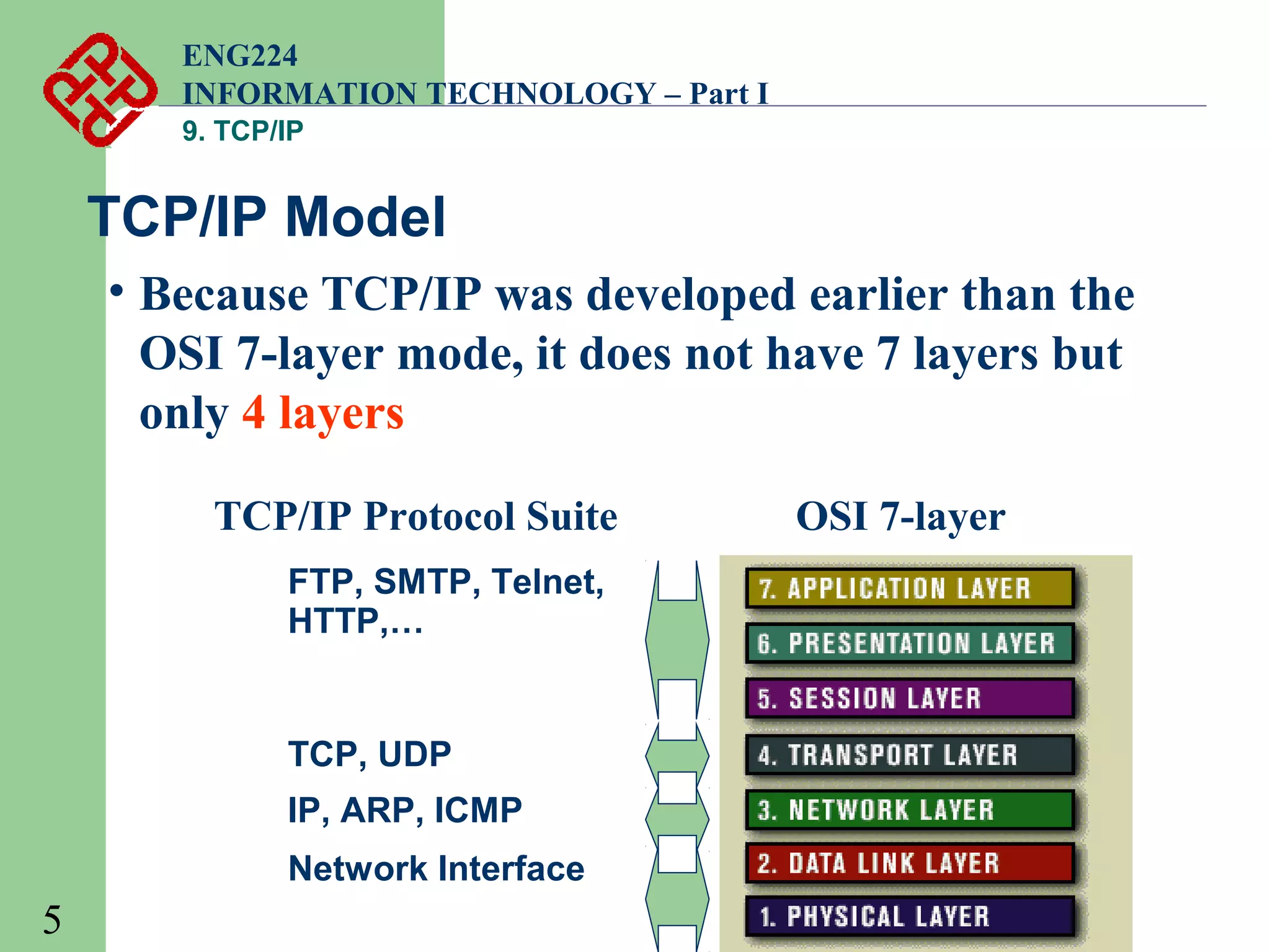
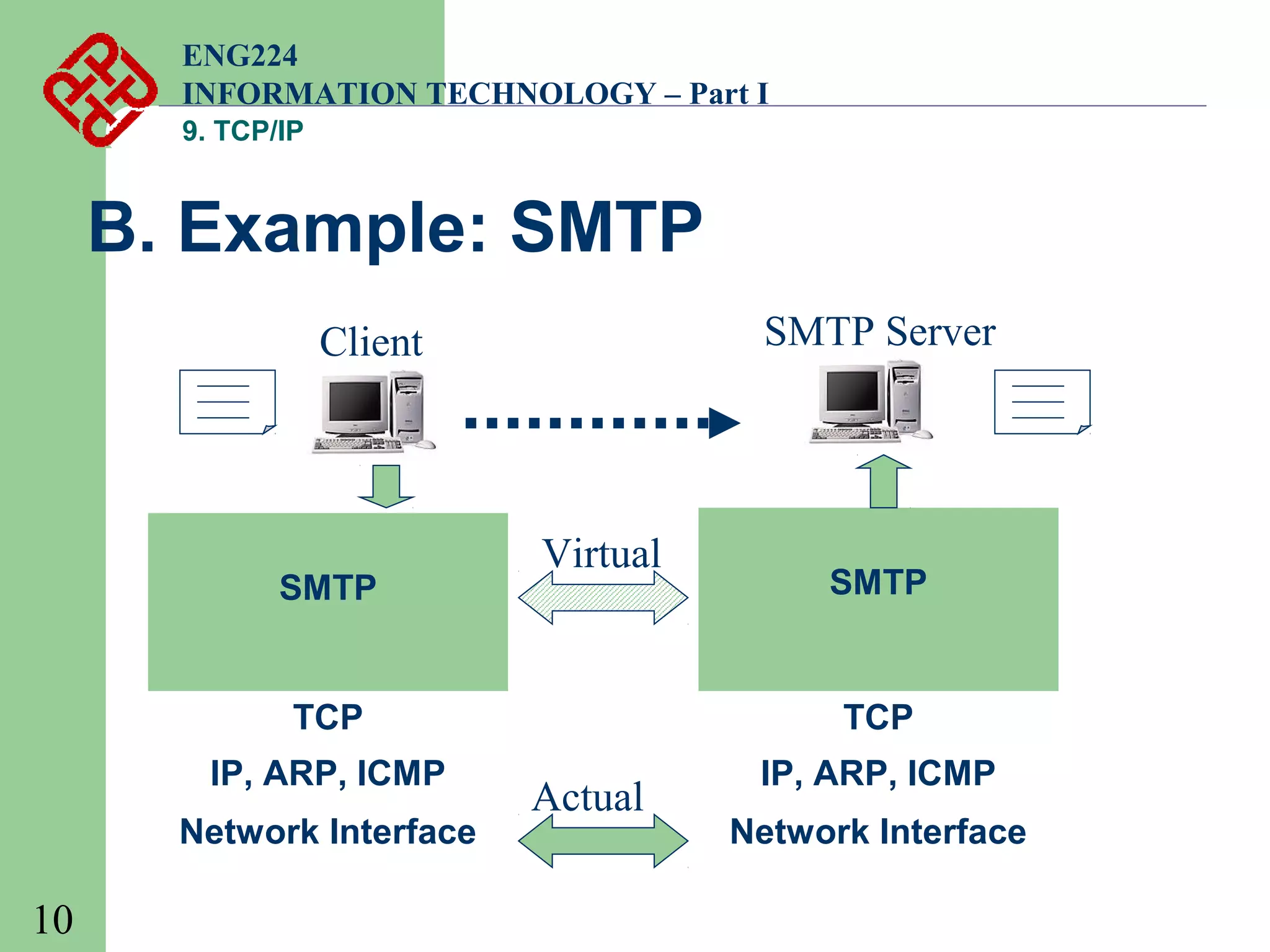
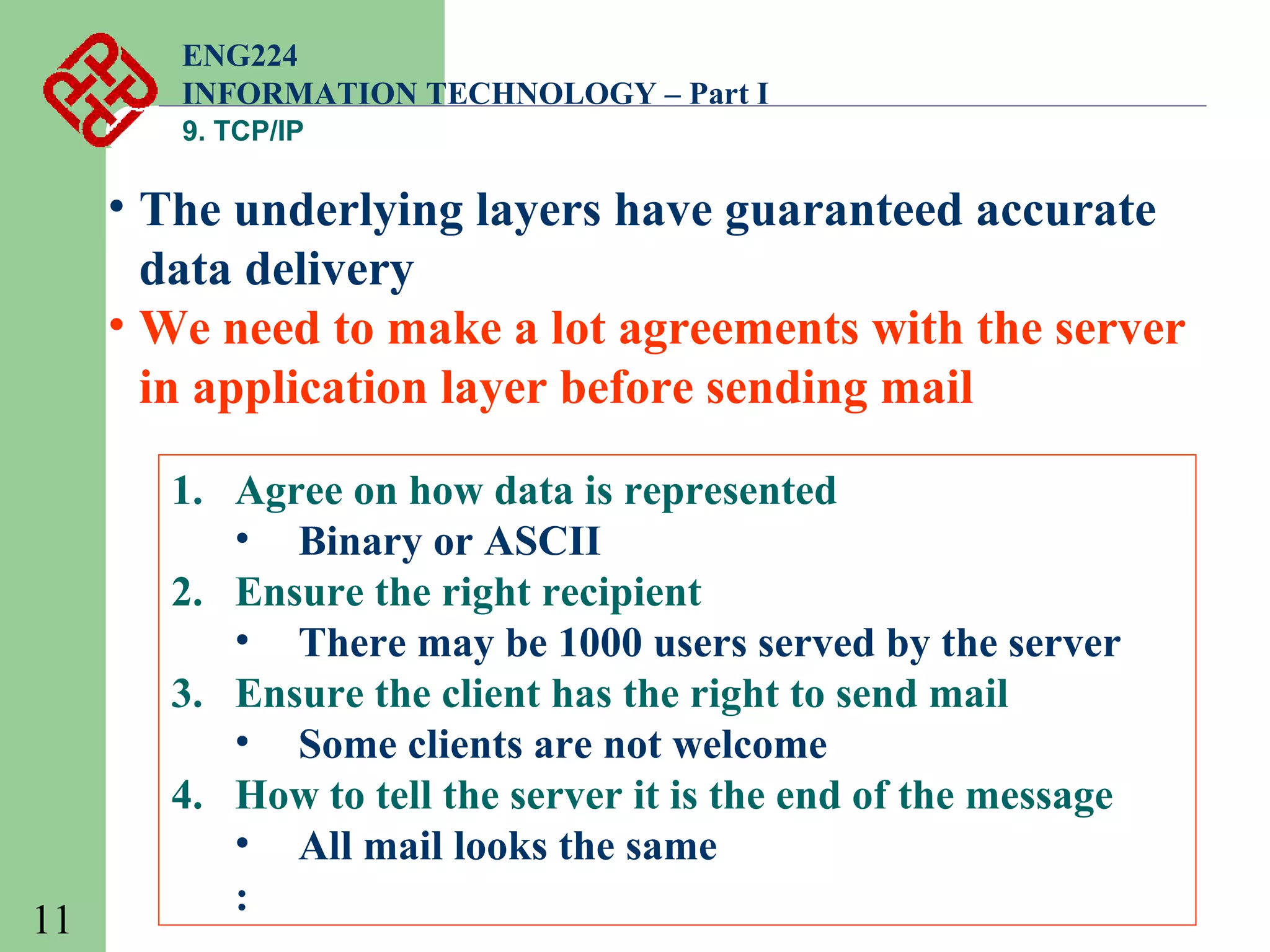
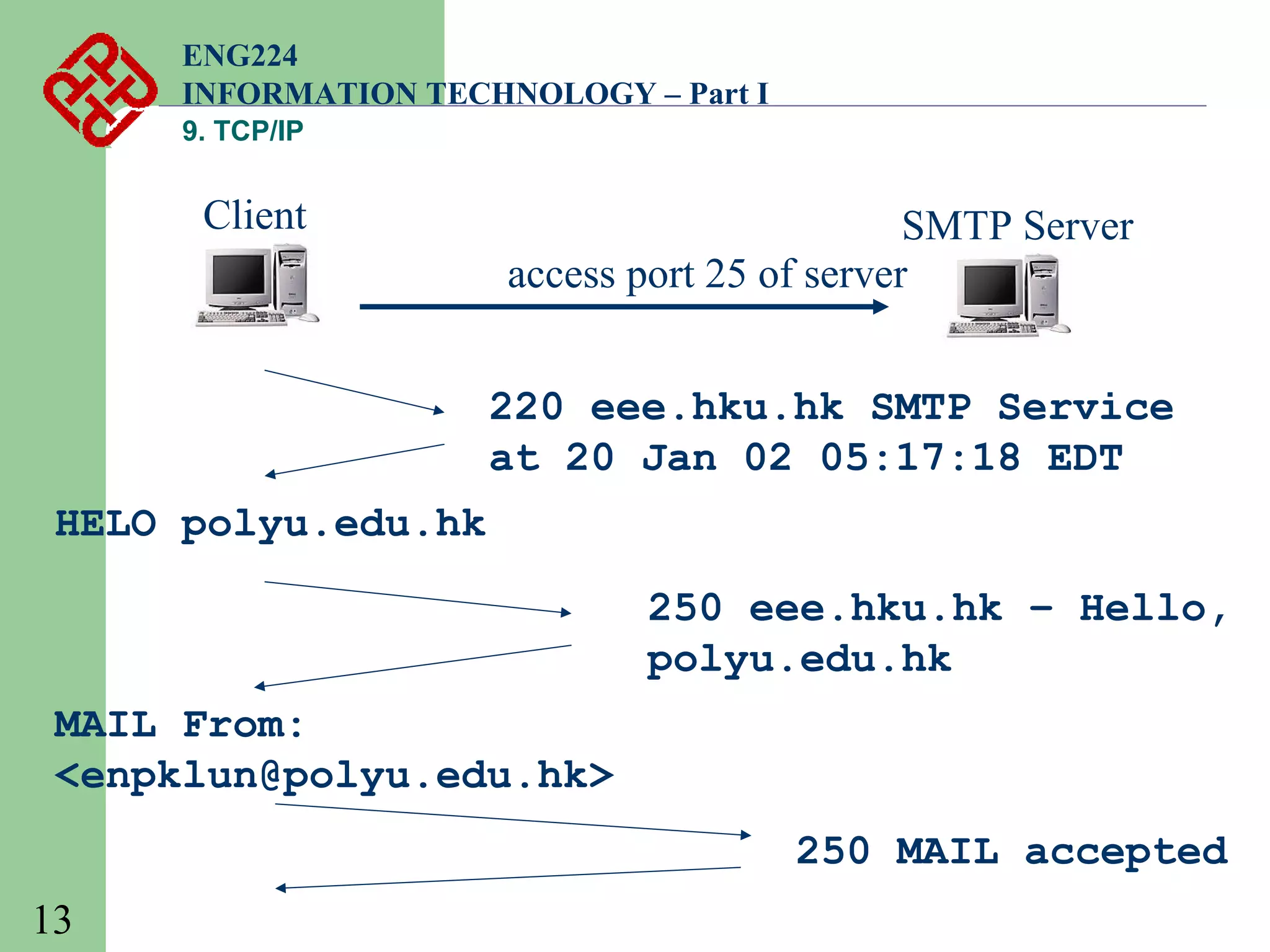
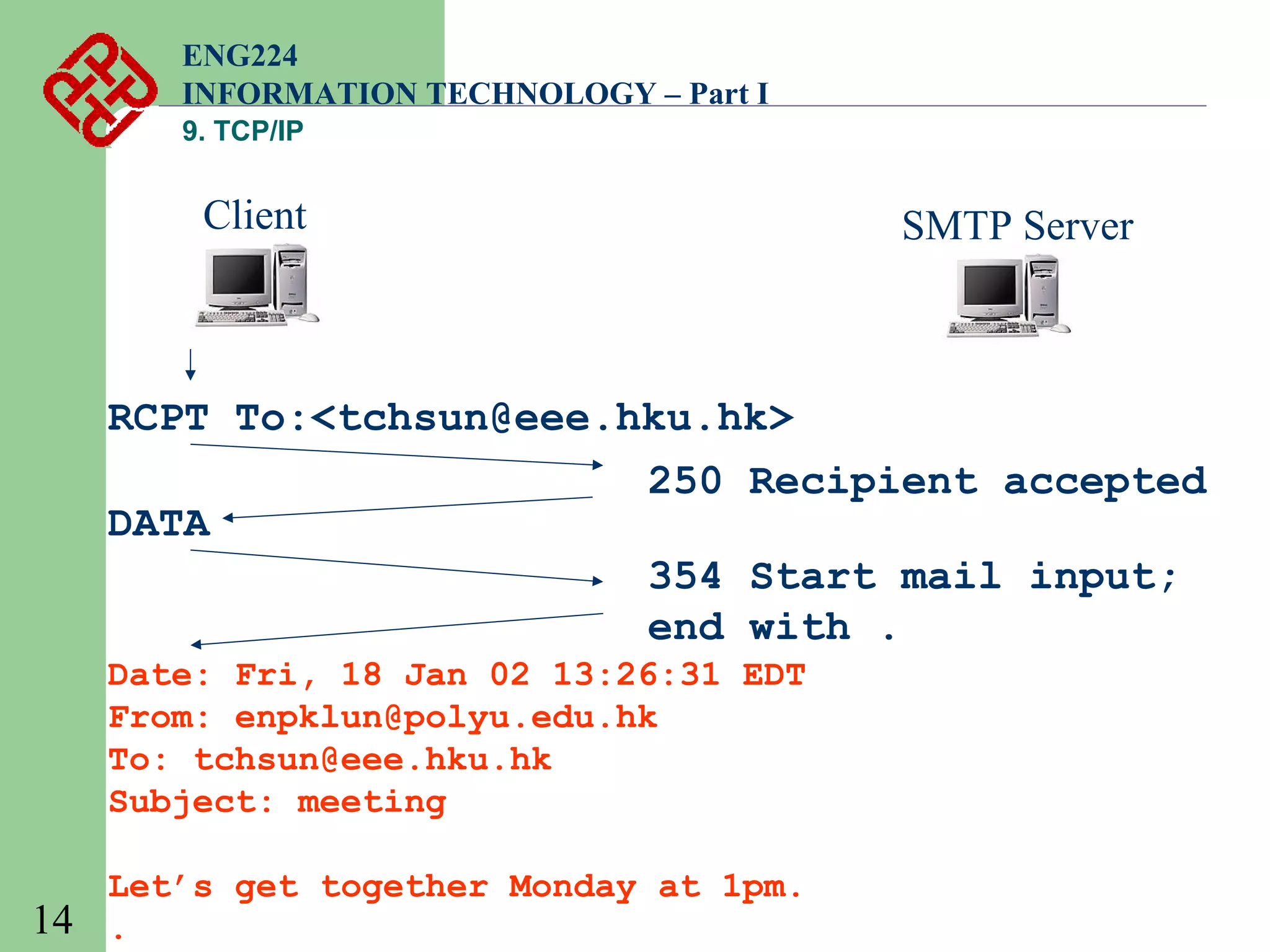
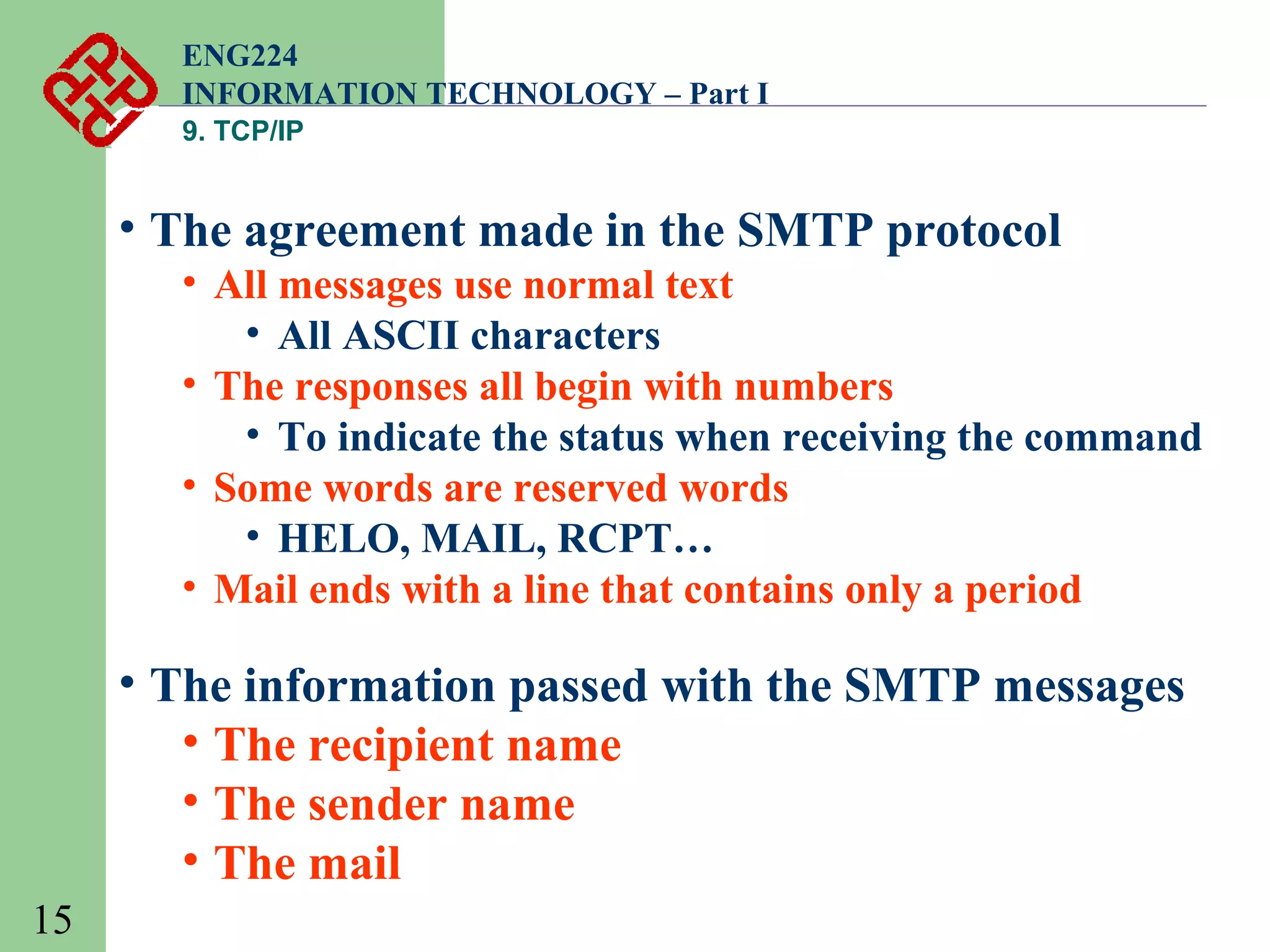
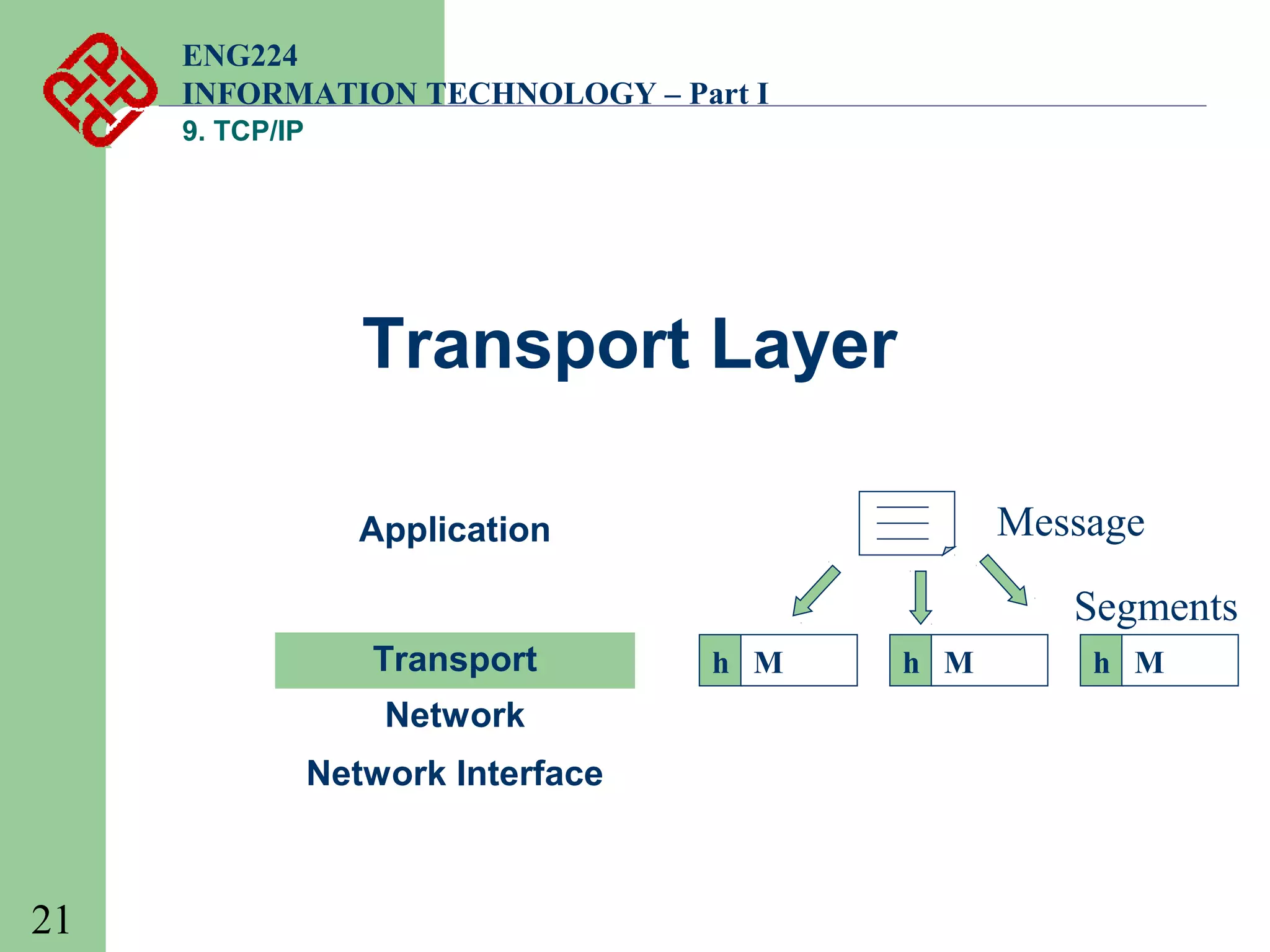
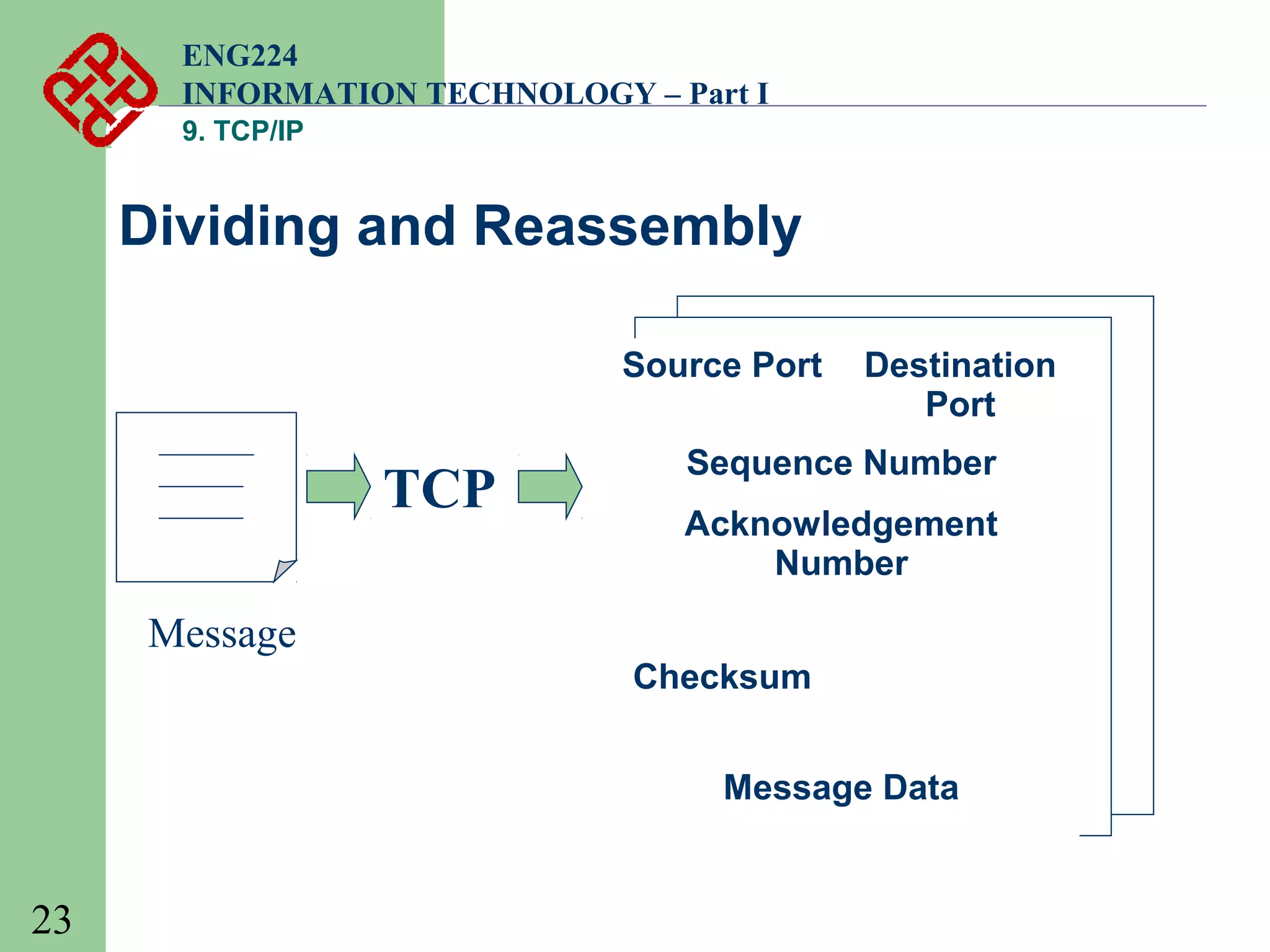
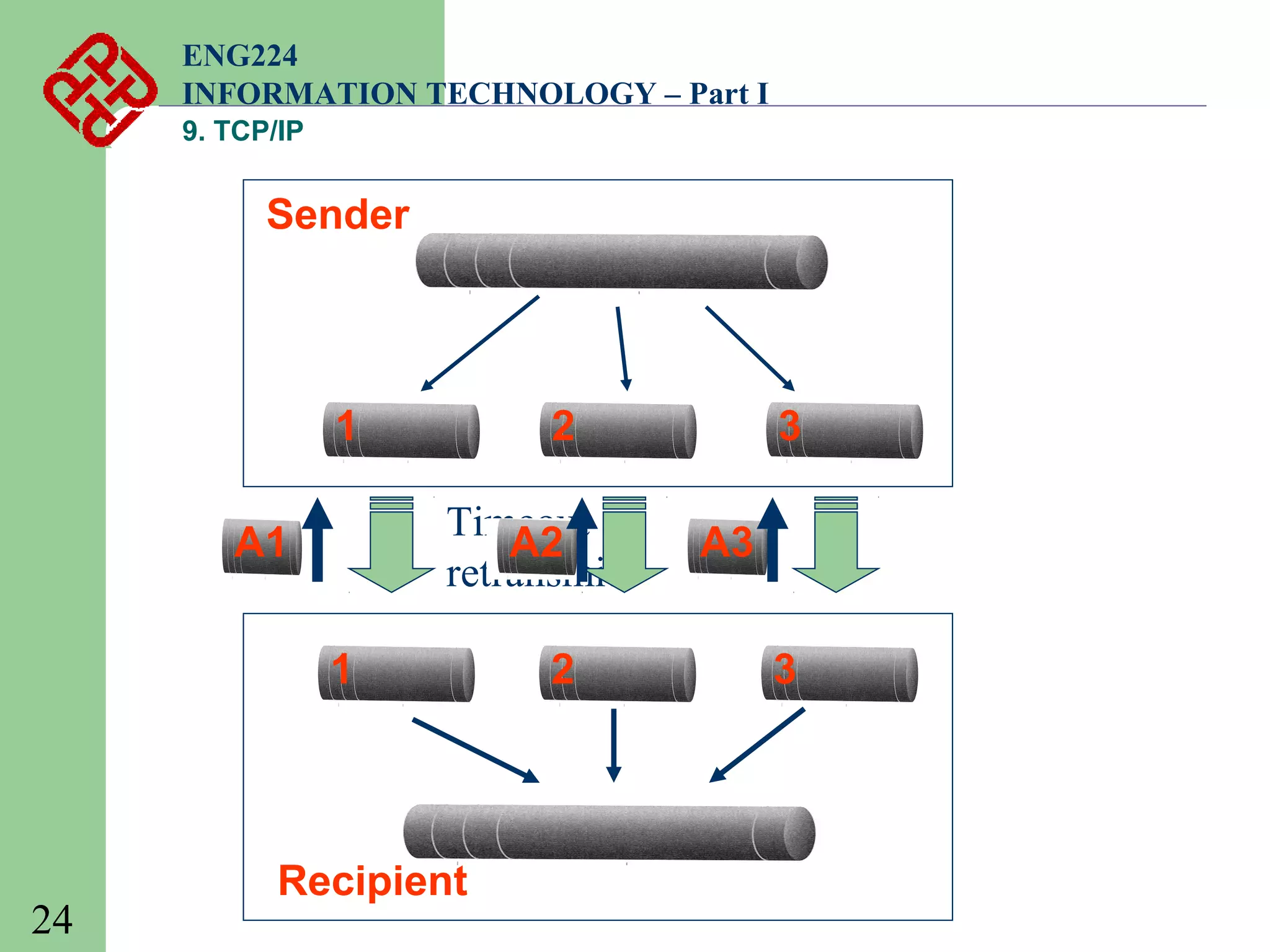
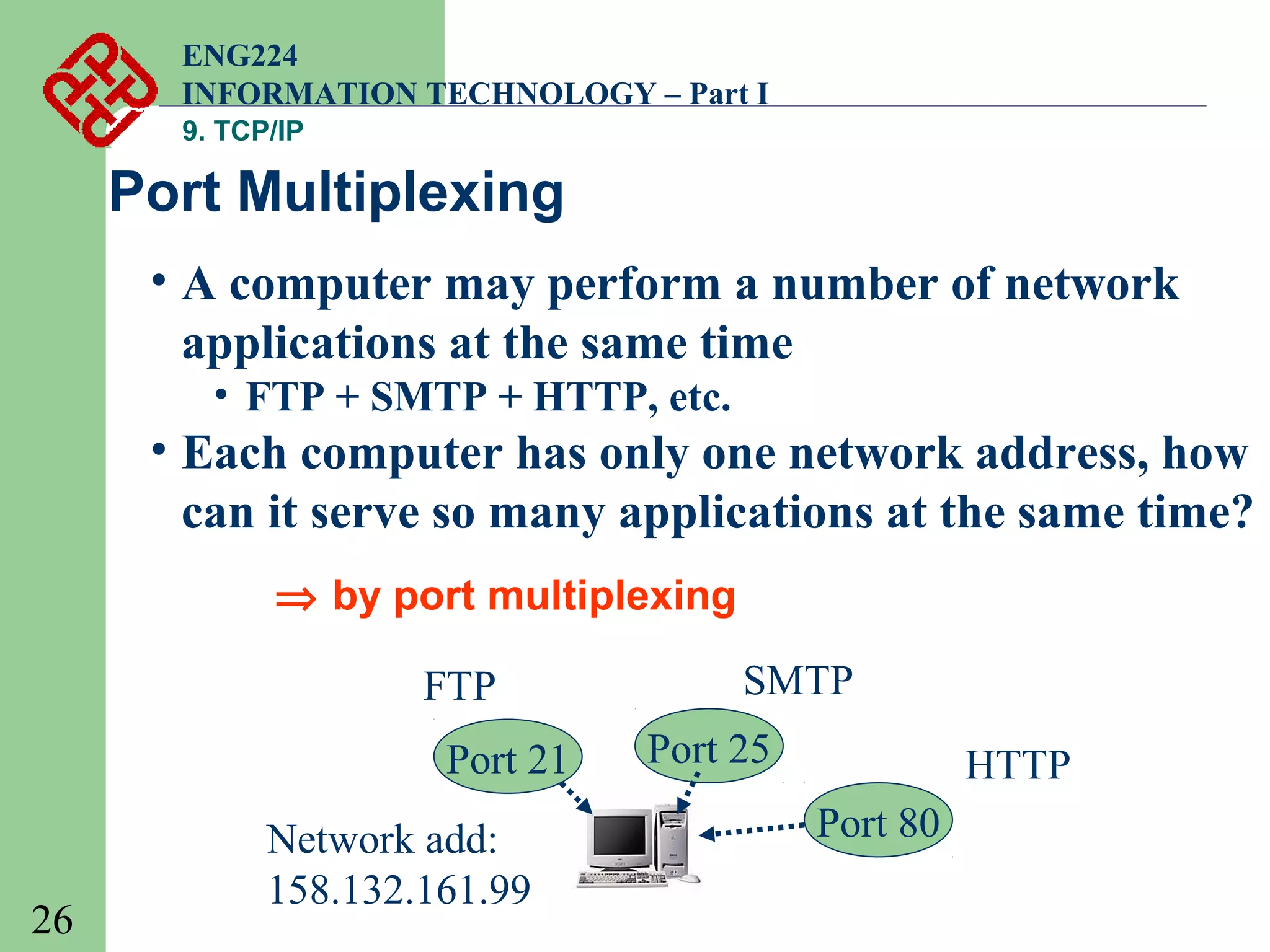
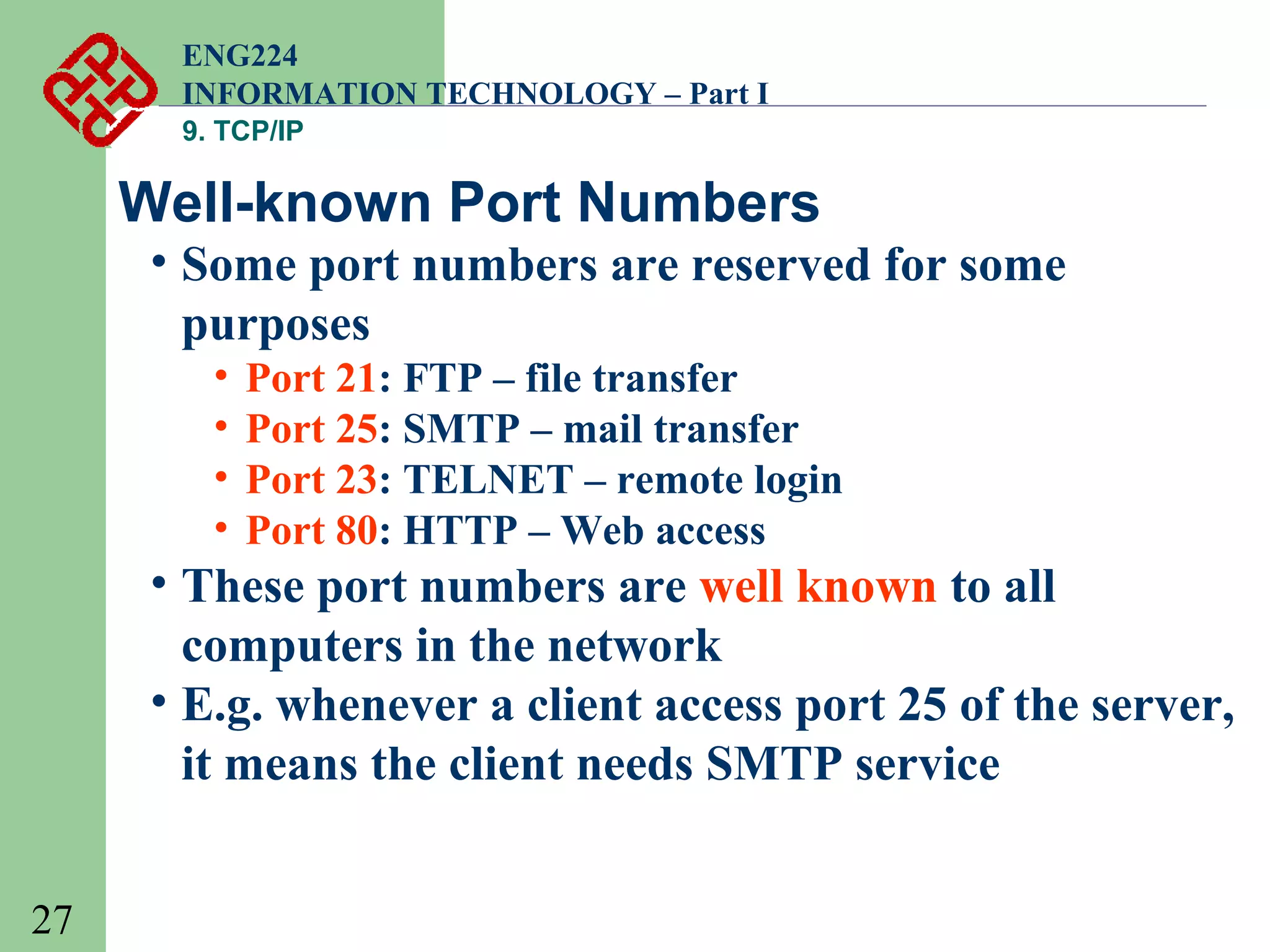
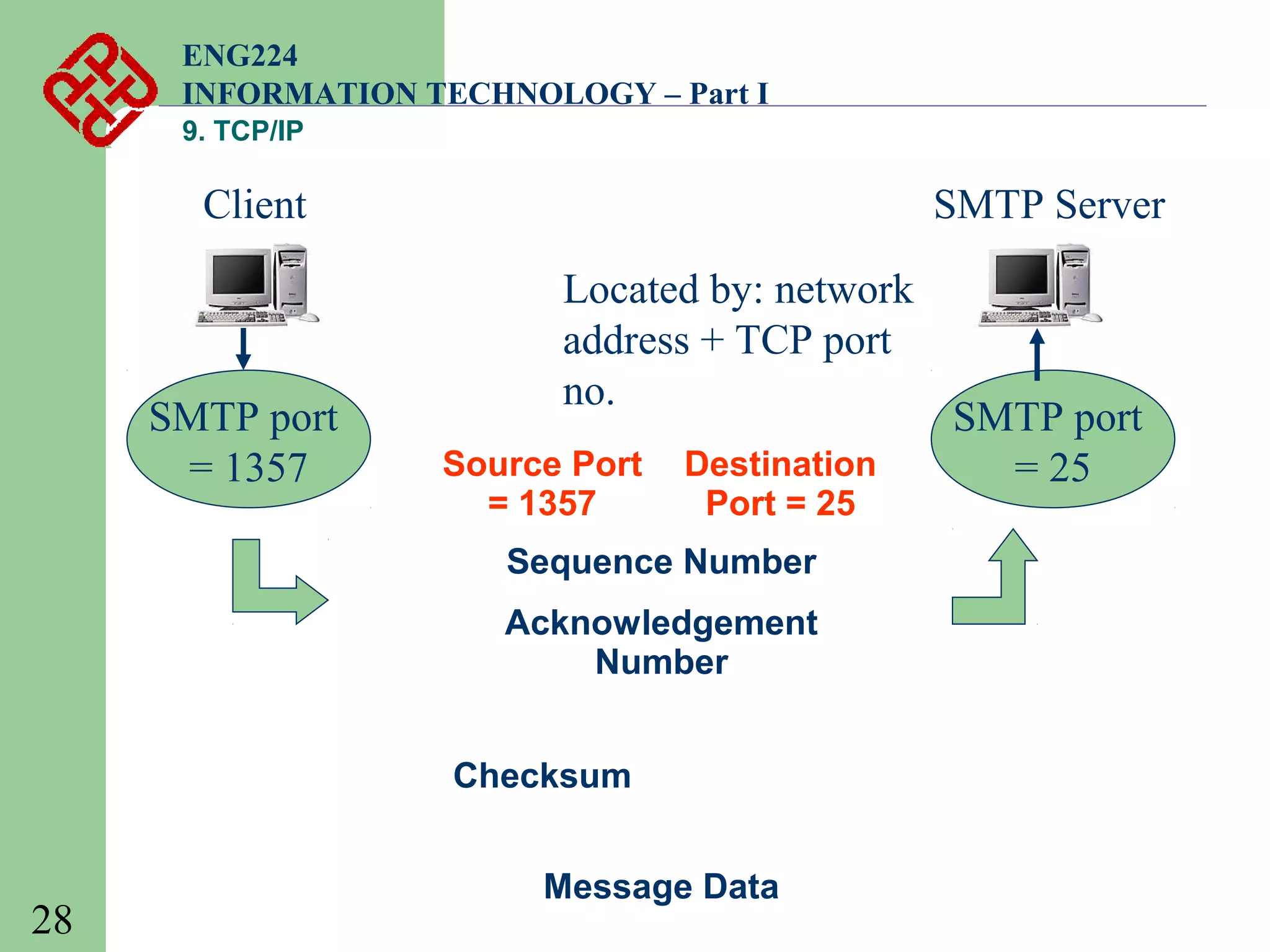
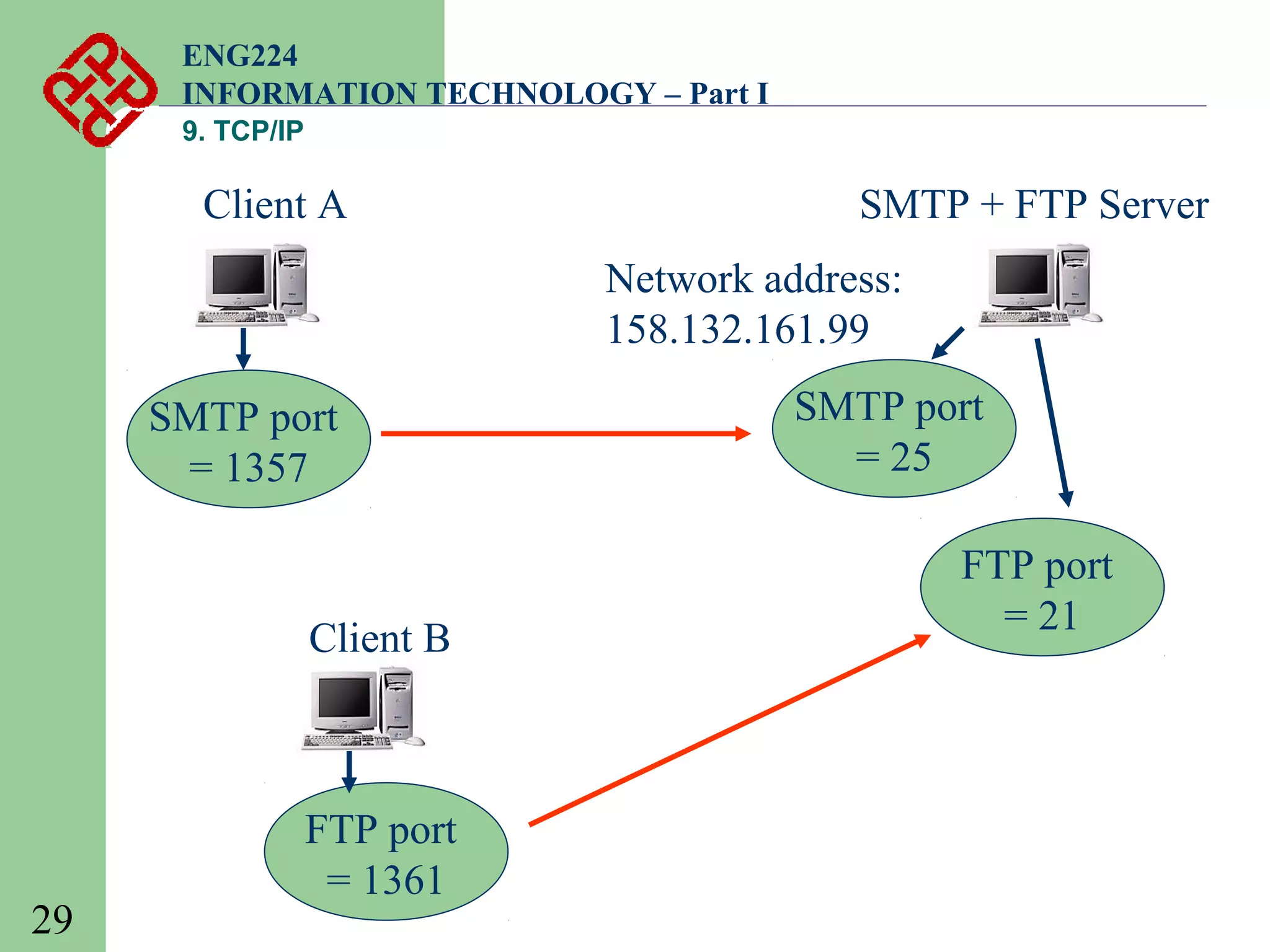
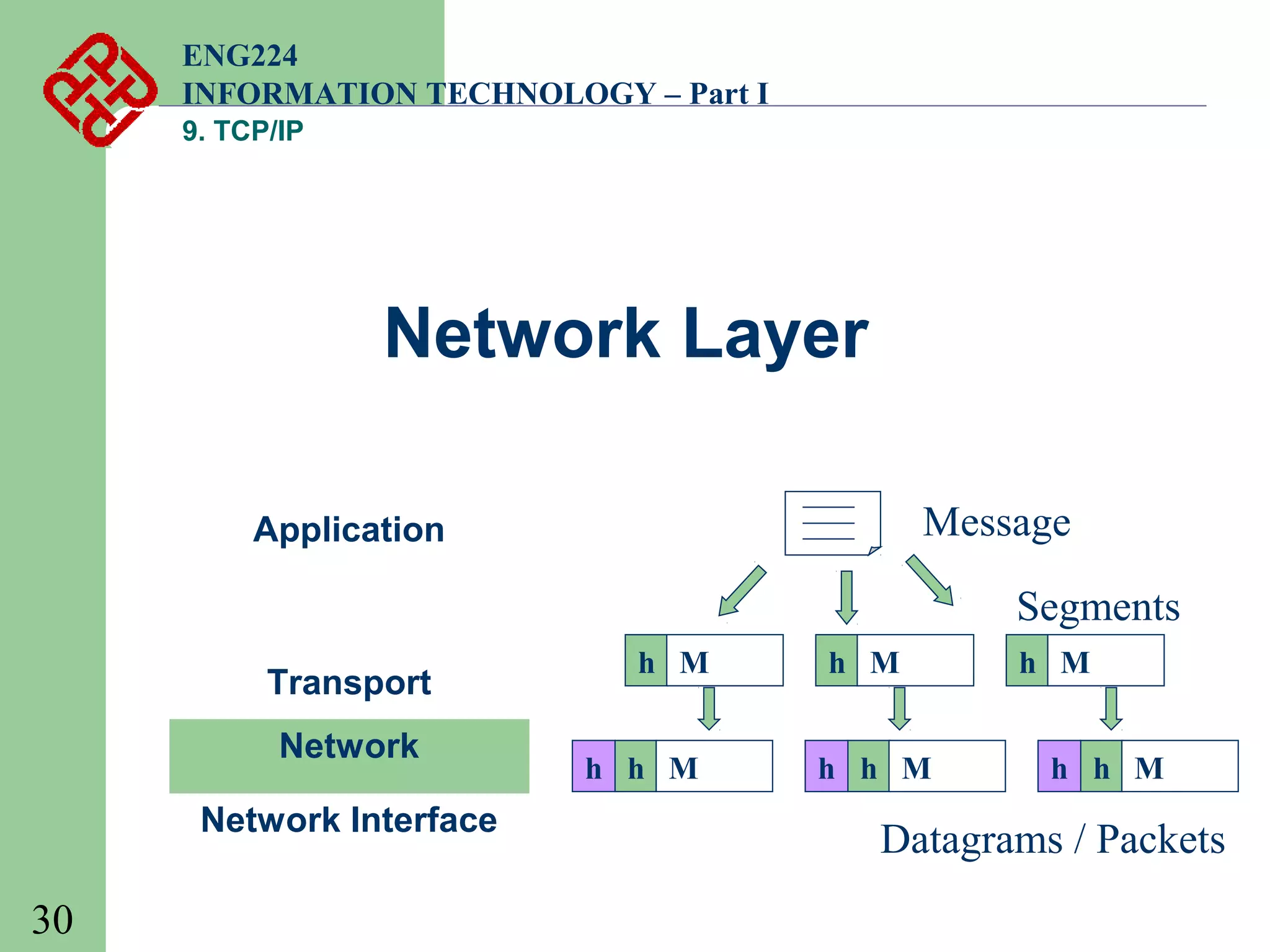
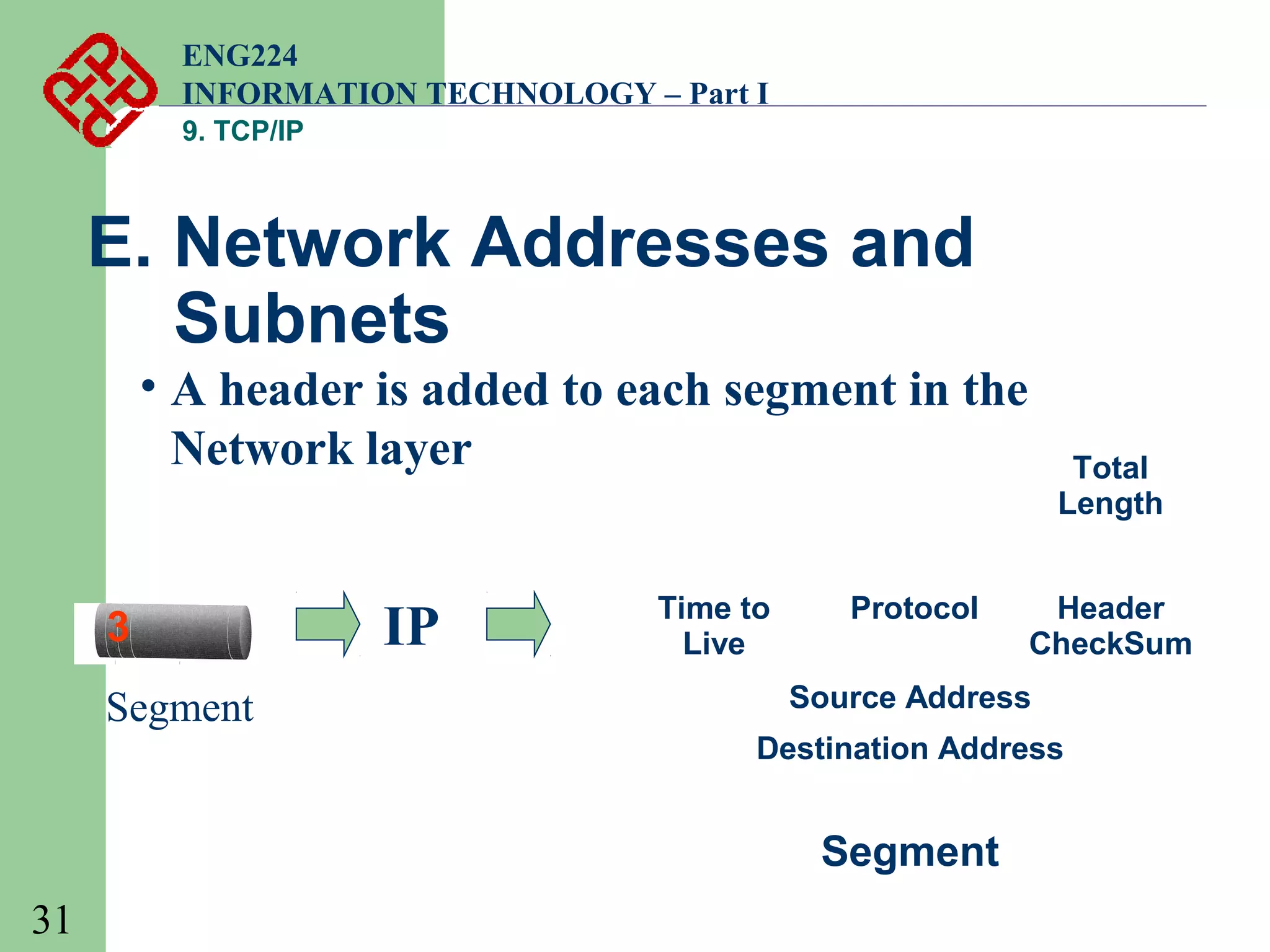
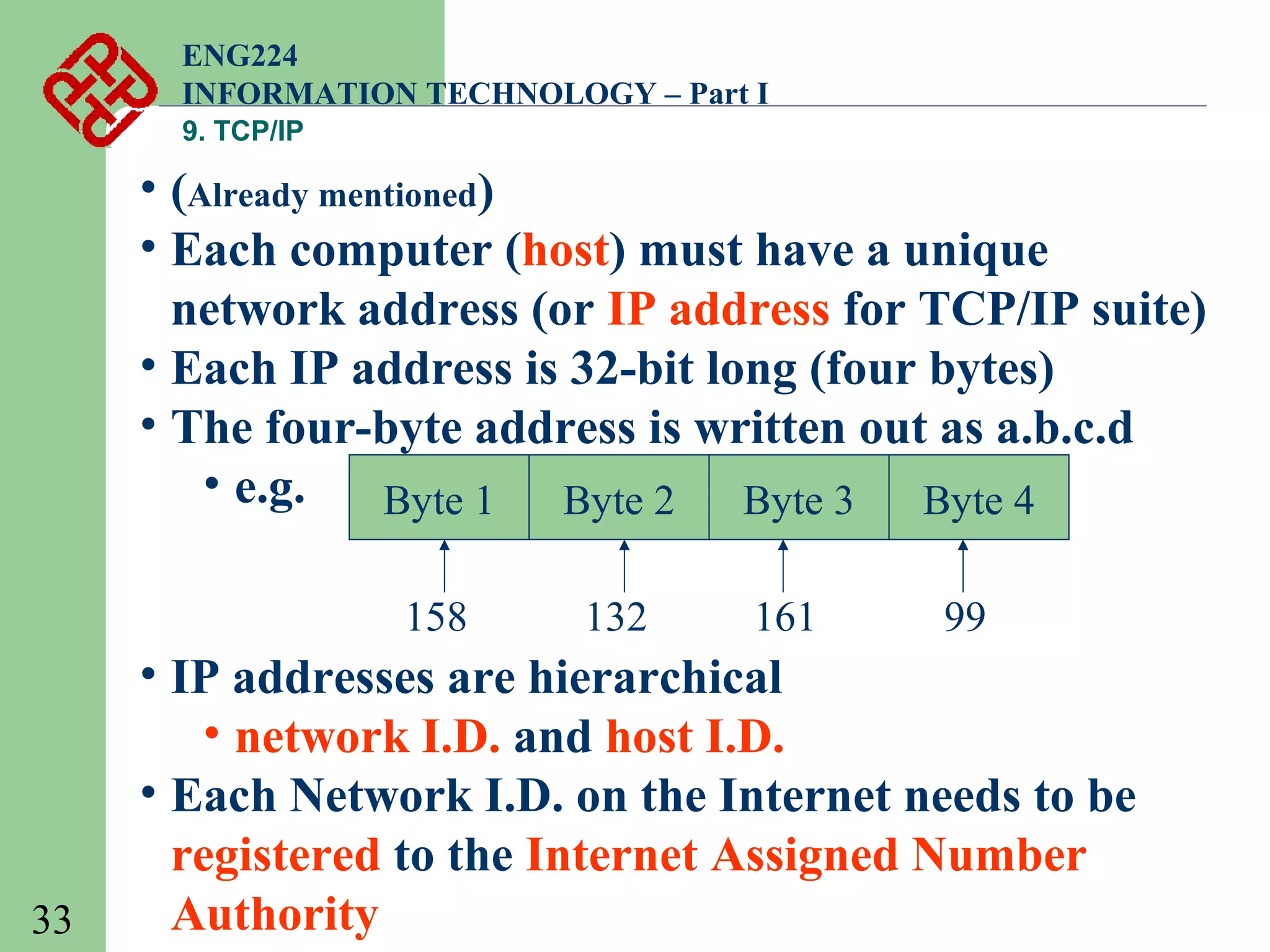
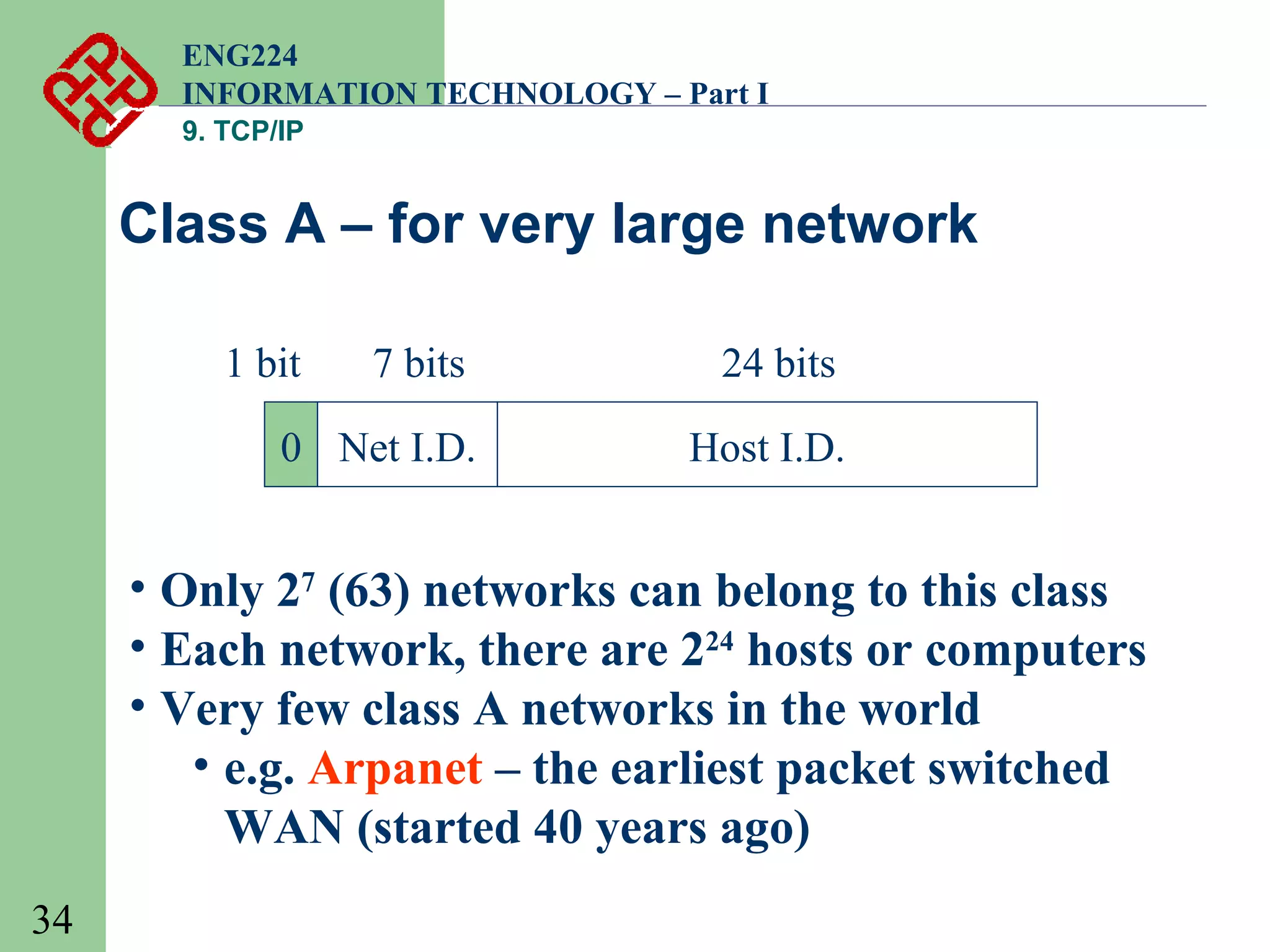
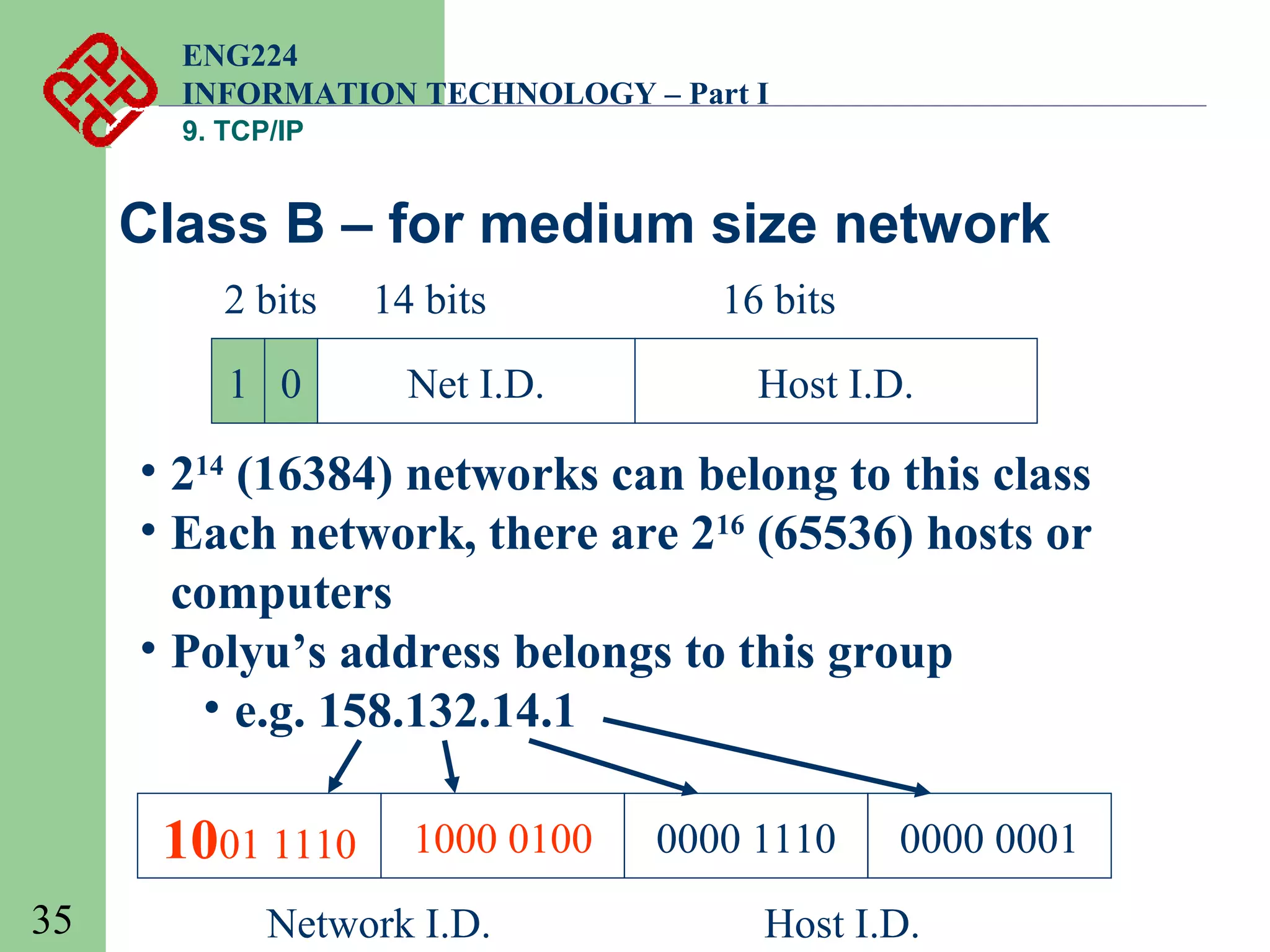
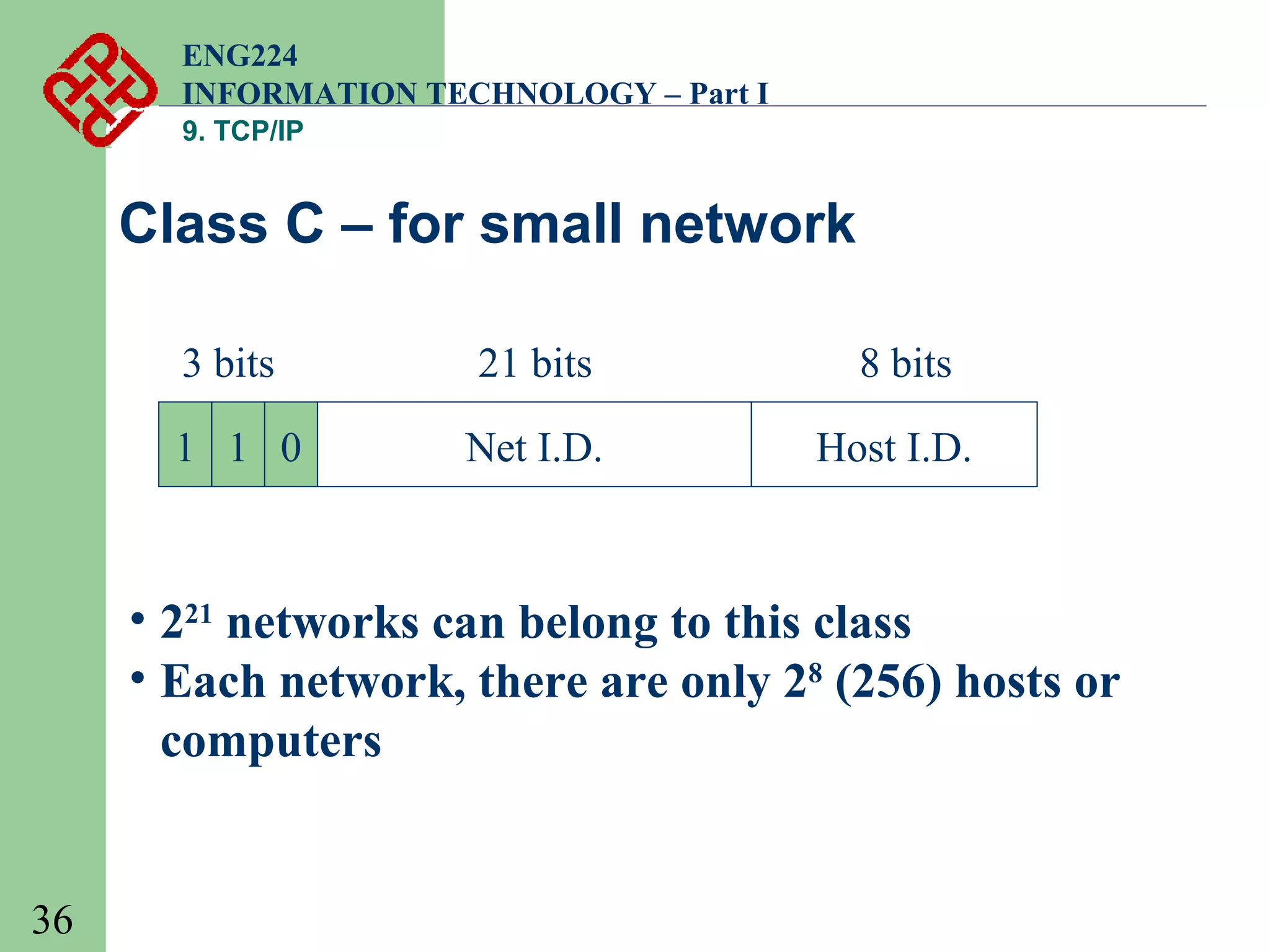
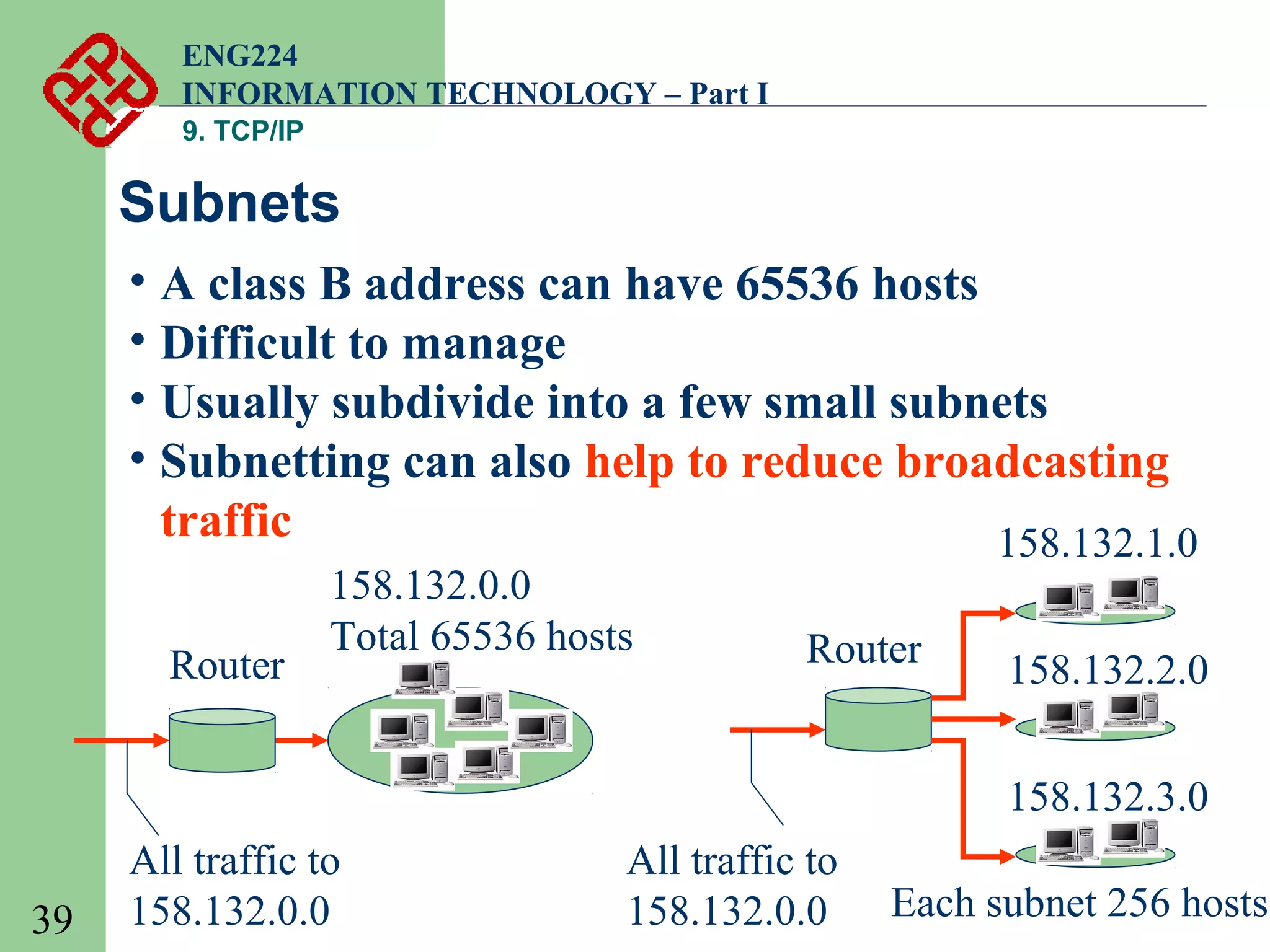
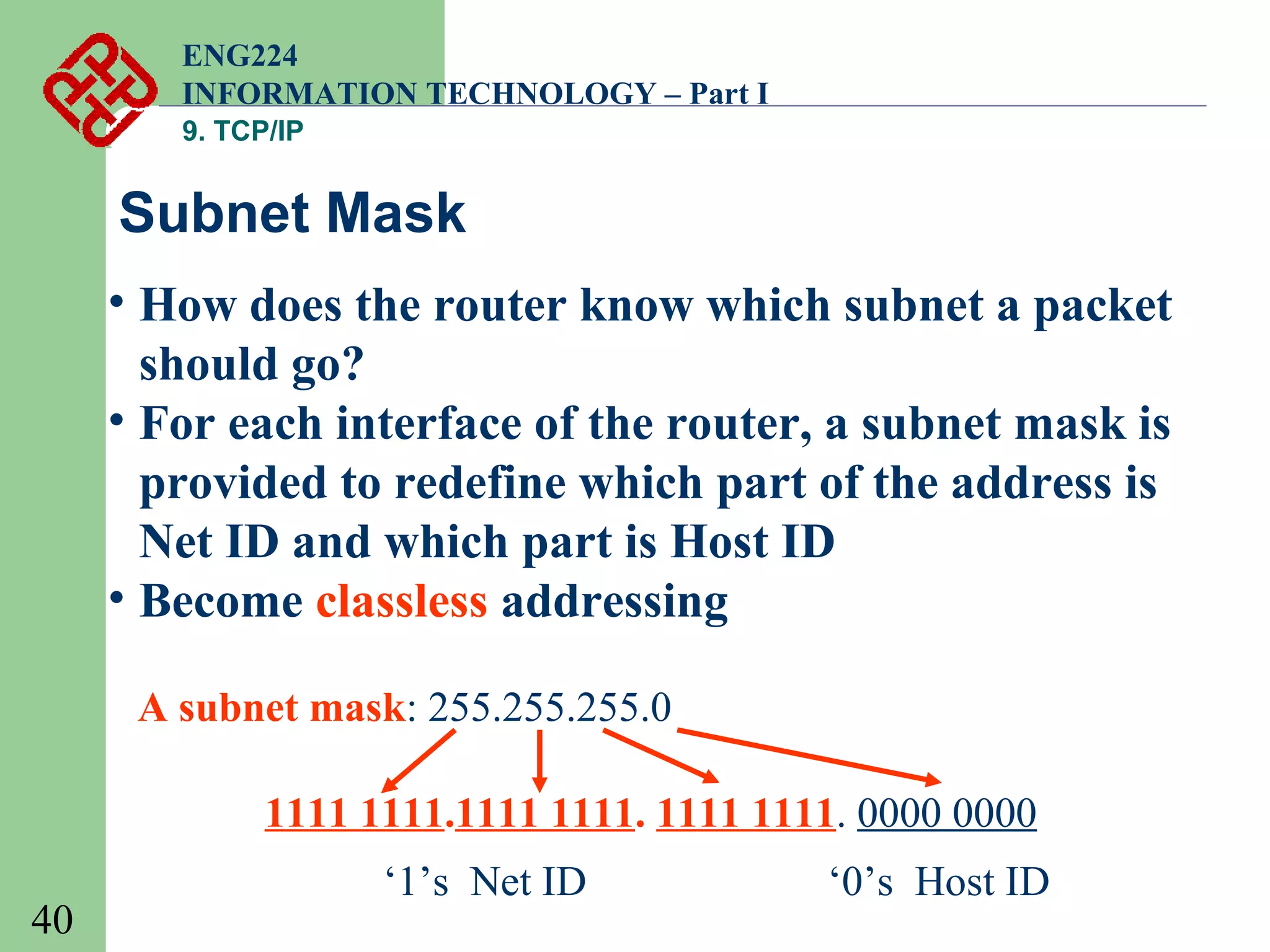
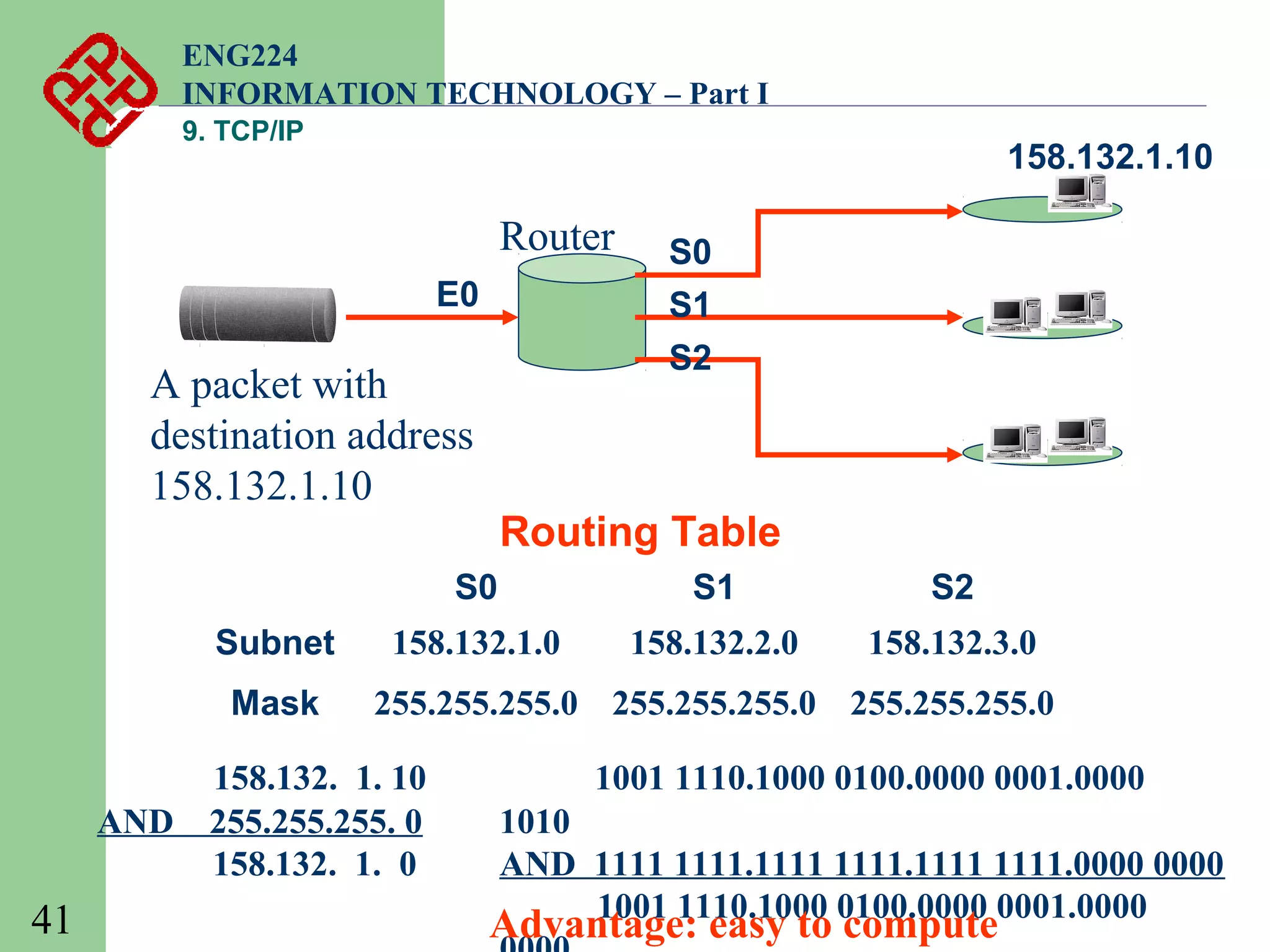
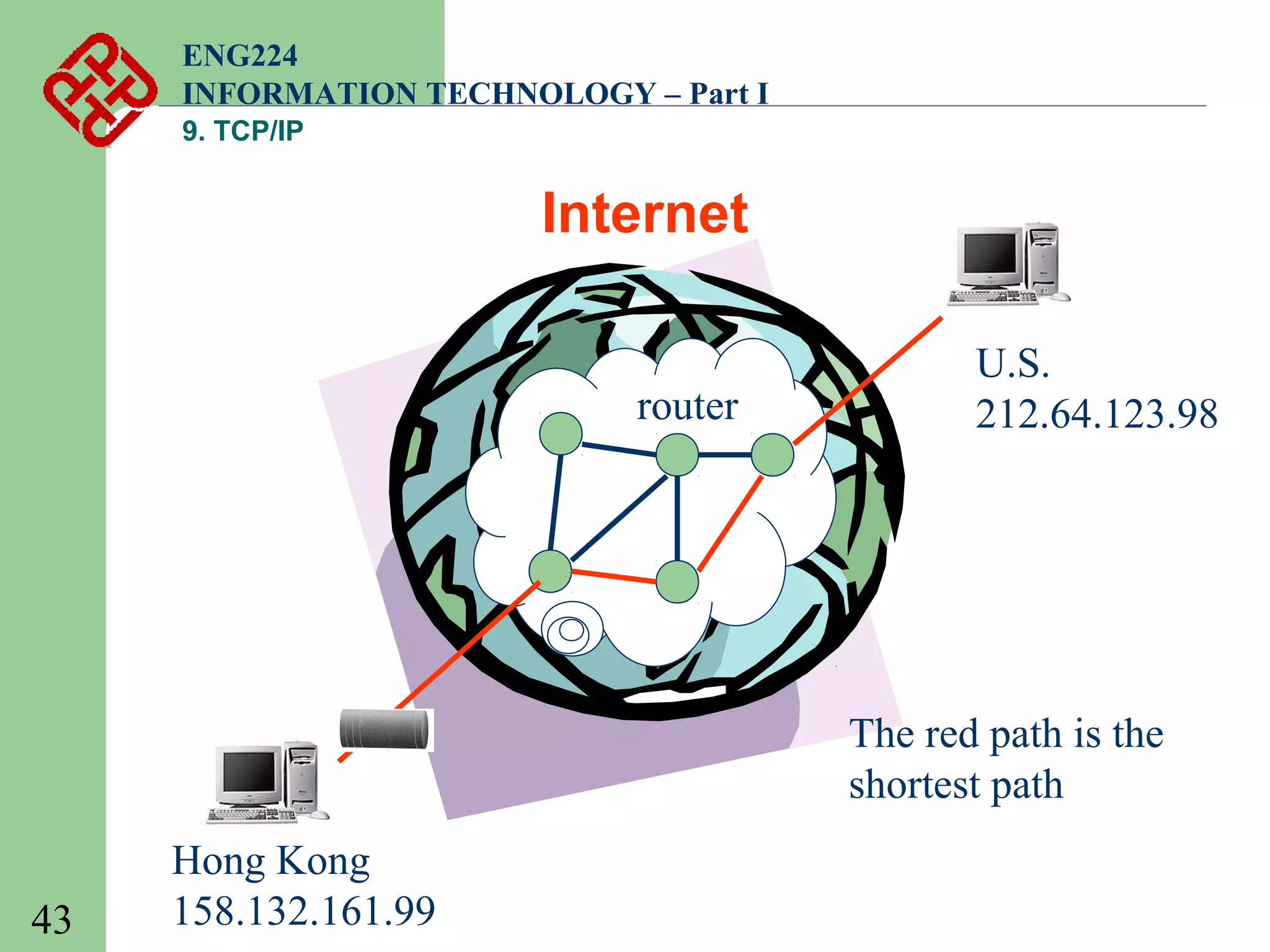
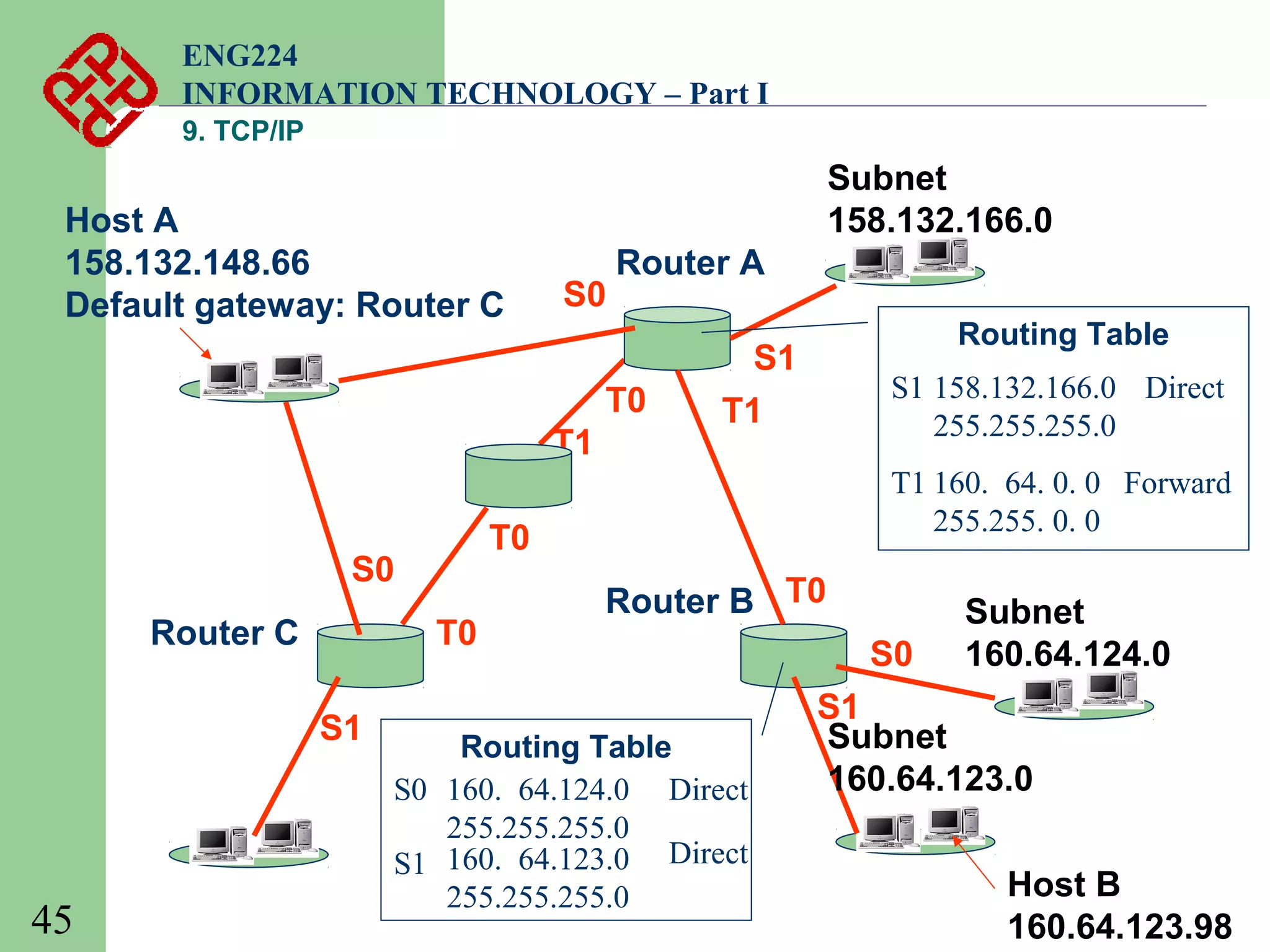
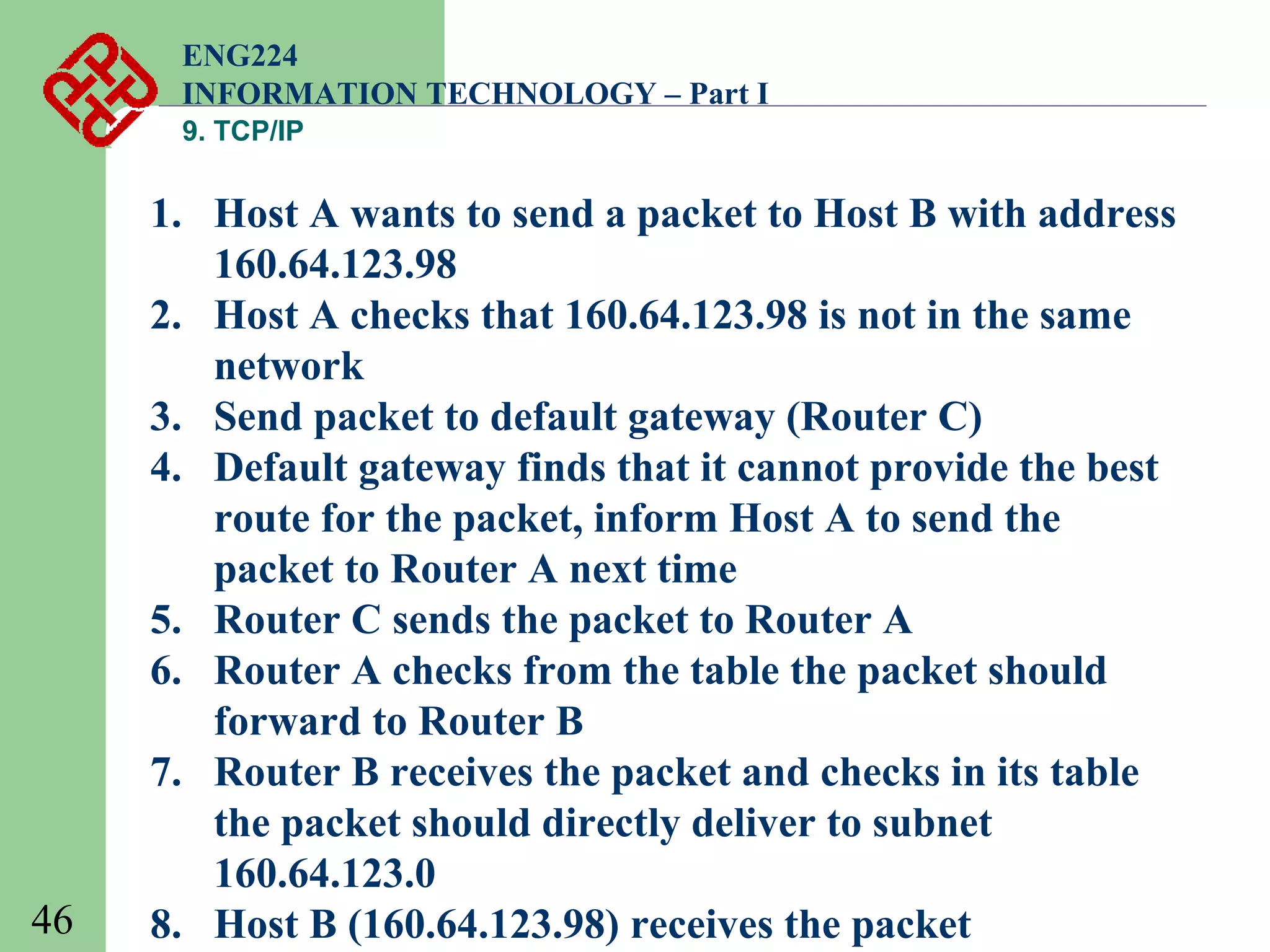
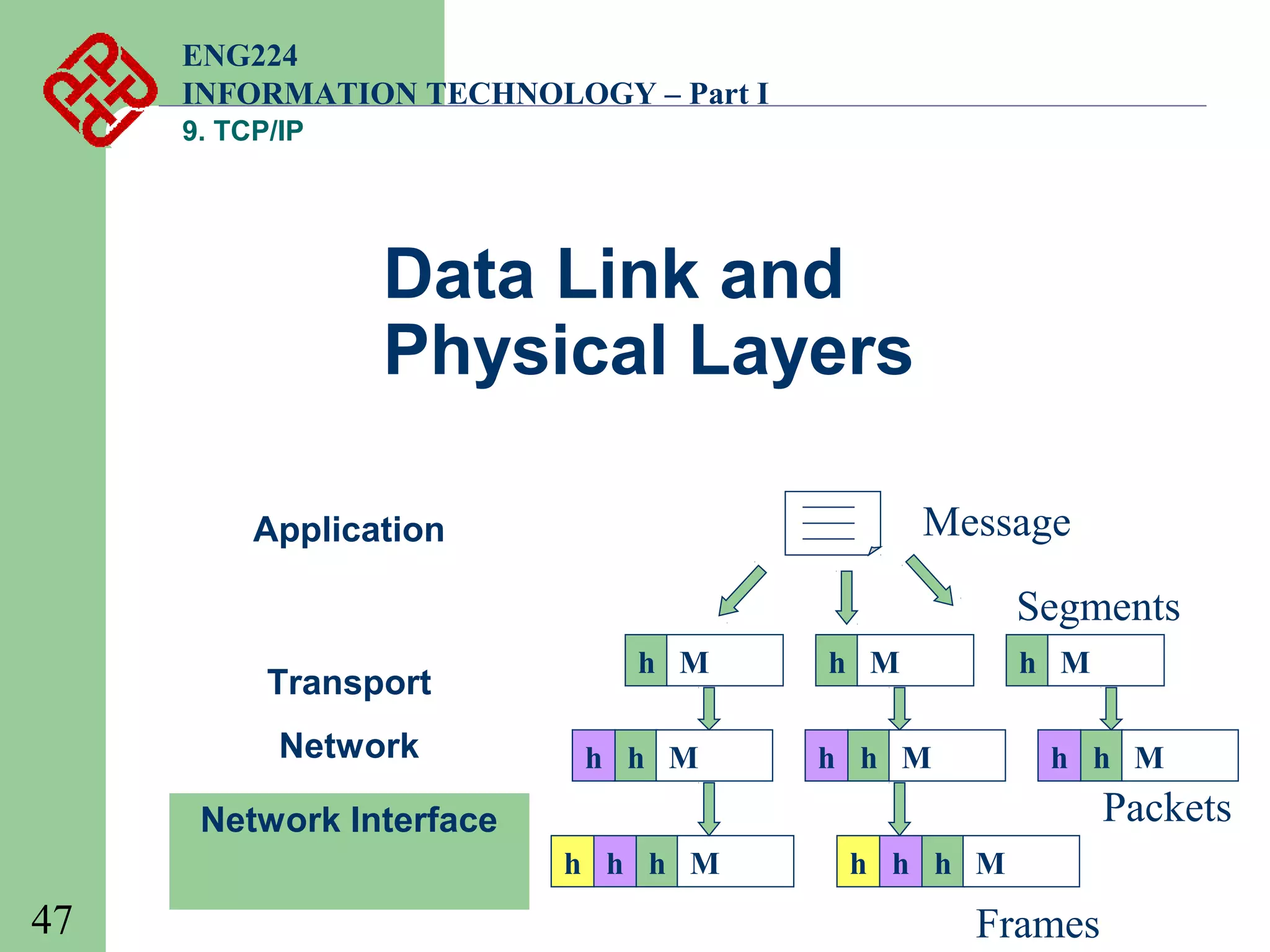
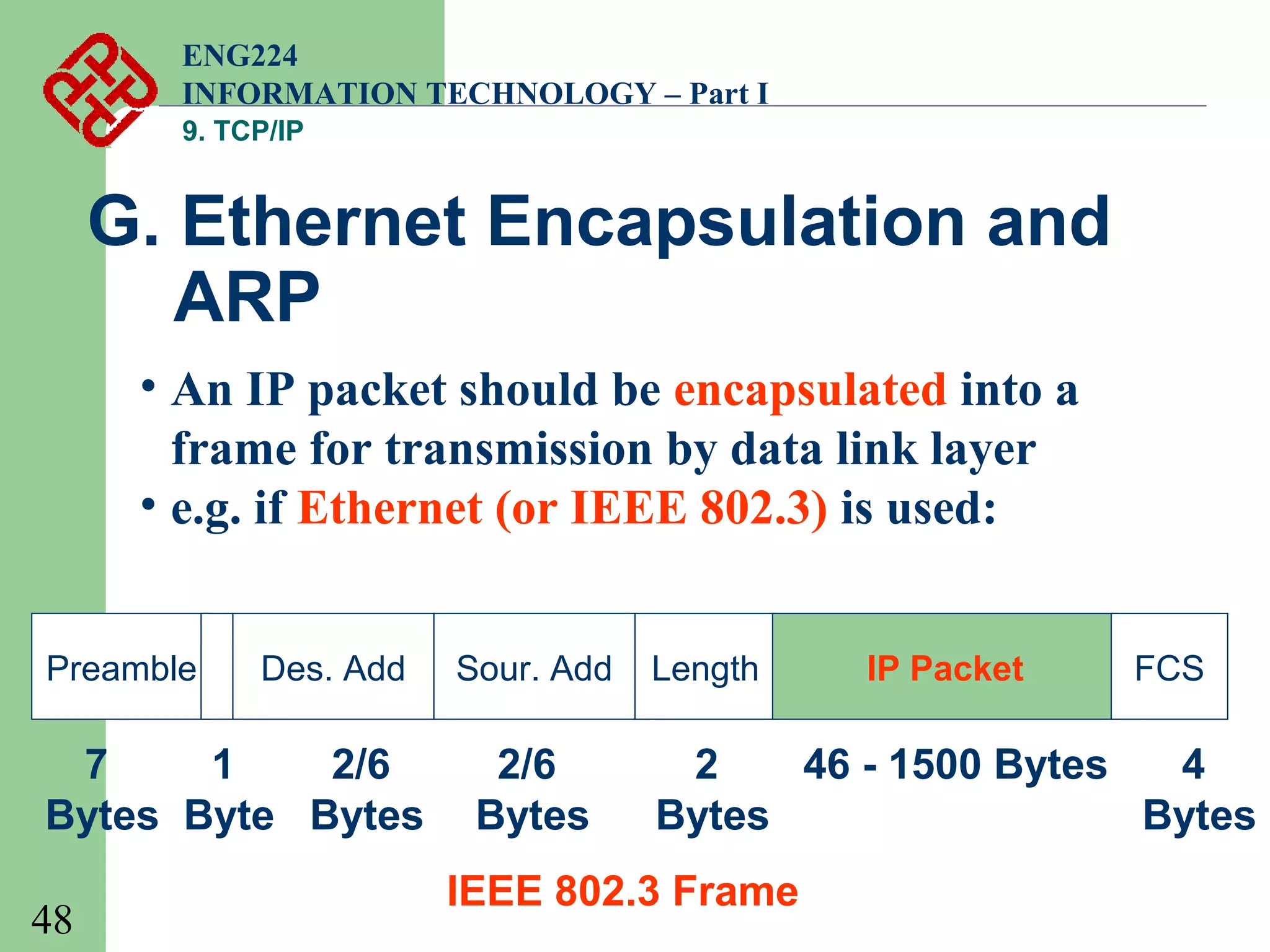
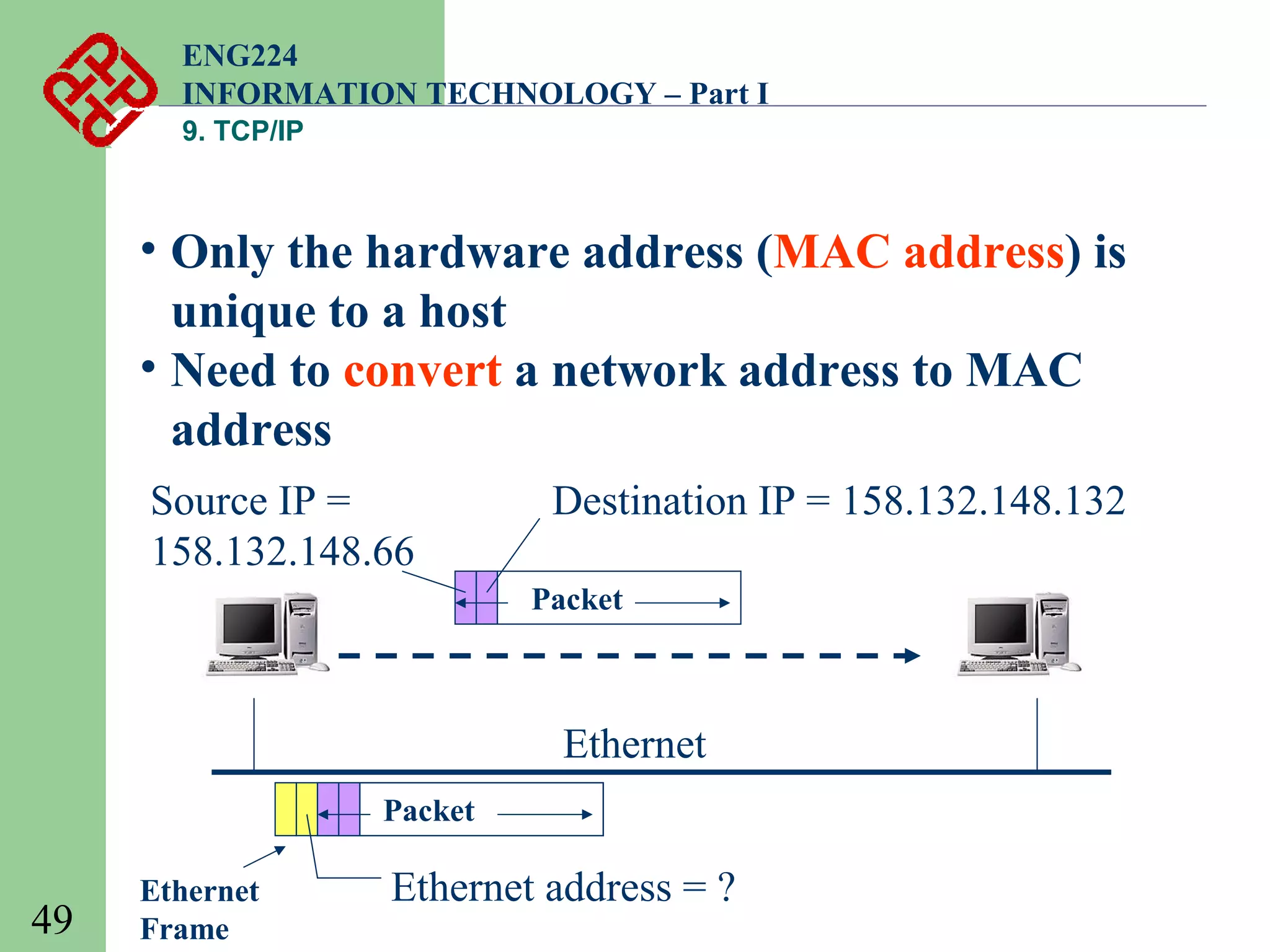
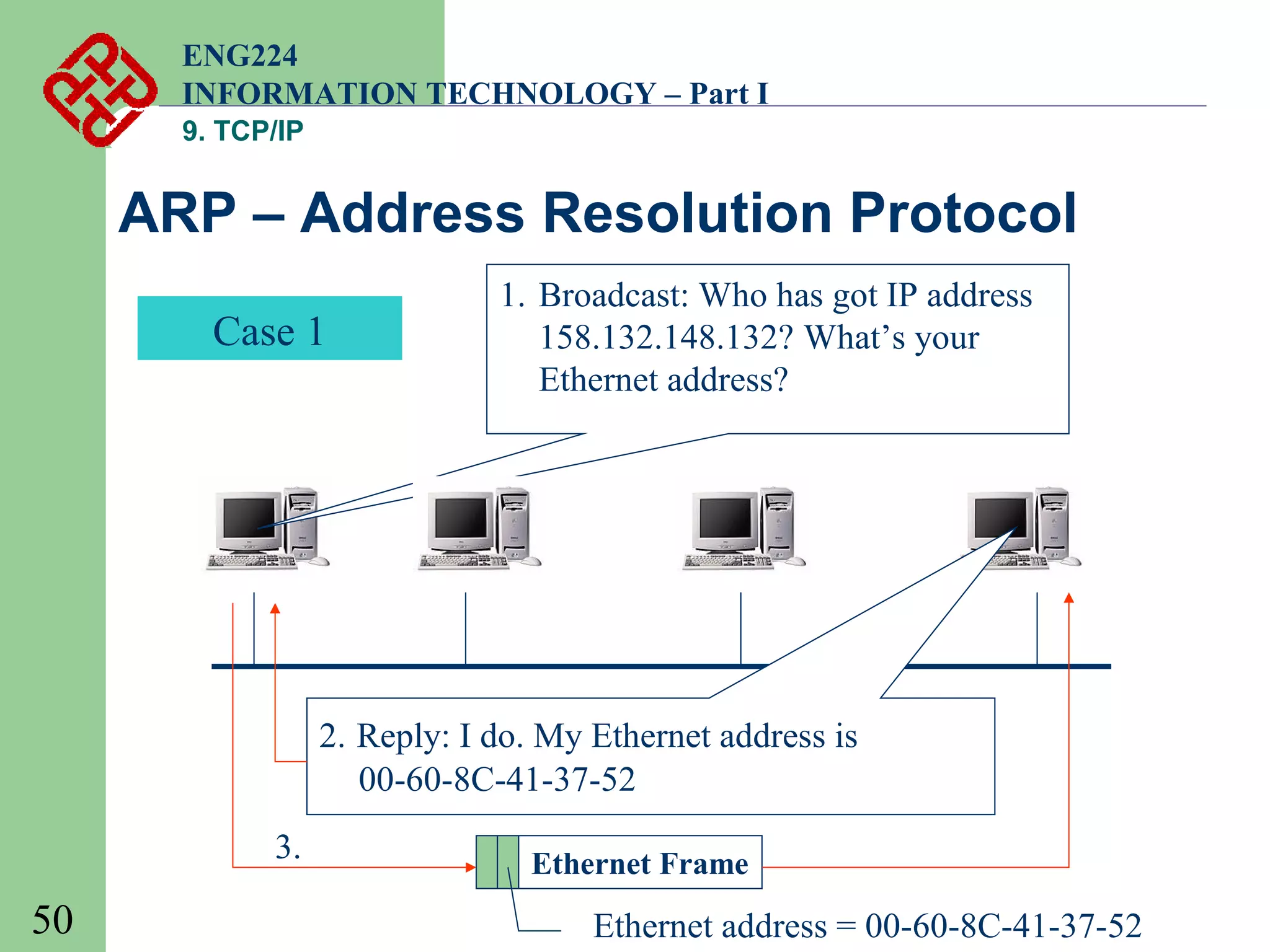
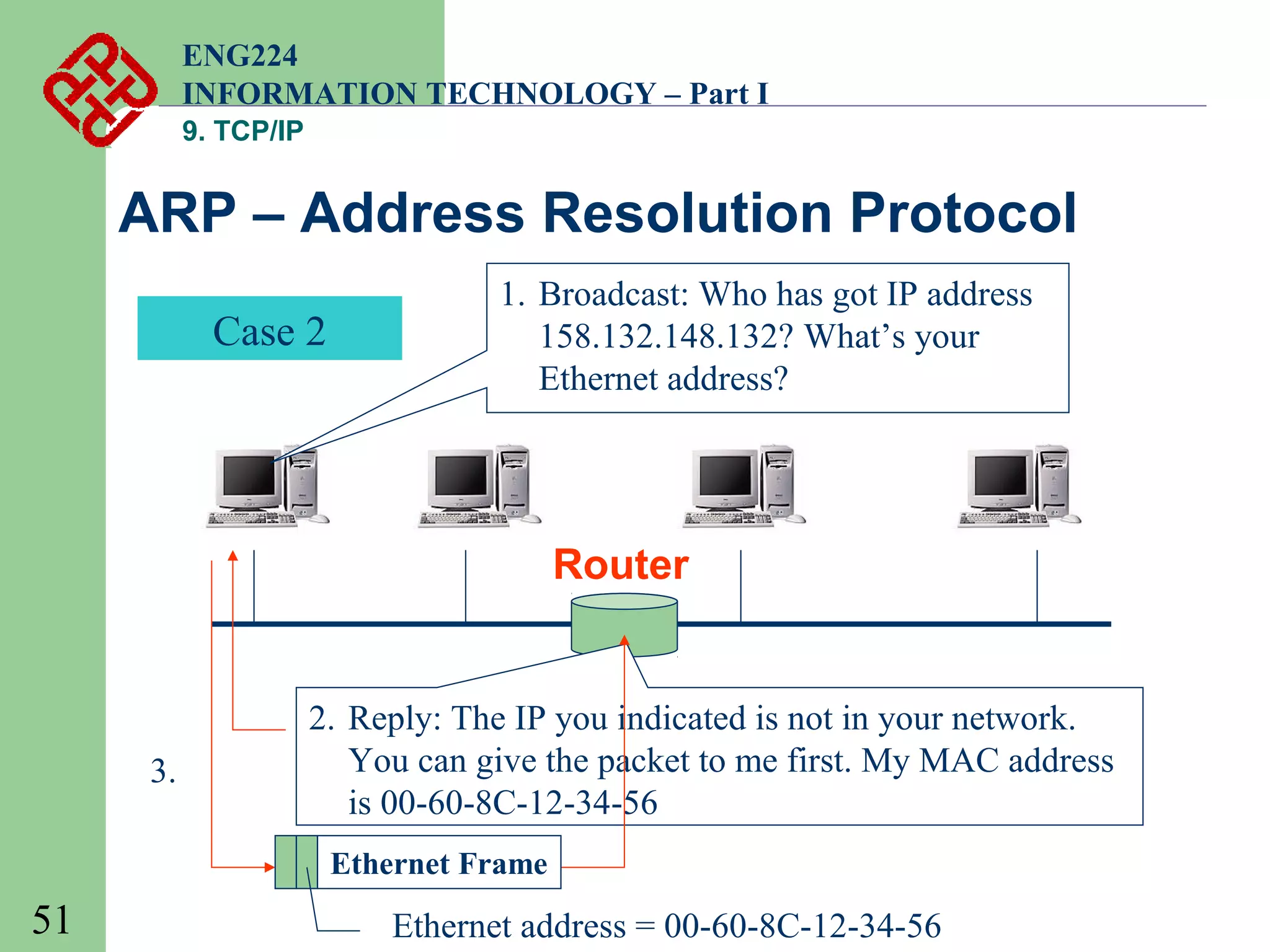
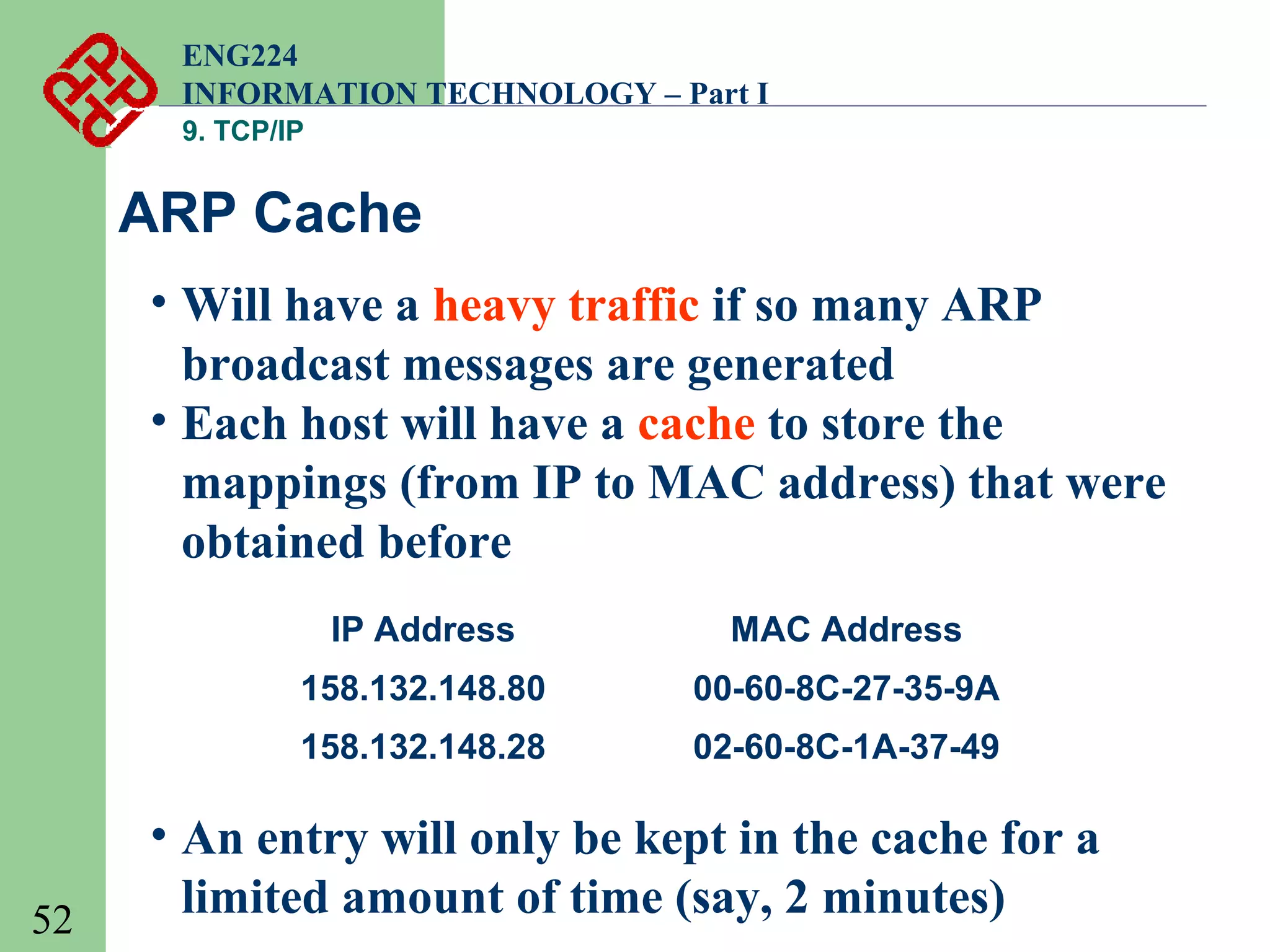
This document provides an overview of the TCP/IP protocol suite. It begins by defining what TCP/IP is, noting that it is a set of protocols that allow cooperating computers to share resources across a network. TCP/IP is made up of the TCP and IP protocols at the transport and network layers respectively. The document then discusses specific protocols at each layer, including application layer protocols like FTP, SMTP, and HTTP, as well as transport layer protocols TCP and UDP. It also covers network layer protocols like IP, ARP, and ICMP. The document concludes by discussing TCP/IP addressing schemes and how networks are divided into subnets.