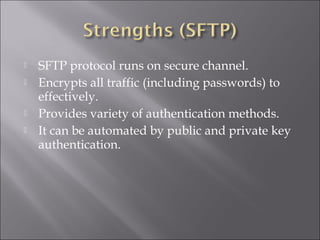
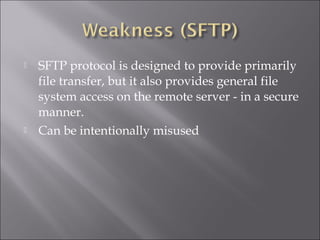
FTP refers to the File Transfer Protocol, which allows transfer of files between computers over the Internet. A user must log into both the source and destination hosts to transfer a file. Common FTP methods include manual transfer, email transfer, HTTP transfer, and anonymous/WU-FTP. More secure options are SFTP and SCP, which encrypt traffic and support authentication.