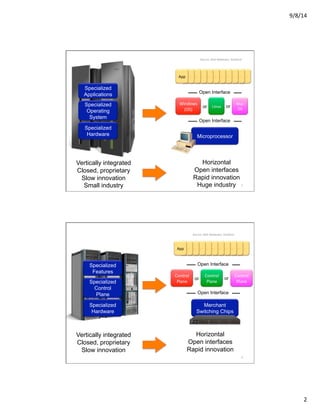
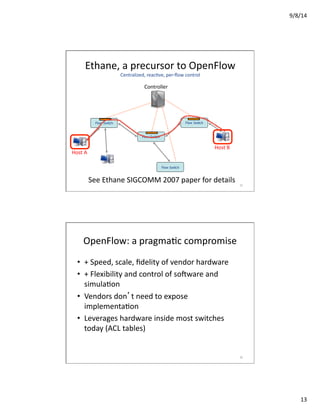
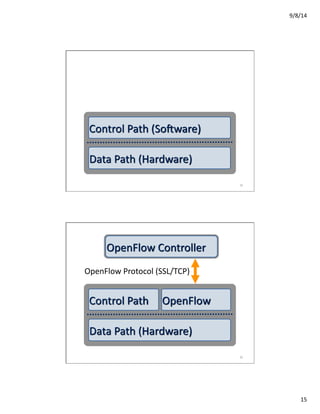
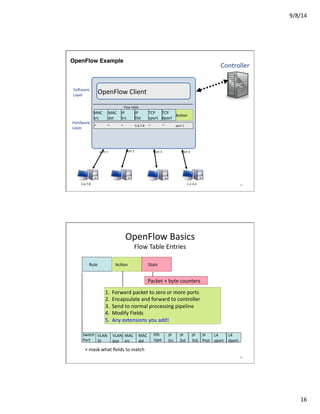
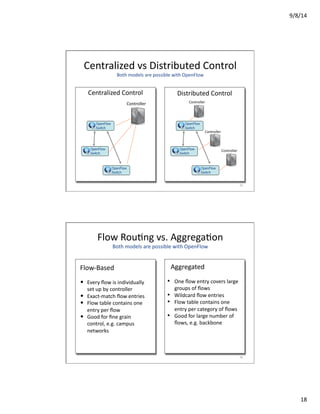
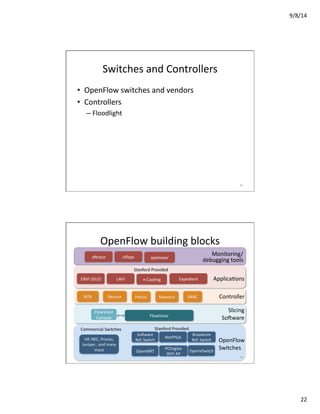
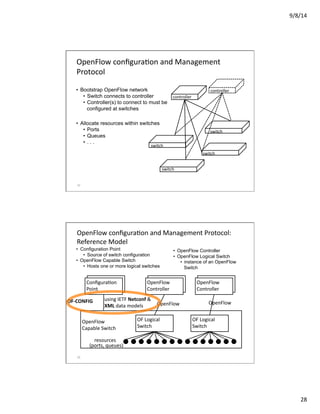
The document provides an overview of Software Defined Networking (SDN), detailing its concepts, the role of OpenFlow, and the architecture of controllers like Floodlight. It contrasts traditional, vertically integrated networking systems with the openness and flexibility offered by SDN, emphasizing the need for better abstractions in networking to keep pace with innovation. The text also discusses various applications of OpenFlow, its limitations, and the evolution of network control models.