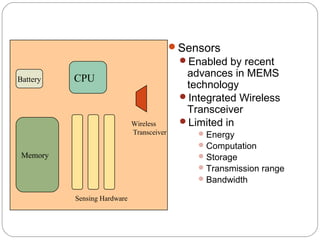
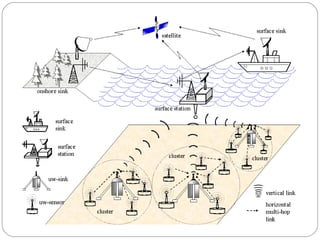
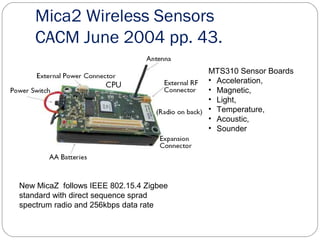
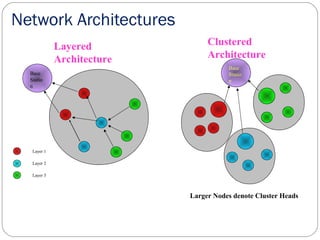
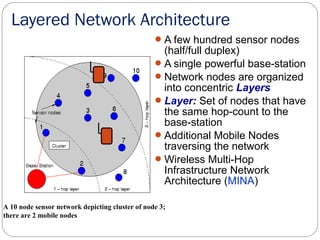
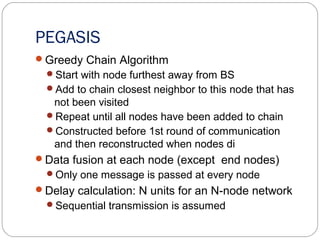
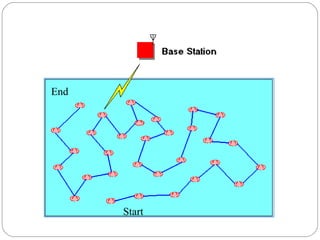
This document summarizes sensor networks, including their definition, components, applications, characteristics, architectures, challenges, and security approaches. Sensor networks consist of spatially distributed nodes that monitor environmental conditions and pass data to a central location. The nodes have sensors, microcontrollers, memory, and radios. Applications include area monitoring, healthcare, and environmental monitoring. Challenges include limited energy, computation, and transmission range. PEGASIS is an approach that forms nodes into chains to more efficiently pass data to the base station and minimize energy use. Security is provided using secret key encryption algorithms.