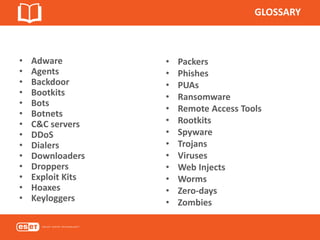
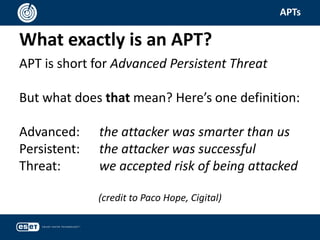
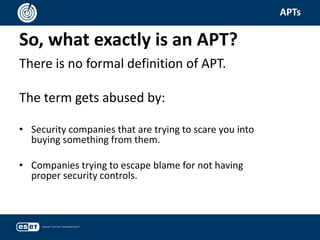
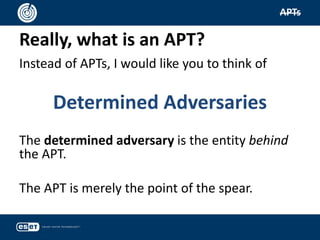
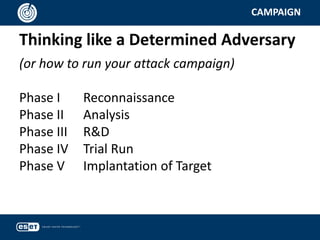
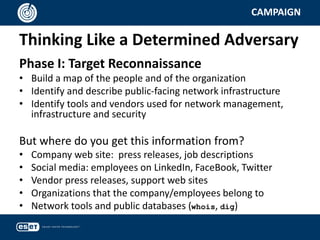
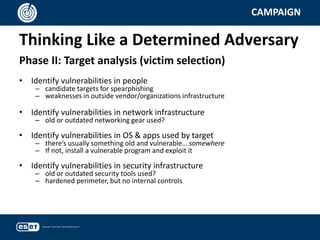
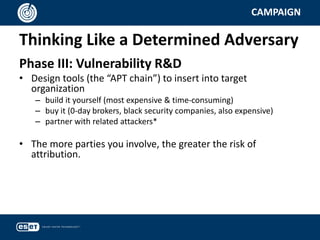
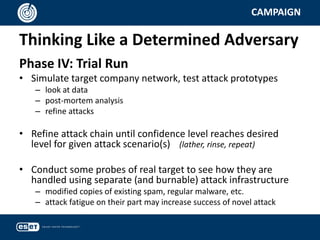
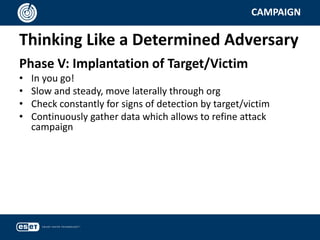
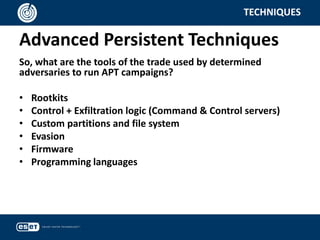
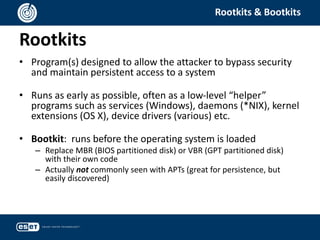
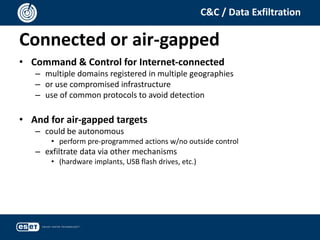
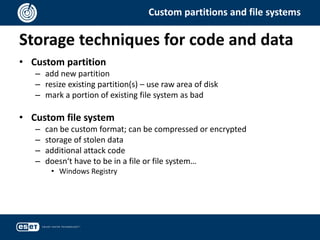
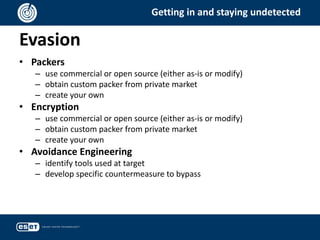
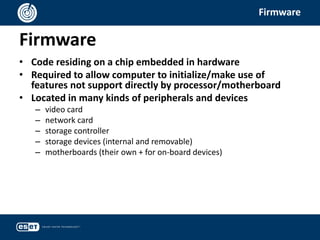
This document summarizes a presentation on Advanced Persistent Threats (APTs) given by Aryeh Goretsky, a Distinguished Researcher at ESET. The presentation defines APTs as determined adversaries who conduct cyber attacks in phases, including reconnaissance of targets, analysis of vulnerabilities, development of tools to exploit vulnerabilities, trial runs of attacks, and implantation of attacks on targets. It discusses techniques used in APTs, such as rootkits, command and control servers, custom file systems and partitions, evasion methods, firmware attacks, and programming languages. The presentation aims to explain how to think like a determined adversary conducting a cyber attack campaign.