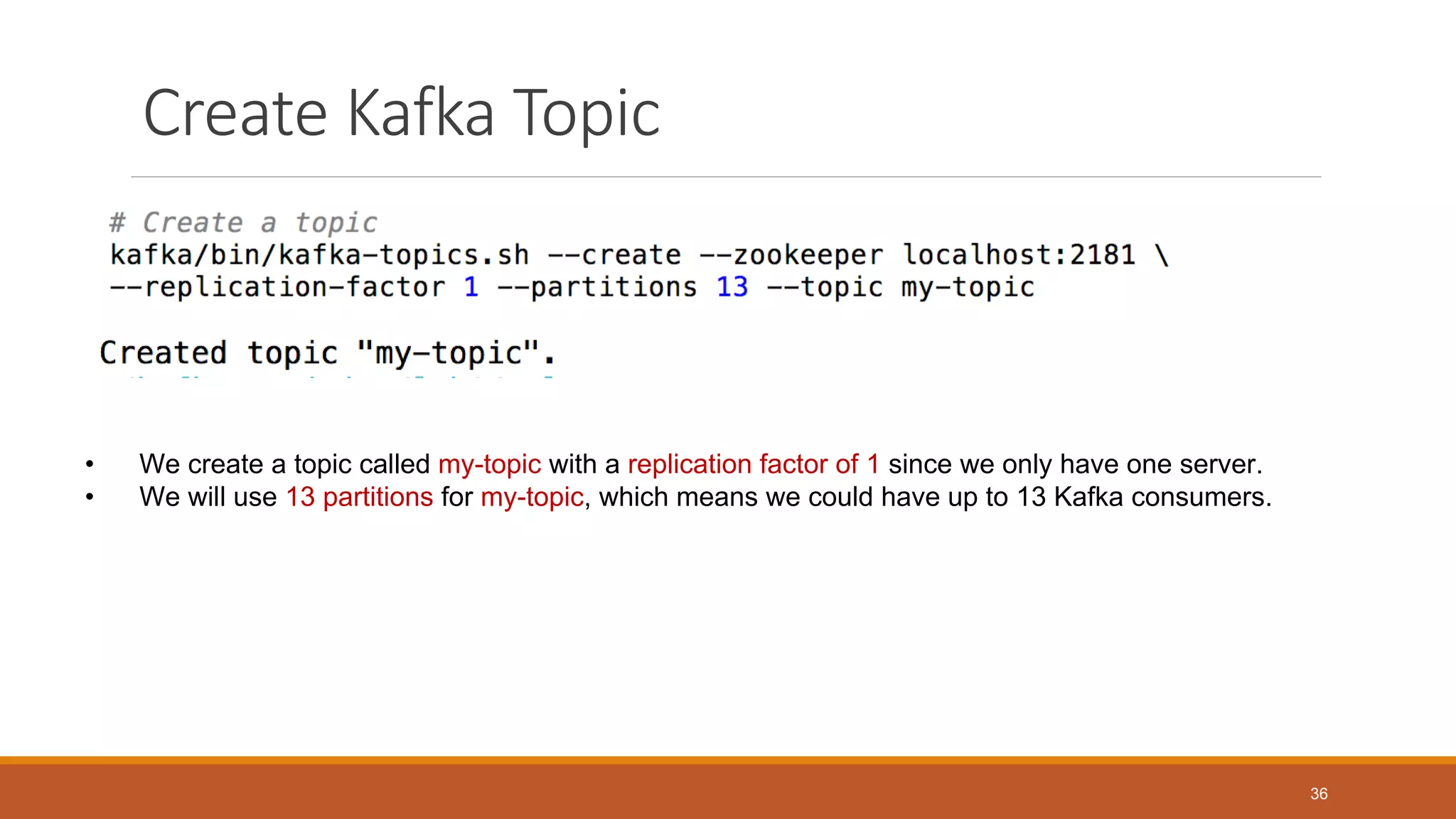
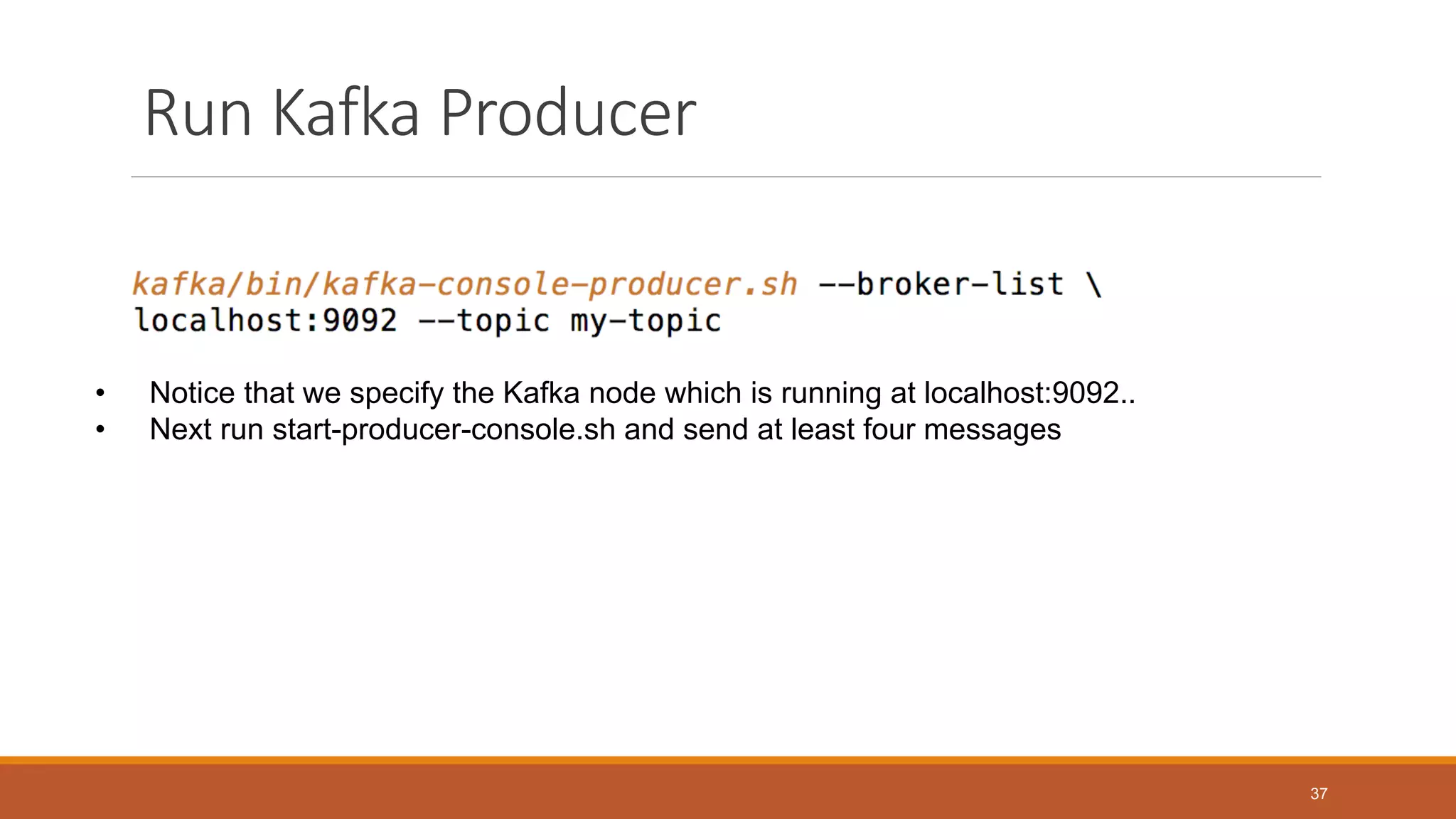
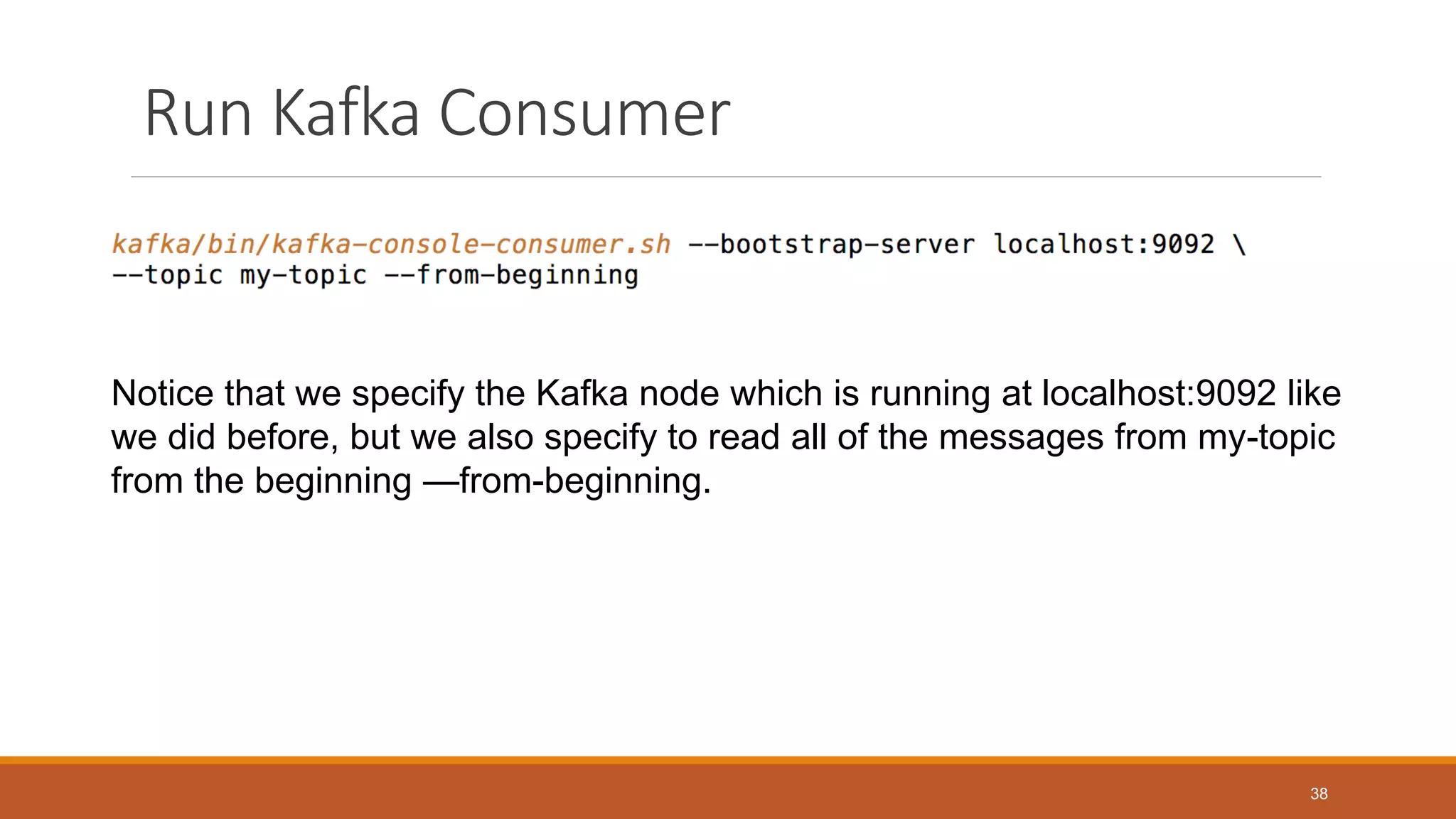
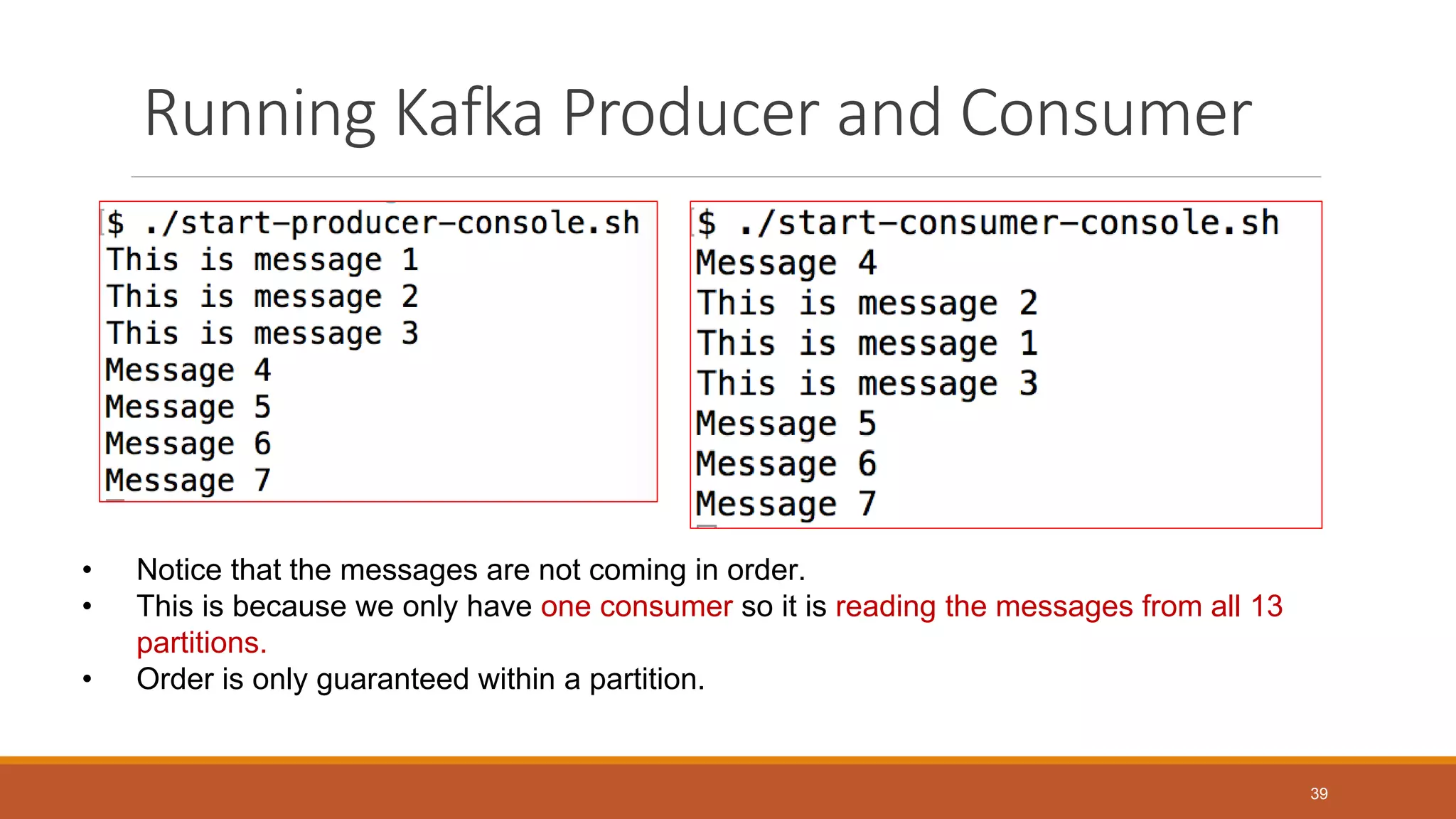
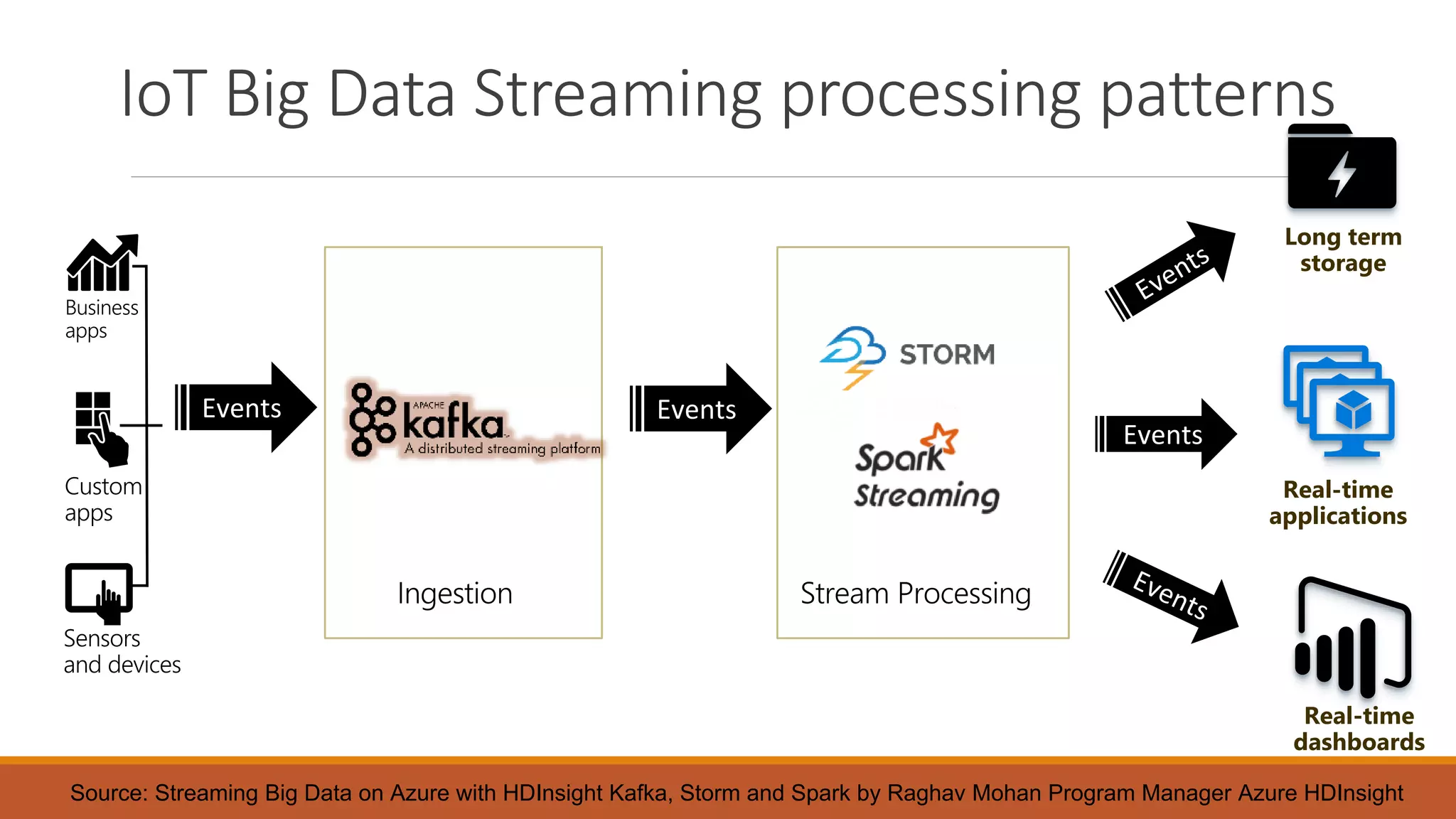
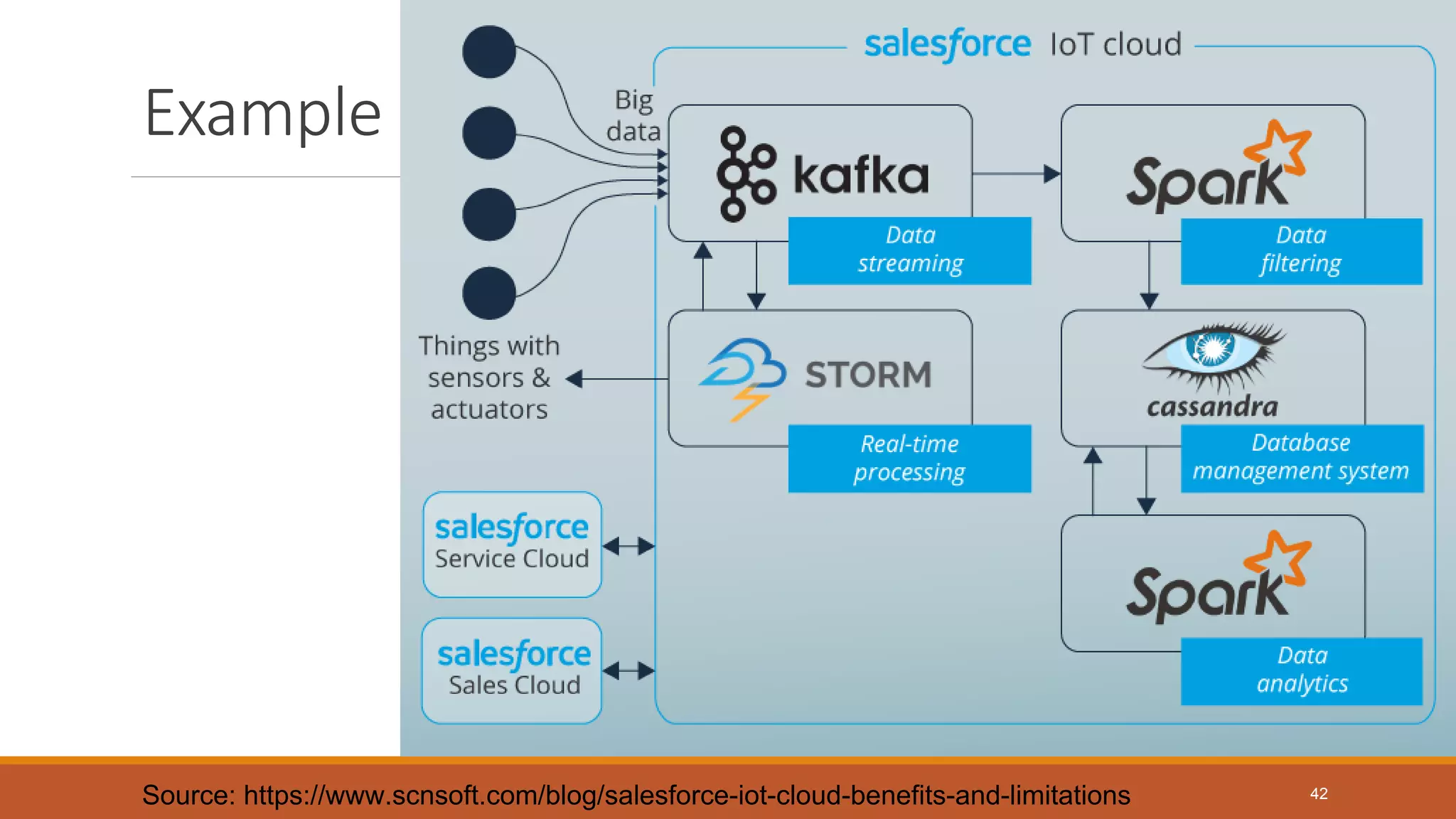
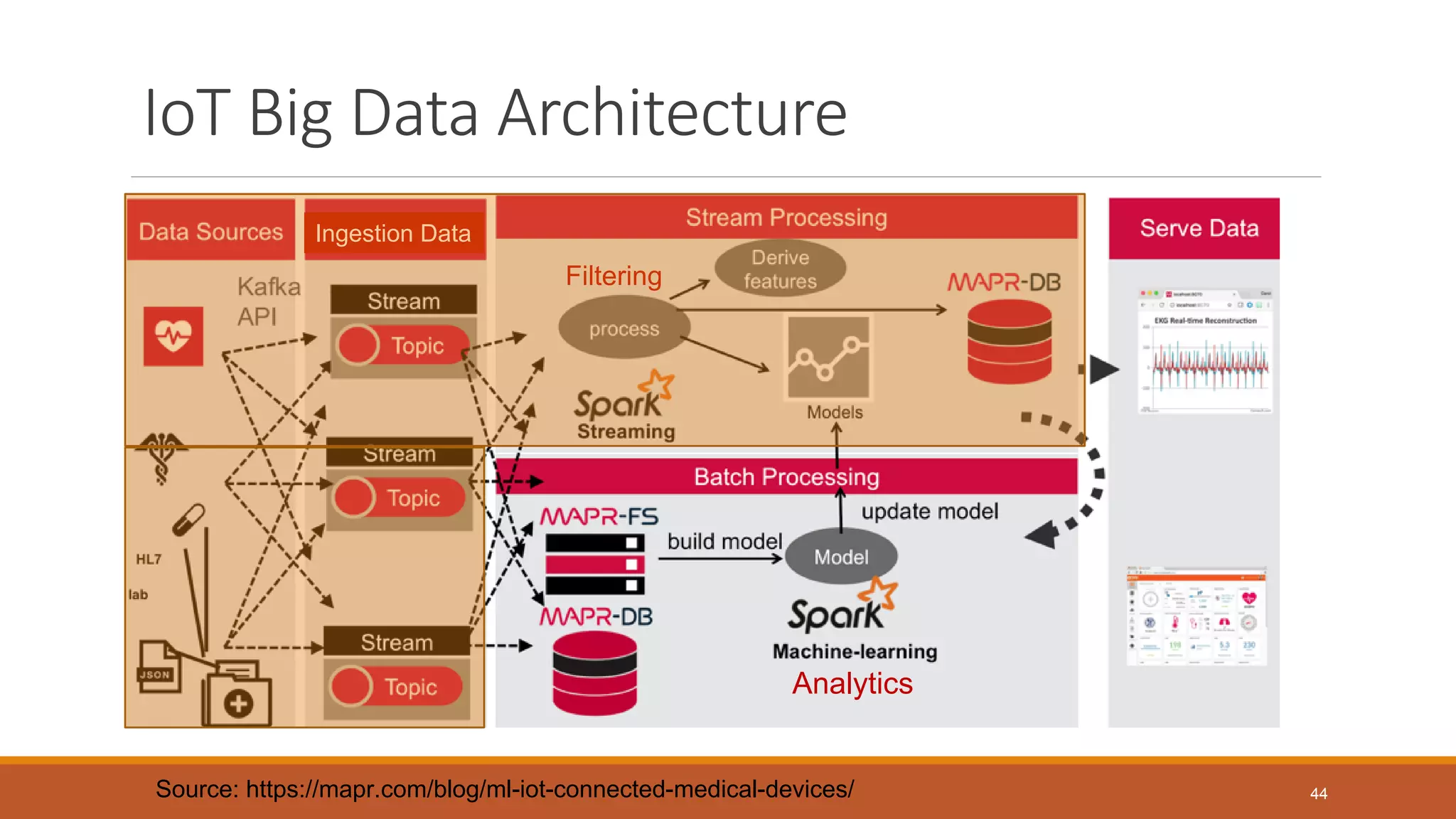
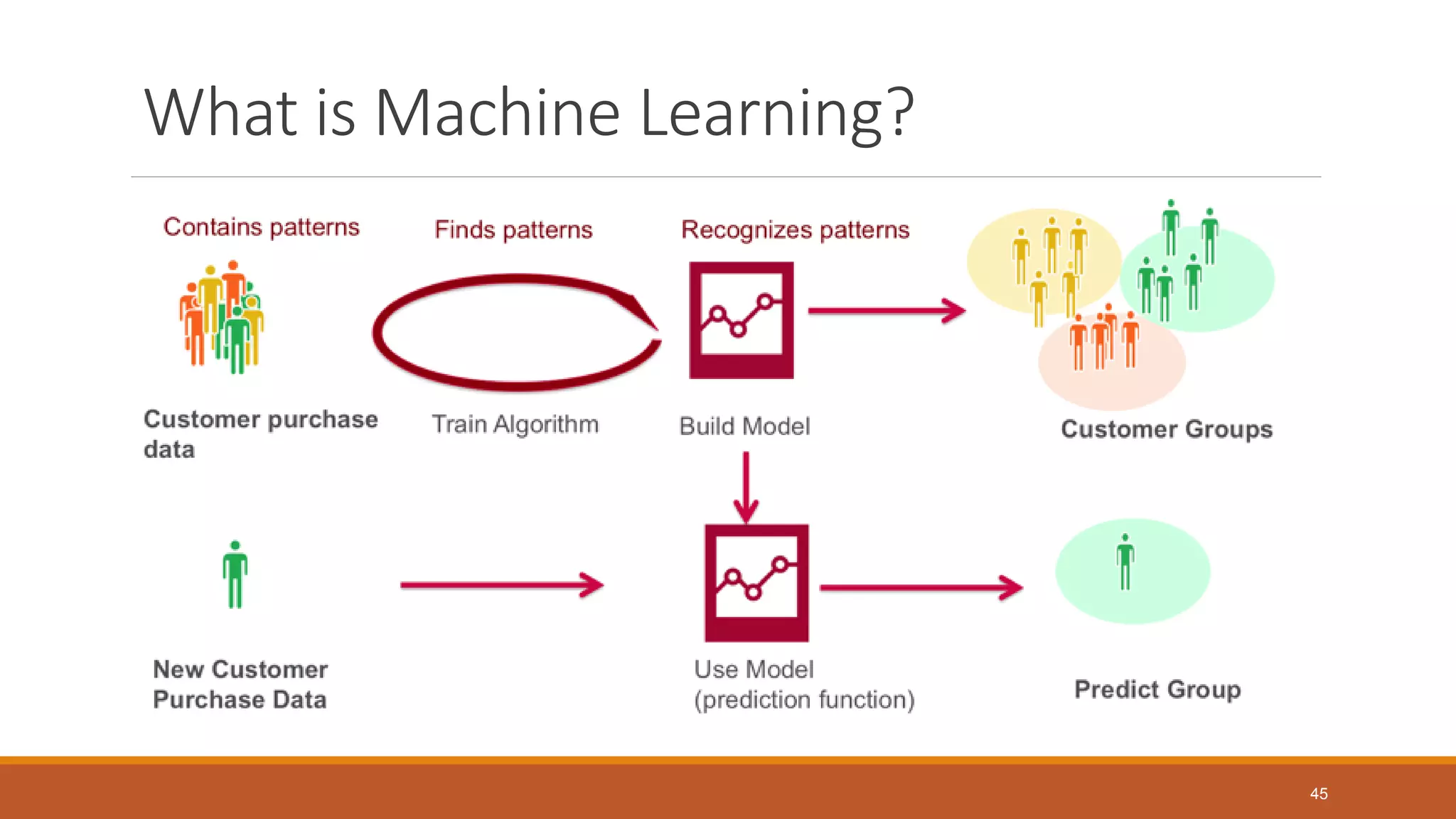
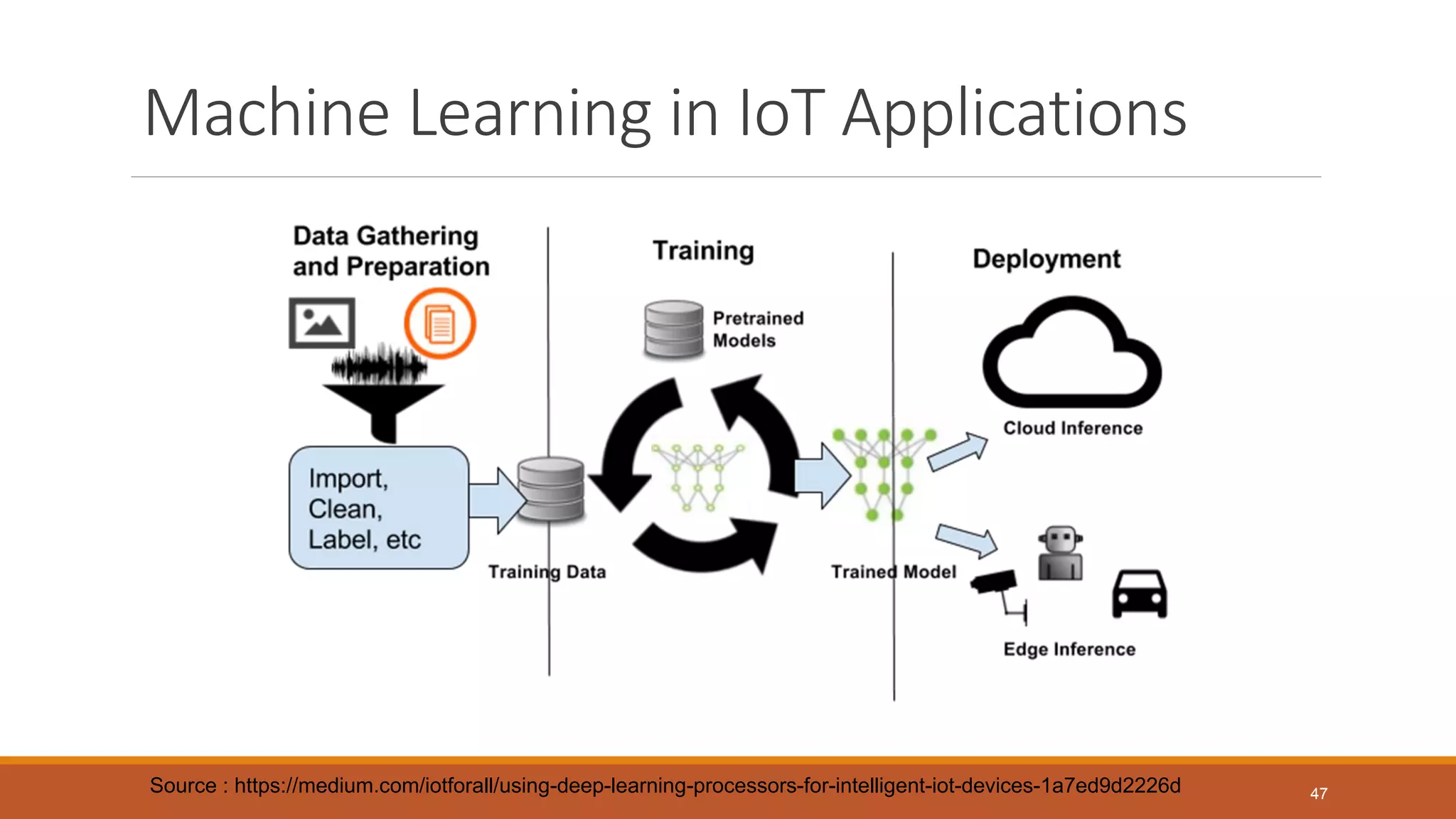
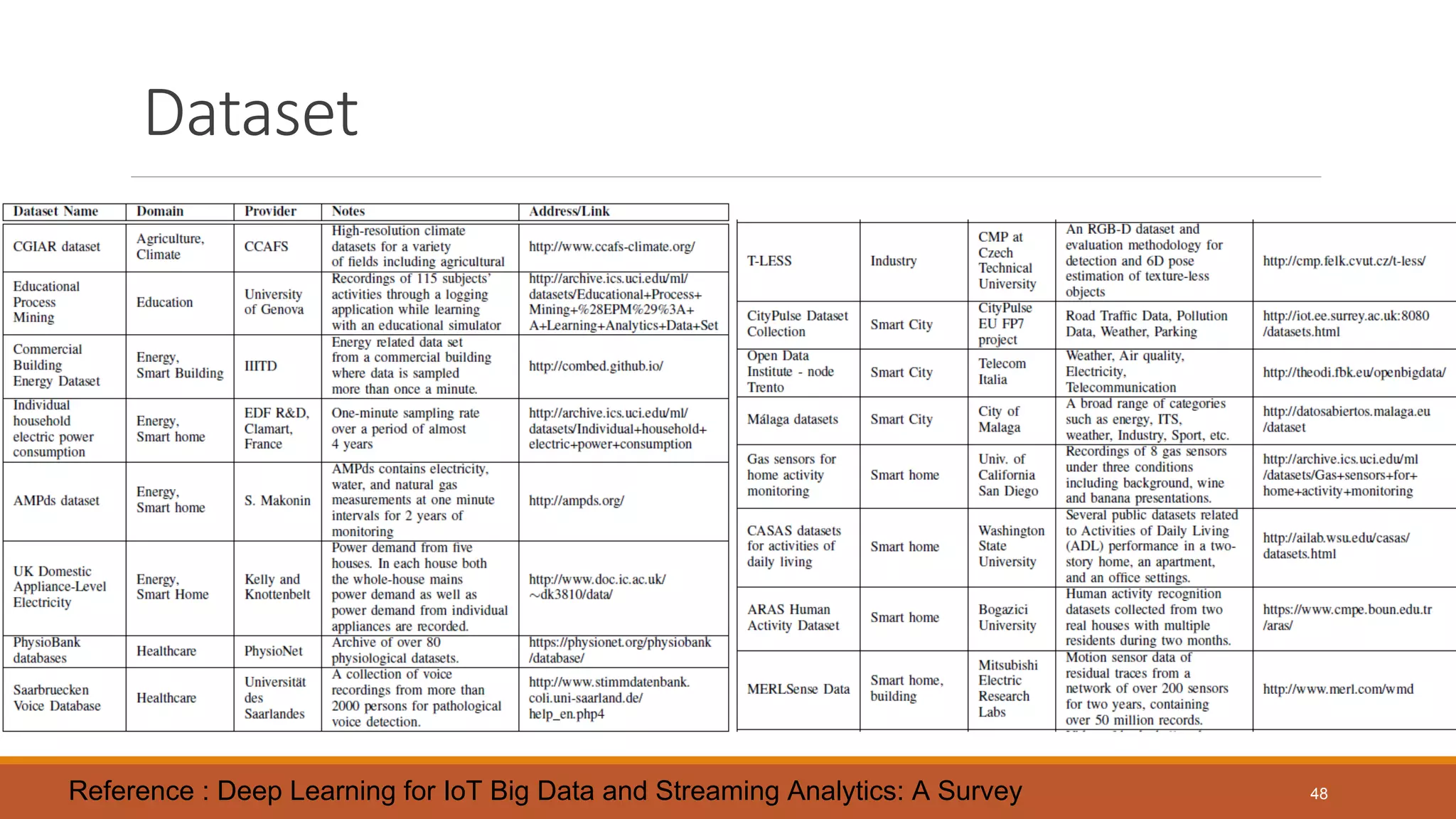
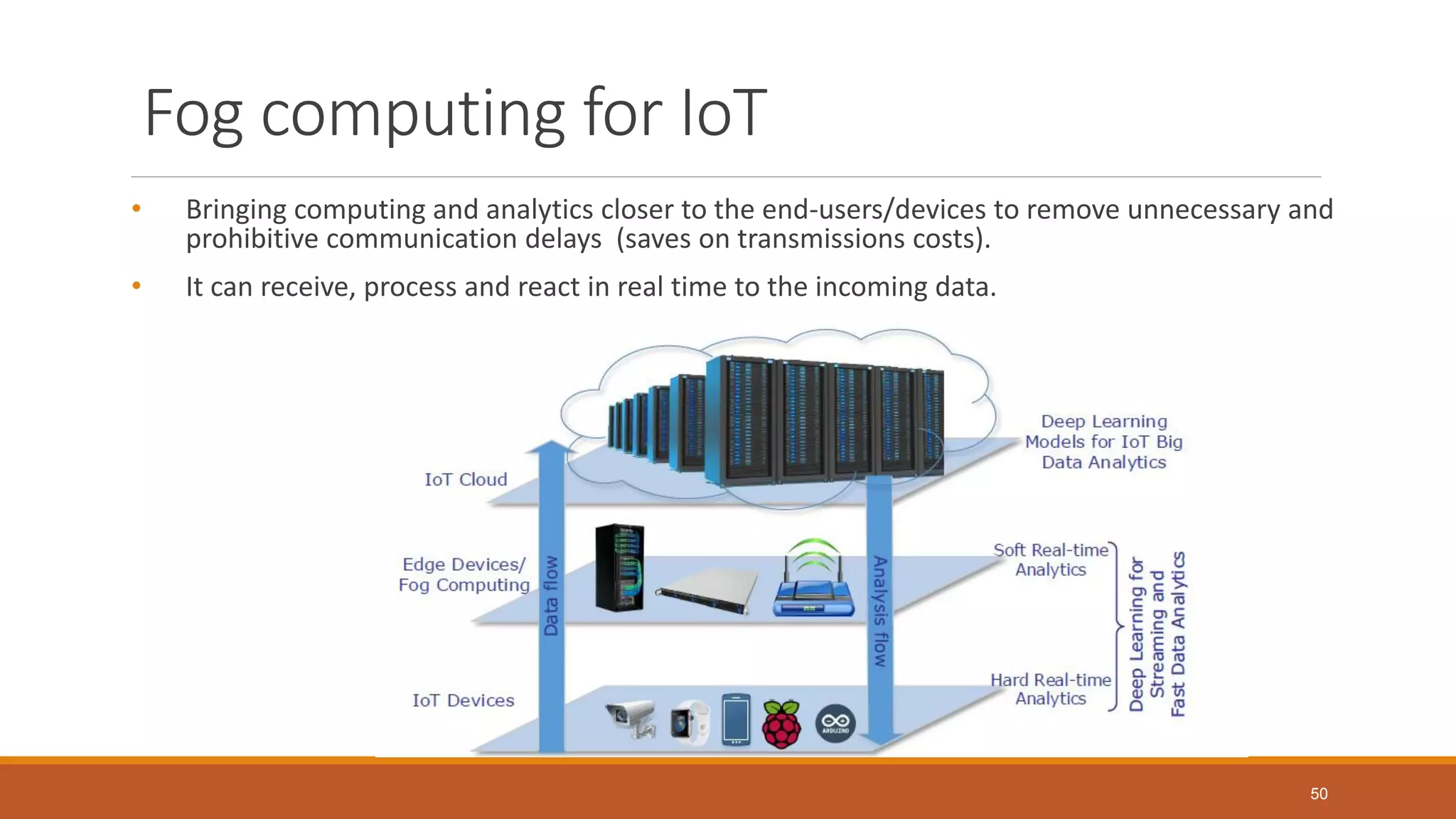
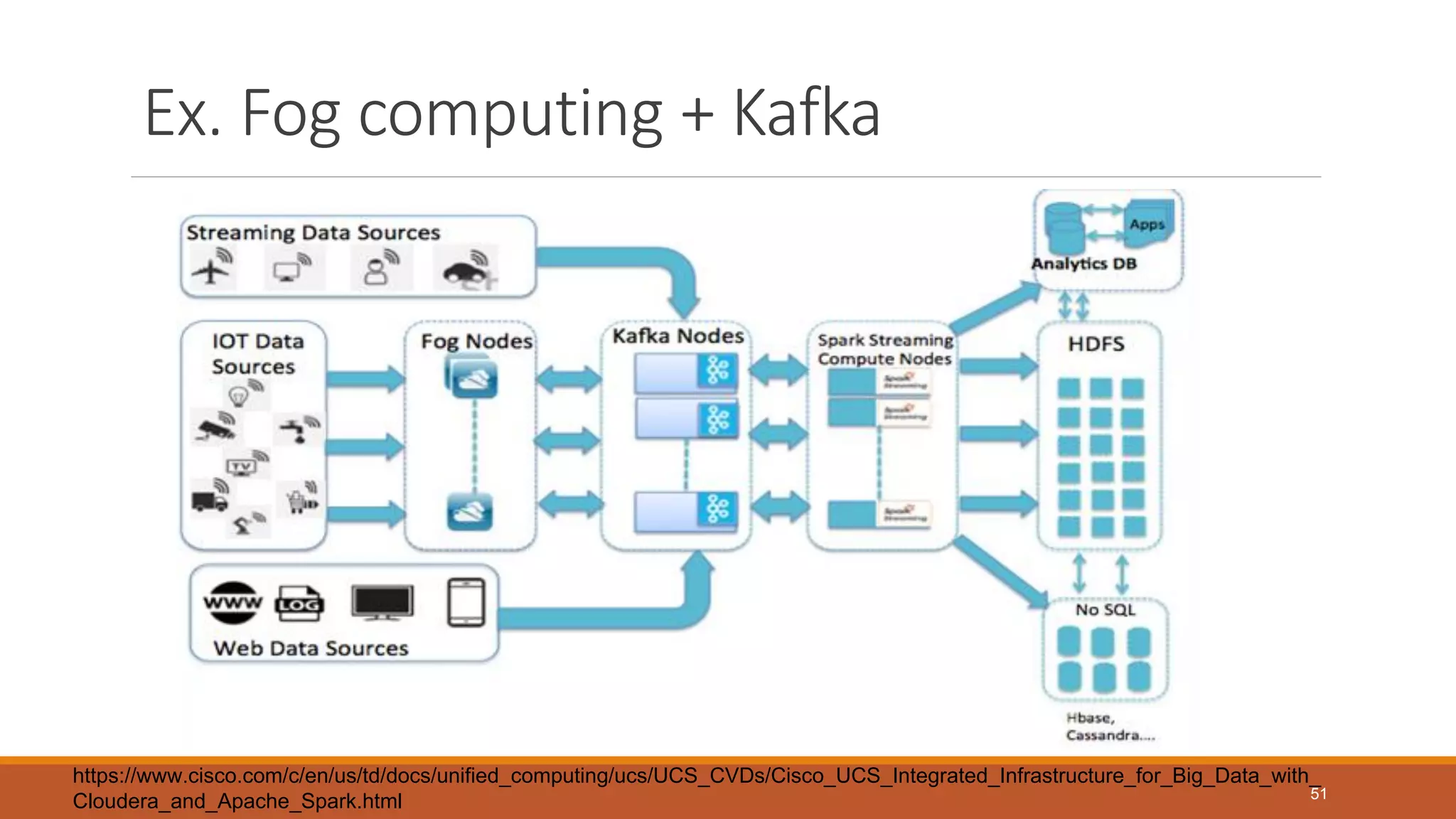
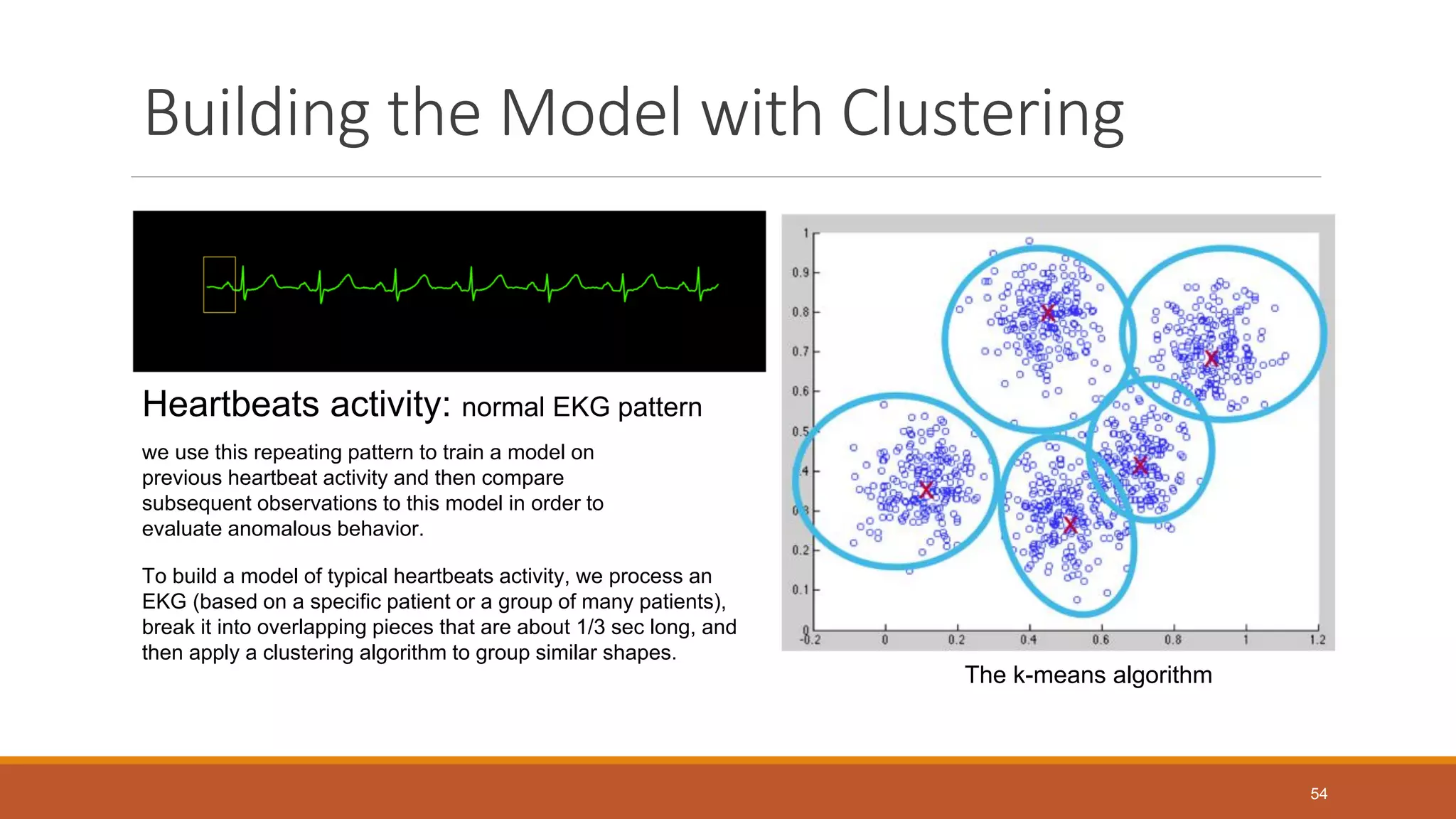
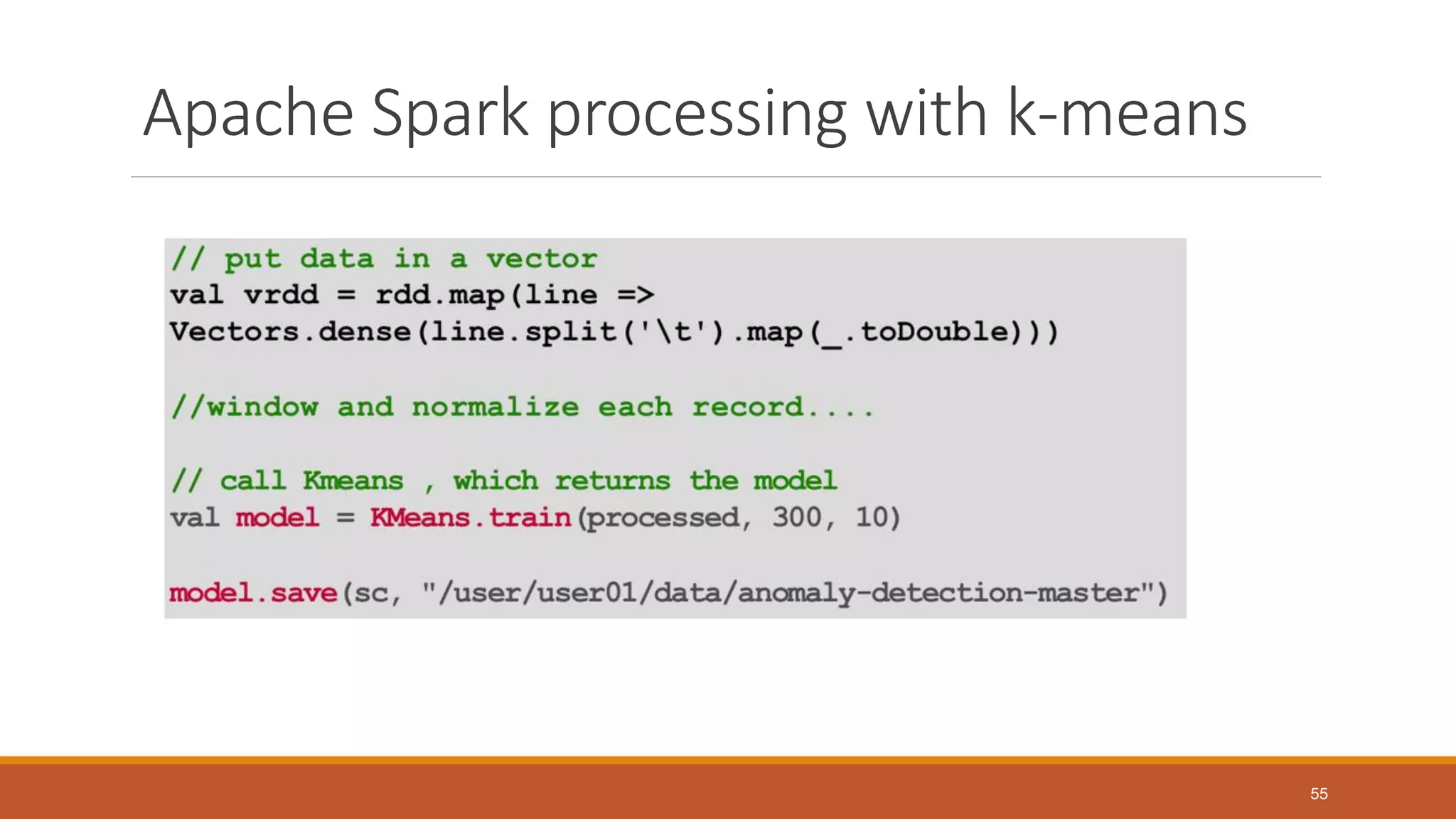
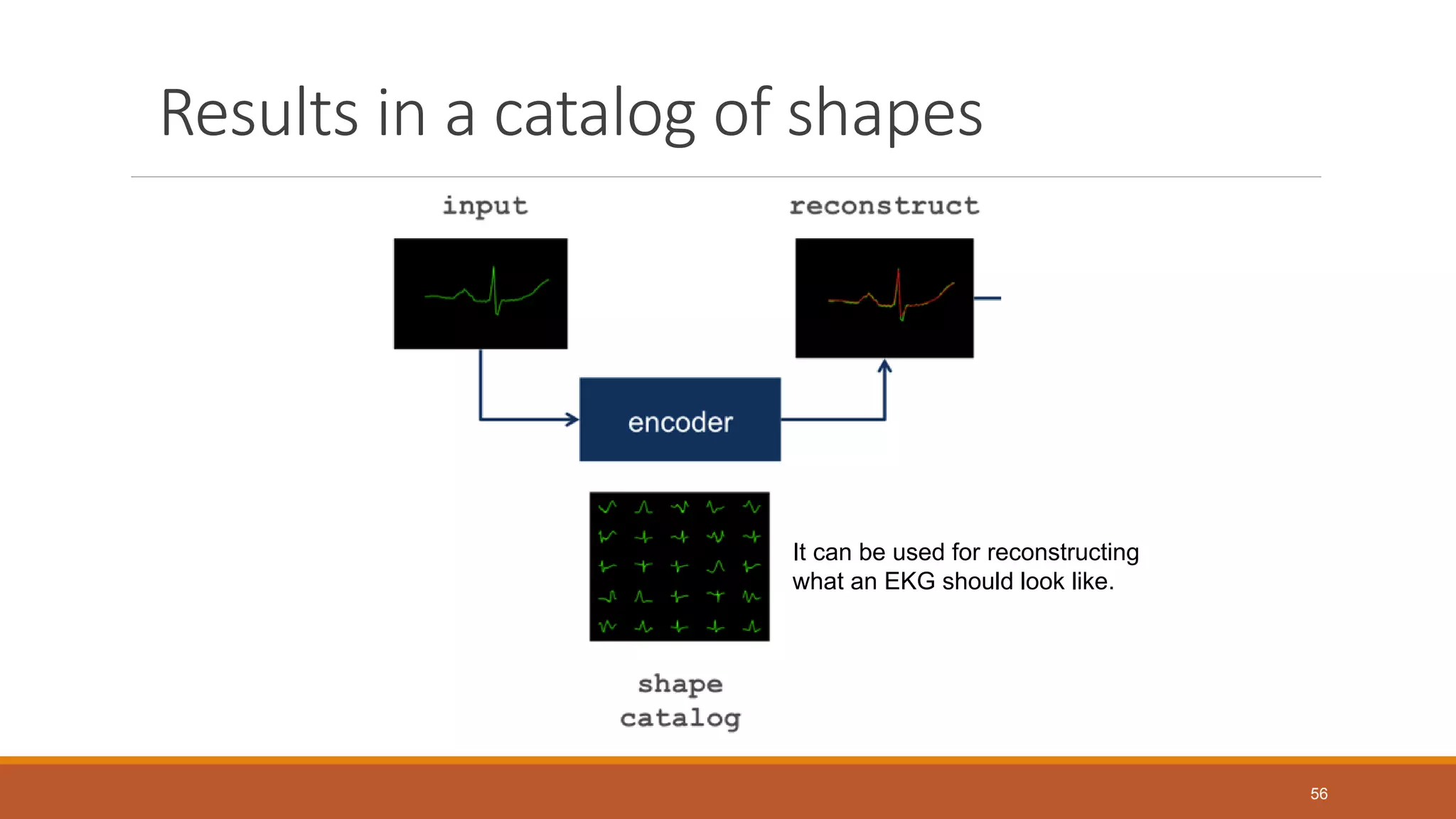
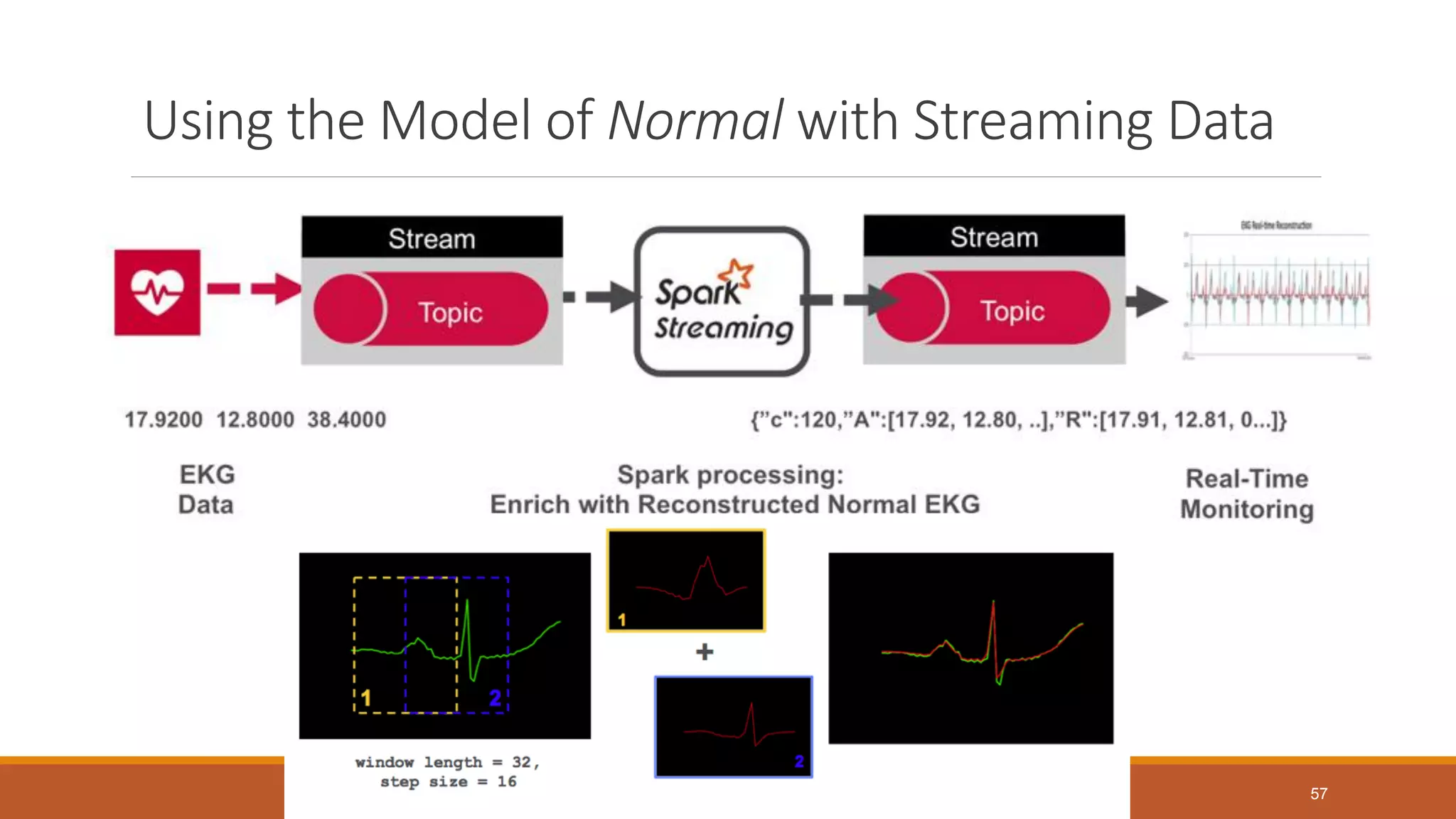
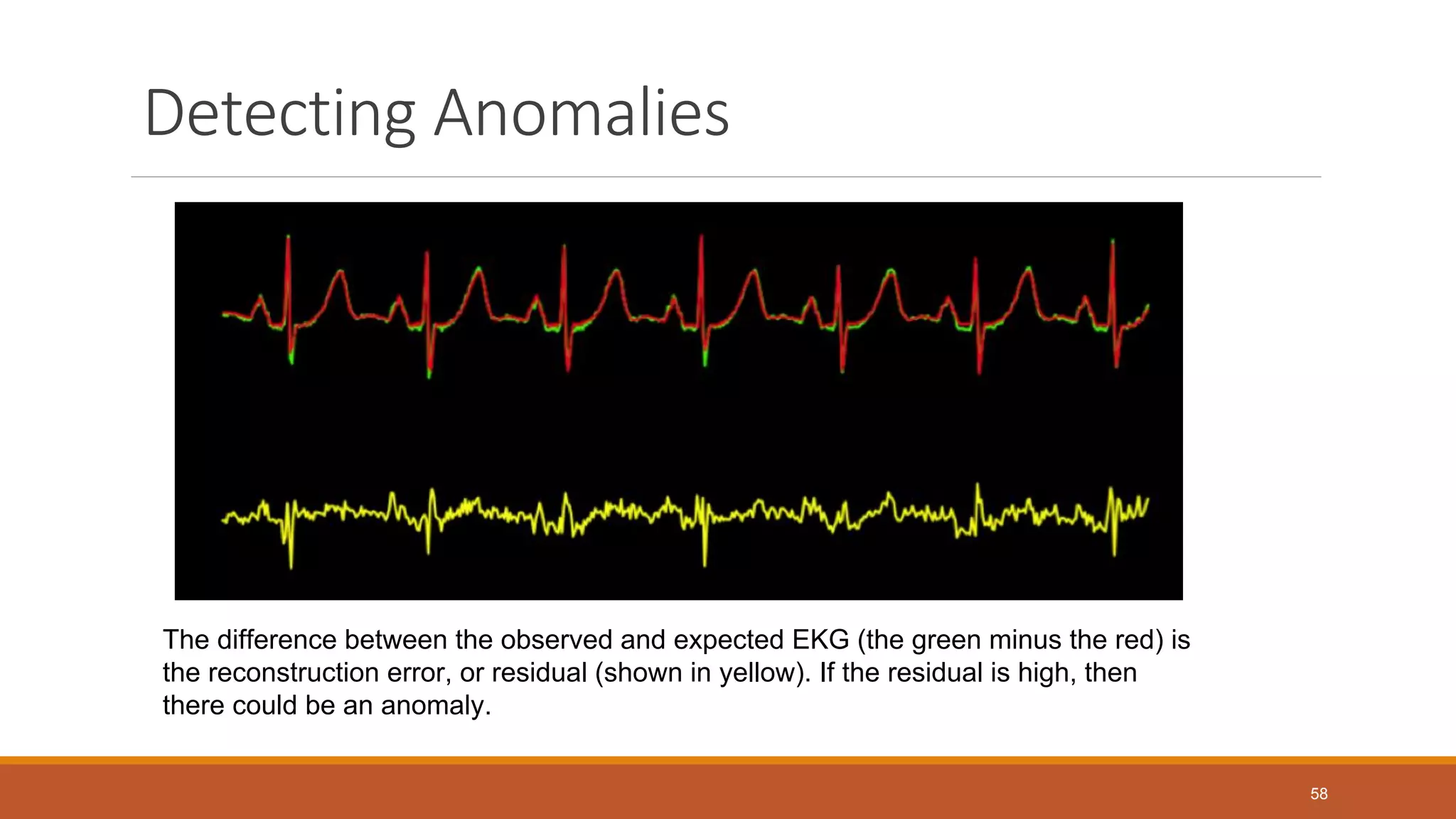
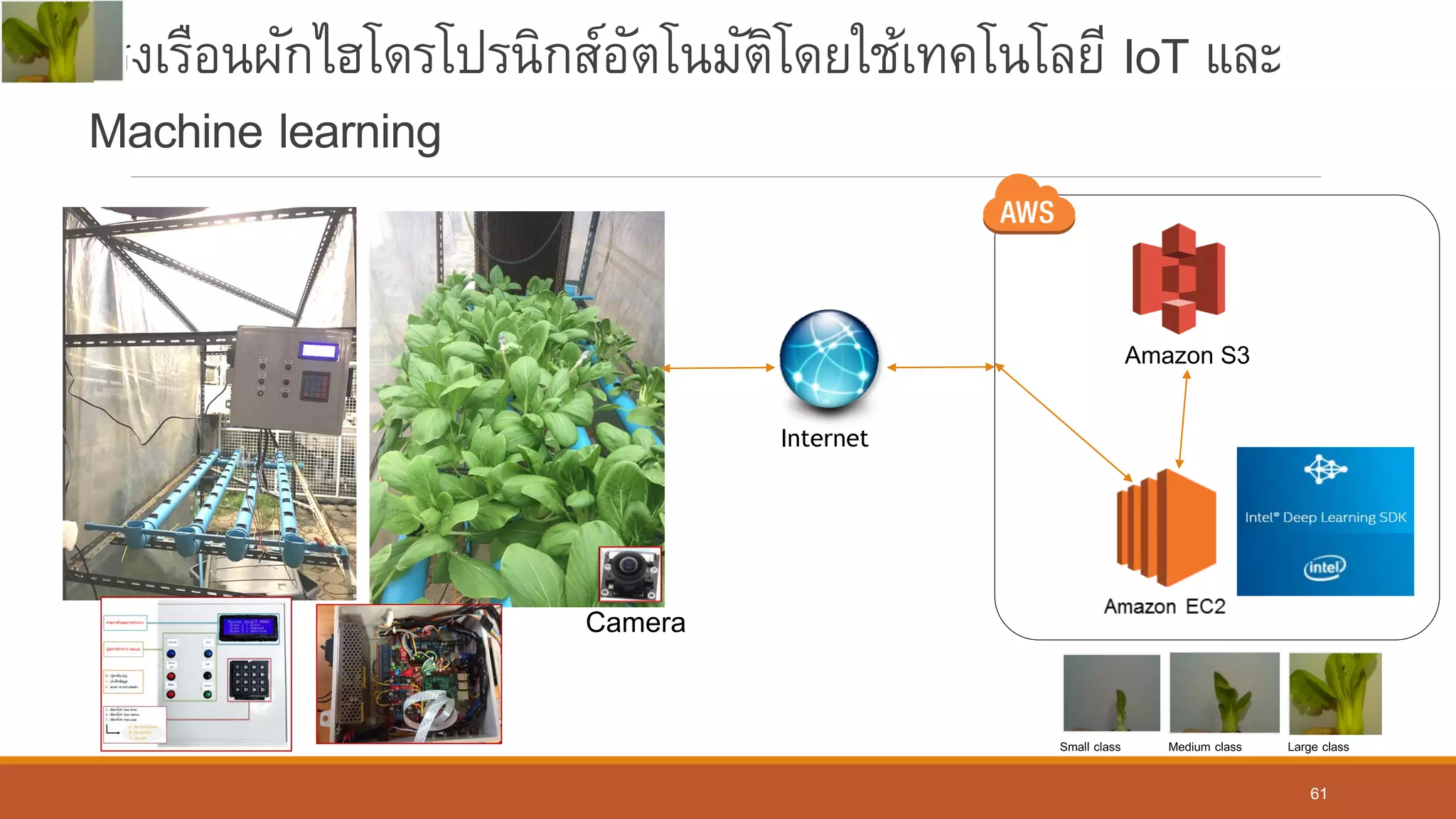
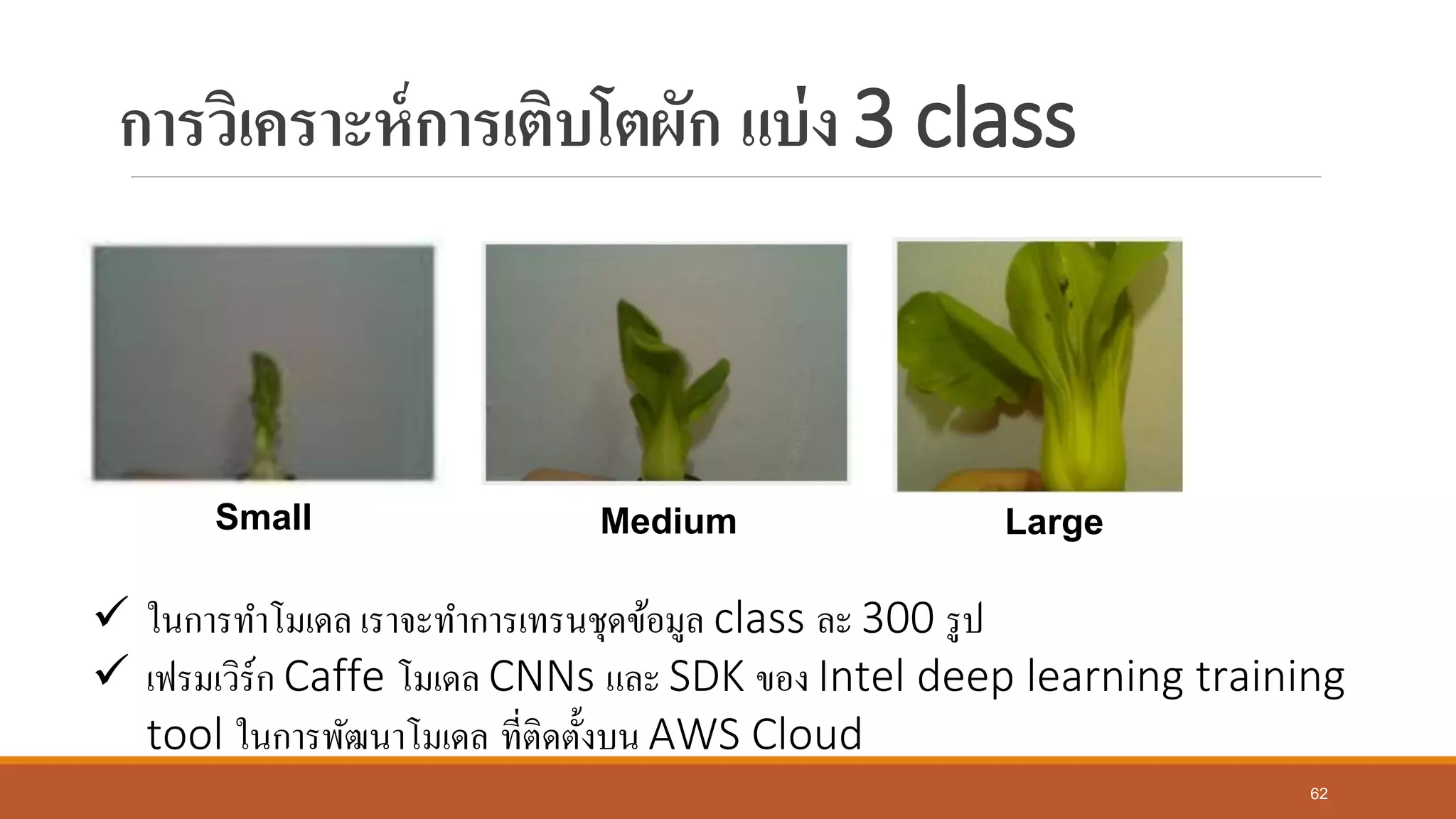
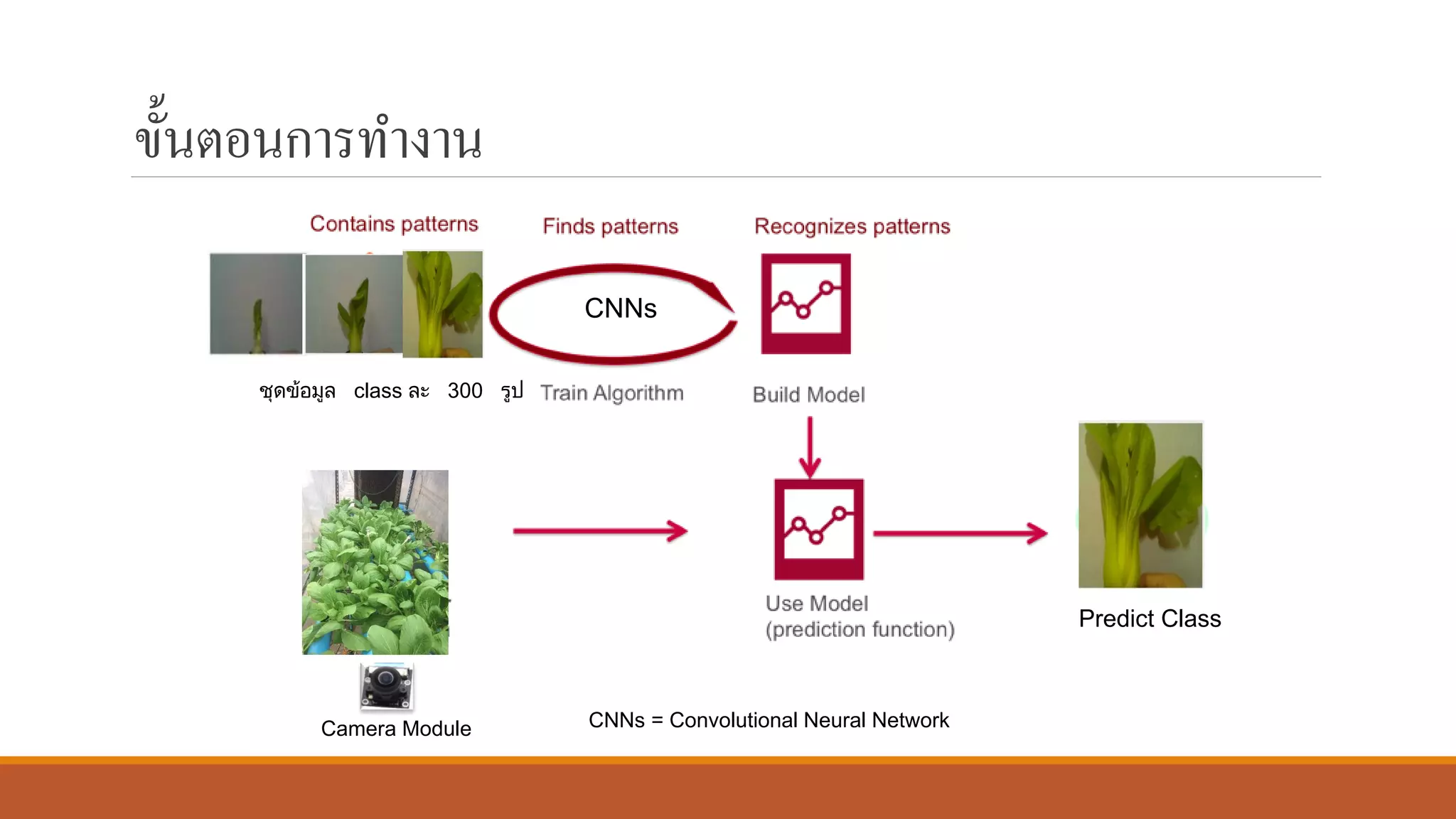
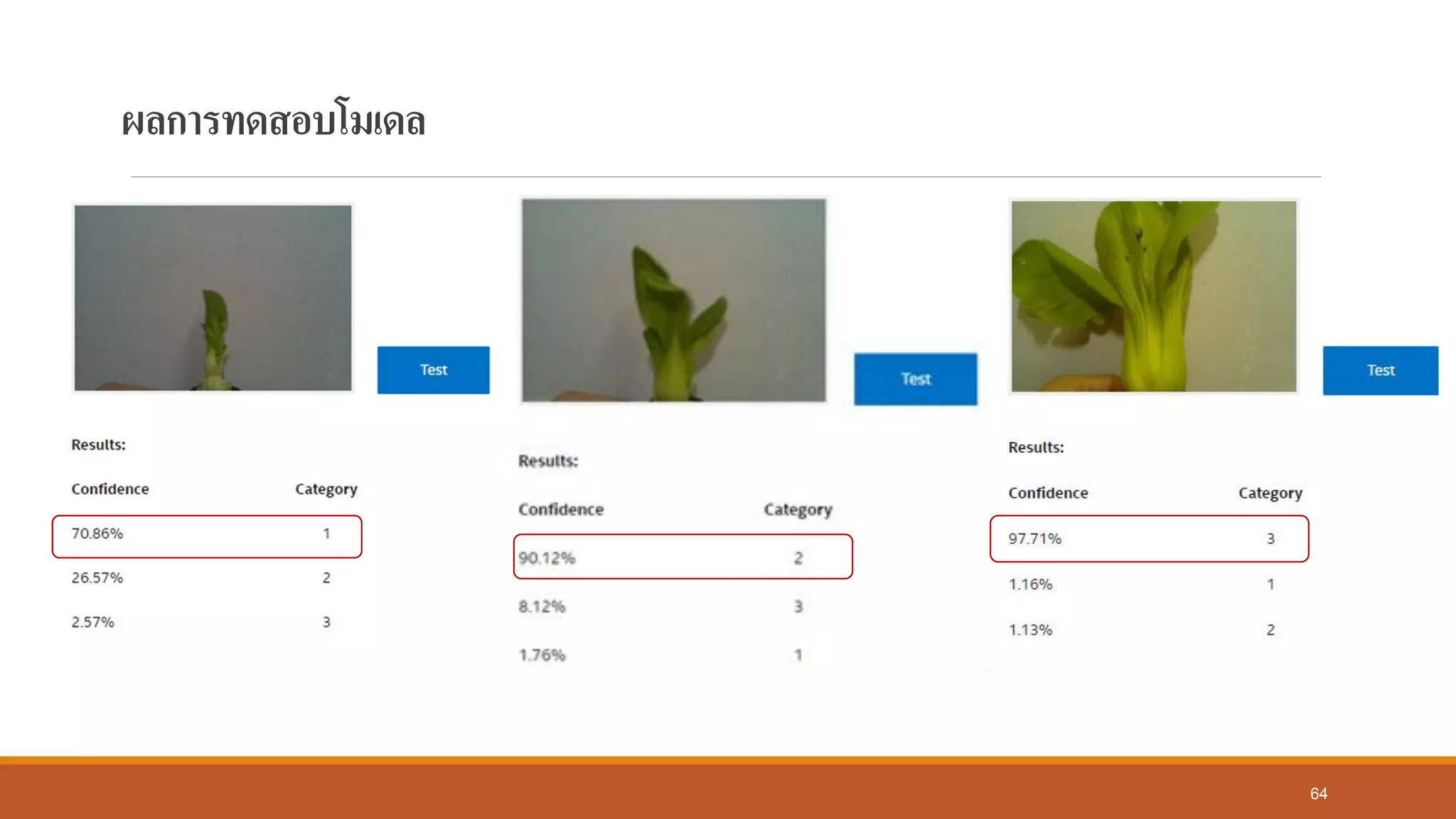
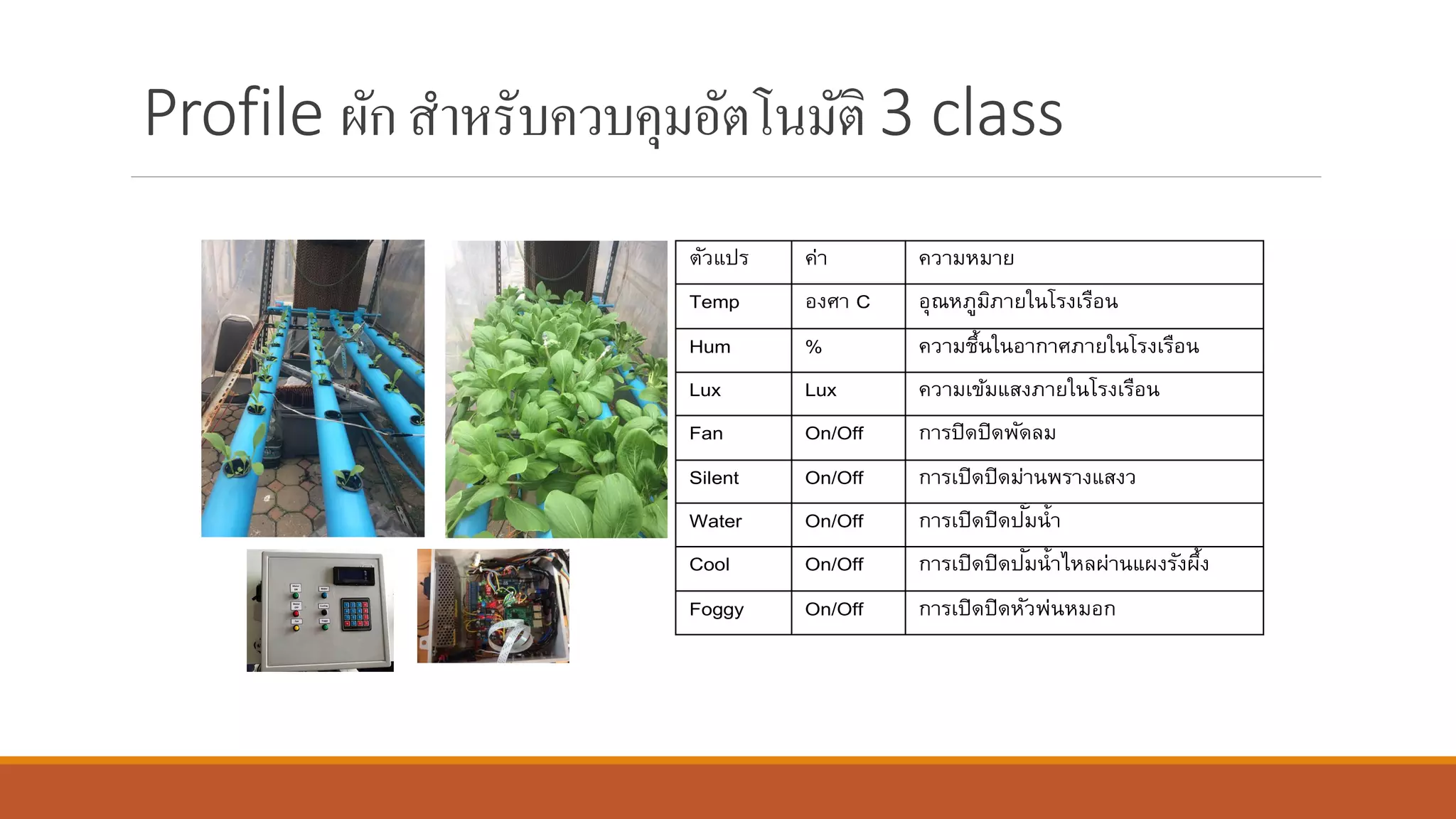
The document discusses the intersection of the Internet of Things (IoT) and Big Data, highlighting the need for advanced machine learning techniques to process high-volume, real-time streaming data. It delves into architectures for IoT Big Data analytics, including the use of Apache Kafka as a distributed streaming platform. Additionally, it presents case studies illustrating machine learning applications in healthcare and agriculture, while addressing challenges such as data security and the need for large datasets.