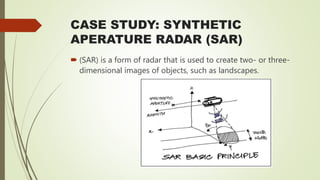
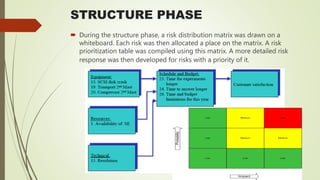
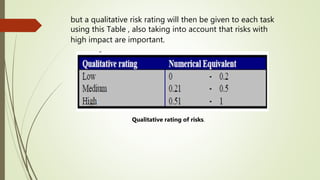
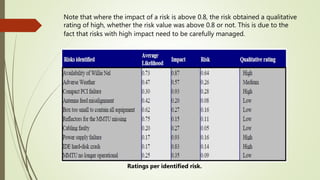
This document outlines the process of risk management for a graduation project on the topic. It defines risk and uncertainty, describes different types of risks like business and operational risks, and explains the principles and benefits of risk management. The key steps in implementing risk management are established as establishing context, risk identification, analysis, evaluation, treatment, and monitoring. Various risk analysis techniques are also presented, along with the application of the risk management process to a case study on developing a synthetic aperture radar system.