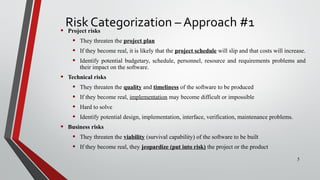
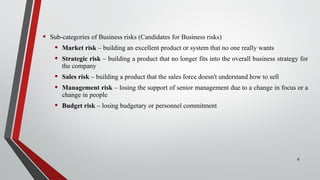
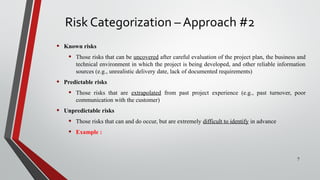
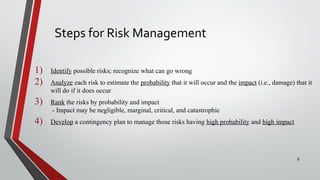
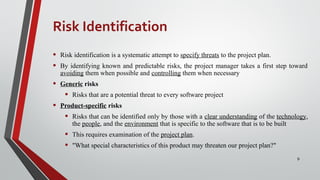
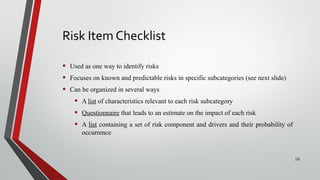
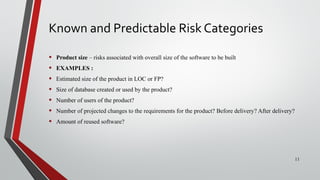
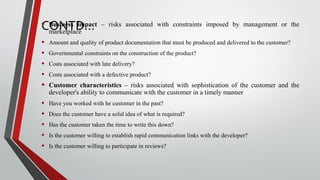
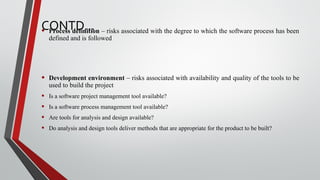
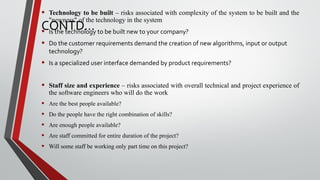
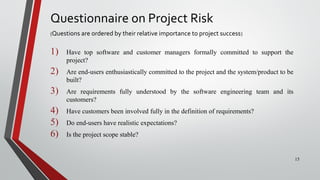
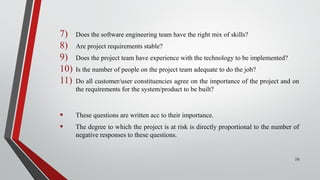
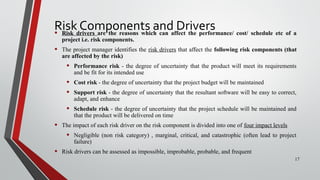
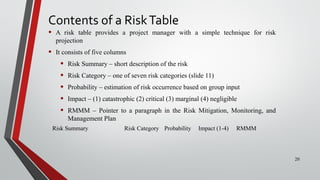
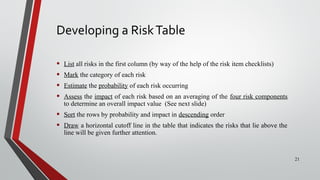
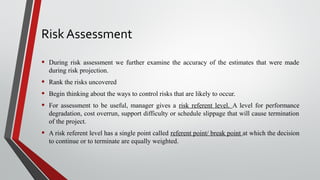
This document defines risk and risk management strategies for software projects. It discusses reactive versus proactive risk strategies, with proactive being preferred. It describes approaches to categorizing, identifying, and assessing risks. Key aspects of risk management covered include developing a risk table, estimating probability and impact, and creating plans to mitigate, monitor, and manage risks. The overall goal is to identify risks early and take steps to avoid or minimize their impact on the project.