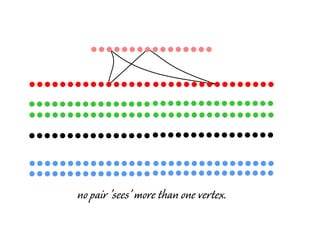
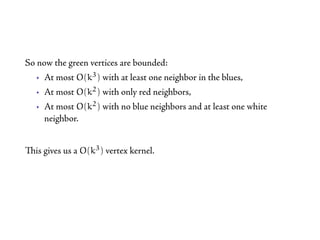
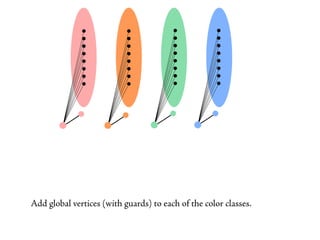
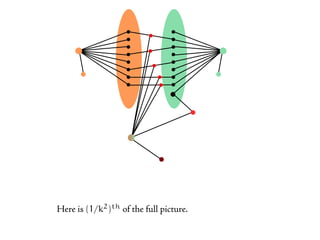
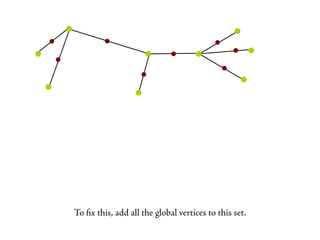
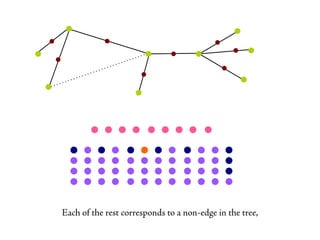
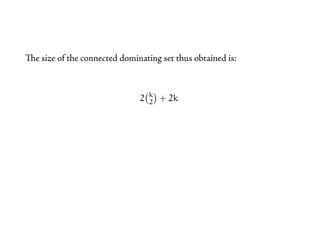
The document discusses connected dominating sets and short cycles. It begins by explaining that excluding longer cycles makes related problems easier to solve. Specifically, it shows that on graphs with girth at least five, high degree vertices must be in any minimum dominating set. However, this does not hold for connected dominating sets, since connectivity must also be maintained. It then describes how to obtain fixed-parameter tractable algorithms for connected dominating set problems by guessing the minimum dominating set and extending it. It also shows that these problems do not admit polynomial kernels by providing a reduction from Fair Connected Colors, which is W-hard.