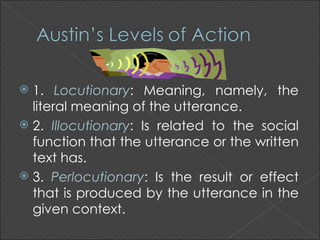
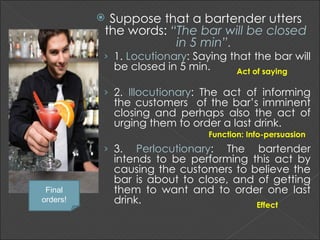
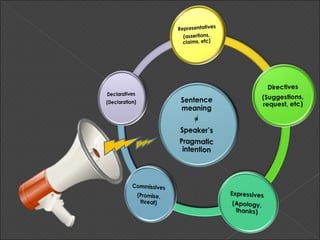
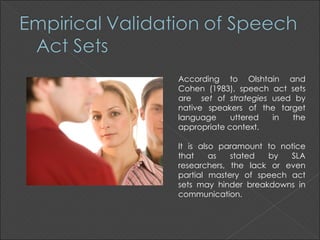
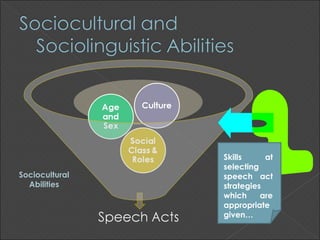
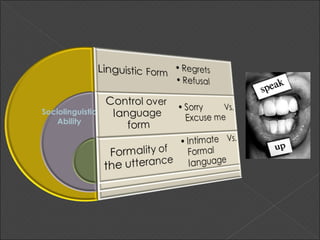
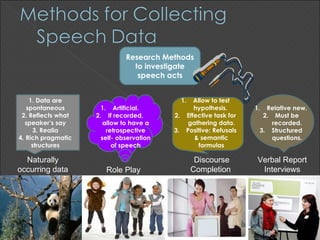
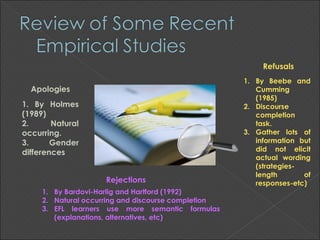
This document discusses speech acts, which are functional units of communication. It defines locutionary, illocutionary, and perlocutionary aspects of speech acts. It also discusses research methods used to study speech acts, including role plays, discourse completion tasks, and interviews. Finally, it notes the importance of teaching speech acts to language learners and recommends techniques like modeling dialogues, role plays, and feedback.