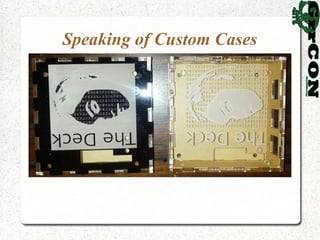
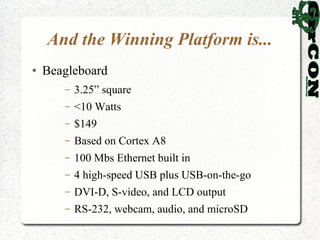
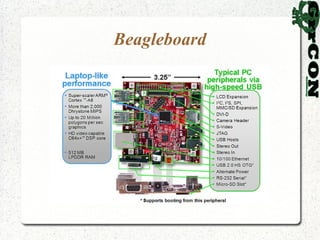
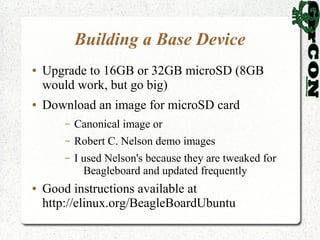
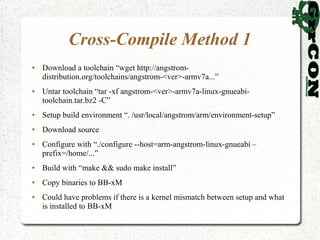
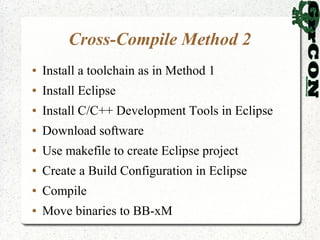
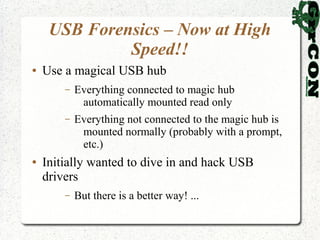
The talk discusses using low-power devices like the Beagleboard for hacking and forensics, emphasizing their portability and capability to run a full suite of tools. It covers selecting platforms, building systems, and the use of udev rules for USB forensics, alongside various cross-compiling methods for software development. Future directions include optimizing packages, creating custom cases, and the potential for weaponization of the technology.
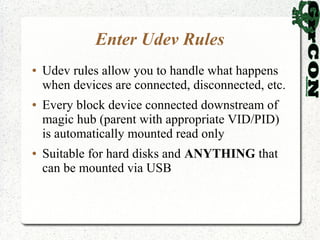
![Udev Rules Realized
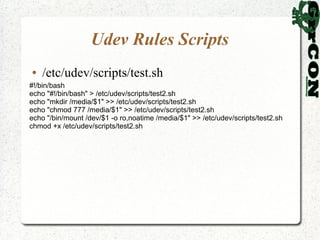
● In /etc/udev/rules.d/10-protectedmt.rules
ACTION=="add", SUBSYSTEM=="block", KERNEL=="sd?[1-9]",
ATTRS{idVendor}=="1a40", ATTRS{idProduct}=="0101",
ENV{PHIL_MOUNT}="1", ENV{PHIL_DEV}="%k",
RUN+="/etc/udev/scripts/test.sh %k"
ACTION=="remove", SUBSYSTEM=="block", KERNEL=="sd?[1-9]",
ATTRS{idVendor}=="1a40", ATTRS{idProduct}=="0101",
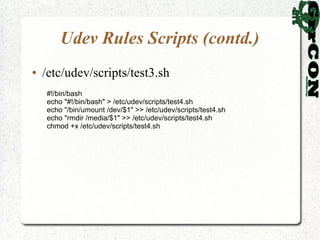
ENV{PHIL_UNMOUNT}="1", RUN+="/etc/udev/scripts/test3.sh %k"
ENV{PHIL_MOUNT}=="1", ENV{UDISKS_PRESENTATION_HIDE}="1",
ENV{UDISKS_AUTOMOUNT_HINT}="never",
RUN+="/etc/udev/scripts/test2.sh"
ENV{PHIL_MOUNT}!="1", ENV{UDISKS_PRESENTATION_HIDE}="0",
ENV{UDISKS_AUTOMOUNT_HINT}="always"
ENV{PHIL_UNMOUNT}=="1", RUN+="/etc/udev/scripts/test4.sh"](https://image.slidesharecdn.com/polstra-grrcon2012-121018164451-phpapp02/85/The-Deck-by-Phil-Polstra-GrrCON2012-44-320.jpg)