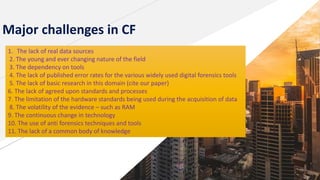
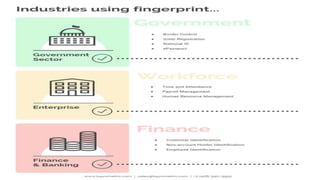
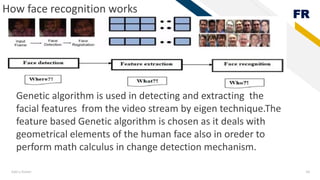
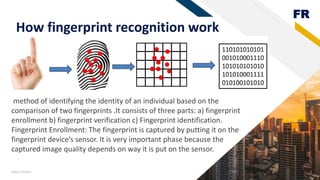
This document discusses cyber law, cyber forensics, and biometrics. It provides definitions and explanations of these topics. Specifically, it defines cyber law as the law governing information technology and aspects related to computing and the internet. It notes cyber law addresses issues like intellectual property, privacy, and jurisdiction in an online context. The document also defines cyber forensics as the process of using forensic science techniques to recover digital evidence from computers and digital devices in a way that preserves evidentiary integrity. It explains some common techniques used in cyber forensics investigations. Finally, the document defines biometrics as body measurements and calculations used for identification and access control. It provides examples of physiological and behavioral biometric identifiers like fingerprints, iris scans, and