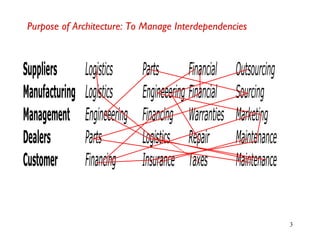
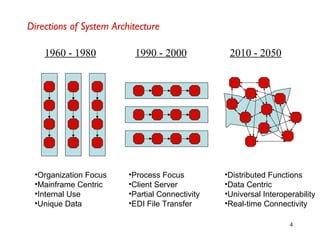
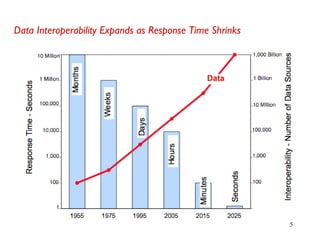
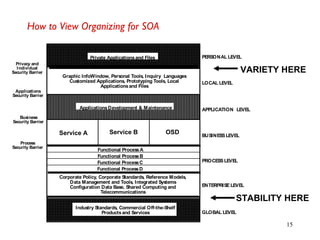
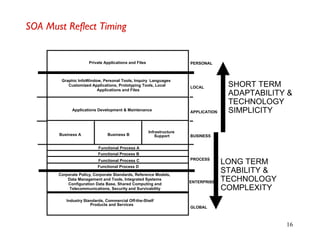
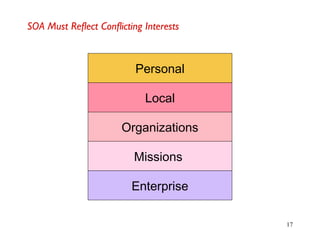
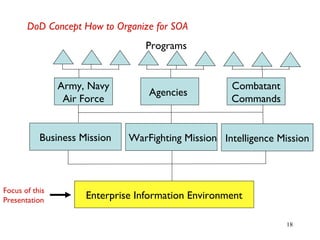
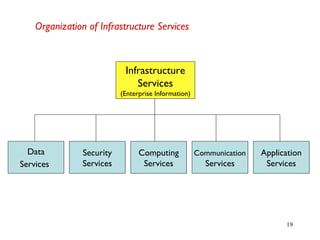
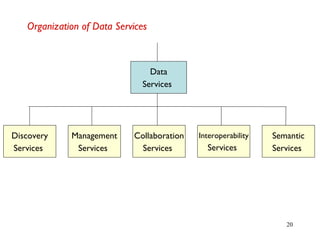
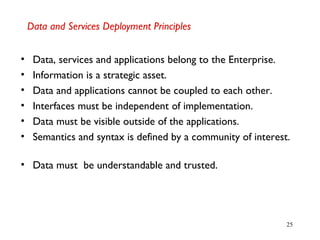
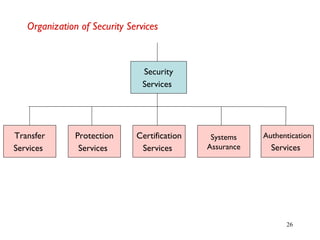
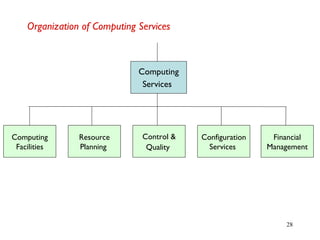
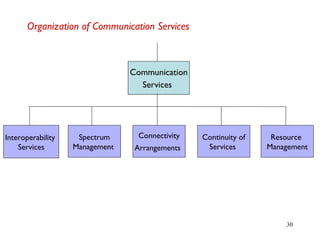
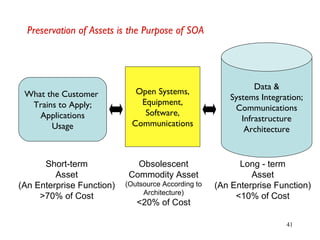
A service oriented architecture (SOA) organizes software into business services that are network accessible and executable. Key characteristics include quality of service specifications, discoverable services and data catalogs, and use of industry standards. A SOA breaks up monolithic systems into reusable components called services that can be more easily maintained and replaced. Implementing a SOA requires organizing infrastructure, data, security, computing, communication, and application services to maximize reuse across the enterprise.