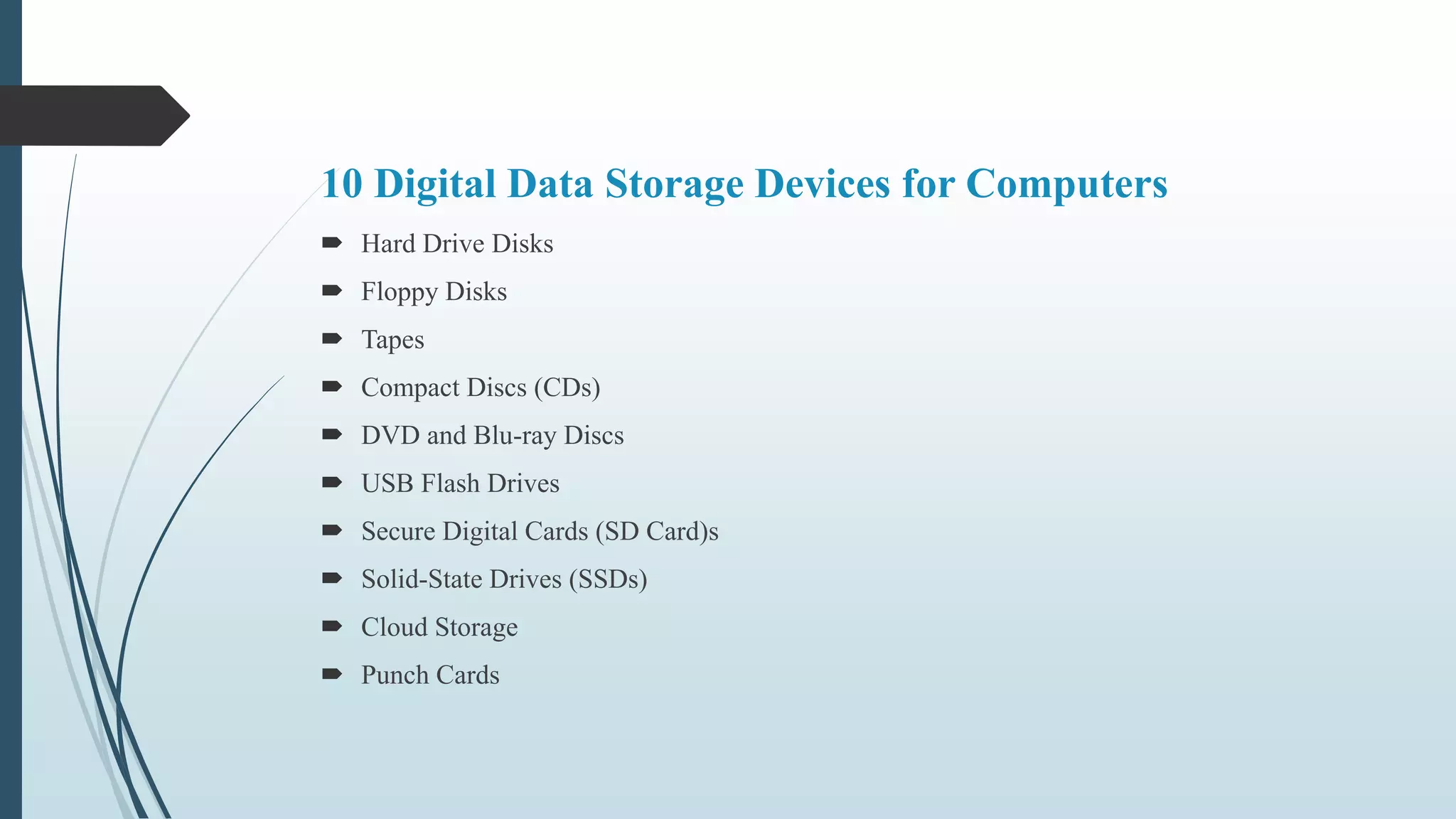
This document discusses different types of computer storage devices. It describes primary storage as the internal memory directly accessible by the CPU, like RAM. Secondary storage is external and not directly accessible, like hard drives and USB drives. Tertiary storage involves robotic functions, like tapes. Common storage devices include magnetic devices like hard drives and floppy disks, optical devices like CDs and DVDs, flash memory devices like USB drives and SD cards, and online cloud storage. Characteristics of these devices include volatile memory, read/write capabilities, increasing capacity and accessibility.