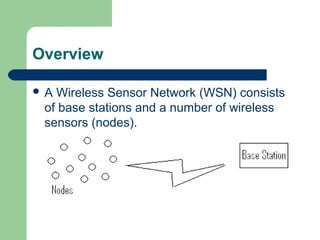
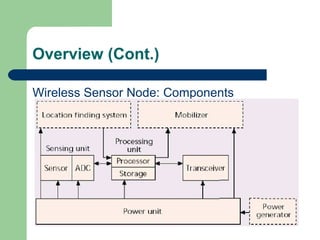
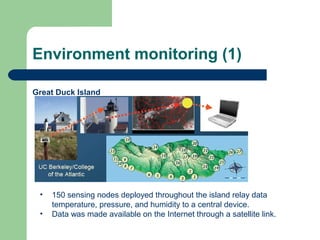
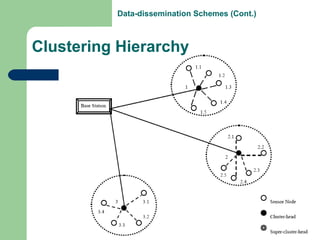
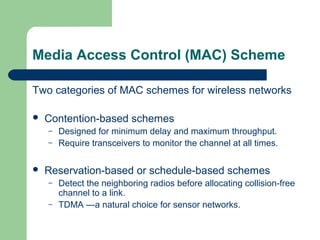
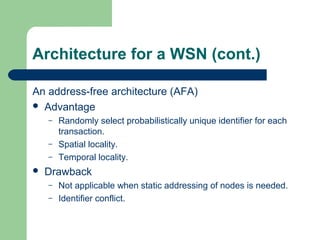
The document provides an overview of wireless sensor networks (WSNs), highlighting their components, characteristics, and applications in areas like environmental and medical monitoring. It discusses data collection methods, energy efficiency, and scalability challenges while emphasizing the importance of data-dissemination and media access control schemes. Key features include the ad-hoc nature of WSNs, stringent energy constraints, and the potential for various applications driven by the need for real-time data from densely deployed sensor nodes.