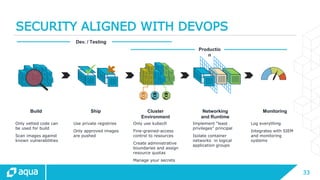
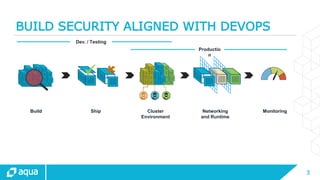
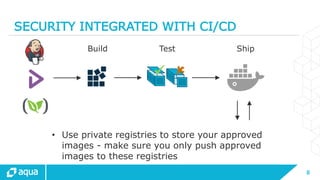
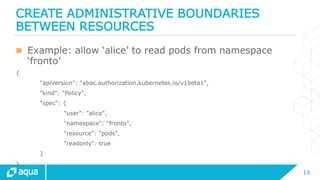
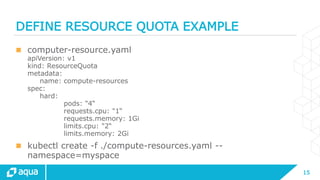
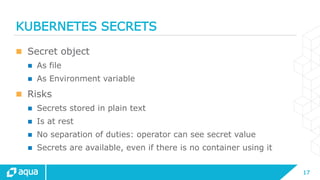
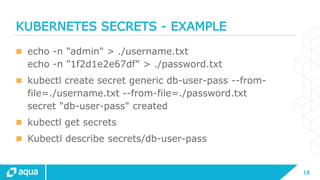
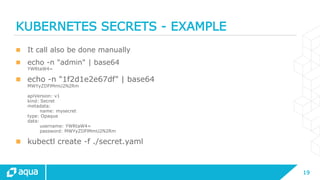
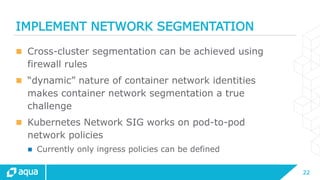
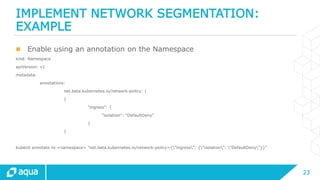
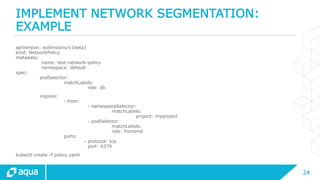
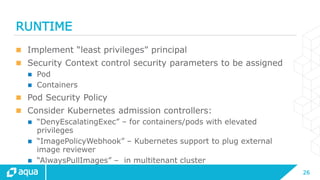
This document provides best practices for securing a Kubernetes deployment. It recommends integrating security into the CI/CD pipeline by only using vetted code for builds, scanning images for vulnerabilities, and using private registries to store and push only approved images. It also suggests limiting direct access to Kubernetes nodes, implementing fine-grained role-based access control and quotas, securely managing secrets, implementing network segmentation and "least privilege" controls. Finally, it stresses the importance of logging all activity and integrating logs with monitoring systems for visibility.




![30
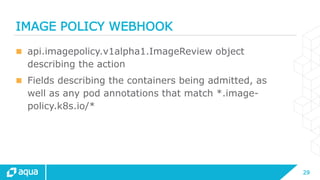
IMAGE POLICY WEBHOOK: EXAMPLE
{
"apiVersion":"imagepolicy.k8s.io/v1alpha1",
"kind":"ImageReview",
"spec":{
"containers":[
{
"image":"myrepo/myimage:v1“
},
{
"image":"myrepo/myimage@sha256:beb6bd6a68f114c1dc2ea4b28db81bdf91de202a9014972bec5e4d9171d
90ed“
}
],
"annotations":[
"mycluster.image-policy.k8s.io/ticket-1234": "break-glass“
],
"namespace":"mynamespace“
}
}](https://image.slidesharecdn.com/securitybestpracticesforkubernetesdeployment-cleanforupload-170427140006/85/Security-best-practices-for-kubernetes-deployment-30-320.jpg)