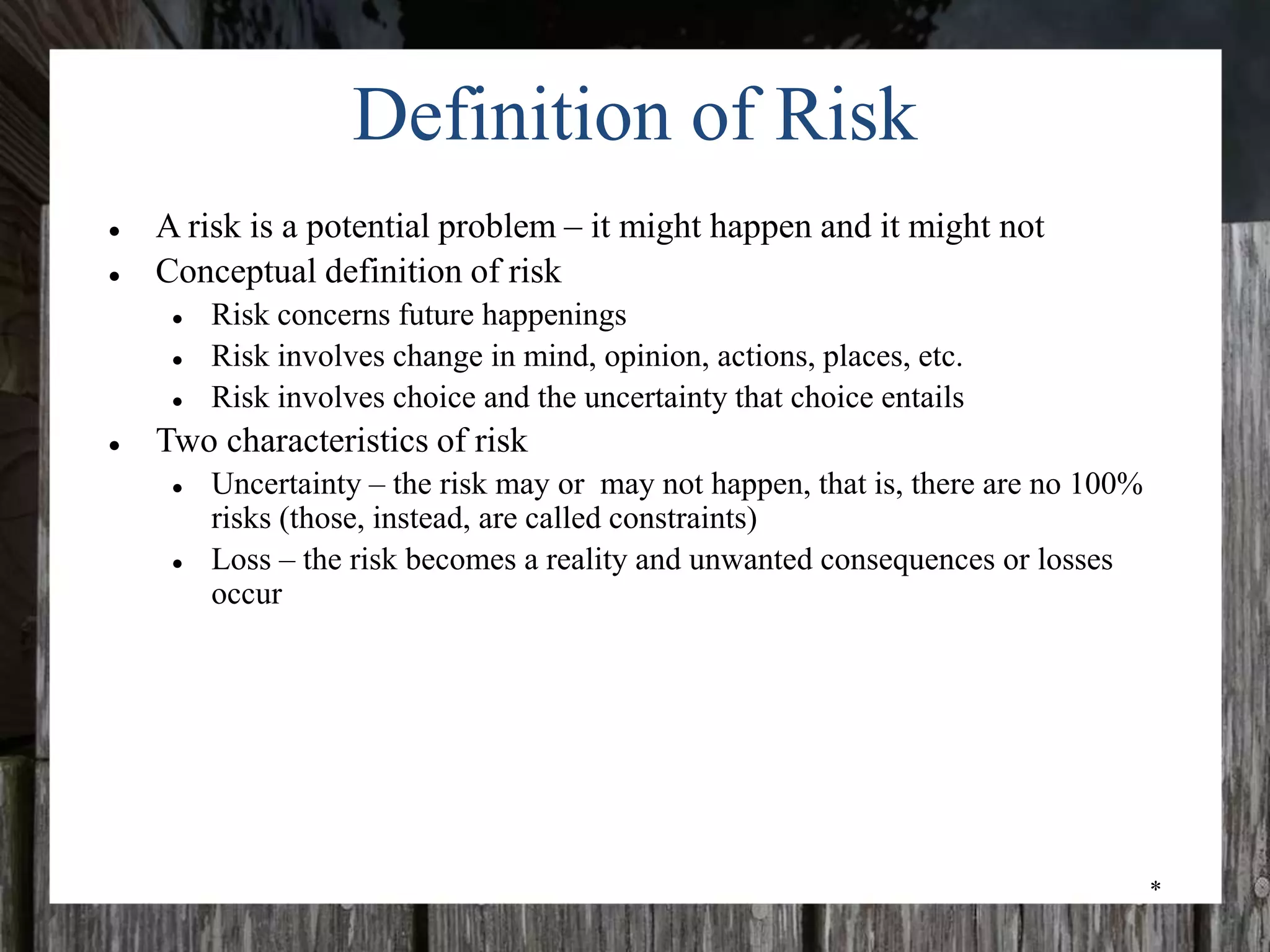
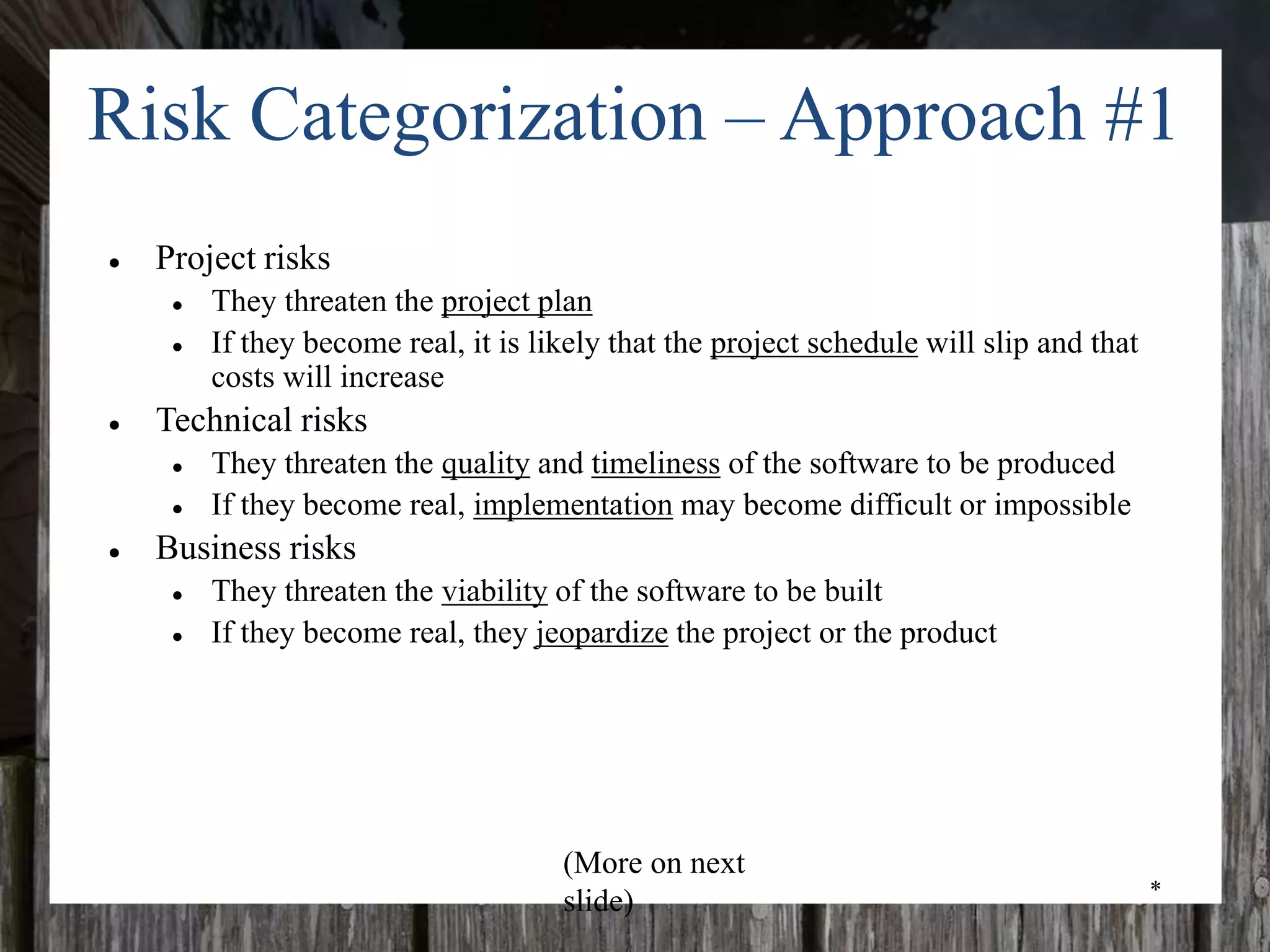
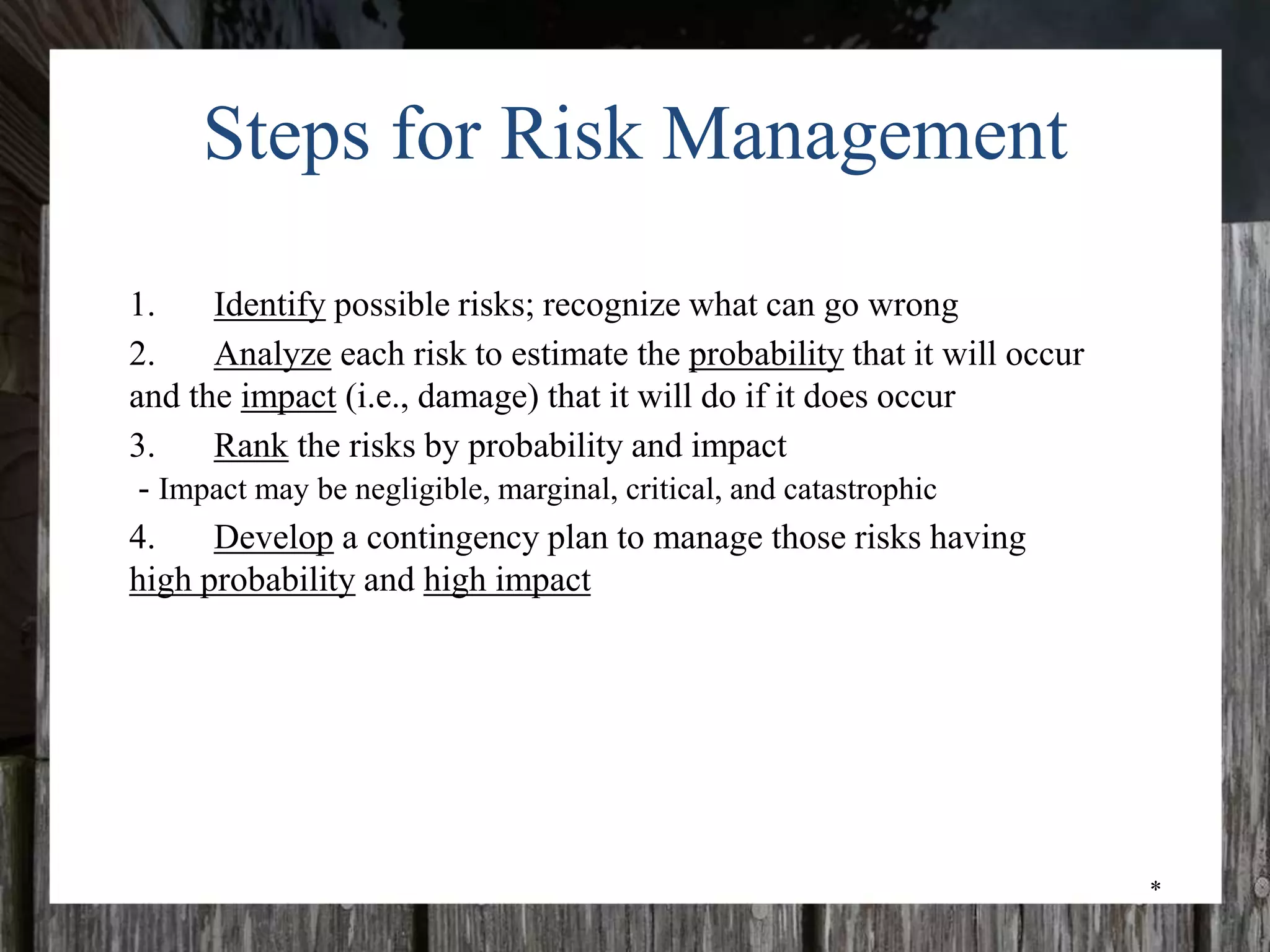
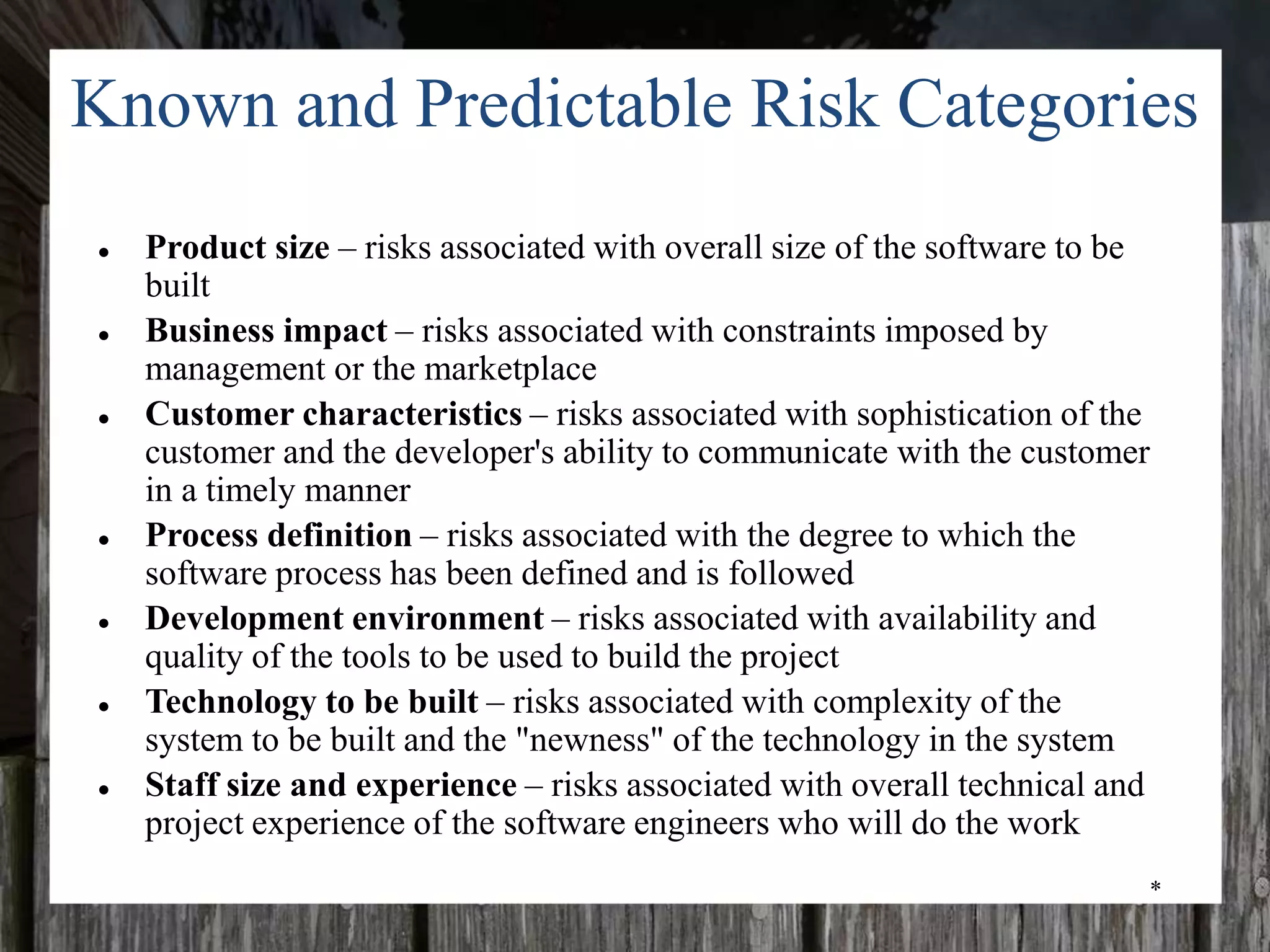
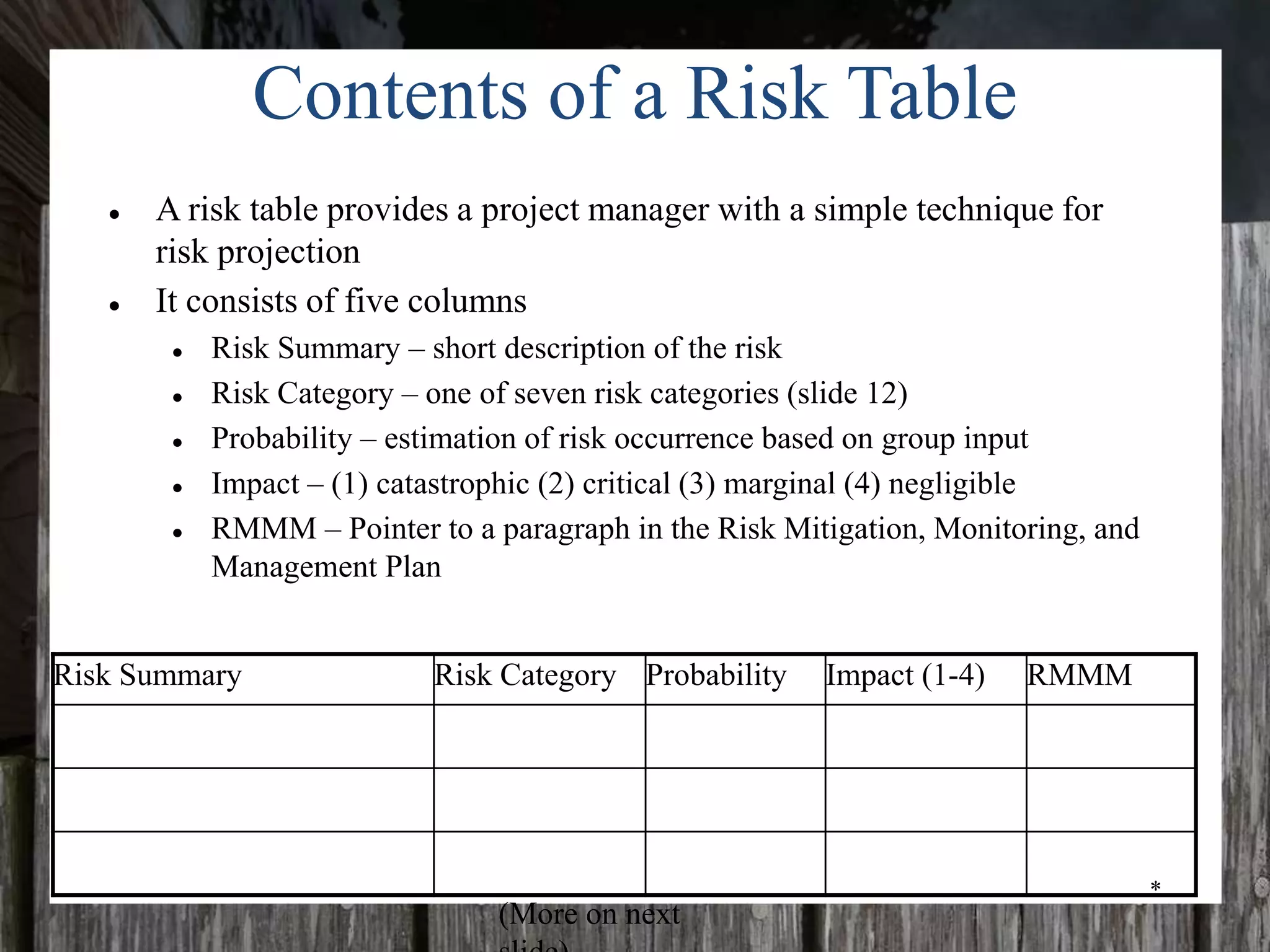
The document discusses risk management for projects. It covers risk identification, which involves categorizing risks and identifying known and predictable risks through checklists and questionnaires. It also discusses risk projection, which involves estimating the probability and impact of risks. Finally, it discusses developing a risk table to prioritize risks and plan risk mitigation, monitoring, and management strategies. The overall goal is to proactively address risks to avoid issues and have contingency plans.