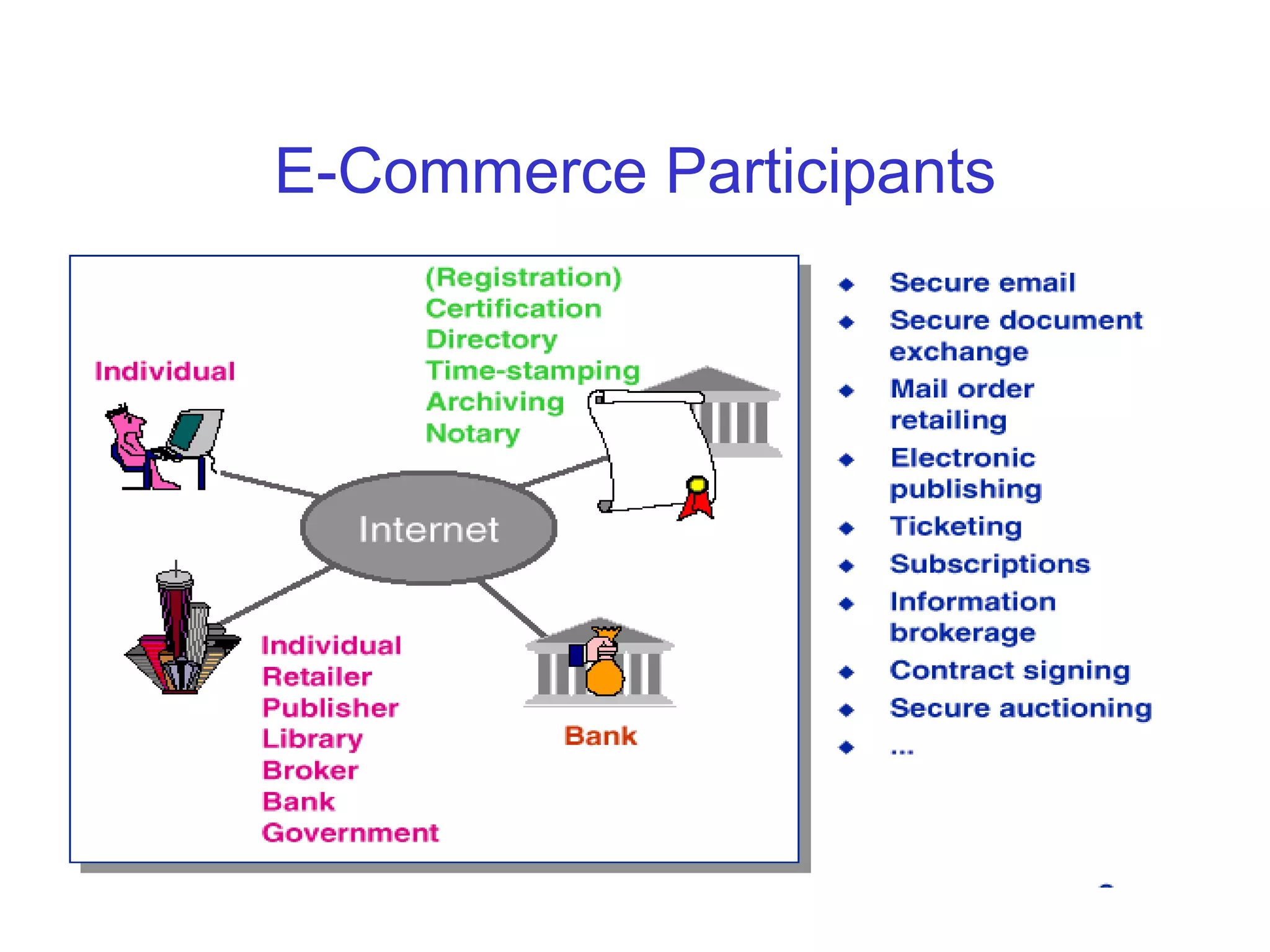
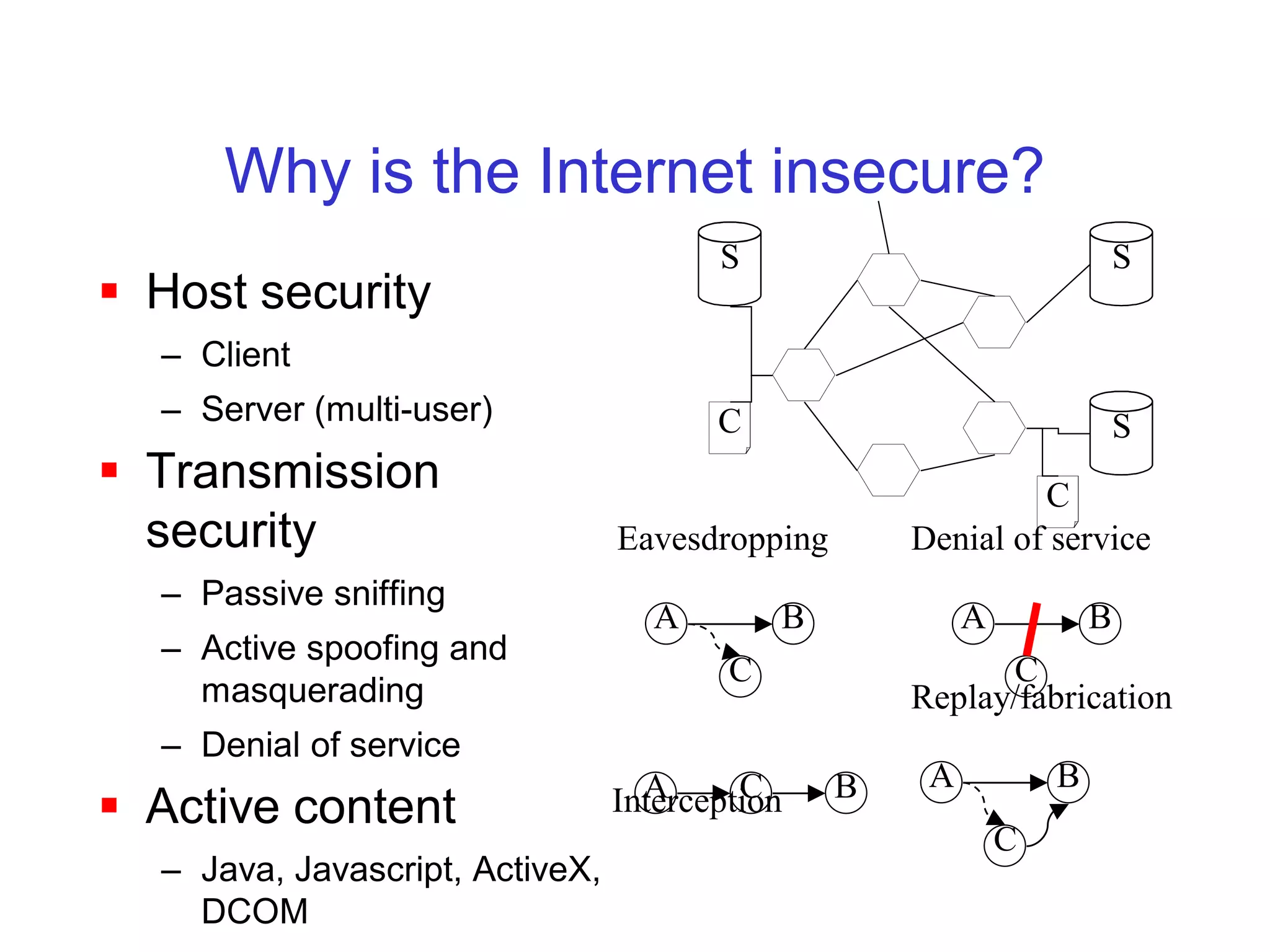
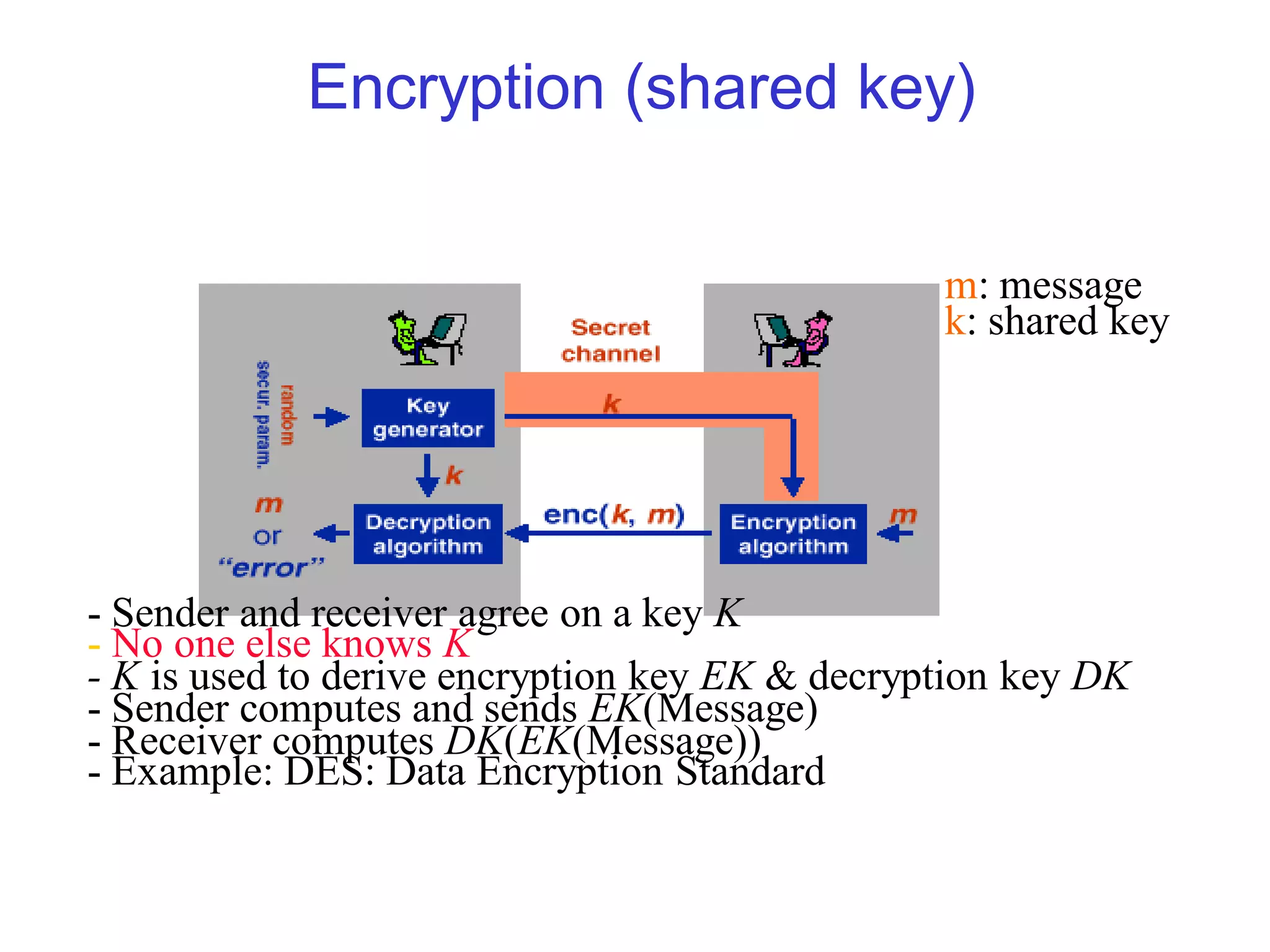
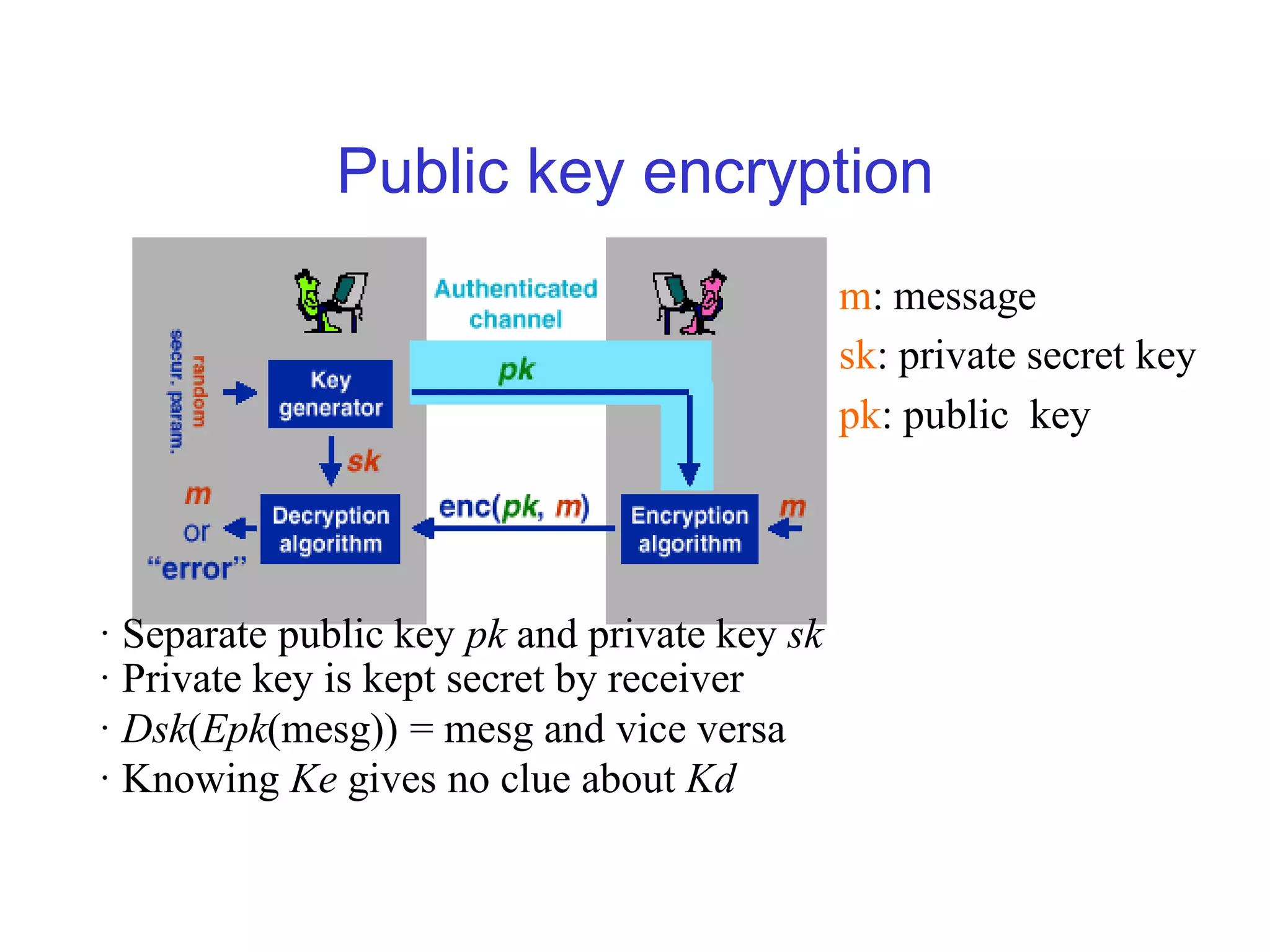
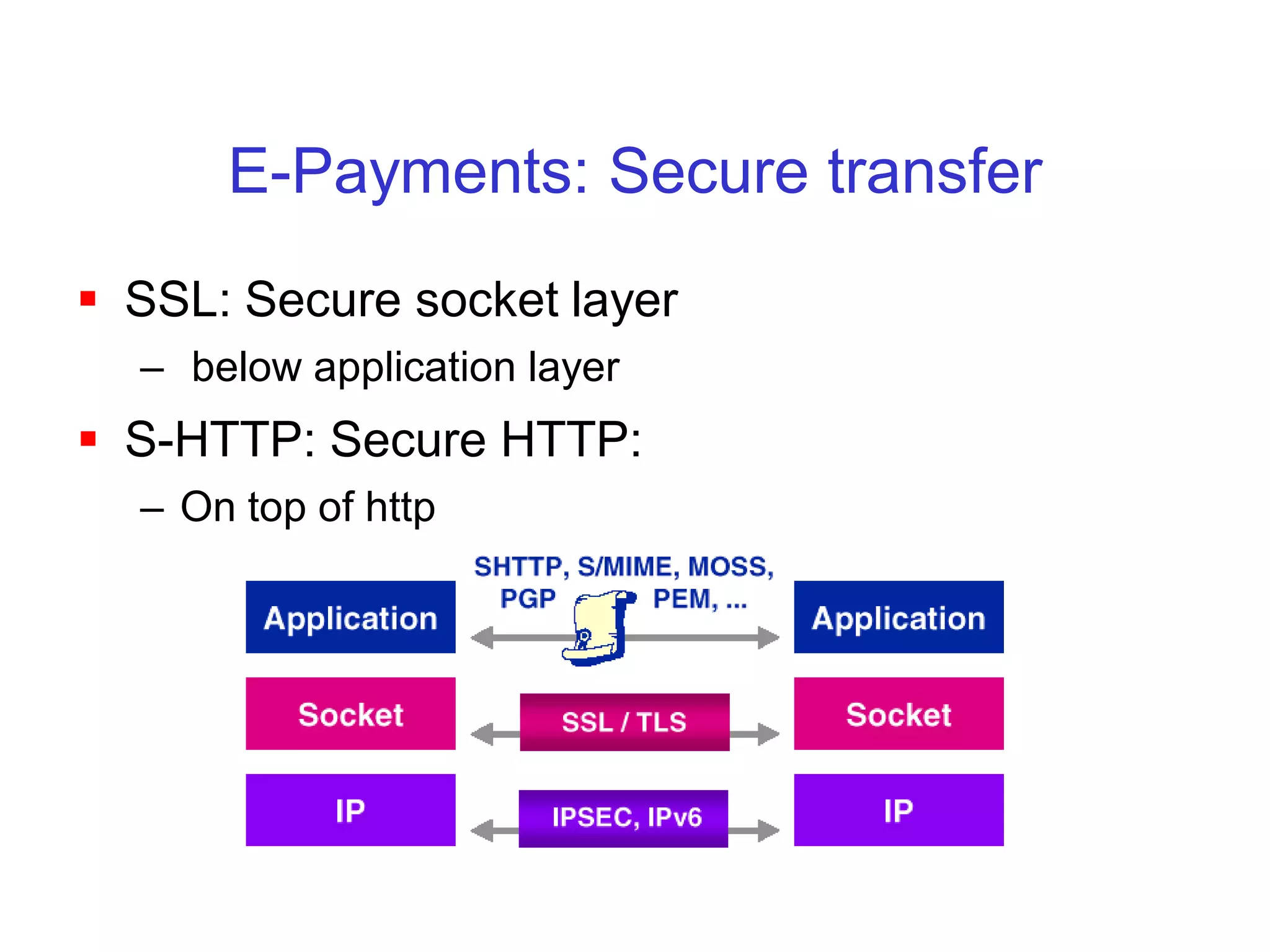
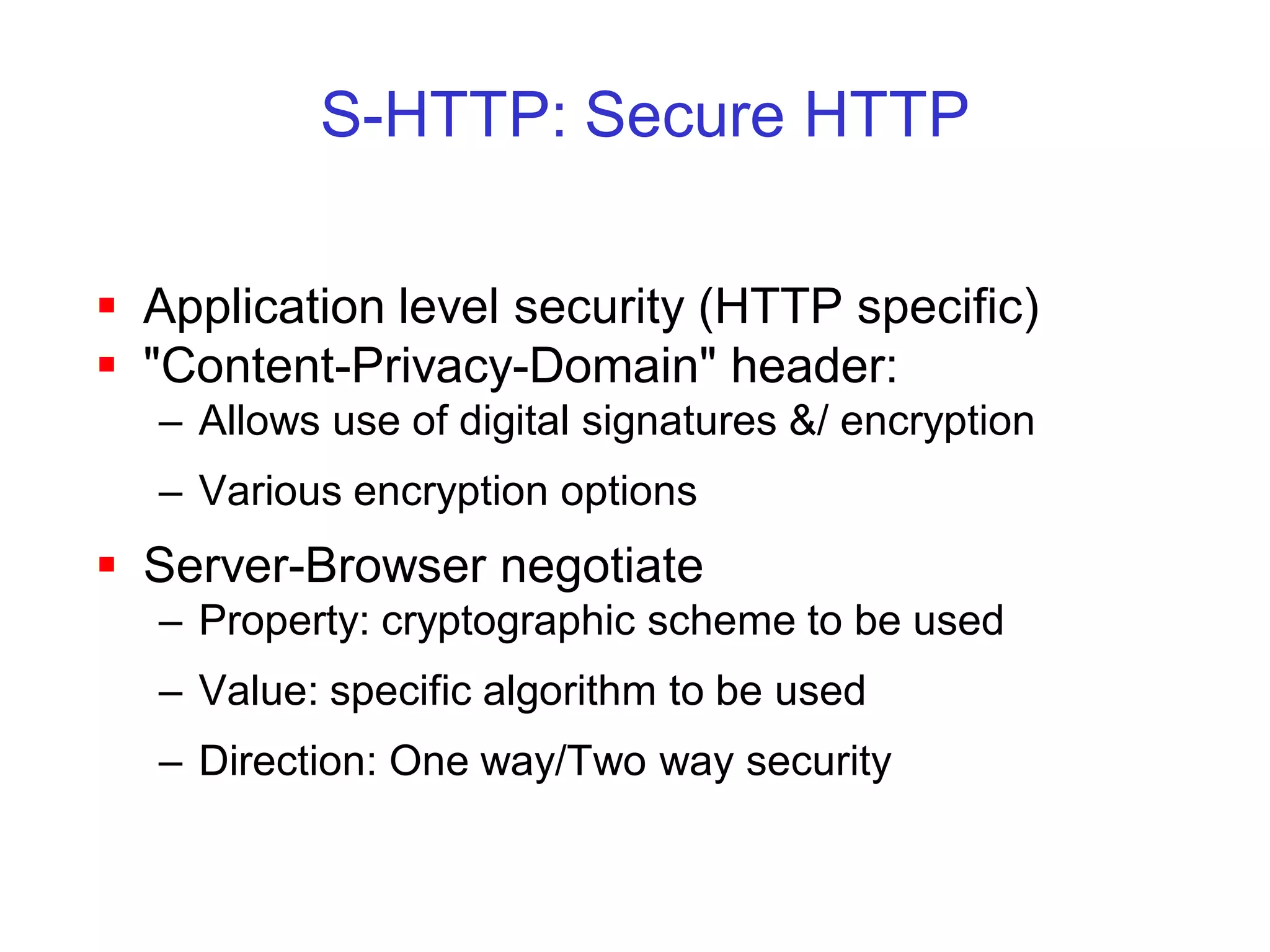
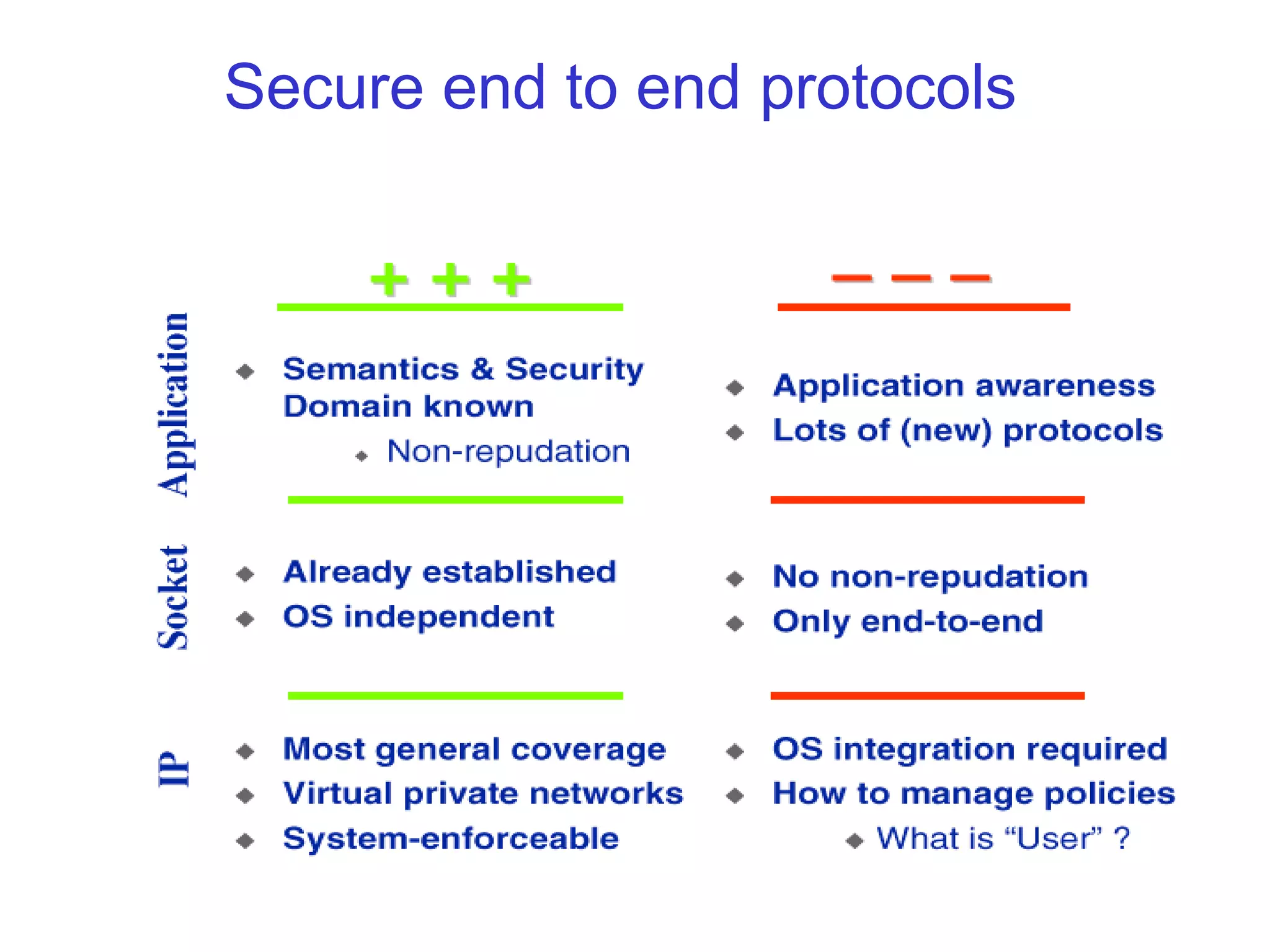
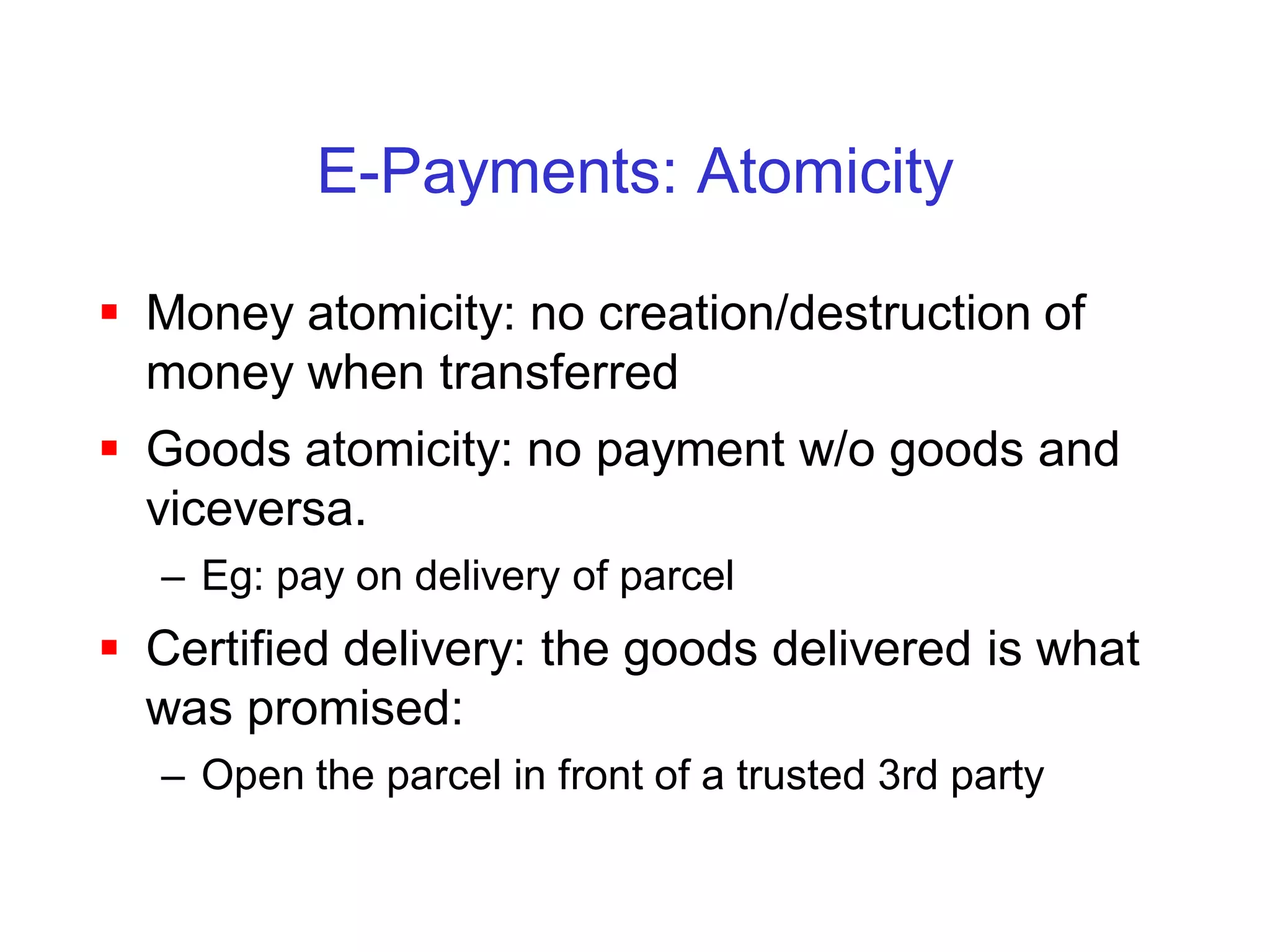
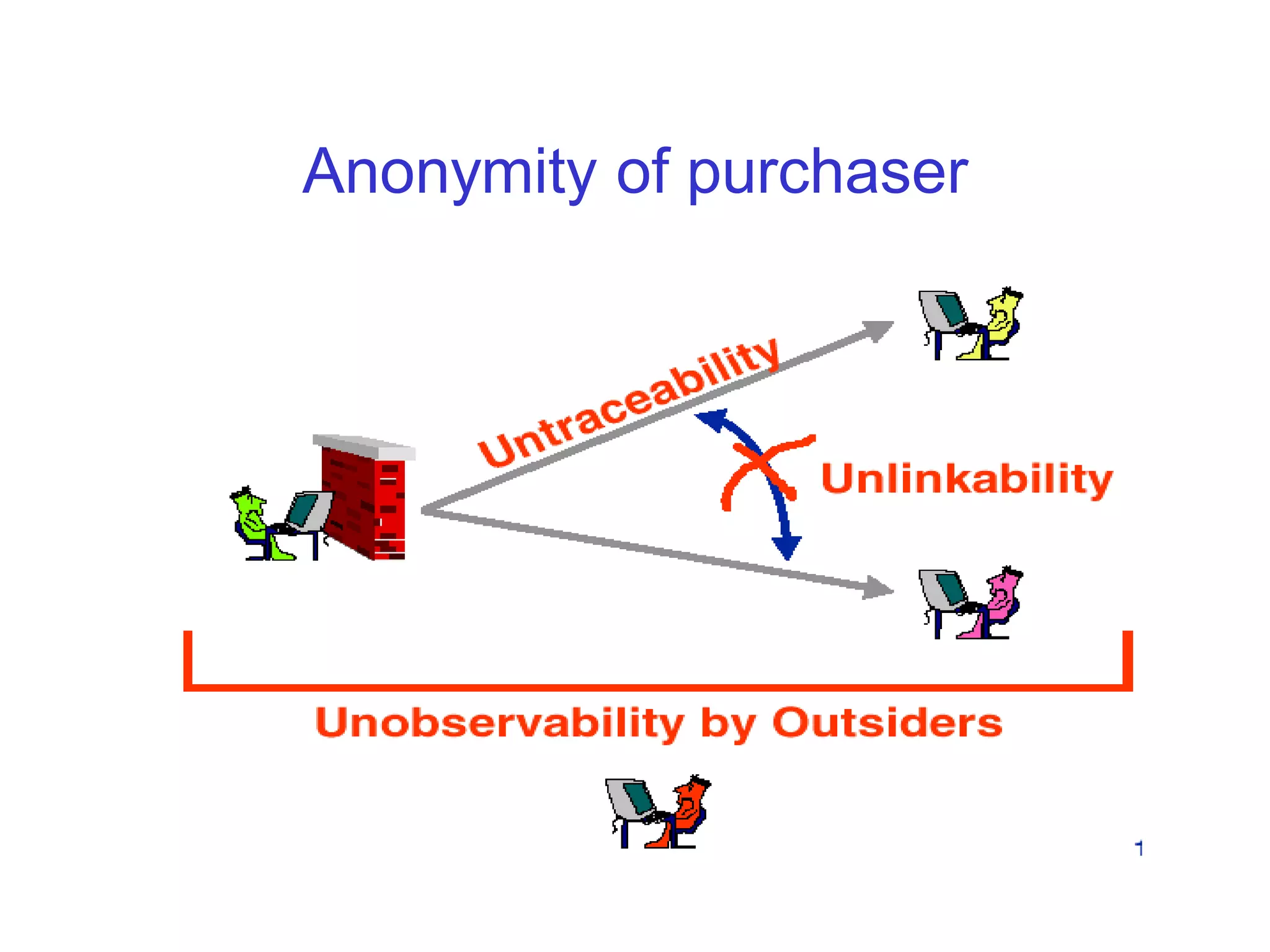
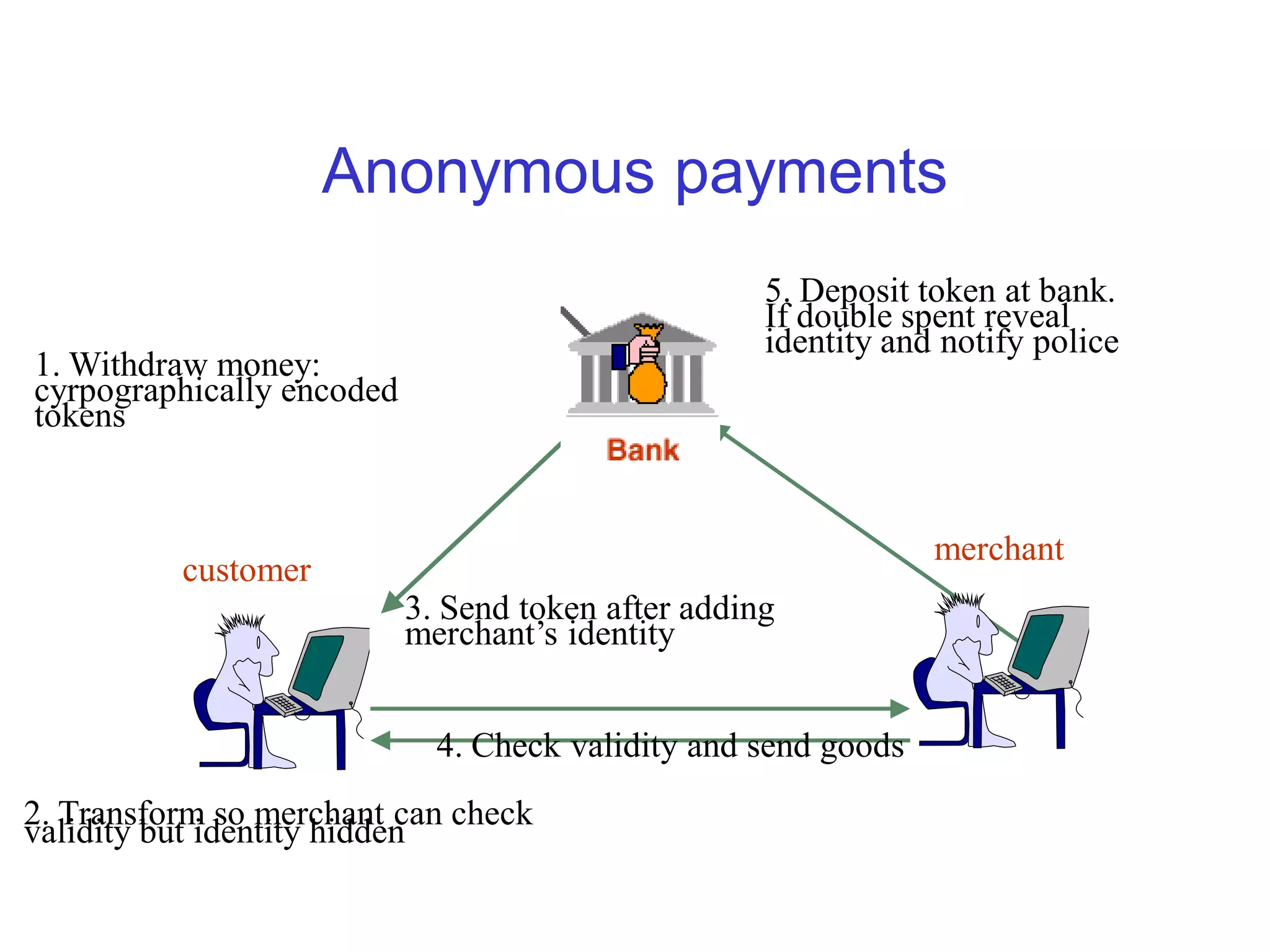
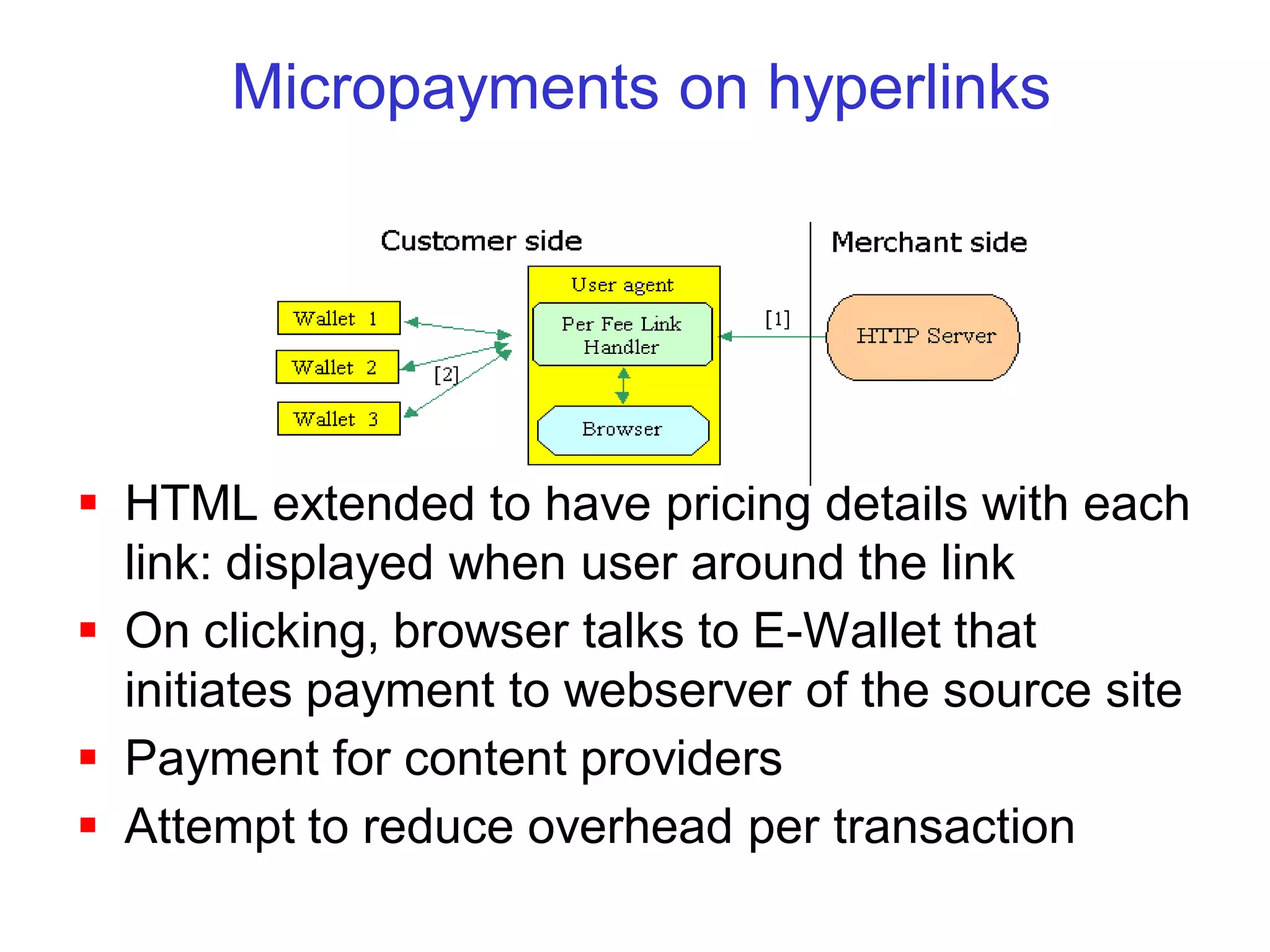
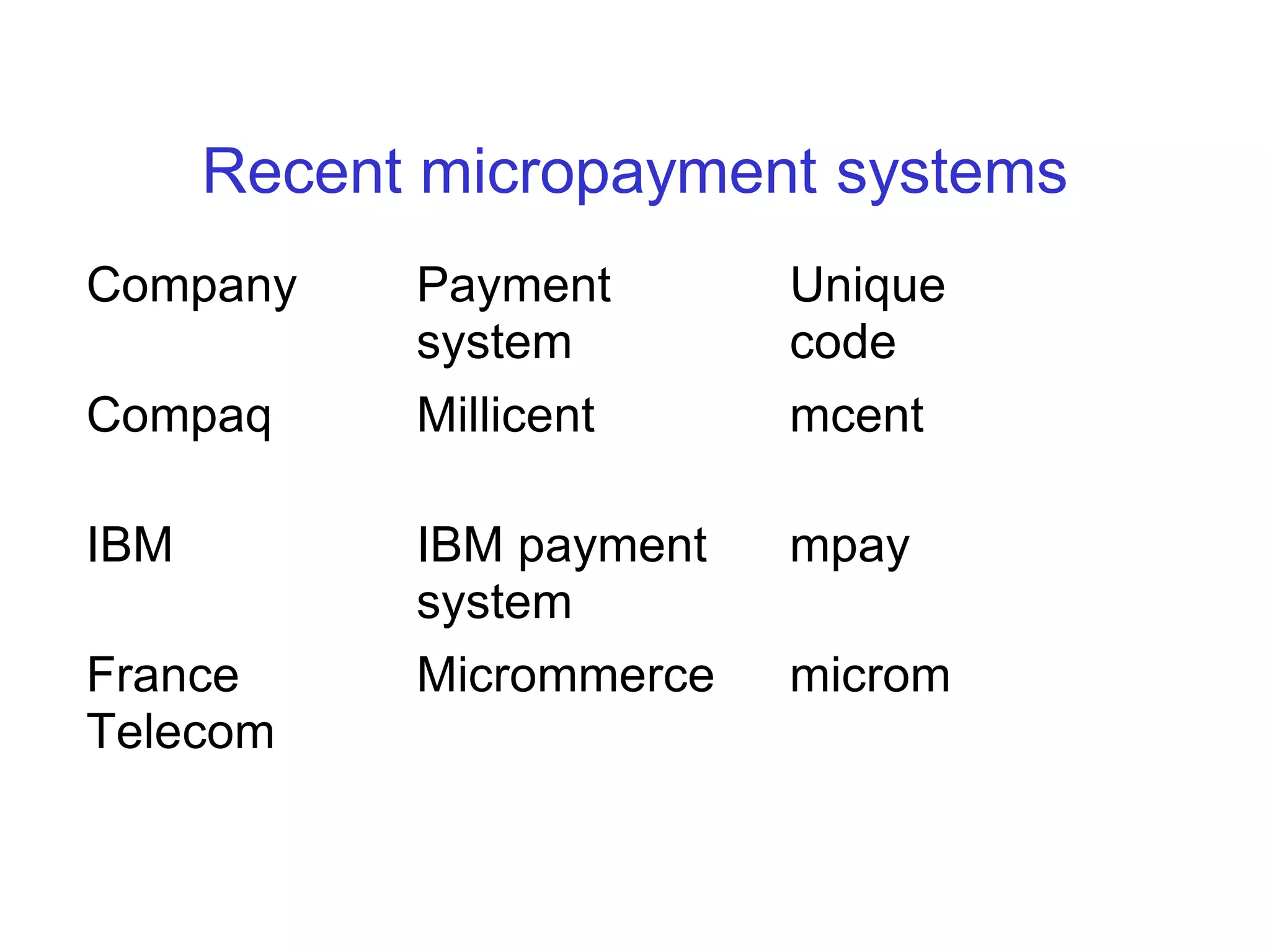
This document discusses secure web transactions and electronic payment systems. It covers underlying technologies like cryptography and network security protocols. It also examines different electronic payment methods including credit cards, electronic checks, anonymous payments, micropayments, and smart cards. The main challenges are providing security, reliability, anonymity, and efficiency for electronic commerce transactions.