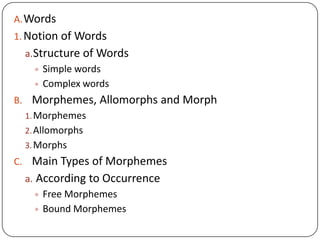
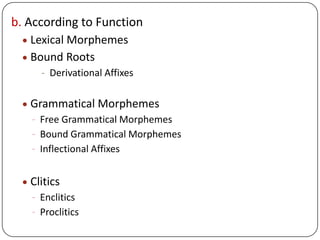
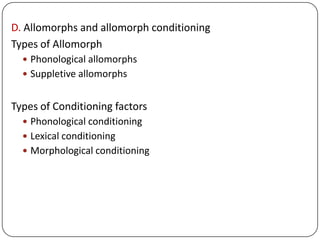
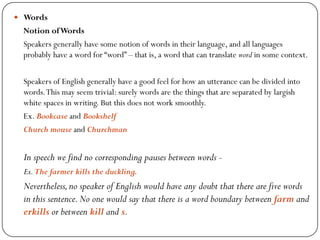
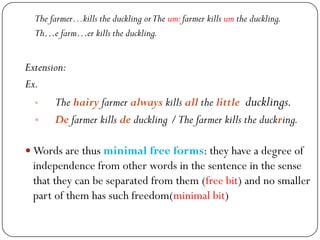
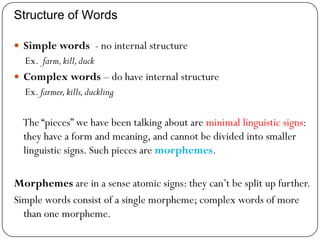
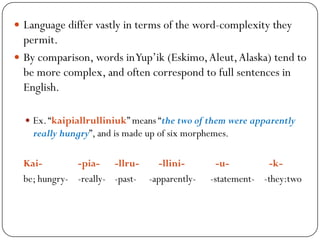
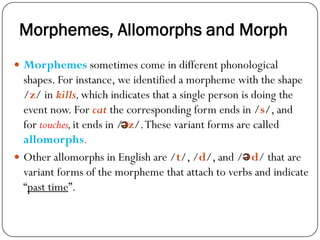
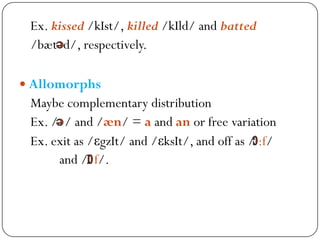
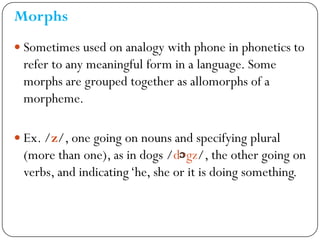
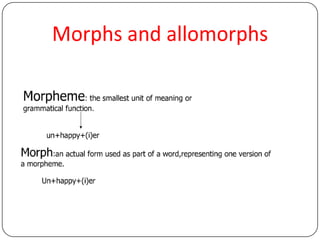
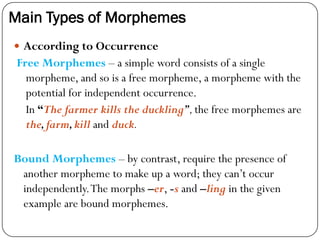
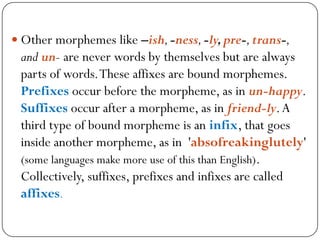
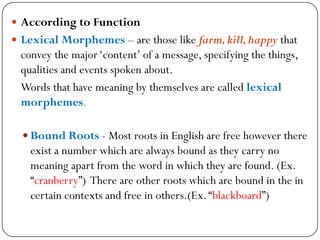
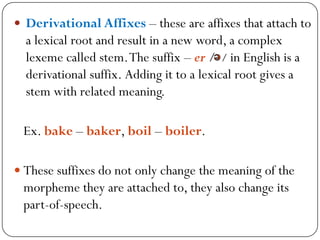
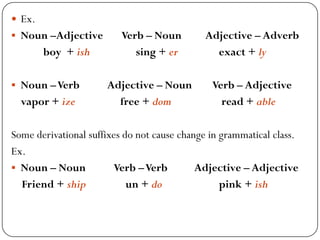
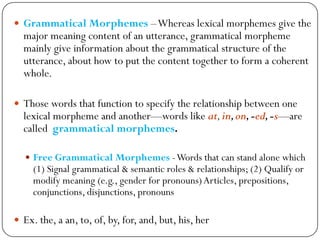
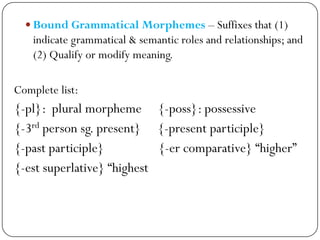
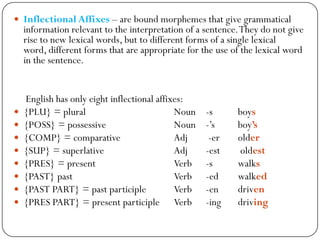
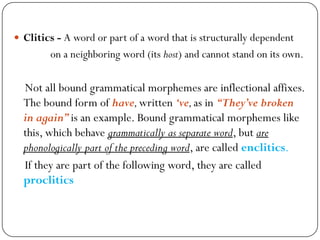
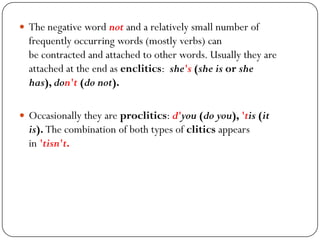
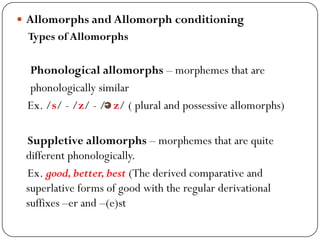
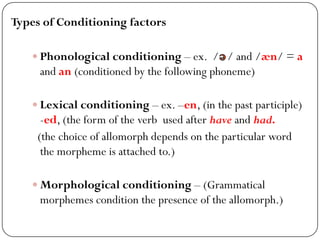
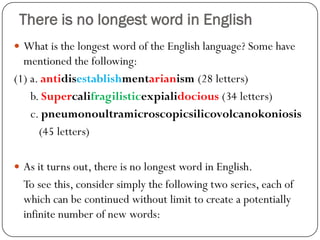
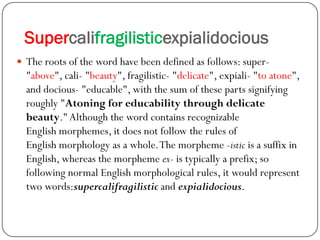
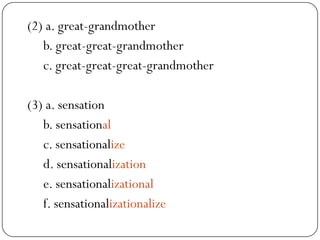
This document discusses the structure of words in morphology. It defines words, morphemes, and different types of morphemes. There are free and bound morphemes. Lexical morphemes convey meaning while grammatical morphemes provide grammatical information. Derivational affixes create new words while inflectional affixes create word forms. Allomorphs are variant forms of morphemes. The structure of words can be analyzed down to the morpheme level. There is no definite longest word in English because new complex words can always be created by combining morphemes.