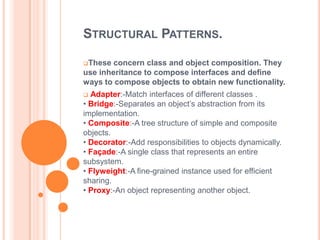
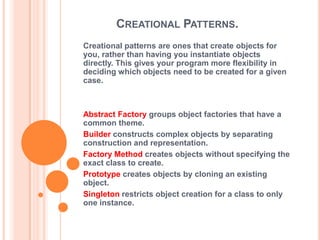
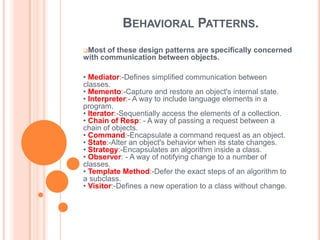
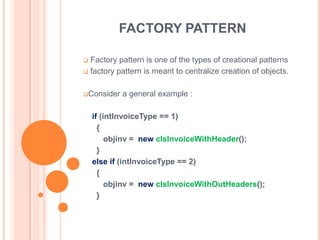
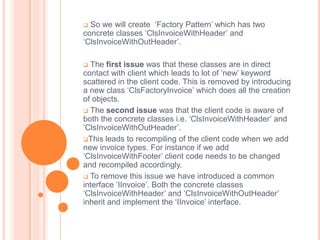
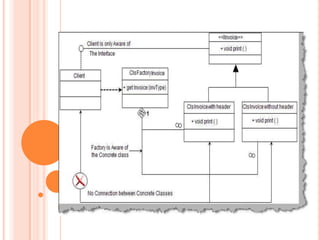
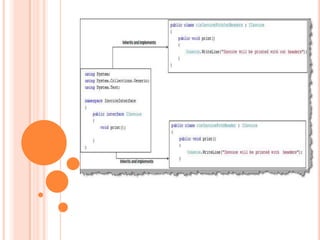
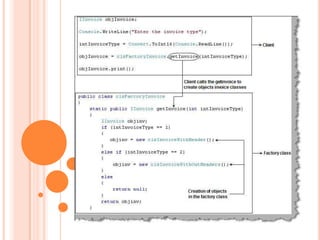
This document discusses software design and the need for design patterns. It covers the three phases of software design: analysis, design, and implementation. It then discusses what design patterns are, providing the definition that they are standard solutions to common programming problems. The document outlines the three main categories of design patterns: structural, creational, and behavioral. It provides examples like the factory pattern, explaining how it works to reduce dependencies and improve flexibility. In summary, the document introduces software design processes and argues that using design patterns provides benefits like improved code reuse and developer communication.